Sub CreatePDFForms () Dim PDFTemplate File, NewPDFName, Save PDFFolder, Name As String Dim Date Submitted As Date Dim CustRow, LastRow As Long With Sheetl LastRow= .Range("A9999").End (x1Up).Row 'Last Row PDFTemplateFile = .Range ("D10").Value Template File Name Save PDFFolder = .Range("D12").Value 'Save PDF Folder OpenURL "" & PDFTemplateFile & "", Show Maximized Application. Wait Now + 0.00006 Next End With End Sub
Sub CreatePDFForms () Dim PDFTemplate File, NewPDFName, Save PDFFolder, Name As String Dim Date Submitted As Date Dim CustRow, LastRow As Long With Sheetl LastRow= .Range("A9999").End (x1Up).Row 'Last Row PDFTemplateFile = .Range ("D10").Value Template File Name Save PDFFolder = .Range("D12").Value 'Save PDF Folder OpenURL "" & PDFTemplateFile & "", Show Maximized Application. Wait Now + 0.00006 Next End With End Sub
Chapter14: Files And Streams
Section: Chapter Questions
Problem 2CP: In Chapter 11, you created the most recent version of the MarshallsRevenue program, which prompts...
Related questions
Question
what's up??? can't figure this out
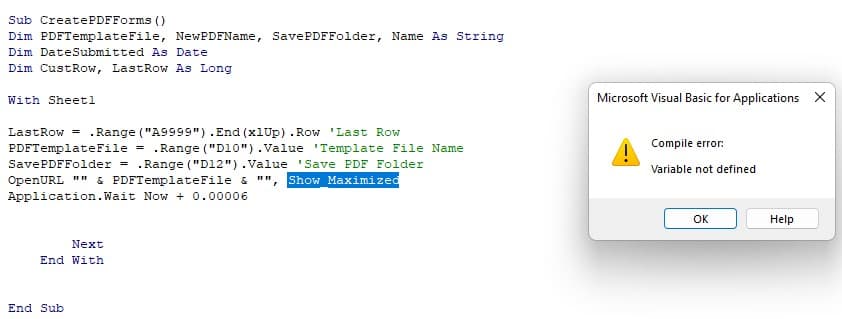
Transcribed Image Text:Sub CreatePDFForms ()
Dim PDFTemplate File, NewPDFName, Save PDFFolder, Name As String
Dim Date Submitted As Date
Dim CustRow, LastRow As Long
With Sheetl
LastRow= .Range("A9999").End (x1Up) .Row 'Last Row
PDFTemplate File = .Range("D10").Value Template File Name
SavePDFFolder = .Range("D12").Value 'Save PDF Folder
OpenURL "" & PDFTemplateFile &
Show Maximized
Application. Wait Now + 0.00006
Next
End With
End Sub
"1"
Microsoft Visual Basic for Applications X
Compile error:
Variable not defined
Ок
Help
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L