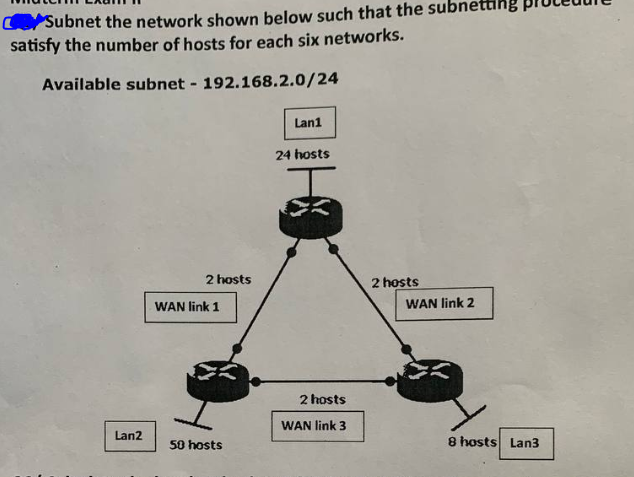
Subnet the network shown below such that the sub satisfy the number of hosts for each six networks. Available subnet - 192.168.2.0/24 Lan2 2 hosts WAN link 1 50 hosts Lan1 24 hosts 2 hosts WAN link 3 2 hosts WAN link 2 8 hosts Lan3
Q: When and how did it start to become what it is today?
A: Introduction: Cybersecurity, also known as information technology security, is the practice of…
Q: The need for, and implementation of, error and flow control in synchronous time-division…
A: Introduction:- Multiplexing :- In telecommunication and computer networking , multiplexing is a…
Q: Explain why, from the point of view of a developer, deep access is preferable than shallow access,…
A: In this question we need to explain why developers prefer deep access over shallow access.
Q: When working in a group, how do you keep a shared printer safe?
A: Please find the detailed answer in the following steps.
Q: 1. Print All Elements of the Array by CodeChum Admin Create an array by asking the user to input the…
A: Algorithm : 1. Start2. Create a Scanner for user input3. Prompt the user for the size of the array4.…
Q: what is a VM, and how does it work? I can't think of a good reason to utilise a virtual machine. Why…
A: Virtual machine: It is an operating system (OS) or application environment that is installed on…
Q: You are given an array of integers (both positive and negative). Find the contiguous sequence with…
A: Given data: an array of integers (both positive and negative). Find the contiguous sequence with…
Q: When we say "system security," what do we really mean?
A: We need to discuss system security.
Q: Please send me answer of this code from the given output ,just i have written the code but some…
A: Please refer to the following steps for the complete solution to the problem above.
Q: lease send me answer within 10 min!! I will rate you good for sure!! Please provide explanation!!…
A: To plot the sine function y(x) for values of x from -3π/2 to 3π/2, we can use a programming language…
Q: Determine what the sale price would be for each item if the Marketing team went off the rails and…
A: The solution is given in the below step
Q: How would you characterise the procedure of archiving and maintaining data?
A: Given: Describe in your own words how information systems may organise and store data.
Q: Think about the essential features that your operating system would have to include if you were to…
A: Any computer system's foundation is its operating system. The goal of an operating system should be…
Q: Information systems' social role and their potential to enhance the productivity of company…
A: Information system's RoleInformation system's Function in Business Process: Information systems…
Q: Some individuals who specialise in information technology believe that former computer criminals…
A: Introduction: As hackers get more skilled, protecting your digital assets and network equipment…
Q: The corporate data model at Mercy is meant to address the following question: how important is it…
A: Mercy must have a well defined organised data model in order to fulfill its data needs and goals.…
Q: How do you make sure that the firewall you're managing is as effective as possible? Explain
A: Define: A firewall is a sort of security programme that guards against unwanted access to a computer…
Q: 3. Check if Value Exists in Array by CodeChum Admin Write a program that creates an integer array by…
A: In this question we need to write a Java program to search for an element as specified in an array.
Q: Prove that r V (rp) is a tautology by applying the laws of propositional logic.
A: Answer: We need to prove the given expression if tautology. so we will see in the more details…
Q: In little more than 300 words, explain why networking is so crucial to the evolution of IT.
