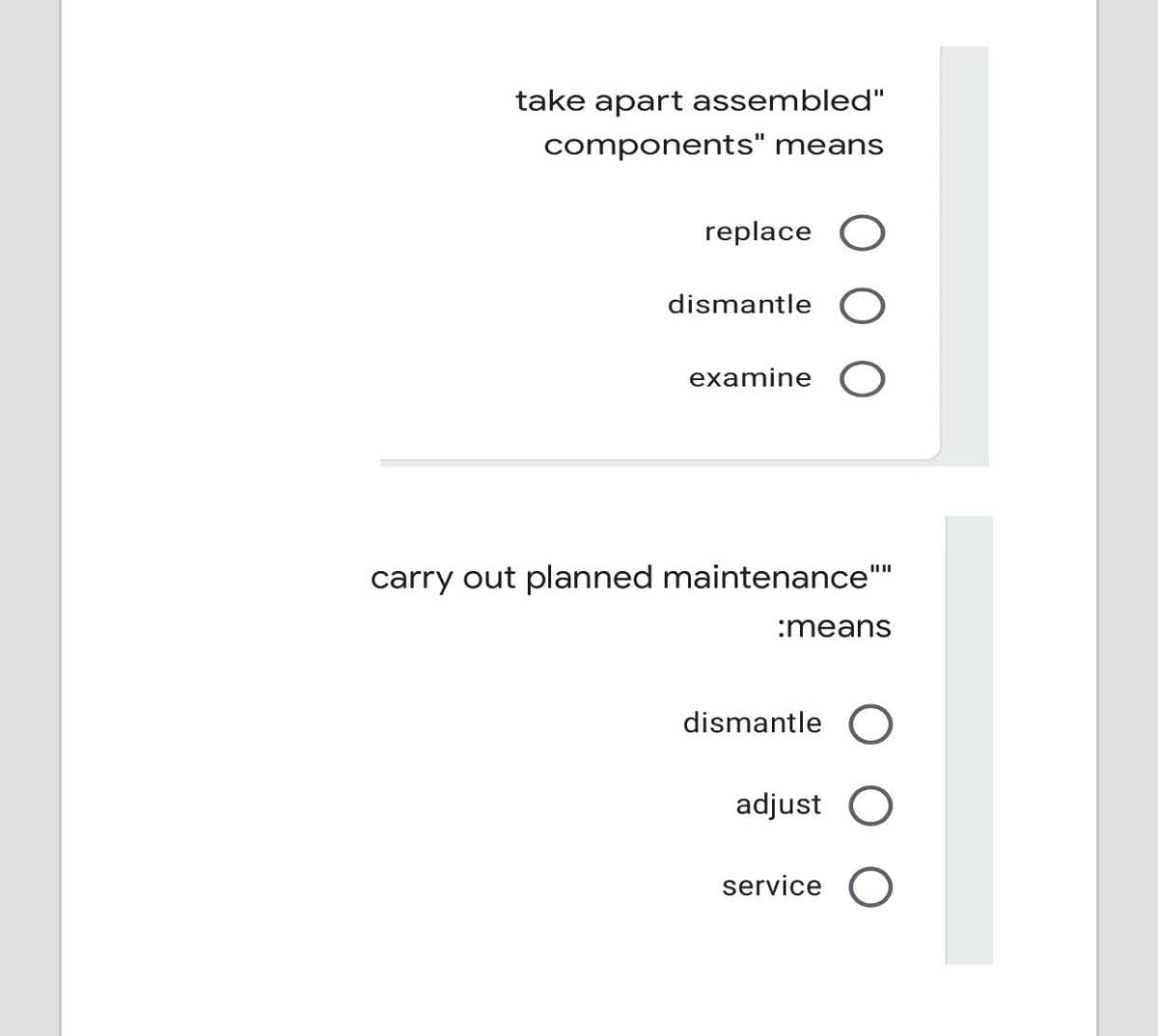
take apart assembled" components" means replace dismantle examine carry out planned maintenance" :means dismantle O adjust O service O
Q: What exactly is an ADT and how does it function? What exactly are the benefits of ADTs? When it…
A: Intro ADT will position the nerves properly throughout your home, so the whole area is covered in a…
Q: There are 3 algorithms to solve the same problem. Let n = problem size. Suppose that their runtime…
A:
Q: Why getting an education is so important to the overall health of our society This section of…
A: Given: The computer was a 20th-century innovation.Computer and information technology have altered…
Q: If you absolutely must, demonstrate that people and information systems are the driving drivers…
A: Introduction If you have to, show that people and information: systems are the driving drivers…
Q: What exactly is an interface? What is the difference between a programme block and a module block?
