Suppose L = {w/w # 0^n 1^n for any ne N} is a language over the alphabet {0, 1}. Prove that L is context free by giving a PDA that accepts it. Examples: • E&L, 0000 € L, . 0011 L, • 111100 € L, • 01111 € L, • 1001€ L
Q: What is the purpose of system utilities and tools in managing and maintaining an operating system?
A: System utilities and tools play a role in the management and maintenance of an operating…
Q: Can you please do this problem step by step so I can follow along and understand this better and can…
A: Normalization can be defined in such a way that it is a database design technique used to…
Q: Discuss the principles and challenges of net neutrality and the potential impact on internet service…
A: Net neutrality is a concept, in the realm of computer science and internet technology.It revolves…
Q: Which of the following is equivalent to WHERE attribute NOT BETWEEN 100 AND 1000? a. WHERE…
A: BETWEEN is an operator in SQL (Structured Query Language) which return the output of whether an…
Q: What is the significance of IoT (Internet of Things) in the context of mobile devices, and how are…
A: In step 2, I have provided complete answer to the question........
Q: How has AI shaped by various information systems? How did certain parts of the world react to AI?
A: Artificial Intelligence (AI) has been shaped by various information systems through the integration…
Q: How does email communication work on the internet, including the role of email servers and clients?
A: Email communication on the internet involves the exchange of electronic messages between individuals…
Q: In the context of cloud computing, how does virtualization play a crucial role in resource…
A: Virtualization plays a role in cloud computing by easing resource allocation, scalability and…
Q: Discuss the importance of mobile device security. What are some common security threats for mobile…
A: In today’s era the security of devices is incredibly important since they have become an integral…
Q: Q2\ Write a java program for the following flowchart. START Base=2 Power =4 Product = Base Counter =…
A: initialize base and power.Take another variable product to store the result.initialize counter with…
Q: How do mobile applications (apps) work, and what are the main categories of mobile apps?
A: Mobile applications, often referred to as apps, have become an integral part of our daily lives.…
Q: What is RAID (Redundant Array of Independent Disks), and how does it provide redundancy and improved…
A: 1) Storage systems refer to the hardware and software components that collectively manage, organize,…
Q: Explore the concept of data backup and the various methods and devices used for data backup and…
A: Making copies or duplicates of digital information, such as files, databases, or entire systems, and…
Q: I need help with a SELECT statement that returns the cust_id and the total number of orders for each…
A: The objective of the question is to write a SQL SELECT statement that returns the customer ID…
Q: Discuss the concept of live migration in virtualized environments and its impact on system…
A: A crucial component of virtualized systems is live migration, which permits the transfer of an…
Q: How does virtual memory management work in modern operating systems, and what benefits does it…
A: Virtual memory management is an aspect of operating systems.It plays a role in perfecting memory…
Q: What are the main types of storage devices commonly used in modern computing, and how do they differ…
A: Modern computing relies on a variety of storage devices, each with different characteristics in…
Q: Case Study: Jack Doe is the Community Liaison Officer for 3D Media Comm. Ltd based in Perth, Western…
A: This case study is on Jack Doe, the Community Liaison Officer at 3D Media Communications Ltd in…
Q: What do the self-loops on state B accomplish? What purpose this serve in the context of this Turing…
A: The state diagram is missing the Reject state.After reading a Blank symbol in state B, we can go…
Q: Explain the concept of the OSI model and the seven layers. How do network protocols relate to these…
A: The OSI (Open Systems Interconnection) model is a conceptual framework that standardizes and…
Q: What is the purpose of the IP (Internet Protocol) in the network stack?
A: the layered architecture of computer networks is key to comprehending how data is transmitted and…
Q: Discuss the concept of mobile app permissions and why they are necessary for app functionality and…
A: 1) Mobile app permissions refer to the explicit authorization granted by a user to a mobile…
Q: Discuss the significance of HTTP, HTTPS, and their differences in web communication.
A: HTTP (Hypertext Transfer Protocol) and HTTPS (Hypertext Transfer Protocol Secure) are the…
Q: Explore the concept of multicast and anycast protocols. How are they used in modern network…
A: The multicast and anycast represent the most recent advances in modern network architecture aimed at…
Q: 1.2 Imagine you've been hired as an IT consultant for a small business that is expanding its…
A: To calculate the required subnet sizes for each department, we need to determine the number of…
Q: Define network protocols and their significance in data communication. How do they ensure reliable…
A: In the realm of modern data communication, the seamless exchange of information between devices is…
Q: Logistics and Cargo Distribution related to Create a mdp search tree and indicate all of the…
A: Creating a Markov Decision Process (MDP) for logistics and cargo distribution involves defining the…
Q: Discuss the role of RAID (Redundant Array of Independent Disks) in data storage and provide examples…
A: RAID, an acronym for Redundant Array of Independent Disks is a technology widely used in data…
Q: Using C# Programming Language Please display all code and steps for the following program. Store…
A: To create a C# Windows Forms application that implements the described functionality, follow these…
Q: Explain the basic structure and functioning of the Internet, including the role of ISPs and DNS.
