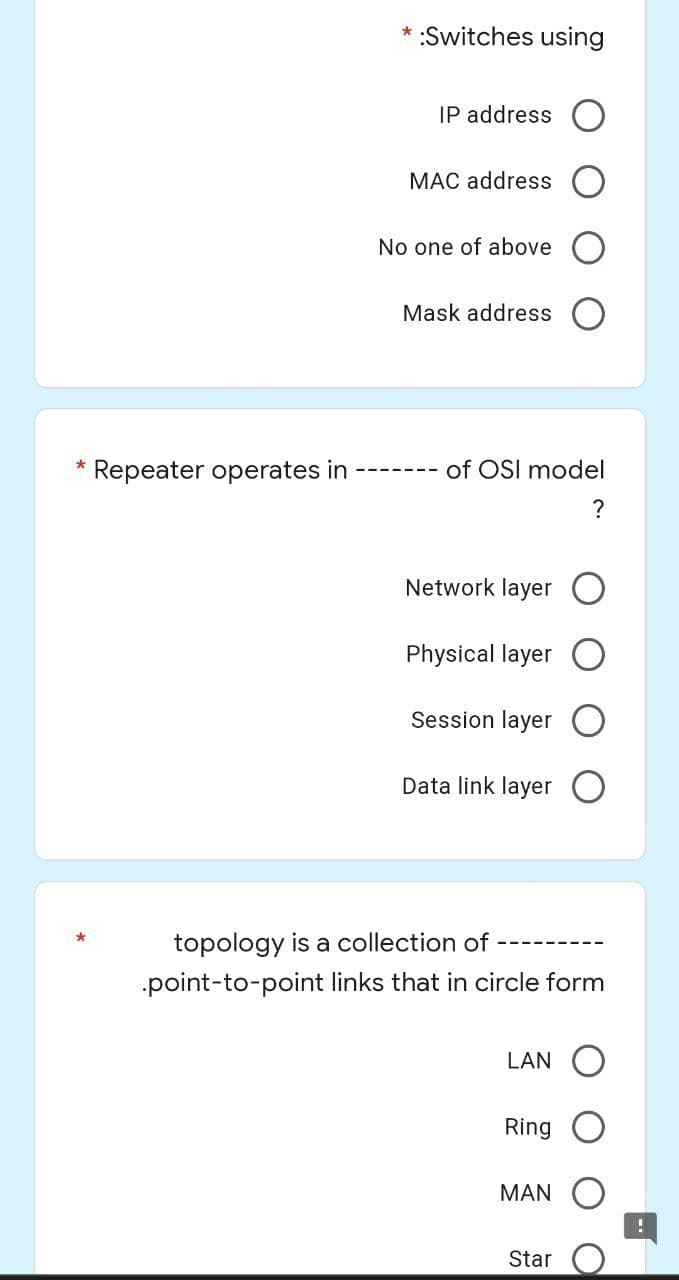
* :Switches using IP address MAC address No one of above Mask address * Repeater operates in ------- of OSI model ? Network layer Physical layer Session layer Data link layer topology is a collection of .point-to-point links that in circle form LAN Ring MAN
Q: 10. Inverted Number-Triangle by Julian Semblante Write a C program that will ask for a positive…
A: Answer: C Source Code: #include <stdio.h> int main() { for (int i = 5; i >= 1; i--) {…
Q: Distinguish and discuss the many ways in which the advancement of technology is lowering the bar for…
A: Technology: In addition to its beneficial qualities, technology has a negative impact on our life.…
Q: discuss the differences between hierarchial,network and relational databases
A: Hierarchical Data Model: The earliest sort of data model is the hierarchical data model. It was…
Q: What kind of design philosophy does the operating system's microkernel follow? How does this…
A: Introduction: Only when the CPU is in kernel mode may specific instructions be performed.Special…
Q: Discuss a situation in which you had difficulty interpreting numbers (Information). What are some…
A: What are the obstacles to comprehending the data? The framework The extent The proportions (in…
Q: The importance of big data technologies in law enforcement and the criminal justice system…
A: Intro Big Data Big data is an important part of every industry, as the world generates 2.5…
Q: Make a distinction between the benefits that education brings to an individual's life and those that…
A: Introduction: It is impossible for anyone in this world to ever be able to take away from you the…
Q: What are the four lessons learned from the creation of MINIX, and how do they apply to the…
A: Introduction: In relation to the creation of MINIX, we discovered the following four things:
Q: Principles of Software Engineering and Development Utilizing Quality Function Deployment allows for…
A: GIVEN: Concepts in Software Engineering Q. Quality Function Deployment (QFD) is a method for…
Q: Why are Strings in C# immutable?
