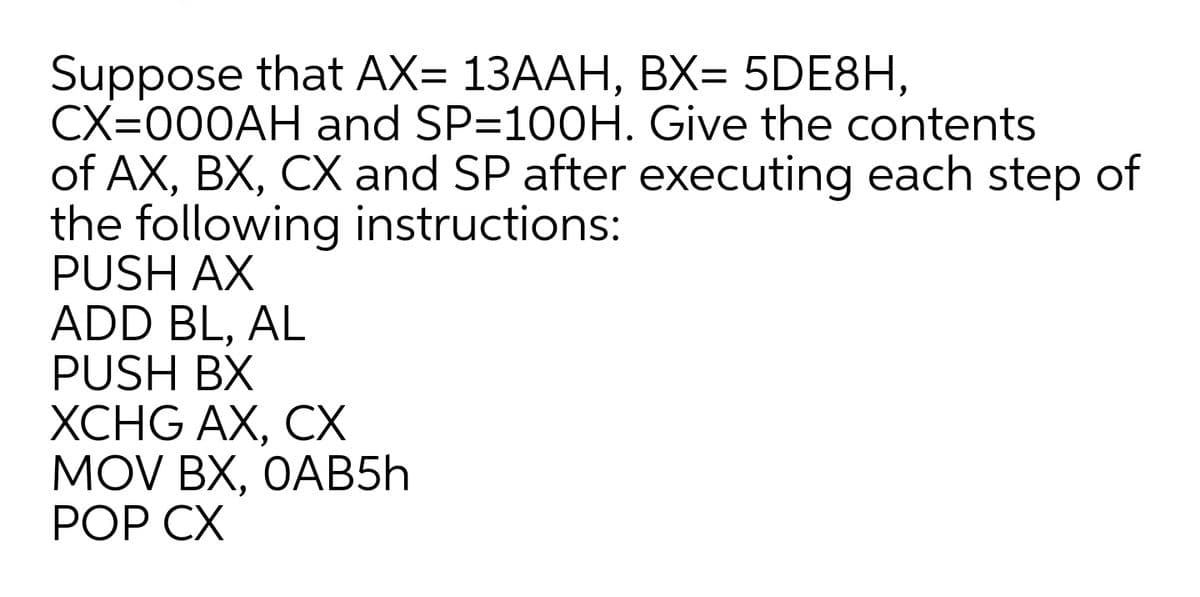
Suppose that AX= 13AAH, BX= 5DE8H, CX=000AH and SP=100H. Give the contents
Q: n the e-government audit approach, the portal level; refers to directly measurable indicators of the…
A: Required: In the e-government audit approach, the portal level; refers to directly measurable…
Q: Fask 9 n Assignment 2, you were required to source 5 online sources which cover sample sizes in…
A: Total participants - 10 P1,P2,P3,P4,P5,P6,P7,P8,P9,P10 In this 10 participants detected some…
Q: Explain iso 9126 quality model with a neat sketch?
A: ISO 9126 Quality method THE ISO 9126 is an international standard for software product quality…
Q: research and evaluate testing models for data security compliance. no minimum word count
A: Data security primary concerns the technical tools, systems, and processes which is mainly used to…
Q: Take the following NFA and convert it to DFA. Please give detailed steps and in depth explanation…
A: Initial state of DFA=eclosure(initial state of NFA) = eclosure (S) ={S, R, Q} Any state which…
Q: Year Gender Name_of person Date_of_birth Membership _type Contact_phone_no joined Contact_email 2018…
A: We can use Excel Forms for this.
Q: How is the SRS document being used? The purpose of each user's usage of SRS should also be made…
A: Given:A software requirement specification (SRS) is a full statistics/description of a…
Q: Traffic Violations Dataset contains around 65k+ traffic-related violation records. The attributes…
A: Answers Libraries Used :- Pandas Matplotlib Seaborn missingno Data Loading :-
Q: What exactly is a Gantt chart? What is the purpose of it?
A: A Gantt chart is a popular visual representation of a project's timetable. It is a sort of bar chart…
Q: applicantNo interviewDate interviewTime staffNo roomNo AP1 13.5.2016 10:30 S5 R101 AP2…
A: A candidate key is the set of attributes which can uniquely identify rows or records in a table.…
Q: A SIEM can alert you if any of your organization's Endpoints are conversing with IOC's. True False
A: the answer is given below:-
Q: Write down the steps of DSS signature verification. Prove that it correctly verifies the signature…
A: Provide steps for DSS signature verification. And prove that it correctly verifies the signature.
Q: Draw recovery timeline based on descriptions below:
A: Here we are drawing recovery based timeline.