A: The Internet, a global network of networks, has become an integral part of modern life, connecting…
Q: Describe the role of cloud storage in modern data management. What are the key cloud storage…
A: The above question that is describe the role of cloud storage in modern data management. What are…
Q: How does virtual memory management work in modern operating systems, and what are the advantages of…
A: 1) Virtual memory management is a memory management technique used by modern operating systems to…
Q: Describe the concept of network-attached storage (NAS) and storage area networks (SANs). How do they…
A: Network-Attached Storage (NAS) and Storage Area Networks (SAN) are two distinct storage…
Q: Describe the evolution of mobile device display technologies and the key features of OLED and AMOLED…
A: Over the years mobile device display technologies have undergone advancements to enhance users’…
Q: Explain the concept of "jailbreaking" in the context of mobile devices. What are the implications…
A: Electronic gadgets that are portable and meant to be used conveniently while on the go are called…
Q: You are sending the following sequence of data, what would be the checksum?…
A: Checksums are commonly used in data transmission and storage to ensure data integrity. When data is…
Q: Discuss the potential implications of quantum computing on Internet security and encryption.
A: Quantum computing represents a revolutionary approach to computation, leveraging the principles of…
Q: Discuss the role of hypervisors in virtualization technology. What are the different types of…
A: Without hypervisor, there is no way we can run more than one VM simultaneously on physically…
Q: Can you create an analogy comparing any process synchronization concept to the holiday of Halloween?…
A: A key idea in computer science and operating systems is process synchronization, which is…
Q: Explain the role of HTTP and HTTPS in web communication, including their differences and encryption…
A: HTTP and HTTPS play key roles in online communication. They govern data communication between a web…
Q: There are several stories of an idea taken on by a small group of people and transformed into a very…
A: The objective of the question is to describe an instance where a small group of people took an idea…
Q: Find the sum and product of each of these pairs of numbers. Express your answers as octal…
A: Octal numbers are base-8 numeral system which utilizes 8 distinct digits: 0, 1, 2, 3, 4, 5, 6, and…
Q: ("View all employees" function) If users click "View all employees" ( call program:…
A: 1-- Table structure for table 'employee' 2 3CREATE TABLE employee ( 4 employee_id INT NOT NULL, 5…
Q: What is the difference between union and union all operators?
A: The question is asking about the difference between two SQL operators: UNION and UNION ALL. These…
Q: Run the following program and make sure that you can explain the output, #include using namespace…
A:
Q: How can virtualization assist in optimizing hardware utilization and reducing power consumption in…
A: Virtualization is a used technology, in data centres that perfects hardware use and reduces power…
Q: Discuss the challenges and strategies involved in managing hybrid and multi-cloud environments for…
A: Cloud environments are scalable and flexible IT infrastructures that offer various services and…
Q: be the concept of mobile device virtualization and its potential applications in enter
A: The question asks for an explanation of mobile device virtualization and its potential uses within…
Q: Explain the concept of net neutrality and its importance in maintaining a free and open Internet.
A: Net neutrality is the principle that all internet traffic should be treated equally,without…
Q: Analyze the challenges and strategies in managing system resources in cloud computing environments.