A: Intro To verify a design we write verification module and test bench to check that it meet…
Q: Computers have made their way into every aspect of our society, from the workings of our economy to…
A: Computer development: Computer development has had a significant influence on human existence, and…
Q: What is dynamic scoping, when and when is it utilized, and what are the performance costs associated…
A: With dynamic scooping, a worldwide identifier alludes to the identifier related with the latest…
Q: ered
A: Integrity is the practice of tell the truth and showing a consistent and uncompromising adherence to…
Q: What's the difference between a disaster recovery plan and a business continuity plan?
A: Introduction: The primary goal of developing a business continuity and disaster recovery strategy is…
Q: In terms of computers, what is the distinction between architecture and organisation?
A: Intro the distinction between architecture and organisation
Q: What is the purpose of numerous fact taBles, and how do they function
A: Introduction: Multiple-fact and multiple-grain searches can be performed on relational data sources…
Q: Explain why it's tough to come up with a cache replacement approach that works for all address…
A: Answer: Cache algorithms (also known as cache replacement algorithms or cache replacement policies)…
Q: What differentiates each network generation, as well as its benefits and drawbacks?
A: Intro What distinguishes each network generation, as well as its advantages and disadvantages?
Q: Describe the many categories of electronic computing devices.
A: Electronic Computing devices are those devices that are controlled by the CPU that including…
Q: When it comes to modeling software systems, what factors should be taken into consideration?
A: Introduction Software systems are the systems that are used for the intercommunication components…
Q: How do you programme? What factors should be addressed before selecting a programming language?
A: Intro In the context of visual programming languages, a programming language is a collection of…
Q: What are the most essential criteria that must be observed by web developers when developing a…
A: Overview: To describe the rules that Web designers must follow while designing a Web site that is…
Q: What are the distinctions between top-down and bottom-up approaches to information security…
A: Intro We have to write the differences between the two types of methods of information security.…
Q: What is a Trojan horse, and how does it operate?
A: A Trojan horse, or Trojan, is a type of malicious code or software that looks legitimate but can…
Q: Do you believe it is feasible to make a difference in the cloud's security after a data breach has…
A: Information breaks At the point when the security of information is compromised inside the cloud,…
Q: Find out the advantages and disadvantages of using solid-state secondary storage devices as opposed…
A: Magnetic storage : Magnetic storage or magnetic recording is the capacity of data on a charged…
Q: In order to speed up the processing of transactions, the vast majority of retail establishments have…
A: Introduction: Bar-code scanning is the term for this kind of data collection, which is done via…
Q: In terms of the amount of memory space and the amount of time required by the computer, what is the…
A: The Answer is in step2
Q: What is multifactor authentication and how does it work? Is it useful in avoiding the theft of login…
A: Intro Step 1 Multi-factor Authentication (MFA) is an authentication method that requires the user…
Q: Is it the responsibility of the database administrator or the database user to backup the database?
A: Introduction: The first stages of a database's life cycle are its design, then its implementation,…
Q: Give one example for each of the addressing modes.
A: Addressing modes are only the various manners by which the area of an operand can be indicated in a…
Q: What are the advantages and disadvantages of various authentication techniques in terms of security?
A: Introduction: This kind of authentication relies on a monitoring team or a third party, such as a…
Q: are application is consuming system resources and slowing down the system ?'s Is it possible to keep…
A: You may have to deal with the issue of system resources until the offending programmer is…
Q: Is it feasible to distinguish between different methods of authentication in terms of security?
A: Intro Distinguished: Being distinct implies appreciating someone. It is not unusual for exceptional…
Q: Which style of organisation is best for you? Why?
A: Answer: What type of organization is best for your business depends on a number of factors,…
Q: What are the several phases that make up the life cycle of the process of developing software?
A: Intro Software development lifecycle is the set of steps which is involved in the process of a…
Q: Describe the components of the security spheres paradigm. There must be enough information in the…
A: Introduction: Information security is primarily concerned with preventing unauthorized access to…
Q: Could you give a quick overview of the operating system's main components? in a nutshell?