A: Introduction: In point of fact, a string is nothing more than a succession of characters.
Q: Which kinds of network topologies are really doable to create, and which kinds do you think are the…
A: A Network Topology is the interconnection of computer systems or network devices. Physical and…
Q: In your own words, could you please clarify what happened during the data breach that was revealed…
A: Introduction: A data breach happens when an unauthorised person obtains access to and discloses…
Q: When troubleshooting a malfunctioning monitor, what would you do first? Check its connections to the…
A: Introduction: The computer power supply unit is one of the main pieces of hardware that has a direct…
Q: What kind of societal and ethical ramifications may technological advancements like robotics and…
A: Start: Artificial intelligence includes building computer systems to execute human-like activities.…
Q: Draw a DAG for the following expression: A = (A + B) * (- (B/D) + (D - E))
A: Answer is attached in Screenshot
Q: distinct types of computer software are
A: Software is a bunch of PC programs and related documentation and data.[1] This is rather than…
Q: It is important that this topic be covered, since it should include a discussion of the digital…
A: Overview: The issue necessitates an examination of information system challenges that affect…
Q: This topic focuses on the social and ethical repercussions that will be brought about by advances in…
A: Answer to the given question: It very well might be difficult to accept, however before the finish…
Q: Compare and contrast an environment for concurrent simulation with a testing facility that is both…
A: Introduction: Test data is information that is used only for the purpose of testing computer…
Q: Examining the similarities and differences between structured and unstructured data through the lens…
A: Answer:
Q: NoSQL is an abbreviation for "not just SQL," which refers to databases that do not employ relational…
A: Start: SQL, DocumentDB, Cassandra, Coachbase, HBase, Redis, and Neo4j are the most prevalent…
Q: Using your own words, describe the problems that can arise from engaging in plagiarism in technical…
A: Consequences: The act of passing off the work of another person as one's own is known as…
Q: A positive integer is entered through the keyboard, write a program to obtain the prime factors of…
A:
Q: Provide an explanation using your own words as to what went wrong with the data security breach that…
A: A cyber attack is referred to as a data violation when the attacker gains unauthorized access to…
Q: What information is stored in the table that manages entry-level interrupt vectors?
A: Table of interrupt vectors: An interrupt vector table, or IVT, is a data structure that links a list…
Q: A battery-powered power protection device that offers a few minutes of electricity. What is UPS's…
A: Introduction: Nickel-cadmium, lead-acid, and lithium-ion batteries are the principal types used in a…
Q: Consider the following typed relational schema describing books and borrowers in a library:…
A: Please upvote. I am providing you the correct answer below. please please please. So basically,…
Q: Despite this, I am still not quite certain that I get the concept of "two level logic." Is there any…
A: Introduction: A logic architecture with no more than two logic gates between the input and output is…
Q: First, you should define and describe the components of the core of the operating system that are…
A: Introduction: Components of the Operating System's Kernel that Make Up the Operating System The…
Q: Please submit three examples to illustrate how education-oriented robots may be employed. Specify…
A: The question has been answered in step2
Q: List 5 types of graphs and for each type, describe for which types of problems the type of graph…
A: A Graph is an data structure comprising of vertices and edges. the hypothesis related with diagram…
Q: With respect to the following nested loops, what is missing or wrong? int loopCount; while…
A: The loops are a programming construct that are utilized to run a bunch of code a number of times…
Q: Please describe how the three big data traits of volume, velocity, and diversity apply to the data…
A: Intro Please explain how volume, velocity, and diversity, the three properties of big data,…
Q: Defend the need for the work breakdown structure (WBS). Is it essential to manage a typical software…
A: INTRODUCTION: We must explain why the Work Breakdown Structure is vital in this section. To follow…
Q: Conduct a research on the CLASS in Java utilize the CLASS syntax. CLASS sample code in java,…
A: The program is written in Java, Check the program screenshot for the correct indentation. Please…
Q: When a host connects to a network using IPv4, it can communicate with other devices in one of three…
A: Introduction: A discussion of each mode of communication follows.