A: Cloud computing environments provide a scalable and flexible solution for businesses, enabling them…
draw a pda on paper
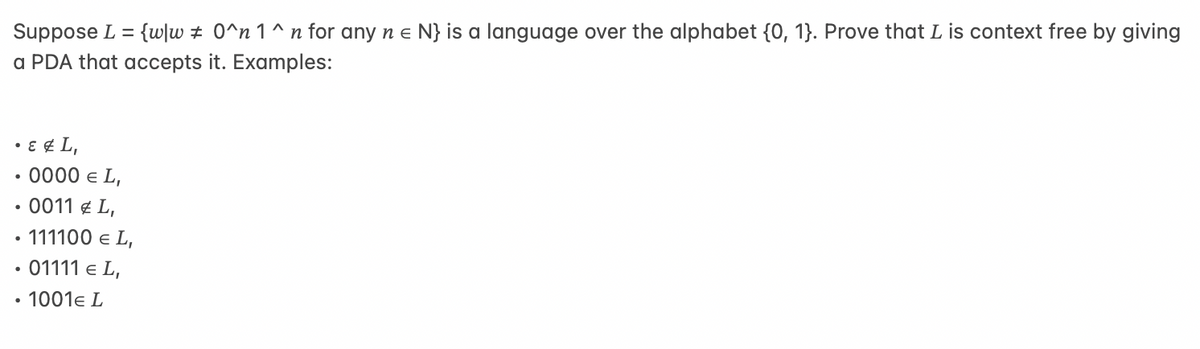
Step by step
Solved in 3 steps with 1 images

- Suppose L ⊆ Σ. Define end(L) = {w ∈ Σ∗ | ∃w′ ∈ Σ∗.(w′.w ∈ L)}. For example, if L = {1, 123} then end(L) = {1, 123, 23, 3, ε}. Show that if L is regular, then end(L) is regular. Hint: use ε-transitions.Suppose a Genetic Algorithm uses chromosomes of the form x=abcdef with a fixed length of six genes.Each gene can be any digit between 0 and 9 . Let the fitness of individual x be calculated as : f(x) =(a+b)-(c+d)-(e+f) And let the initial population consist of four individuals x1, ... ,x4 with the following chromosomes : x1 = 3 5 3 2 6 5, x2 = 9 8 0 1 2 2, x3 = 1 2 2 1 2 3, x4 = 7 9 2 3 1 1 1. 1.Evaluate the fitness of each individual, showing all your workings, and arrange them in order with the fittest first and the least fit last. 2. calculate the average fitness. 3. Perform the following crossover operations:a- Cross the fittest two individuals using one point crossover at the middle point.b- Cross the second and third fittest individuals using a two point crossover (points b and e). Suppose the new population consists of the four offspring individuals received by the crossover operations in the above question. Evaluate the fitness of the new population, showing all your…Given strings x = “Deep”, y = “Learning” and an empty string ε, the following are some operations undertaken on the strings: i) Lengths of x, y, ε are |x| = |“Deep”| = 4, |y| = |“Learning”| = 8 and |ε| = 0. ii) The concatenation operation applied over x, y and ε as follows yields the resulting strings and results: x + y = “DeepLearning” y + x = “LearningDeep” x + ε = “Deep” ε + y = “Learning” |x + y| = 12 | ε + y| = 8 iii) “Learn” is a prefix of string y, and “Deep” is a prefix of string x + y. iv) “earning” is a suffix of string y, and “Learning” is a suffix of string x + y. v) “earn” is a substring of string y. vi) x = y is false; x = x+ ε is true. vii) “Lenin” is a subsequence of string y. implement a program using given data
- Given strings x = “Deep”, y = “Learning” and an empty string ε, the following are some operations undertaken on the strings: i) Lengths of x, y, ε are |x| = |“Deep”| = 4, |y| = |“Learning”| = 8 and |ε| = 0. ii) The concatenation operation applied over x, y and ε as follows yields the resulting strings and results: x + y = “DeepLearning” y + x = “LearningDeep” x + ε = “Deep” ε + y = “Learning” |x + y| = 12 | ε + y| = 8 iii) “Learn” is a prefix of string y, and “Deep” is a prefix of string x + y. iv) “earning” is a suffix of string y, and “Learning” is a suffix of string x + y. v) “earn” is a substring of string y. vi) x = y is false; x = x+ ε is true. vii) “Lenin” is a subsequence of string y. make a program using given data:Let s = σ1. . . σk be a binary string of length k > 0. We say that a binary string w = w1 . . . wn contains s as a subsequence if there are k indices 1 ≤ i1 < i2, . . . < ik ≤ n such that wik = sr for every 1 ≤ r ≤ k. For example, if s = 11 then 10001, 1010 and 110 contain s as a subsequence whereas 000 and 1000 do not. Prove that the language of all binary strings containing a fixed binary string s of length k as a subsequence is a regular language.1. Consider the following dynamic programming implementation of the Knapsack problem: #include int find_max(int a, int b) { if(a > b) return a; return b; } int knapsack(int W, int *wt, int *val,int n) { int ans[n + 1][W + 1]; int itm,w; for(itm = 0; itm <= n; itm++) ans[itm][0] = 0; for(w = 0;w <= W; w++) ans[0][w] = 0; for(itm = 1; itm <= n; itm++) { for(w = 1; w <= W; w++) { if(wt[itm - 1] <= w) ans[itm][w] = ______________; else ans[itm][w] = ans[itm - 1][w]; } } return ans[n][W]; } int main() { int w[] = {10,20,30}, v[] = {60, 100, 120}, W = 50; int ans = knapsack(W, w, v, 3); printf("%d",ans); return 0; } Which of the following lines completes the above code? A. find_max(ans[itm – 1][w – wt[itm – 1]] + val[itm – 1], ans[itm – 1][w]) B. find_max(ans[itm – 1][w –…
