sum = 0; for (int i = 1; i< n; i = sum++ || 2*i)
Q: Convert the numbers represented in base 2 to base 10: a) 101101 b) 110.011 c) 0.01101
A: Your answer is given below with calculation.
Q: Using the following information, make a Python dictionary called "Contacts" that can print out all…
A: ALGORITHM:- 1. Create the dictionary in python. 2. Store values in the created dictionary. 3. Print…
Q: What will the value of eax be after this sequence? mov eax, 10 push eax dec [esp] inc eax pop eax
A: mov eax,10 It assigns 10 to eax push eax It puts eax to stack dec [esp] esp points to top of…
Q: What does the central processing unit (CPU) signify and how does it work? Describe your viewpoint!
A: C.P.U:- CPU refers to the central processing unit or operating system. The brain of the computer…
Q: For each of the following function, indicate the class Q(n) the function belongs (use the simplest…
A: We need to indicate the class θ(n) of the given function.
Q: Suppose you are sitting in a restaurant and see a waiter cleaning tables. As a robotics student, you…
A: The sample output should be 120 seconds. Here is the code of this program. Code:…
Q: What are the advantages and disadvantages of using a probabilistic model for information retrieval?
A: PROBABILISTIC MODELS IN INFORMATION RETRIEVAL DEFINITION: In order to rate the matched documents in…
Q: A computer is an electrical device that can store, retrieve, and analyse both qualitative and…
A: Explanation: An electrical device used to manage data or information is a computer. Data may be…
Q: What does it mean to adhere to a naming convention?
A: Introduction: A naming convention, which is used in programming, is a set of rules for selecting the…
Q: Why can a programme running on a single server or a cluster of clustered servers achieve this but…
A: Introduction: In a cloud-native architectural approach known as microservices, a single application…
Q: modified code didn't work
A: Please find the answer below :
Q: A. Exactly what does an antiviral regimen entail? B. As a user, you may have run upon…
A: Antivirus: An antivirus is a piece of software, or group of applications, created expressly to find,…
Q: What will the value of eax be after this sequence? O 8 09 O 10 mov eax, 10 push eax dec [esp] inc…
A: Answer: 10
Q: Contact a local multimedia development Ask them what kinds of products they develop and whether they…
A: 1)Sony Play Station 5 2)Gaming console 3)Many tools, such as programming languages and hardware…
Q: If the computer has 32 kilobytes of memory and the storage location is the largest word (8 bytes),…
A: Introduction: A preliminary look at the archival repositoryShelf locations are components of a…
Q: Write a Java program to take nth number from the user. So your code have to print the Fibonacci…
A: Java:- Java is an object-oriented language as its concept is based on OOPS, it also supports…
Q: What part does AI play in the design of databases? What benefits and drawbacks come with integrating…
A: Introduction: This explanation focuses on using a purpose-built database to expedite ML model…
Q: Google just launched a new office in Pakistan. There is a job opening there for you. You were…
A: The above question is solved in step 2 :-
Q: In order to help identify the source or causes of this issue, how would you classify data based on…
A: stratification: Stratification involves arranging data, people, and things into tiers. It combines…
Q: What advantages does this file system have over a sequential one?
A: All the advantage of sequential file system over file system is below:
Q: What distinguishes some Windows modes from others that don't turn the system off?
A: Introduction A tool called Installer Windows Module is utilized to automatically check for updates…
Q: mputer is a piece of technology with a lot of parts but no ene
A: Introduction: A computer is an electronic device that is controlled by programmes stored in its own…
Q: Write a recursive method in java public static long numPaths(int r, int c) which can solve the…
A: The approach of this problem is right. The recursive call to move one column up then one row is also…
Q: Do you know that a computer is a piece of technology with a lot of parts but no energy needed to run…
A: Computer: A computer is an electrical device with the capacity to store, retrieve, and process…
Q: What part does AI play in the design of databases? What benefits and drawbacks come with integrating…
A: Introduction: The more practical notion and focus of this explanation is using a purpose-built…
Q: What software and hardware resources do library management systems have at their disposal?
A: Software and hardware resources library management System have at disposal
Q: In this problem, we wish to design and build components of an assessment management system using…
A: import ballerina/io; import ballerina/grpc as grpc; ReposityOfFunctionsClient ep = check new…
Q: 3-) Find a,b,c a) 2.5 GB in MB? b) 32 x 2 10 bits in KB? c) 3.5 MB in bits?
