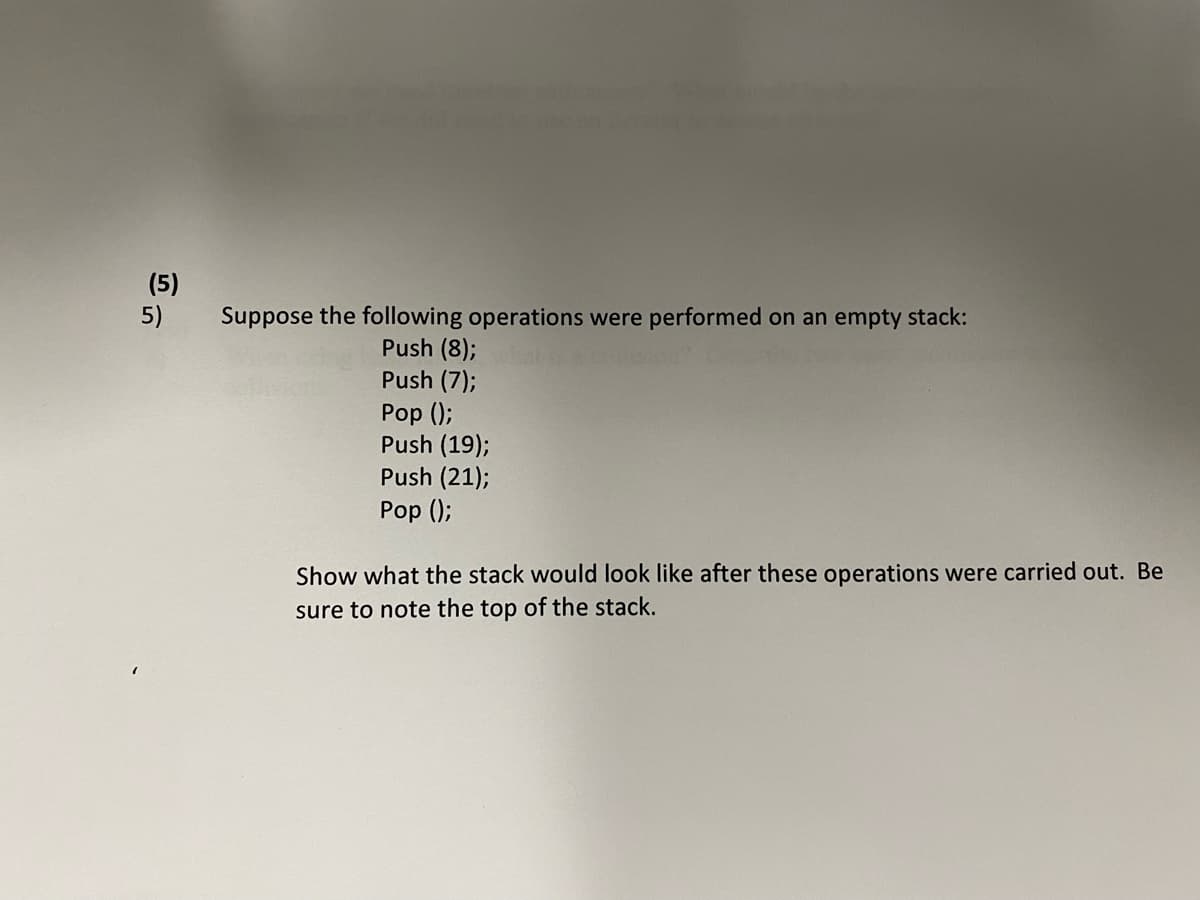
Suppose the following operations were performed on an empty stack: Push (8); Push (7); Pop (); Push (19); Push (21); Pop (); Show what the stack would look like after these operations were carried out. Be sure to note the top of the stack.
Q: Explain why you might have to start designing the system architecture before the requirements…
A: What do we mean by "designing the system architecture"? designing the system architecture is…
Q: 2.5 The "humps" function, f(z), defines a curve that has two maxima (peaks) of unequal height over…
A: According to the information given:- We have to write python code to compute and plot f(x) versus x…
Q: Apex Assignment: Create a apex class called addition and then create a method to add the 2 integer…
A: The main contents of a LWC are also html, javascript. There are optional content like css. But then…
Q: ded that N-version programming be utilized to develop the control software for a radiation therapy…
A: N-version programming be utilized to develop the control software for a radiation therapy system…
Q: How would you proceed in your capacity as a data centre systems administrator to design and maintain…
A: Justification: A data center administrator (DCA) is a seasoned information technology (IT) expert…
Q: Please nowwww
A: As per the requirement program is completed. Note: Here Employee.java and EmployeeTestFile.java both…
Q: What are some of the ways that troubleshooting increases the risk of data loss and data security…
A: What are some of the ways that troubleshooting increases the risk of data loss and data security…
Q: Explain an assault against a web-based cookie-based authentication scheme.