A: Why Networking is Crucial to the Evolution of IT Networking has become an essential part of IT. It…
Q: Compare and contrast the data and computational needs, accuracy requirements, hyperparameter…
A: Models ML and DL: AI systems that can self-learn based on an algorithm are referred to as ML.…
Q: When designing a security strategy for our system, why is it so important to first comprehend its…
A: In this question we need to explain the importance of comprehending current and prospective…
Q: 5. Why do hackers devote substantial amount of time to their trade?
A: Note : As per the bartleby policy we can answer single question at a time so i am answering the…
Q: Explain how networking has influenced the development of IT.
A: Describe the role that networking has had in the advancement of information technology. Information…
Q: Is there a method to simulate a login on a website?
A: There are several ways to assess a web application's login capabilities: Use a legitimate account…
Q: 16) For 1010.11₂, normalizing yields 1.01011. Identify the biased exponent of the given example. a.…
A: According the information given:- We have to choose the correct option to satisfy the statement.
Q: What comes to mind when you think of the data plane and the control plane of the network layer?
A: Control plane is the part of the network that controls how data packets are forwarded, meaning how…
Q: What other kinds of firewall management strategies are you familiar with? Explain.
A: Firewall management strategies refer to the methods and techniques used to control and secure…
Q: Consider the following scenario: Users of a popular social media site upload photos and videos of…
A: The answer for the above question is given in the following step for your reference
Q: Consider an input image of shape 512 X 512 X 3. You run this image in a convolutional layer of CNN…
A: We need to find the number of parameter of convolution layer for the given scenario.
Q: When developing a plan for security, it is necessary to keep track of three essential components.
A: Security refers to the protection of assets, such as information, systems, and infrastructure, from…
Q: In place of making their own text files to store information, why do most businesses use a DBMS?
A: INTRODUCTION: Database Management System: The Database Management System (DBMS) manages the…
Q: Write a javascript that asks the user to enter two numbers, obtains your name, student id and the…
A: This code uses HTML input elements to allow the user to enter their name, student ID, and two…
Q: Explain the output medium in a few words.
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: What are the most important parts of a data governance programme, and how are they connected to data…
A: Introduction: Manage Data Data governance underpins all data management programmes. Data warehouses,…
Q: Were each of the five data segments supplied within a timeframe that was considered acceptable?
A: Data: Data in computer science is information that is stored and organized in a specific…
Q: Information system experts in various organisations help to simplify and coordinate the performance…
A: The answer is given in the below step
Q: Active hardware metering in the EPIC approach provides safety for computer systems at the design…
A: EPIC signals the end of integrated circuit piracy. There are several approaches that may be applied…
Q: aluate how Governance and Management stack up against one another in the context of IS auditing
A: Governance and management play distinct but complementary roles in the context of Information…
Q: Data movement between sections of a website must be clearly shown.
A: Introduction: The elements of a Web application that will be described include the following:…
Q: When and how did it start to become what it is today?
A: Introduction: Protecting computer systems and networks from unauthorised access to or disclosure of…
Q: Talk about some of the difficulties of using international computer networks.
A: Introduction : International computer networks refer to the interconnected systems of computers,…
Q: 1. Implement insert() in tree.cpp and show the results of inserting 3, 2, 5, 6, 10, 4, 7, 8, 11, 15,…
A: Algorithm: START Initialize an array arr[] of size n. Create a Node class to store the data of…
Q: Describe the variations in UNIX/Linux and Windows' implementations of the concept of least…
A: The next step contains the response. Explanation The permission of computer resources that may only…
Q: Curious minds want to learn more about how to hack into a computer.
A: Authentication It authenticates identify to provide access to the system. Verification is necessary…
Q: Is there anything a centralised database could provide Mercy? After making such a major jump into…
A: Answer: Mercy Hospital, a St. Louis Catholic health institution, uses big data to enhance…
Q: 2. Print Multidimensional Array Elements in Reverse Order by CodeChum Admin Ask the user to input…
A: Introduction Java Programming: Java is a general-purpose, object-oriented programming language…
Q: is there a reason why false memory should be implanted
A: In reality, memories are not encoded and preserved through a single location, but rather in networks…
Q: How exactly should a corporation store and organise its passwords?