- point p is on line l if and only if point l∗is on line p∗.1. Using the property above, prove the following properties:(a) If n points p1, ..., pnare on a common line l, then p∗1, p∗2, ..., p∗nintersect at a common point l∗.(b) If n lines l1, ..., lnintersect at a common point p, then l∗1, l∗2, ..., l∗nare on a common line p∗.2. If we have a line segment s connecting two points p1 and p2, describe a region s∗corresponding to thedual of s in terms of p∗1 and p∗2. (No rigorous proof is needed.)3. If a line l intersects the line segment s, prove that l∗is in the region s∗.Given a set of n positive integers, C = {c1,c2, ..., cn} and a positive integer K, is there a subset of C whose elements sum to K? A dynamic program for solving this problem uses a 2-dimensional Boolean table T, with n rows and k + 1 columns. T[i,j] 1≤ i ≤ n, 0 ≤ j ≤ K, is TRUE if and only if there is a subset of C = {c1,c2, ..., ci} whose elements sum to j. Which of the following is valid for 2 ≤ i ≤ n, ci ≤ j ≤ K? a) T[i, j] = ( T[i − 1, j] or T[i, j − ci]) b) T[i, j] = ( T[i − 1, j] and T[i, j − ci ]) c) T[i, j] = ( T[i − 1, j] or T[i − 1, j − ci ]) d) T[i, j] = ( T[i − 1, j] and T[i − 1, j − cj ]) In the above problem, which entry of the table T, if TRUE, implies that there is a subset whose elements sum to K? a) T[1, K + 1] b) T[n, K] c) T[n, 0] d) T[n, K + 1]Given a set of n positive integers, C = {c1,c2, ..., cn} and a positive integer K, is there a subset of C whose elements sum to K? A dynamic program for solving this problem uses a 2-dimensional Boolean table T, with n rows and k + 1 columns. T[i,j] 1≤ i ≤ n, 0 ≤ j ≤ K, is TRUE if and only if there is a subset of C = {c1,c2, ..., ci} whose elements sum to j. Which of the following is valid for 2 ≤ i ≤ n, ci ≤ j ≤ K? a) ?[?, ?] = ( ?[? − 1, ?] ?? ?[?, ? − ?? ]) b) ?[?, ?] = ( ?[? − 1, ?] ??? ?[?, ? − ?? ]) c) ?[?, ?] = ( ?[? − 1, ?] ?? ?[? − 1, ? − ?? ]) d) ?[?, ?] = ( ?[? − 1, ?] ??? ?[? − 1, ? − ?? ]) In the above problem, which entry of the table T, if TRUE, implies that there is a subset whose elements sum to K? a) ?[1, ? + 1] b) ?[?, ?] c) ?[?, 0] d) ?[?, ? + 1]
- Draw out a Turing machine that computes a mapping reduction from L1 ≤ m L2 where L1 = {w:w ∈ {a,b}* and |W| is even} and where L2 = {anbn:n ≥ 0}.For each language below, indicate whether the language is: 1) in P, 2) in NP but probably not in P, or 3) probably not in NP. Give a brief informal justification for your answer 1. L = { (M, w) | M is a Turing machine, w is a string and M should accept the input w}. 2. L = {[w,x] | w is list of cities with distance between them, x is a visiting order and x must be the shortest path that travels between all the cities visiting each one only once}. 3. L = {[M, w] | M is a context free language in Chomsky normal form, w is a string and w is accepted by the language M}.Problem Alice was given a number line containing every positive integer, x, where 1<=x<=n. She was also given m line segments, each having a left endpoint, l (1<=l<=n), a right endpoint, r (1<=r<=n), and an integer weight, w. Her task is to cover all numbers on the given number line using a subset of the line segments, such that the maximum weight among all the line segments in the chosen subset is minimal. In other words, let S=(l1,r1,w1),(l2,r2,w2),....,(lk,rk,wk), represent a set of k line segments chosen by Alice, max(w1,w2,...,wk) should be minimized. All numbers 1,2,....n should be covered by at least one of k the chosen line segments. It is okay for the chosen line segments to overlap. You program should output the minimized maximum weight in the chosen subset that covers all the numbers on the number line, or -1 if it is not possible to cover the number line. Input format The first line of the input contains an integer, n - denoting the range of numbers…