A: Answer and explanation is attached in step 2
Q: What does the central processing unit (CPU) signify and how does it work? Describe your viewpoint!
A: CPU (Central Processing Unit): The component that handles the majority of the processing inside a…
Q: Live backups of physical hard drives can be produced by setting up a RAID array, although doing so…
A: Answer is in next step.
Q: For each of the following function, indicate the class Q(n) the function belongs (use the simplest…
A: We need to indicate the class θ(n) of the given function.
Q: What are the two most frequently used file types? Do these two types of files vary in any way, or…
A: Introduction: On a computer, a file is a container that houses data, information, or commands…
Q: Use the signed magnitude convention to convert the following numbers in base 10 to base 2 a) 7.5 b)…
A: We need to convert the given base 10 numbers to signed magnitude base 2 notation.
Q: .Write a Java program to print an American flag on the screen. Expected Output * |||||| |||| !!!!…
A: Introduction: A section of the program is repeatedly iterated using the Java for loop. Use of a for…
Q: What distinguishes text formatting from other types of formatting text?
A: Texting formatting, paragraph formatting, etc are cool features of HTML, CSS, word to creative good…
Q: on JAVA language Define a class named Wall. The class should have two private double…
A: As per the requirement program is developed. Algorithm: Step 1: Define the required variables Step…
Q: What's going on? In [ ]: x = np. linspace(0, 1, 3) #y = 2*x + 1: y = x y = 2 y += 1 print(y) # Z =…
A: The complete commented python program is below:
Q: Can you explain why, in certain instances, automated transactions utilizing credit card numbers may…
A: Given: Due to the widespread use of internet-based banking and shopping, electronic payment methods…
Q: What is the Cybercrime Conceptual Framework? Do you have any sources to support your assertions?
A: Theorists of the internet agree that cyberspace enables near-instantaneous contact between…
Q: When should you utilise your inheritances if you have more than one?
A: If you have more than one child, you've probably considered whether you should leave the same amount…
Q: Describe the advantages of undergoing normalisation first, then denormalization.
A: Introduction: Normalization: In order to boost the database's performance, normalization is the act…
Q: Why would you want to utilise a reverse proxy server in your network setup and what precisely is…
A: Introduction: Server That Acts as a Reverse Proxy: It is in charge of managing any internet or…
Q: In 20 words or fewer, describe how you would create a heuristic function for the scenario you choose…
A: Introduction: Determine a heuristic function to apply to the issue. A heuristic function, which is…
Q: Nowadays, you may connect to the Internet using your cell phone or other mobile device, which is…
A: Some of the ways to prevent data loss or theft from a mobile device include: -Avoid using public…
Q: Which JavaScript code using the jQuery library should be placed in the blank to make the boldbright…
A: The fadeIn() method gradually changes the opacity, for selected elements, from hidden to visible. It…
Q: 10.List the advantages of multiprocessor systems.
A:
Q: What distinguishes centralised version control software from distributed version control software?…
A:
Q: wo languages: L1 = { x ∈{a,b}* | x starts with b} L2 = { x ∈ {a,b}* | x ends with a} Construct a…
A: I have solved below:
Q: Give an explanation of the connections between the Isa and Hasa classes. How would you go about…
A: Introduction: Therefore, since a specialised class "is" another class a, it also has the ISA link…
Q: Q3. Consider a system in which a process is allocated three frames in memory. Given the page…
A: optimal replacement:- number of hit=9hit ratio =920=45%number of page fault=11fault…
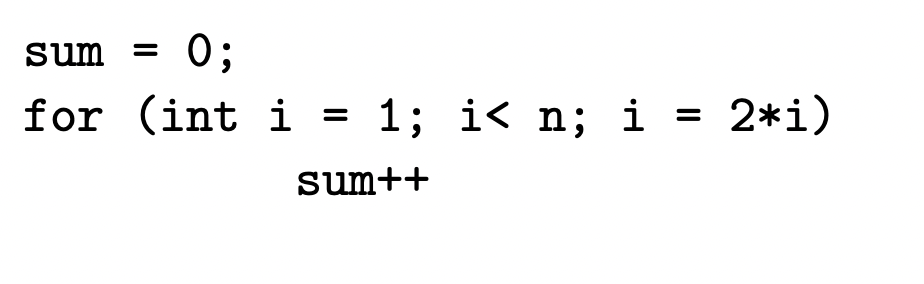
give a Θ(·) estimation of the running time as a function of n.