A: INTRODUCTION The answer is in the following step. The query is about how corporations manage…
Q: A Risk Management Framework (RMF): a. is only needed for big projects b.can also be applied to…
A: The correct answer is c and e. C) A Risk Management Framework (RME) is designed to manage software…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Transcribed Image Text 2. You are required to design IP addressing scheme for the Pantai Siring's branch for all floors using VLSM subnetting. You may use any private IP address class (10.0.0.0 to 10.255.255.255, 172.16.0.0 to 172.31.255.255 or 192.168.0.0 to 192.168.255.255). User group are as follows: a. Ground Floor- Administrator – 10 hosts b. 1* Floor - Lecturer – (Based on the last 2 digits of your Matric Number) For Example: B031910402 – 2 hosts only c. 2nd Floor - Student – 250 hosts d. 3rd Floor - Management – 80 hosts Explain in steps the calculations of your IP addressing scheme.Protocols at the Transport Layer's Core Both TCP and UDP are known by their respective acronyms. Justify the decision to implement TCP rather than UDP in an application. Please provide two (2) separate instances.Please help with as many of the following concepts and terms in regards to operating systems and networking: Socket Stream Client/Server Model Open end-to-end protocol for email POP3 vs IMAP FTP protocol DSN protocol Multiplexer vs Demultiplexer
- USING JAVA (Java Socket /TCP Programming) Create a chat/messaging application that has the following functionalities/features: Each user must log in to the system before he/she can perform actions/tasks. (passwords and usernames are stored in an XML file) Users must be allowed to send a broadcast message to all other users that are logged in. Any user must be allowed to send private messages to any of the established users.Both the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP) are transport layer fundamental protocols. Please provide an explanation for why an application would be built to use TCP rather than UDP. Please submit two (2) further examples.Q2-A) Using the Class C network 200.18.55.0, subnet the network so that you will have 8 usable subnets and at least 14 hosts in each subnet. List the subnet address and the broadcast address for each of the subnets, as well as the usable host range available in the subnet. 1. Number of bits borrowed for the subnet. 2. Number of bits for hosts 3. Subnet Mask 4. Number usable hosts per subnet Subnet Number Subnet Address Broadcast Address Usable Host Range 1 2 3 4 5 6
- Subnetting.The Thulani Productions Company has been allocated the 172.30.32.0/20 block by one of the Internetservice providers. As the network administrator of the company, you are required to allocate validsubnets to the three office branches: Midrrand branch 450 users Centurion branch 100 users Brooklyn branch 200 users Use VLSM subnetting to accommodate all users for all mentioned office branches. For eachnetwork/subnet assigned to each office branch (group of users), specify the subnet mask,broadcast address and the valid host address range using the format below: Branch NameNumber of host bits neededSubnetSubnet mask (dot notation)Range of valid hostsBroadcast addressYou have been allocated a class A network address of 28.0.0.0. Create at least 20 networks and each network will support a maximum of 160 hosts using the subnet mask 255.255.0.0Assume a client is connected to the server and has already received an HTML webpage. It reads the webpage, and it now needs to get 3 new files, File A is 5 MB file B is 1 MB and file C is 1 KB. The client requests the files in the order A B C. The link has an RTT (round trip time) of 0.5 seconds and a bandwidth of 8 Mb/s(Megabits per second) (or 1 Megabyte per second). The client can reuse the open connection if the protocol allows it to. For all parts of this problem ignore header sizes, and start the timer when the client sends How long does it take to get file C under HTTP 0? How long does it take to get file C under HTTP 1 (assume the browser does not support pipeling)? How long does it take to get file C under HTTP 2 assuming a frame size of 1 KB and no server push? What event would make HTTP 3 faster than HTTP 2 for this use case (ignore TLS)?
- Obtain the HTTP/1.1 specification (RFC 2616). Answer the following questions: a. Explain the mechanism used for signaling between the client and server to indicate that a persistent connection is being closed. Can the client, the server, or both signal the close of a connection? b. What encryption services are provided by HTTP? c. Can a client open three or more simultaneous connections with a given server? d. Either a server or a client may close a transport connection between them if either one detects the connection has been idle for some time. Is it possible that one side starts closing a connection while the other side is transmitting data via this connection? Explain.Subnets used: For the LAN addresses, you must use the classful network space 192.168.13.0. Use the VLSM design guidelines to subnet that classful network between R1, R2, and R3 based on the following requirements: R1 needs to support 29 hosts R2 needs to support 56 hosts R3 needs to support 11 hostsQ6: The web server in the below diagram cannot response to all requests come from different users in the network that caused delay in display the pages to the users, as network administrator suggest as solutions for the issues.