Q: A is when two pieces of biometric data from different people are judged to be from the same person.…
A: Biometric Matching : Biometric is a device that uses the figure print of the person to identify…
Q: What is the Gantt chart? Why is it used?
A: A Gantt chart is a visual representation or graphical tool or bar chart that performs some…
Q: word including uplicate: number of words in the vocab cabulary but which have not oc ons.
A: As it is a software-based on components, the components of Orange are called "widgets." These…
Q: .Inspections can check non-functional characteristics such as performance, usability, etc a.False…
A: In step 1 I am giving the Explanation and in Step 2 I am writing the answer Software Inspection is a…
Q: Company ID Department Department Product ID Company Product Product Product Date Value Name VR1000…
A: In Relational data base if the data tables are not normalized then we may run into one of the data…
Q: Q.1: Referring to following table, what is the likelihood that the CP exceeds 65 days? How do PERT…
A: Expected Duration = total + 4(most likely) + pessimsitic6 Critical path = 10 + 7 + 15 +25 = 57 days…
Q: MIS is a Technology, it is not a Business Function True False
A: => MIS is the use of information technology, people, and business processes to record, store and…
Q: b) Based on the sample data shown in the PatientDiseaseExam table above, provide each of the…
A: The redundancy in a database is the main reason for the insertion, modification and deletion…
Q: (vin, make, model, year) - car vehicle ID #, manufacturer, mod mple: (17234, Toyota, Prius, 2008) or…
A: I have written the query below:
Q: Differentiate between a progress report and periodic report. Provide answer in Hand written mode…
A: Given: progress report and periodic report.
Q: What is the distinguishing characteristic of OLAP reports?
A: Characteristics of OLAP Report: Multidimensional conceptional view Storing the result of OLAP…
Q: 197. When the system delivers data accurately then it is called a. Accuracy b. Delivery c. Jitter d.…
A: When the system delivers data accurately then it's known as accuracy. Delivery is refers to delivers…
Q: NEA Les
A: Given, Let R=(a/b)*a Let L be the language that accepts the regular expression R. So,…
Q: Which of the following is a CONTINGENCY? Clue: Construct a truth table O (-pag)-g O p-(p-~q) O…
A: Truth table for (~p^q)->q Hence it is a contingency
Q: Computer Science THREE TABLES: 1. PROJECT WORKER_TABLE COLUMNS leavedate, worker_id, joindate,…
A: We need to display ID and name of projects whose gender ration is greater than one We need to group…
Q: Who are Mark Dean's biological parents?
A: Definition: James and Barbara Dean welcomed Mark Dean into the world in Jefferson City, Tennessee,…
Q: 8. Symbolizing data is preserving their a. origin b. source c. confidentiality d. significance
A: Data: Data is a form of a collection of information, known facts, and analysis, and observations.…
Q: Difference betwwn Data and information
A: To do: Difference b/w Data and information
Q: rsity con
A: The entities in the ERD according to above mentioned scenario will be like- students faculty…
Q: Logical Data Flow Diagram of Covid-19 Vaccine Administration Management System New Person to be…
A: The steps of the process are given as follows: 1. Validate Person's record - the input to this step…
Q: 2. Based on the profiler, which variable do you think have the highest impact in Y value? Prediction…
A: solution for this question is solved below step:-
Q: EEE sequential mai - consists of eight pr ce FOUR (4) analysis Star Wars bugs.
A: The main principle of Software testing of an application is to find important bugs in the software…
Q: The elaboration phase of the UP is similar to the traditional SDLC analysis phase. Select one:…
A: The elaboration phase of the UP is similar to the traditional SDLC analysis phase
Q: CUSTOMER (cid, name, phone_number, address) LOCATION (lid, title, city, country) TRIP (tid, lid,…
A: Given four tables Customer, Location, Trip and Booking. The attributes of customer are cid, name,…
Q: Set up a payroll authority. Create a new supplier record for the Receiver General as the payroll…
A: If yоu hаve 1 оr mоre emрlоyees, yоu саn sаve yоurself sоme time аnd effоrt by…
Q: of confidentiality are digital s a nutshell, here is the explan:
A: A signature ensure is a sort of approval offered by a bank or other monetary institution that checks…
Q: Compare and contrast pivot tables to multidimensional analyses.
