Step 1 W = (Pext)dV -V2 Step 2 W = (P, dV ext 'V1 Step 3 W = (Pext) InV -V, Step 4 W = (Pext)(V2 – V1) %3D Step 5 W = PeyAV ext
Q: (1) Mark the linear range (2) How can you extend this linear range? Show an approximate extended…
A: Solution::
Q: 1- Convert NFA to DFA for following NFA Convert the given NFA to DFA. 0,1 2- Convert NFA to DFA for…
A: Solution-1) The transition diagram is as follows:- The transition table of NFA is as follows:- The…
Q: Consider the following &-NFA M=({q1, q2, q3}), {a, b}, ō,q1, {q2}), where õ is: ō (q1, ɛ) = {q2} Ō…
A: Introductions : Given ,A epsilon-NFAWe have to find the entries for (q1,a) and (q3,b) in the…
Q: Which of the following statement is TRUE about Boundary Representation (B-Rep)? O B-Rep = Wireframe…
A: B-rep (boundary representation) 1) It is a rendering technique for solid modeling. 2) It is a…
Q: • Based on the graph given, perform the following: 1. DFS @ 11: (Lowest Data Value) 2. BFS @ 11:…
A: Here, we are going to traverse the given graph using BFS and DFS.
Q: MATLAB program to compute the 2N-point DFT of a length-2N real sequence using a single N-point DFT…
A: Task : Given the two random N length vector. Find their DFT and plot it for comparsion.
Q: reduce this DFA
A:
Q: Assuming that Σ = {0, 1}, for the expressions given below, draw transition diagrams and transition…
A: Assuming that Σ = {0, 1}, for the expressions given below, draw transition diagrams and transition…
Q: 11. Which graph represents the solution set for -4(1- x) s-12 + 2x? A. +++ -34 -32 -30 -28 -26 B…
A: We are going to find the graph which can represent the equation given. Please refer to image for the…
Q: 1. Enter 1 variable and draw the truth table of FMEV1. 2. Enter 2 variables and draw the truth table…
A: Truth table of FMEV1 and FMEV2
Q: Match the following : 1. Complementary Law - + AB = A -- I) A 2. AND Law - II) A + A = A 3. OR Law -…
A: Task :- Match the given options and choose the correct one.
Q: Convert the following algorithm into Python code Algorithm 2: Cluster formation phase: Selection…
A: Convert the following algorithm into Python code Algorithm 2: Cluster formation phase: Selection…
Q: ) From source code , derive a CFG . B) Select paths from CFG based on path selection criteria C)…
A: Answer A) Control flow graph:…
Q: Use the paired values below to create a perceptron to model the distribution. Assume that the paired…
A: First, we will declare the DATAX array and DATAY array. Then we will fir the model. And finally,…
Q: Consider the two pairs of hazard conditions are 1a. EX/MEM.RegisterRd ID/EX.RegisterRs 1b. EX/MEM…
A: 1a. EX/MEM.RegisterRd = ID/EX.RegisterRs 1b. EX/MEM.RegisterRd = ID/EX.RegisterRt 2a.…
Q: Q3 Determine the minimum expression for each K map in Figure CD CD CD CD AB AB CD CD CD CD 1 1 AB 1…
A: The Karnaugh map is a method of simplifying boolean algebra expressions.
Q: True/False: a) There exists a mapping reduction from ETM to EDFA. b) There exists a mapping…
A: Please give positive ratings for my efforts. Thanks. ANSWER a) Yes, there exists a mapping…
Q: Apply the strongly connected component (SCC) algorithm described in the course to identify all the…
A: Pseudo Code: 1. For each vertex u of the graph, mark u as unvisited. Let L be empty. 2. For each…
Q: Given the following code written in GLSL for Blinn-Phong model. Name v1, v2, v3, v4, component1,…
A: Solution is given below :
Q: Given the Deterministic Finite Automation (DFA) below 1 $2 i) Write the set of final states for the…
A: The graph is given with characteristics:- It is a type of Deterministic finite automation. There…
Q: -10 7 8 -6 -6 0 7 1 A = -7 -1 1 7 B = -3 7 -7 -3 -6 7 -4 -2 0 -10 3 1 -3 10 -3 3 1 -4 C = 6 -8 7 D =…
A: Given:
Q: Transform the following NFA to DFA 0, 1 0, 1 2 3 1 1
A: transform NFA to DFA
Q: IMG_SHAPE = (3, 32, 32) test_input = torch.randn(1, *IMG_SHAPE) model = DeepAutoencoder(IMG_SHAPE,…
A: Answer: I have complete code in python.