Step by step
Solved in 2 steps

give a Θ(·) estimation of the running time as a function of n.
- For function addOdd(n) write the missing recursive call. This function should return the sum of all postive odd numbers less than or equal to n. Examples: addOdd(1) -> 1addOdd(2) -> 1addOdd(3) -> 4addOdd(7) -> 16 public int addOdd(int n) { if (n <= 0) { return 0; } if (n % 2 != 0) { // Odd value return <<Missing a Recursive call>> } else { // Even value return addOdd(n - 1); }}Question#1: Let P and Q be integers and suppose F (P, Q) is recursively defined by: F(int P, int Q) if (P == 0) return Q else return F(P- 1, P + Q) Find and Trace F(8,1)Q // Write a program in C++ language that enters a number of integer numbers into a singular matrix whose size is renewed after asking the user about the number of numbers he wants to enter, then he collects these numbers and prints the result on the screen
- 1: |R|←|P| Reserve space for |P| = 13 values.2: x ← n3: for i ← 0 ...(|P| − 1) do4: c ← x div Pi Number of multiplicands Pi in x.5: Ri ← c6: x ← x − c · Pi7: end for8: return RA Java programmer could implement Algorithm by first modelling the primitivenumbers with the enumeration type RomanNumeral. Each enum constant (I, IV, ..., M) is declared with its decimal value, which can be accessed with the function getValue().Write a function that takes in an integer n and computes n!. Do this without recursion. In [ ]: deffactorial_iter(n):"""Takes in an integer n>0 and returns the product of all integers from 1 to n."""# YOUR CODE HEREraiseNotImplementedError() In [ ]: In [ ]: assert factorial_iter(6) == 720 assert factorial_iter(7) == 5040 assert factorial_iter(10) == 362880026 78.497 Bytes question. Write a recursive function that returns the sum of the digits of a given integer.Input format :Integer NOutput format :Sum of digits of NConstraints :0 <= N <= 10^9Sample Input 1 :12345Sample Output 1 :15Sample Input 2 :9Sample Output 2 :9 Solution:///////////// public class solution { public static int sumOfDigits(int input){ int sum; if(input<10){ return input; } sum = (input % 10) + sumOfDigits(input / 10); return sum; }}.
- Java Functions with 1D Array Write a Function that accepts two integers X and Y and prints the binary representation of the numbers starting from X to Y. Note: X would always be lesser than Y. Input 1. Integer X 2. Integer Y 3. Integer X 4. Integer Y Output: Enter X: 5 Enter Y: 10 101 110 111 1000 1001 1010Addition Rule Product Rule Log Exponent Rule Log Base Rule Transitivity In the following section, indicate what reference function (g(x)) we should use when attempting to prove that f(x) is O(g(x)). Use the rules and reference functions above to guide you. f(x)=n+log2n f(x)=n2+log n4 f(x)=n2∗n3 f(x)=n5/n2 f(x)=n∗(log n)∗n f(x)=n+n log n+log nExample: Enter an integer = 75 Smallest divisor is = 3
- In C++ whats the answer from below ? int size = 10; for ( int i = -1; i < size ; i++) { arr[size - i] = i; } This array: has 12 positions is out of bounds has 10 positions has 11 positions•rewrite calculateSum function as a recursive function. m(i) = m(i-1) + i/(i+1), where i >=1In java: Develop a function that accepts an array of integers and returns their average. Develop a function that accepts an array of integers and a threshold value from the user. The function returns how many values in the array are strictly greater than the cutoff. Using the functions written for #1, #3, and #4, find the number of values above average in two randomly generated arrays. Develop two functions:a. a function that returns the index of the maximum value in an array of integers passed by a caller, the caller prints the returned index and the value at that indexb. a function that returns the index of the alphabetically first value in an array of strings, the caller prints the returned index and the value at that inde Develop two functions:a. a function that swaps the alphabetically first value in an array of Strings with the first value in the array. Call this function twice on two different arrays of Strings; in the caller, use the function written for #2b to display…



