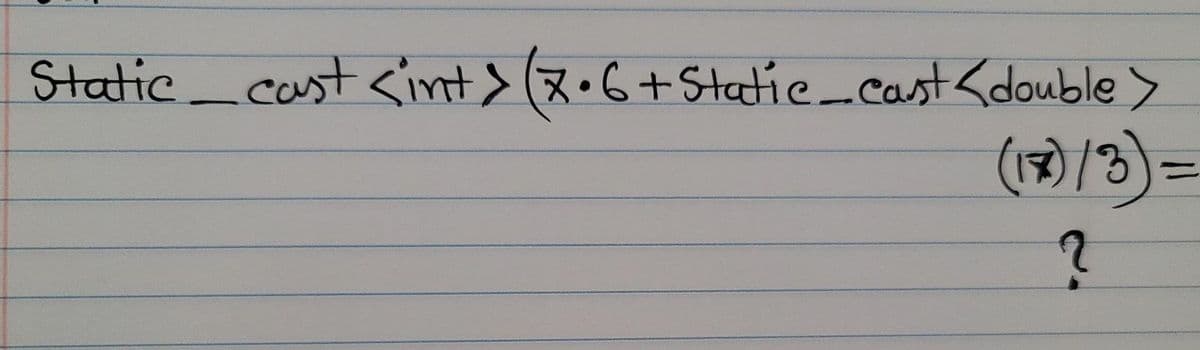
Static_coust (x•G+Statie_cast (1)/3) =
Q: Computer Science Hello, I have a question regarding R studio. How can I write a function named x tha...
A: Code: fun <- function(x,y){ return(x*y)} a <- c(1,2 ,3)b <- c(2 ,3, 4) c <- fun(a,b)c
Q: Information bits consisting of 1101 is to be transmitted using Hamming (7,4) code. a) Determine the ...
A: The question is on write the answer of the question related to Hamming code.
Q: A compound Boolean expression containing the or operator is true only when one of its subexpressions...
A: Intro A compound Boolean expression containing the or operator is true only when one of its subexpr...
Q: A program in the C language that receives from the user an actual number up to 3 digits after the do...
A: #include<stdio.h>#include <math.h>void main(){ double num = 0.0; printf("Enter a n...
Q: show problem using Hungarian method Min case Table
A: Find Solution using Hungarian method: Work\Job 1 2 3 4 5 A 10 5 13 15 16 B 3 9 18 13 6 C 10...
Q: What is the purpose of an operating system (OS)? What's the connection between a computer's operatin...
A: INTRODUCTION: We need to tell the purpose of OS and also tell about the connection between a compute...
Q: Which of the following statements is true about Deep Learning? a. Deep Learning is based on statist...
A: Answer: The correct option is (b) => Deep learning is a subset of machine learning
Q: for (i=0; i<1000; i++){ y[i] = w * x[i] + b[i]; } Above C-code has a for loop which will repeat 1...
A: Introduction for (i=0; i<1000; i++){ y[i] = w * x[i] + b[i]; } Above C-code has a for loop which ...
Q: 1. Decision tree problem See the following table- Sender Occupation Blood pressure level Diabetes re...
A: A decision tree is a flowchart-like structure in which each internal node represents a "test" on an ...
Q: Use an example to explain how business can better utilize disruptive and sustaining technologies for...
A: -innovation and technology plays vital role in modern bussiness and the working world. -the modern e...
Q: Can you please help me to do Snow Flakes in python please
A: Given: Could you kindly assist me with making Snow Flakes?
Q: 2. Consider the following network address: 209.15.6.0/28 a. How many subnets are there in this netwo...
A: Below is the answer to above question. I hope this will be helpful for you...
Q: 2. This involves a .txt file with one thousand rows of random numbers (between 1-1000) Using Py...
A: 1. File Input/OutputFile Input/Ouput (IO) requires 3 steps: Open the file for read or write or both...
Q: Conduct brief research on these two malwares and write in bullets their exploited vulnerabilities, i...
A: Cryptolocker is a type of ransomware that confines admittance to contaminated computer by encoding i...
Q: You are to create an example that demonstrates the use of different data types. Describe a problem y...
A: Suppose You are the manufacturer of a refrigerator. So to indicate the properties and characteristic...
Q: What exactly is DBMS? Using a coffee shop as an example, how can we retain data using DBMS? The cof...
A: The DBMS software is used to store and restore user data as well as to implement appropriate securit...
Q: ESSAY Non-technical cybersecurity threats Non-technical danger countermeasures
A: Non-technical cybersecurity threats non technical cybersecurity threat inclu...
Q: What are the considerations that should be made while switching from one system to another? Give det...
A: Introduction: Keep the following in mind while switching from one system to several: Changing a sing...
Q: Which of the following can be exploited to direct host to malware-laced servers?
A: An exploited server is one that is no longer fully under your control. Someone else is using it for ...
Q: n countries. One obvious way to estimate this is using a ratio est LATION. How can a linear regressi...
A: Step by step with explanation is given below: from the above question we can conclude that Hansen Hu...
Q: 4. In JAVA language strings are immutable, so how can you reverse a string. Write a JAVA program to ...
A: In JAVA language strings are immutable. Write a JAVA program to input a string and reverse the strin...
Q: What are the similarities and differences between a derived class and its base class?
A: Base class is the class in object oriented programming language from which other classes are derived...
