Suppose that you forgot your four-digit passcode to unlock your smartphone. You begin by trying 0-0-0-0 and intend to try every possible passcode until you unlock the phone. This method is an example of which of the following approaches? O approximation Ointractable problem brute force approach heuristic approach
Suppose that you forgot your four-digit passcode to unlock your smartphone. You begin by trying 0-0-0-0 and intend to try every possible passcode until you unlock the phone. This method is an example of which of the following approaches? O approximation Ointractable problem brute force approach heuristic approach
COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
1st Edition
ISBN:9780357392676
Author:FREUND, Steven
Publisher:FREUND, Steven
Chapter4: Financial Functions, Data Tables, And Amortization Schedules
Section: Chapter Questions
Problem 8AYK
Related questions
Question
Transcribed Image Text:X
+
arn.edgenuity.com/player/
ples Semester A
1 2 3 4 5
Mark this and return
O
►
ME
Save and Exit
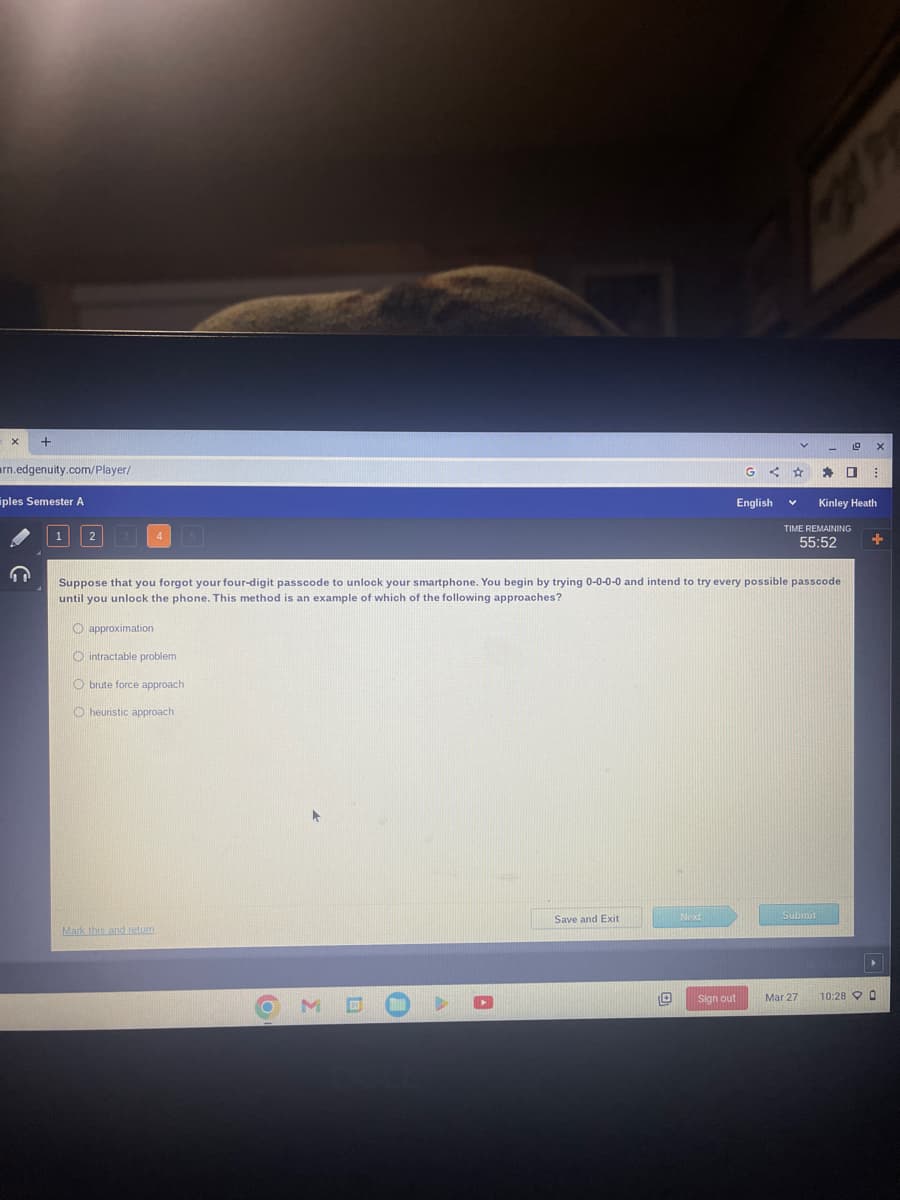
Suppose that you forgot your four-digit passcode to unlock your smartphone. You begin by trying 0-0-0-0 and intend to try every possible passcode
until you unlock the phone. This method is an example of which of the following approaches?
O approximation
Ointractable problem
O brute force approach
O heuristic approach
Next
G < ☆
English
Sign out
V
Submit
19
TIME REMAINING
55:52
Mar 27
* 0 B
X
Kinley Heath
+
10:28 0
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781305480537
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781305480537
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT