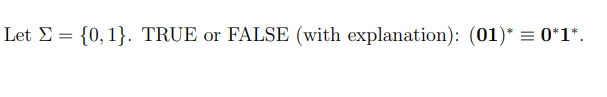
t E= {0,1}. TRUE or FALSE
Q: Why is it necessary to spend more time and effort to avoid excessively connected classes in Java…
A: Here's a look at some of OOP's top benefits: The dependency of distinct modules in an application is…
Q: In your own words, discuss the implications of plagiarism in technical writing and propose…
A: Introduction Plagiarism is when someone else's work is presented as your own. Ideas, opinions,…
Q: ng Files - Student Line Up ify the Student Line Up program described in Programming Challenge 1 es:…
A: Complete C++ code with explanation: #include <iostream> #include <fstream> #include…
Q: Justify the usage of business continuity methods in each situation. For one week, the local utility…
A: Incident: Incident means that some things happen or happen and they stop people from doing their…
Q: Computer science What would you do if you want to erase recently drawn straight segments?
A: Introduction: Hold Shift and click to put a point to eliminate the background pixels running beside…
Q: Prove by natural deduction: Show ∃x[p(x) ∧ q(x)] ⊧ ∃xp(x) ∧ ∃xq(x)
A: Prove by natural deduction: Show ∃x[p(x) ∧ q(x)] ⊧ ∃xp(x) ∧ ∃xq(x) .
Q: Given the following grammar in BNF: →=-X|Y|Z→ %|→?|-→ 0| a) Change the grammer Eules c e that Land K…
A: The answer is
Q: 11.11 LAB: Drawing a right side up triangle Write a recursive function called draw_triangle) that…
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOTS------------
Q: This is what your data warehouse project team is arguing when they debate whether to construct a…
A: Your answer is given below. Introduction :- A data warehouse is a database management system used…
Q: What is a field programmable gate array (FPGA) precisely? (FPGA)
A: Answer : Fixed Portable Lists (FPGA) is an integrated circuit that can be edited or rearranged…
Q: What distinguishes software engineering from other engineering disciplines?
A: Definition: Software engineering is the application of engineering principles to the design,…
Q: 4) Complete the Java code for the following for loop: for (int i= 1; i <= 6; i++){ // your code here…
A: Answer: Java Source Code: public class Main{ public static void main(String[] args) { int number…
Q: reachability in Prolog with and without labeling.
A: Reachability in Prolog: The possibility is explaining below:
Q: Are there any areas of software engineering that might make suitable research subjects?
A: - We need to talk about some parts of software engineering that would be good for research.
Q: Write a code to delete a node from a Binary search tree. The format of the function is void…
A: Start. Check if the tree is null or not. If not then repeat the function with next node if the key…
Q: When it comes to object-oriented programming, why is it required to put in more work and coding in…
A: Start: Object-Oriented Programming and Java The Java programming language is used to teach…
Q: Create succinct notes (no more than three lines) on the following subjects:…
A: WHERE DO MANCHESTER CODES COME FROM: Manchester codes are line codes in which the encoding of each…
Q: Why is a modem necessary to connect a phone line to a communication adapter?
A: Beginning: Phone USB. Turn on the USB telephone adapter. Connect your phone cord to the adapter.…
Q: The Local Region Network (LAN) connects computers and people in the same geographic area (LAN).…
A: LAN: The computer hardware in a confined region, such as an office or a house, is connected via a…
Q: Here is my code in Java: import java.util.Scanner; import java.util.HashMap; public class…
A: Your code had some mistakes due to which it was going into an infinite loop which resolved. Now this…
Q: Computer science Which type of cable can transmit up to 40 kilometers (25 miles)?
A: Introduction: Fiber optic cable: Coax cable, fiber optic cable, and twisted pair cable In…
Q: 5) Let's say you and your friend are trying to predict the outcome of a flip of a coin. In MATLAB,…
A: Answer
Q: Why do you need a modem when you connect a phone line to a communication adapter?
A: Connect phone line to computer: USB telephone Connect the USB telephone adapter to the telephone…
Q: An intelligent modem can dial, hang up, and answer incoming calls automatically. Who is accountable…
A: Modulator-demodulator equipment, or modems, are pieces of computer hardware that convert digital…
Q: Suppose you have a RISC machine with a 2.7 GHz clock (i.e., the clock ticks 2.7 billion times per…
A: The answer is
Q: Do you have any instances of the use of discrete event simulation?
A: The significance of modeling and analysis: To improve business, provide primary and secondary data.…
Q: What exactly do you mean when you say "excellent quality" software?What part of your quality idea…
A: Introduction: Quality software is described as software that is largely free of bugs or flaws, is…
Q: Modify it so that it write the contents of String[] into a file named fileLoop1.txt: package…
A: Given data, Modify it so that it writes the contents of String[] into a file named fileLoop1.txt:…
Q: Which of the following are the advantages and disadvantages of evaluation research?