Q: What is the difference between network architecture and application architecture?
A: Introduction: The architecture of the network is broken down in great detail.
Q: Where can I upload music, photos, and movies to the internet?
A: Introduction: Many things all over the world have been altered as a result of the proliferation of…
Q: In terms of its managerial, technological, and organizational components, how would you define…
A: Information System: People, technology, and business process to achieve a business goal. It's a…
Q: Explain the difference between the two primary graph traversal algorithms and also state which data…
A: As i have read guidelines i can provide answer of only 1 part of questions in case of multiple…
Q: How would you define risk in terms of the underlying operating system? Is there anything more on…
A: Intro Beginning: A network operating a system is a computer operating system designed primarily…
Q: The components of the operating system and the tasks they perform may be summed up in a single…
A: Introduction: The kernel is loaded initially when an operating system is loaded and stays in memory…
Q: In what ways does the age of big data provide ethical challenges?
A: Intro Big Data: The primary problem in terms of ethical considerations at the supply chain level is…
Q: :How can you do a training requirements assessment for an e-learning system?
A: Intro Companies undertake need-gap analyses to determine the skills needed for competitive success,…
Q: Recognize the advantages that come with the use of information technology and put those advantages…
A: Introduction: Data innovation must be seen as a whole, including both the data that organisations…
Q: At least three network devices utilised in network infrastructure should be discussed.
A: Intro Network infrastructure services are the network components that transport the necessary…
Q: your opinion, which configurations of a network may be successfully executed, and which of those…
A: It is defined as the way a network is arranged, including the physical or logical description of how…
Q: When comparing the advanced features of Pfsense, Opnsense, and other commercial wireless router…
A: Inspection: Any DNS filtering business may help you with DNS filtering. It's more suitable to…
Q: How many subnets are created by the ?address 192.168.1.0255.255.255.248
A: here in the question ask for multiple choice question,
Q: If you had to enumerate all of the components that go into making up the kernel of a conventional…
A: Introduction Process management, memory management, hardware device drivers, filesystem drivers,…
Step by step
Solved in 2 steps

- The gRPC protocol does not have this: The gRPC protocol does not have this: a) Support for streams of requests or streams of responses. b) Ability to choose UDP or TCP for communication at the transport layer. c) Ability for the client to specify how long it's willing to wait for a response by providing a timeout. d) Use of HTTP/2 as an underlying protocol.q33- What is one of the characteristics is commonly associated with dynamic routing protocols? Select one: A. Requre special subnets masks B. Require less processing power than static routes require C. Require device configuration D. Consume some bandwidth to exchange routes informationTranscribed Image Text 2. You are required to design IP addressing scheme for the Pantai Siring's branch for all floors using VLSM subnetting. You may use any private IP address class (10.0.0.0 to 10.255.255.255, 172.16.0.0 to 172.31.255.255 or 192.168.0.0 to 192.168.255.255). User group are as follows: a. Ground Floor- Administrator – 10 hosts b. 1* Floor - Lecturer – (Based on the last 2 digits of your Matric Number) For Example: B031910402 – 2 hosts only c. 2nd Floor - Student – 250 hosts d. 3rd Floor - Management – 80 hosts Explain in steps the calculations of your IP addressing scheme.