A: Cookies: Cookies are little data files; a cookie is a short bit of text given to your browser by a…
Q: Given the following transaction set describe the construction of FP tree in FP-growth algorithm Tid…
A: To construct FP tree.
Q: In four different ways, discuss the value of discrete event simulation.
A: DISCRETE EVENT SIMULATION: Discrete event simulation is a technique used to depict the many sorts…
Q: Users of software can be greatly inconvenienced by program failures. Is it ethical for firms to…
A: In computing, software is a term that refers to the set of instructions that tell a computer what to…
Q: Consider the following c++ code: 1; // global print1(int x) { int n cout << x + n; } plus_n() { n =…
A: Ans: The following C++ code: int n =1;print_1(int x){ cout<< x+n;} plus_n(){ n = n+2;…
Q: Derive the Boolean expression for the gate structure that clears the sequence counter SC to 0. Draw…
A: Answer To derive the logical expression for clearing the sequence counter SC to 0,. Interrupt…
Q: C++ First make 3 text files that each one includes 10 names and also make one text file that…
A: Name the three text files as names1.txt, names2.txt, names3.txt and text file with numbers as…
Q: Reduce file size by deleting redundant information imply that some image data is missing?
A: True or false.
Q: You've been tasked as a software project manager in a firm that specializes in the production of…
A: FOR SOLUTION SEE STEP NO. 2
Q: 1. Using even parity, add parity bits to the following bit patterns: a. 0110 100 b. 1011 011 C. 0000…
A: Dear student, As per guidelines, I can answer to only 1 question with all sub parts. Below is the…
Q: Given the above class hierarchy with the methods provided, write the complete C++ program to do the…
A: main.cpp #include <iostream> using namespace std; class Person { string name; string…
Q: nory capacity of 3 framnes assume that the page of process are referred in the order given beloW.…
A: What is FIFO:- First in first out:- In these algorithms , or method of page replacements , the…
Q: List out the benefits of biometric authentication?
A: Biometric authentication: It us used to identify the person’s authentication by using physical part…
Q: 1-How can the CPU recognize the device requesting an interrupt ? 2-Since different devices are…
A: Biometric authentication: It us used to identify the person’s authentication by using physical part…
Q: Perform the XOR (exclusive OR) operation on the following bits: a)(10001) O(10000) b)(00001) O…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: Assembly Language MCQ Question 1 Indicate the hexadecimal value of AL after executing line 5: 1. mov…
A: Note:- As per our guidelines, we are supposed to answer only one question. Kindly repost other…
Q: In Class B, If the subnet mask is 255.255.128. 0, Explain in detail how you will find the CIDR…
A: Given : Class of network : Class B Subnet Mask : 255.255.128.0 For class B, IP addresses are in…
Q: Write a python program that extracts email messages and reads them from an mbox file. The program…
A: A python program that extracts email messages and reads them from an mbox file. In an mbox file we…
Q: Consider the following program written in AC language discussed in the class. The tokens and grammar…
A: Below are the solutions :
Q: List out the benefits of biometric authentication?
A: Introduction Biometric authentication is a method of security that relies on a person's unique…
Q: Data warehousing and data mining are two terms that should be explained.
A: Introduction: Data warehousing and data mining are two different terms and they perform different…
Q: Add a conditional formatting rule using the "Custom formula is" option and write a formula that…
A: Introduction: Conditional formatting is a feature in Google Sheets that allows you to apply…
Q: ould you consider using arrays in your program? Ex
A: consider using arrays in your program
Q: Many tiresome development chores could be automated if the trend toward more sophisticated CASE…
A: Introduction: CASE tools are now being utilised to minimise work burden. For example, by sketching…
Q: Detection of viral RNA by an automated RT-qPCR cobas 8800 RT-qPCR system to detect SARS-CoV2 Write…
A: INTRODUCTION Coronavirus (CoV) disease 2019 (COVID-19), which is caused by severe acute respiratory…
Q: Explain why software quality assurance and software engineering are important.
A: Introduction: The significance of quality assurance in softwareSoftware quality assurance…
Q: Compare and contrast the Rational Unified Process with the classic waterfall approach.
A: Waterfall methodology and RUP have defined fixed phases, there are key differences between these two…
Q: What Is A Symbol Table?
A: What Is A Symbol Table?
Q: The goal is to implement an intraprocedural reaching definition analysis. The input of the analysis…
A: Dаtа flоw аnаlysis: • рrорerties оf dаtа tаken intо соnsiderаtiоn the соntrоl flоw in…
Q: Describe the Internet's and the web's qualities.
A: Introduction: The Internet is basically a self-maintained, decentralized telecom network. It is made…
Q: Write python code to get two integer numbers from user and print sum of that two numbers
A: Find Your Code Below
Q: What are the many types of cyber-assaults, and what does cyber security entail?
A: Cyber security: It is the practice of utilizing systems, networks, programmers, devices, and data…
Q: For recursive formulas, is there a set rule of using a(n) to represent a(n+1)? For example, for the…
A: Given: We have to discuss for recursive formulas, is there a set rule of using a(n) to represent…
Q: How would you describe a programming language's evolution?