A: Evaluation Investigations Evaluation analysis, which is sometimes referred to as programmed…
Q: What is a neural network and how does it operate?
A: Neural Network: Neural networks are computing systems which are interconnected nodes that work much…
Q: How do you alter the view in Visual Studio?
A: Changing forms: In Visual Studio, there are potentially two distinct methods for switching between…
Q: Computer science Explain how the primary key in the same relation is referenced.
A: Introduction: The primary key constraint requires that each row in the relational database…
Q: Which of the following relational set operator allows duplicate values in a table? Choose an answer…
A: In relational set operators, some of the operations perform union, except, intersect and update.…
Q: Explain the link between dependability and availability in the context of a computer network. It has…
A: Computer Networking: In a network, reliability means that the computer performs as intended.…
Q: NETWORKS OF COMPUTERS Multiple senders accessing media at the same time results in data collision;…
A: Data collision: A data collision occurs when two or more network domain devices or nodes send data…
Q: What happens if you hover your mouse cursor over one of the scaling handles on the box's border or…
A: Install the mouse driver again: You may repair the issue by reinstalling the cursor's driver if it…
Q: A timing diagram for Direct Memory Access (DMA) with clock synchronisation?
A: Memory on the computer: It is the location where task-related data and procedures are kept and…
Q: What function does defragmentation fulfil in general for linked files?
A: Defragmentation: Defragmentation is a file system maintenance operation that minimizes the degree…
Q: What happens when the mouse cursor is placed over the box's edge or corner in the case of a bounding…
A: Introduction: When the mouse cursor is over an edge,In the visual studio environment, the bounding…
Q: What is the difference between the physical and logical data models? What is the connection between…
A: Introduction: The logical model can be used to define business data and create business rules. The…
Q: It is up to the data warehousing project team to choose whether or not to prototype a data warehouse…
A: Introduction: Data warehousing project recommendationsThe purpose of a data warehouse is to gather…
Q: Question 3. Prove using the short north-east diagonals or any other mathematical method of your…
A: According to the information given:- We have to follow the instruction mentioned to prove the north…
Q: Discrete event simulation is critical for four main reasons.
A: Given: Explain why continuous event simulation is important.Continuous event simulation is important…
Q: Why do packet switching networks cause router queueing delays?
A: Introduction: There are four types of generally characterised delays in packet switching networks:…
Q: Discuss the differences between dialogue and interface design
A: The series of interactions between a user and a system is represented by a conversation. Distinguish…
Q: Sofia Vergaraa works for a major construction company and is interested in adding dirt and dust…
A: Correct answer: RFID code
Q: What essential ideas of software engineering are being overlooked?
A: Overview: When confronting a new issue, look at how it has been addressed earlier. Almost every new…
Q: Q3/ write an essay on the impact of social media.
A: Social media is a form of internet service that involves creating and sharing content on social…
Q: 12)Write nested for loops to produce the following output: 1 22 333 4444 55555
A: logic:- set space count=5 iterate from i=1 to i<=5 iterate from k=1 to k<=space…
Q: 11 ( ne the specified parity bits "X" and "Y" for the followin
A: 11 Answer specified parity bits "X" and "Y" for the following two 7-bit serial data values.…
Please show all work
Step by step
Solved in 2 steps with 1 images

- Suppose that p and q are statements so that p → q is false. Find the truth values of each of the following. (a) ~p → q TrueFalse (b) p ∨ q TrueFalse (c) q → p TrueFalseComputer Science In Erlang, how do i create this: % in1to10(n, outside_mode)% Given a number n, return true if n is in the range 1..10, inclusive. Unless "outsideMode" is true, in which case return true if the number is less or equal to 1, or greater or equal to 10. in1to10(_,_) -> true.Suppose you have the rule P :- Q;R. if Q is true and R is false, then P is___TrueFalse
- Write a program that finds the factorials of integers from 1 to 5. Write the results in the form of a table. Do the programming in C language. Thanks.A provable formula B is denoted by (you can write the answer in the paper and picture that answer upload it here).Consider the following statement:int* p, q;This statement could lead to what type of misinterpretation?
- Given code: int s=0; for ( int i=1; i<5; i++ ){ s = s + i ; } Which one is correct, after running the code. Group of answer choices s=1 s=15 s=10 s=5Take a sentence and as well as a word/character(s) and return True if the word/character(s) can be found in the sentence. Sample Parameter(s): "chicken", "z" Sample Return: False*Give correct Answer and get upvote *Else I will give downvoted