- 6 Implement live video over udp from sender to viewer with opencv Please don't copy from internet. Thank you!Write down the OSI layers for each device as shown. Draw a NAT Table Entry at the Router for the Computer (A) (shown with a smiley face J) trying to reach the Web Server (listening at Port 80) as shown. You may use dynamic port numbers. Divide the LAN into 2 subnets and then re-draw it to show the subnets. Assume that you have a supply of switches as needed. A frame is sent from Computer A to Router R1, assume that it is using Ethernet. Draw the frame showing the Source and Destination MAC addresses, IP addresses, and port numbers.Consider the following topology. iMac2 wants to send a file to iMac3. iMac2 knows the destination IP of iMac3. Assuming that the fully configured network has just been switched on, explain the exact process that occurs to send the file from source to destination (only one way). Since many things happen along the way, you only need to address the following in your answer: 1. The appropriate names of the PDU during different stages 2. The ARP table population 3. The MAC table population 4. The usage and role of the IP Routing table (assume that the router already knows all routes to different networks) Hint: This question does not require explanation of the OSI Reference Model or TCP/IP stack. Your answer should be strictly structured in a step-by-step number-point format.
- You are assign to setup a real LAN network with 2 real servers PC with Centos. The nework IP address range selected from the network is 172.16.16.0/24.The two(2) servers to be setup is a FTP server (172.16.16.23) and a Web Server and DHCP Server setup in a VirtualBox environment in the 2nd server. WebServer(172.16.16.80) and DHCPServer(172.16.16.2).Show the instruction step by step to Setup the IP address of all the servers using the nmcli command.The usage of static routing has been met with opposition for several reasons, but which of the following is NOT one of them? O. Extra hardware or bandwidth is unnecessary. O.b. The routing tables are modest in size, need just occasional attention. Any alteration to the topology will, of course, have consequences for the setup. The path to the destination never deviates from that one.1- What is the error message that occurs when the manager sends Set_Request to a read-only object? Also, list out any three error messages in SNMP v1. 2- What kind of network management protocols are available? What information can these protocols provide? Explain it with example. 3- Encode 32-bit INTEGER 12 in TLV format? What is the broadband communication system and how broadband network support quality of service (Qos)?
- Lab – Routing Objective Learn and practice routing using Node and Express. Specification Create a web server that Accepts and processes request messages submitted from browser, and Generates and sends response messages back to browser for display. Your web server must be able to handle URL with hostname and port Request message URL: 0.0.1:3000 Response message: “SUCCESS!” URL with hostname, port and path echo Request message URL: 0.0.1:3000/echo Response message: “SUCCESS! echo” URL with hostname, port, path foxtrot and route parameter value kilo Request message URL: 0.0.1:3000/foxtrot/kilo Response message: “SUCCESS! Received kilo via foxtrot” where the value kilo must be retrieved via the route parameter Invalid/unexpected URL Request message URL: 0.0.1:3000/<any other value> Response message: “FAILED! Fix your URL.” Hostname 127.0.0.1 can be replaced by localhost. Port number 3000 can be replaced by any other port number that is from 1024 (2^11)…Use the following filter rule in Wireshark ip.flags.mf == 1 || (ip.flags.mf == 0 && ip.frag_offset > 0) Answer the following questions What is the size of the largest fragment you are able to find? What address is common to all the fragments of this size? 3. What is the size of the smallest fragment you are able to find?.Consider the following non-default subnet masks: (a) 255.255.248.0, (b) 255.128.0.0 . To which IP address class do they pertain?Write down the following in CIDR notation: (a) IP: 150.160.170.180, Subnet Mask:255.255.224.0; (b) IP: 75.80.85.90, Subnet Mask: 255.252.0.0 Three stations A, B, C and D are connected to a common Ethernet hub. Their IPaddresses and subnet mask are respectively: 200.100.50.67, 255.255.255.252;200.100.50.7, 255.255.255.248; 200.100.50.138, 255.255.255.240 and 200.100.50.1,255.255.255.254. Determine which among these stations can communicate with eachother. You need to show all detailed workings.