Q: What is K Map and how to make table through k map and how to grouping 1) Implement Half Subtractor…
A: K-Map (Karnaugh Map) The graphical technique of simplifying Boolean expressions is known as the…
Q: Given: CFG G2 S -> ABA | C A-> Sale B-> bB | b C -> CA Clean the given CFG G2 by: 1 - Remove useless…
A: Given :
Q: 1. A sequence of n operations is performed on a data structure. The ith operation costs i if i is an…
A: Amortized analysis: They have no involvement of probabilities where the average performance on a…
Q: .Convert the following CFG into CNF: 1- s> bA | aB, A-→ a| as | bAA, B→ b | bS | aBB, 2- s>Xax,…
A:
Q: Consider the degree-4 LFSR given by x to the power of 4 space plus space x squared space plus space…
A:
Q: Use an example to demonstrate the properties of OOP.
A: Introduction: oop (Object-Oriented Programming) is based on the class and object principles. Class:…
Q: Compute the similarity between R and T by using Jaccard Coeficient and SMC (Mathematically
A: Task : Given the dataset having two rows. Find the Jaccard Coeficient and SMC.
Q: Given: CFG G1 S-> BC | DaD | b A-> CD | bA | c B> Cb C-> aB D -> bs | E Clean the given CFG G1 by: 1…
A: 1) remove useless symbols Useless symbols are symbols that have never been a part of any string. The…
Q: What is the value of a and b if (49), = (133), %3D
A: Introduction Given If (49)a = (133)b we have to find value of a and b.
Q: /*Line 1:*/ doublevalues[6] = {10, 20, 30, 40, 50, 60}; /*Line 2:*/ double* yalptr= values; /*Line…
A: NOTE: - There is error on line 1 the way of declaring and initializing an array is wrong.…
Q: 8-11 A- 1 4 2 256 3 6 then >> D - CELL (A) returns
A: Answer in step 2
Q: aSn-q + bSn-r + cSn-s Sn+1 = Sn-p dSn-q + eS n-r + f Sn-s ) ’ b. are investigated, where a, b, c, d,…
A: Note: Answering the question in python as no language is mentioned. Input : Initial values of…
Q: Draw a non-deterministic PDA that recognizes the following: ‒‒‒‒‒‒ a. {wOwR | w€ {0,1}* } R is for…
A: Non-deterministic PDA (NPDA): It require multiple computation to check acceptance of string .…
Q: 5. Consider the following transition table: q 6 (q, a) | 8 (q, b) | & (q, A) {2} {5} Ф 1 Ф Ф 2 {3} Ф…
A:
Q: Q:Change this code from Matlab to Phython: clear data = load('ex2data2.txt'); x = data (:, [1, 2]);…
A: I attache your answer above.
Q: Q1. step B-reduce below untyped A-terms to their normal form. Clearly demonstrate every single…
A: using System; public class Sudoku { int[,] mat; int N; // number of columns/rows. int SRN; //…
Q: Draw the diagram of LFSR with characteristic polynomial x^6+x^5+x^3+x^2+1. What is the maximum…
A: The above question is solved in step 2:-
Q: Compute the sv for game w =u+v = {W₁, W2, W3, W12, W13, W23. W123} = {1, 0, 0, 3.64, 2.7, 0.3, 4}
A: The sv for the equation w=u+v=W1, W2, W3, W12, W13, W23, and W123 is equal to 1, 0, 0, 3.64, 2.7,…
Q: Explain collision & abortion in CSMA/CD with neat diagram and also explain flow diagram for CSMA/CD.
A:
Q: Find the network diagram of the following data.
A: Given that: Solution: Activity Immediate Predecessors Duration A - 2 B - 4 C - 3 D A 1…
Q: ate between a xt of a grocery store. one-to-many and one-to-one relationship. Provide an examp
A: Introduction: Below the Difference between a one-to-many and one-to-one relationship an example of…
Q: 4) In the working set model, for: ... 1 34 5 6 0 3 2 3 2 0 4 0 3 2 9 2 1..., if DELTA = 6, then the…
A: Given: Working set model: 13456032320 4032921 DELTA = 6
Q: Compute the global alignment and the best score of the following sequences CGTGAA, GACTTAC with the…
A: Compute the global alignment and the best score of the following sequences CGTGAA, GACTTAC with the…
Q: l222: div bx push dx mov dx,0 mov ah,0 inc cx cmp ax,0 jne l222
A: Assembly level language is a low-level programming language, it's used to communicate directly with…
Q: onst <- as.matrix( rep(1,8), 8,1); :<- cbind( runif(8,0,1), runif(8,0,1) ); <- cbind( const ,…
A: The answer is
Q: Q1: a)Evaluate the following Integration: S(x-3)3 dx (x2-9)
A: Problem 1.
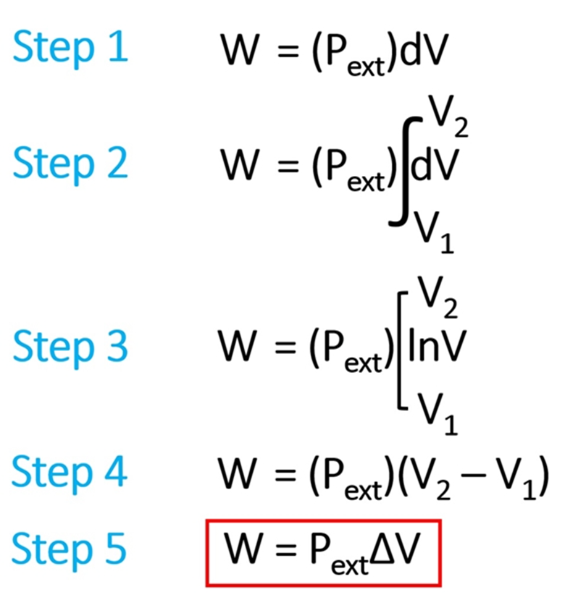
In which step the derivation had a mistake?
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- 1. Every time refactoring is done, one must run _______ _______ . 2. In the observer design pattern the observer must be registered (added) to the _________ that will _________ the observer of state changes. 3. When contextually different ways of solving a problem is required then the ________ pattern may be used to change the solution by testing a __________ . 4. In the layered architecture each layer consists of highly ________ components. A disadvantage of the layered architecture is skipping ________ to communicate.A featured transition system (FTS) represents a tuple F = (S, Act, trans, I, AP, L, F, K, δ), where S, Act, trans, I, AP, and L are defined as in TS; F is the set of available features; K is a set of valid configurations; and δ : trans → F eatExp(F) is a total function decorating transitions with presence conditions (feature expressions)(a). Without running the code in Python, describe the architecture for the followingdeep learning model, including number of layers, dimension of images in each layer,number of parameters in each layer. Show details of all you calculations.inputs = keras.Input(shape=(36, 36, 1))x = layers.Conv2D(filters=16, kernel_size=5, activation="relu")(inputs)x = layers.MaxPooling2D(pool_size=3)(x)x = layers.Conv2D(filters=64, kernel_size=3, activation="relu")(x)x = layers.MaxPooling2D(pool_size=2)(x)x = layers.Conv2D(filters=128, kernel_size=2, activation="relu")(x)x = layers.Flatten()(x)x = layers.Dense(128, activation="relu")(x)x = layers.Dropout(0.5)(x)outputs = layers.Dense(10, activation="softmax")(x)model = keras.Model(inputs=inputs, outputs=outputs)
- Please describe the idea of "expandability" as a criterion to be taken into account while choosing neighbor devices in your own words.Considering the datagram “JAZAN UNIVERSITY”. Explain with the help of a diagram all the transformations that it has to go through in each layer of the OSI reference model. Define all the headers that will be added in each layer while sending and define all the headers that will be removed while receiving. answer has a word limit of 100 words; you have to follow the word limit strictly. This is how to do it please I need that answer asap Given data: Datagram= “JAZAN UNIVERSITY” Step 2 Explanation of question: The datagram is given in the problem and it is asked to represent the given datagram transformation in each layer of the OSI reference model. So, you have to consider all the layers of the OSI model and display what will happen with the given datagram in each layer one by one by using diagrams. It asked to specify the sending and receiving header in each layer. For example: First, you have to specify what will happen with the datagram "JAZAN UNIVERSITY" in the…Considering the datagram “JAZAN UNIVERSITY”. Explain with the help of a diagram all the transformations that it has to go through in each layer of the OSI reference model. Define all the headers that will be added in each layer while sending and define all the headers that will be removed while receiving. answer has a word limit of 100 words; you have to follow the word limit strictly. This is how to do it please I need that answer asap Given data: Datagram= “JAZAN UNIVERSITY” Step 2 Explanation of question: The datagram is given in the problem and it is asked to represent the given datagram transformation in each layer of the OSI reference model. So, you have to consider all the layers of the OSI model and display what will happen with the given datagram in each layer one by one by using diagrams. It asked to specify the sending and receiving header in each layer. For example: First, you have to specify what will happen with the datagram "JAZAN UNIVERSITY" in the…
- In what ways does the Model-View-Controller (MVC) architecture contribute to the making of web apps generally? In what ways might the advantages of an MVC framework be put to good use?What is Hierarchical cGAs? Write Pseudo-code of H-cGA.Most real-world CS architectures have fewer layers than the OSI model. Digital computers cause this. Lower the level limit to doable. Should we worry about fewer layers?