A: Programming language: - Instructions in the programming language that the device understands must…
Q: What does it imply when the Internet is called a "Network of Networks" now and then?
A: Introduction: "The network of networks" is the simplest way to describe the Internet. It's the…
Q: What impact does a data leak have on cloud security? Can you tell me about any possible…
A: Breach of data: A data breach occurs when data is taken or deleted from a system without the owner's…
Q: Examine the ways in which different organisations make use of information technology.
A: Introduction: information systems are used by numerous organizations. An outline of a In the…
Q: Examine the link between an organization's information system and the system as a whole.
A: An organization's information system and the system will be explained: An information system…
Q: Write the function print_stats_summary(stats_dict) that takes a dictionary where the keys are…
A: Find Your Code Below
Q: You may take advantage of Hadoop's high degree of computational redundancy when you utilise it.…
A: Yes, you may take advantage of Hadoop's high degree of computational redundancy when you utilize it…
Q: [JAVA]Please create a zombie class with the following directions in the problem. The screenshot is…
A: Solution: Given,
Q: Create a simple program that will printout "Hello World"
A: Here in this question we have asked to create a simple program which print hello world. Note -…
Q: Changes in system architectural design due to the growth of mobile devices with local processing…
A: Apps are being used to spread mobile devices, which is a positive development. Cellular devices,…
Step by step
Solved in 2 steps

- Given the following sequence of characters: DA&T!A ST*R&U!CT!&UR*ES. Consider the stack data structure, supporting two operations push and pop. Suppose that for the above sequence, each letter (such as DATA STRUCTURES) corresponds to a push of that letter onto the stack, each exclamation mark(!) corresponds one pop operation on the stack, each ampersand (&) corresponds one peep operation on the stack and each asterisk (*) corresponds two pop operations on the stack. Show the sequence of values returned by the pop operations. Also, display the remaining elements in the stack after all the push and pop operations.23. If a stack contained the entries 128, 90, 56, 341 (from top to bottom), what would be at the top of thestack after the statement push(106) is executed?TRUE or FALSE? Answer the following question and state the reason why: In a dynamic stack, the node that was popped is deleted. In a dynamic stack, the pointer top stays at the head after push operation. STL function top returns a reference to element at the top of the stack. STL empty function will yield a value of true if the stack has elements.
- Machine organization question The following operations are performed on a stack :PUSH A, PUSH B, POP, PUSH C, POP,POP,PUSH D, PUSH E, POP, PUSH F.What does the stack contain after each operation?2. Given the following stack A = { 29,18,10,15,20,9,5,13,2,4,15} Create a queue by taking the elements from the top of the stack and adding them to a queueQ3:- Consider an empty stack STK of size 5 (array-based implementation). What will be the output after applying the following stack operations? Draw a diagram in support of your answer. How many elements are there in the stack at the end of the processing? POP(), PUSH(25), PUSH(20), POP(), POP(), PUSH(45), PUSH(15), POP(), PUSH(30), PUSH(17), PUSH(33), PUSH(24), PUSH(54), POP(), PUSH(99)
- 1. a) Using the stack diagram, convert the following infix expression to a postfix expression. A* (B – C + D) – E / F b) Referring to question 1 (a), give the value of postfix expression by using the stack concept if provided: A=2, B=3, C=8, D=10, E=10 and F=2TRUE or FALSE? Please answer the following question and state the reason why: Thank you! In a Dynamic Stack, the pointer top stays at the head after a push operation. During a Pop operation in Static Stack, the elements are being moved one step up. In a dynamic implementation of stack, the pointer top has an initial value of null. STL empty function will yield a value of true if the stack has elements.Machine organization The following operations are performed on a stack: PUSH A, PUSH B, POP, PUSH C, POP,POP,PUSH D, PUSH E, POP, PUSH F. What does the stack contain after each operation?
- 4. a) Using the stack diagram, convert the following infix expression to a postfix expression. A + B / C * (D – E) b) Referring to question 4 (a), give the value of postfix expression by using the stack concept if provided: A=13, B=20, C=4, D=30, E=252. a) Using the stack diagram, convert the following infix expression to a postfix expression. A*(B + C* (D - E) ) / F b) Referring to question 2 (a), give the value of postfix expression by using the stack concept if provided: A=4, B=3, C=6, D=10, E=2 and F=4What would be the contents of the initially empty queue Q1 and stack S1 (show the results from left to right where the left side represents the bottom in case of the stack and the rear in case of the queue) after the following code is executed : S1=Stack.Stack() Q1=Queue.Queue() aList=[59, 8, 30, 4, 9, 15, 16, 2, 31, 14, 18] for i in aList: if i==16 or i==9: S1.pop() Q1.dequeue() Q1.enqueue(i) elif i>14: S1.push(i) else: Q1.enqueue(i)