Q: Explain the words undervoltage and overvoltage and how they might harm a computer or data.
A: INTRODUCTION: We need to define the terms Undervoltage and overvoltage and these terms harm the comp...
Q: Is it true or false The "margin" CSS attribute defines the space outside the element's border.
A: Explanation To create some space on every side of the elements and outside the borders, Cascading ...
Q: Assume you have access to the caches in your department's local DNS servers. Can you provide a metho...
A: Introduction: The local DNS (Domain Naming Registry) server's cache is available. This is the reposi...
Q: Write a program in python that takes a sequence of non-negative numbers and performs the computation...
A:
Q: How does multifactor authentication work? What role does it play in preventing password theft?
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful. Tha...
Q: Kindly could you please help me to do Snow flakes in python Please explain this for me I’m really co...
A: The Snowflake Connector for Python provides a way for Python programmers to connect to Snowflake and...
Q: If your GPU runs out of memory during training a CNN, what additional options do you have except acq...
A: Introduction: GPUs rely on data being set out as dense vectors in order to fill very broad single in...
Q: ths 2 to 6.
A: given - define in detail the execution paths 2 to 6.
Q: What is the connection between data and information?
A: Data: It is an assortment of values. Those values can be characters, numbers, or some other type. ...
Q: Take the list of elements from the user and after that, you realised that you forgot an element to p...
A: I give the code in python along with output and code screenshot
Q: A new veterinary clinic will need to create a database. The clinic would want to preserve records of...
A: Intro For creating tables in 1NF or 1st Normal Form, the following properties must be satisfied: Th...
Q: What are the advantages and disadvantages of using IPSec over other network security solutions, such...
A: IPSec or IP security is a pack of protocols in an Internet protocol network between any two communic...
Q: Give two reasons why data should be duplicated across several data centers that are geographically s...
A: Introduction: In the context of data replication, the use of the network to replicate data across ma...
Q: If we use 5 bits to represent special symbols in a binary coding scheme, how many different symbols ...
A: You have 5 bits, so there are 32 different combinations. It means that you can make 32 different num...
Q: Given information: # A set of constants, each representing a list index for station information. ID...
A: Introduction Given information: # A set of constants, each representing a list index for station inf...
Q: Suppose that a manufacturing company builds n different types of robots, say robots 1, 2, . . . , n....
A: We call this a canvassing because it is not a representative, randomized survey. Its finding emerge ...
Q: Define/Explain the topic fully and identify the role that particular term, concept, or analysis play...
A: As per company guidelines we are suppose to answer only first 3 subparts of the question. Kindly re-...
Q: 3. Write a C++ program to print the week days from the week number(1= Saturday, 2= Sunday,.. 7= Frid...
A: We are going to write a C++ code which will print week days based on weekday number given based on m...
Q: Describe a case in which a user's total denial of a service (i.e., the user receives no answer from ...
A: INTRODUCTION: A Denial-of-Service (DoS) attack is an attempt to prevent a computer or network from f...
Q: Create a class called Complex for performing arithmetic with complex numbers. Write a program to te...
A: The solution as given below steps :
Q: Write python codes to implement two images addition with different weights. Then show the original t...
A: You can substitue your own images in the imread ,change weights accordingly and blend and execute in...
Q: A) Create a super (parent) class called Course. The Course class represents any course that does not...
A: NOTE: Programming language is not mentioned, so I am doing in JAVA In this question, there are three...
Q: Explain rounding briefly.
A: Introduction the question is about Explaining rounding briefly and here is the solution in the next ...
Q: In terms of media, what distinguishes an infrared network?
A: An infrared network:-
Q: Modify this program to open the file "Customers.dat" so that all data can be read, and data written ...
A: Introduction: Modify this program to open the file "Customers.dat" so that all data can be read, and...
Q: what is NORA and Explain with example Nonobvious Relationship Awereness
A: answer is
Q: What factors should be considered while selecting a physical network protection solution?
A: we just need to used Secure Network Topologies to protect the physical network Topology is the physi...
Q: What exactly is a natural ordering? How can you define a natural ordering for a class that you creat...
A: Natural ordering is a type of total ordering that is the default (most commonly used) for the provid...
Step by step
Solved in 4 steps with 2 images

- C++ Code 9.16 Lab 06: Dynamic Arrays (Part 2) Step 1a: Preparation The suite of Part 1 tests has been moved to its own function. The code in main() is focused on testing the new operators you'll write in this part. main() relies on a change you're going to make to the DynamicArray::print() member function (coming up in Step 1b). Instead of directly using cout, this member function is now going to print to a stringstream. This allows my test code to examine the output and check it automatically. How 3 representative lines of the new main program work: // Use stringstream to capture your print function's output.stringstream testoutput;// Use the same testoutput variable over and over, so we reset it to the empty string between tests using its str() member function.testoutput.str(""); // Reset test output string// Call the print function on your array, and it prints to testoutput instead of cout.a.print(testoutput);// Use the RunIndividualTest function also included in main.cpp to…In terms of type declaration, how are rvalue references and lvalue references different?What are the advantages and disadvantages of keyword parameters?
- The functions that can be used in an elements classList() function are:Static analyzer write code c++ create your static analyzer tool thatreads your code as a text. Then, it analyzes it based on the below checklist. The checklist: - Do the attributes (e.g., data type and size) of each parameter match theattributes of each corresponding argument?What are the advantages of typed parameters?