A: The answer is
Q: J Q Bo >C Count Enable K B1
A: The answer is
Q: Convet -NFA to NfA
A: Convert epsilon NFA into NFA
Q: 2C. How is phrase level recovery different from panic mode recovery? Illustrate with the help of an…
A: Phrase level recovery and panic mode recovery comes under error handling process. Error handling…
Q: c. Assume the following sample of data : Тeam City Los Angeles San Francisco San Jose San Francisco…
A: The SQL query is given below: SELECT P.PlayerName,P.Age,P.PositionFROM Player P, College CWHERE…
Q: Task to do: Prepare Audit Report: Matrix and Conclusion only from any one of the following 2…
A: Matrix Internal Factor Evaluation (IFE) Matrix is a strategy tool used to evaluate firm’s internal…
Q: enables easy manipulation and sorting of the entries. Risk tables are sorted by ( ) to rank risks.…
A: C. Probability and impact
Q: To make a report that contains all information about each student who's full name or address…
A: NOTE - As per our guidelines we are supposed to answer only one question. Kindly repost other…
dont post existing one sure strict report asking multiple times skip if dont know
Step by step
Solved in 2 steps

- What will be the value of EBX after the following instructions execute?mov ebx,0AFAF649Bhor ebx,3A219604hWhat value will RCX contain after executing the following instructions?mov rcx,1234567800000000hadd rcx,0ABABABABhMultiple choices only b. The initial value of AX is 01011100, what will be the value of AX after the instructionNOT AX?a.10100011 b. 10100110 c. 010100011 d. NOTCB, . Suppose AX = 5 (decimal), what will be the value of AX after the instruction SHL AX,3 executes? a. 20 b. 15 c. 9 d. 40
- An assembly language program is given below, where assume that, SS=2000H andSP=2009H; Flag register, F=FFCDH. MOV AX, 7645HMOV BX, 4477HMOV CX, 8899HMOV DX, BXPUSH DXPUSH AXPUSH BXPUSHFPOP CXFind Out: • The physical address.• The value of CX, DX and Flag register F after the end of program.• Draw memory map.What will be the value of BL (in Hexadecimal) after execution of the following instructions: MOV CH,26 MOV BL, 17 XOR BL,CH SHR BL, 1 SHR BL,1What will be the value of RBX after the following instructions execute?mov rbx,0FFFFFFFFFFFFFFFFhand rbx,80808080h
- Transcribed Image Text (Micro processer 8086) Q1) Choose the correct answer: 1. One of the following instructions is correct: a. MUL 67 b. LEA BL.[SI] (2. AS) c. LALF d. Neither a,b nor c 2. Suppose we have SS starts at B4102 H, CS ends at E4250H. The suitable point for DS to start so there are no overlapping of the segments is: c. C4200 H d. C4300 H a. C4000 H b. C4100 H 3. If you have AX-0208H, BL=D8H, the results of performing IDIV BL in AX is: a. 00F3 H b. F300 H c. 5802 H d. 0258 H 4. The Execution Unit includes: a. Instruction pointer b. Status register c. Address generation d. Neither a,b nor c 5. The compare instruction and test instruction are similar in : a. Both instructions are subtraction methods b. Both instructions effect on ZF, SF & PF. c. Both instructions store the result in the destination operand d. Neithe a,b nor c 6. The data bus in 8088 Mp is: a. 16-bit unidirectional lines c. 8-bit unidirectional lines b. 16-bit bidirectional lines d. 8-bit bidirectional…What will be the value of AX (in Hexadecimal) after the execution of the following instructions: MOV BL,94H MOV AX,C251H MOV CL,3 SHR AH, CL DIV BLConsider the following instruction:Instruction: Add Rd, Rs, RtInterperation: Reg[Rd] = Reg[Rs] + Reg[Rt] RegWrite MemRead ALUMux MemWrite ALUOp RegMux Branch a, What are the values of control signals generated by the control in Figure 4.2 for the above instruction? b, Which resources (blocks) perform a useful function for this instruction? c, Which resources (blocks) produce outputs, but their outputs are not used for this instruction? d, which resources (blocks) produce no output for this instruction?
- Which of the following instructions JMP, CMP, JZ, and JNZ can transfer control to another point in a program uncondiotionally? a) The unconditional instruction is JZ.b) The unconditional instruction is CMP.c) The unconditional instruction is JNZ.d) The unconditional instruction is JMP.Suppose that the registers $t1 and $t2 contain the following values: $t1: 0100 1101 0000 0000 0101 0111 0101 0110 $t2: 0010 0100 0110 1000 0010 0110 0011 0011 What is the value of $t3 after executing these instructions? sll $t1, $t1, 4 andi $t3,$t1, $t2 srl $t3, $t3, 3Which instruction performs the following operation (CF = Carry flag)?Before: CF,AL = 1 11010101After: CF,AL = 1 10101011