A: Introduction: The following is a list of the primary elements that make up the Operating System:
Q: Complete the sentences with the correct preposition: At, of, on, in, to, from, with, for, about, at)…
A: Find the required answer given as below : As per company guidelines we are supposed to answer first…
Q: Which three characteristics of an object-oriented language are considered to be the most important?
A: Given: What are the three most significant elements of an object-oriented language?
Q: Describe the features and capabilities of various electronic devices, including as mobile phones,…
A: Introduction 1) Uses and Purposes SMARTPHONES It is possible to make and receive phone calls and SMS…
Q: In terms of the functionality that they both provide, could you please give a full description of…
A: Object-Oriented Programming: Object-oriented programming, sometimes known as OOP, is a kind of…
Q: Which encryption standard assures that data isn't tampered with after it's sent and before it's…
A: TLS/SSL: TLS/SSL is the most used encryption protocol, and it is used on the internet on a daily…
Q: Web Services and SOA (Service-Oriented Architecture) are compared and contrasted (Web Services).
A: Introduction: Web-based service providers
Q: Explain the advantages and disadvantages of traffic engineering as a solution to network congestion.
A: Intro Broadcast communications networks benefit from traffic engineering, which is the practice of…
Q: How do the rows in a table in a database organize the data that is stored in them?
A: The question has been answered in step2
Q: Explain the following: i) Connection Oriented and Connectionless Thanks in advance.......
A: The basic difference between connectionless and connection-oriented is as the name suggests that in…
Q: Provide a rundown of the many types of DNS records. Every single one need to be dissected in minute…
A: DNS: DNS translates IP addresses to space names globally. When a client visits a web address like…
Q: What precisely does the word "phishing" imply, and how can its meaning be summed up in a single…
A: The word Phishing: Phishing (pronounced "fishing") is an assault that tries to steal your money or…
Q: The creation of graphical user interfaces (GUIs) is commonly sped up by using event delegation…
A: Delegation Models: In GUI programming languages, the Delegation Event model is used to manage…
Q: The OSI model, on the other hand, specifies that a computer system must have a minimum of seven…
A: Given: The OSI reference model divides the connections between computer systems into seven levels of…
Q: My understanding of the two-factor authentication idea is lacking at the moment. How much of a…
A: Password protection important: Passwords are your computer's and personal information's first line…
Q: In C++ or pyhton Design and code a class as described in the following diagram BankAccount…
A: The solution is done using C++. Please refer to the following step for the complete solution to the…
Q: Object-oriented and procedural programming languages each have their own unique set of strengths and…
A: Definition: Procedure-oriented programmes are built on the basis of subprograms, sometimes known as…
Q: What is the microkernel design philosophy of the operating system?Is this a different technique from…
A: Introduction: The microkernel operating system is based on the concept of reducing the kernel to…
Step by step
Solved in 3 steps

- Make a deployment diagram of following We are making a system of Smart Counselling Application In which there will be a user who can get paid services from counselor.. Also user can post his problem on a free platform and can get free advice from counselor in comment section. User can give review to counselor after getting service. Admin can conduct a interview of counselor if he has doubts about counselor. There will be a payment method in over system.Give an example of any system. Of how you could calculate virtual works.CAN YOU ALSO WRITE ITS REPORT PLEASE WRITE THE REPORT OF THE GIVEN PROBLEM BELOW: You are asked to prepare a detailed report about your project Recommended page length is 5 without cover and references pages. Provide at least the below sections in your report. You can add more sections if you need. • Introduction Explain the problem you are assigned to. How it relates to Operating Systems? Which area of Operating System does the algorithm provide the solution? Explain in detail. MethodologyExplain your solution with pseudo-codes in detail. Implementation Demonstrate your code with a simulation. Explain step-by-step which functions are invoked. Do not write any code in this section, but use only function names. Show your run results. ConclusionSummarize the report. Discuss the efficiency of the algorithm and your implementation. PREPARE A REPORT AS ABOVE GIVEN DETAILS!!!
- A decent user interface should contain an exhaustive list of functionality. What are the most essential talents to have? Is it planned to use the same methodology across the board? Give specific instances to substantiate your claims.The capacity for numerous users to work at once is referred to as multi-user multitasking. To make your points, use concrete, daily instances.How can I define datetime in the following: because it keeps coming back with Error Type "help", "copyright", "credits" or "license" for more information.>>> def calculate_seconds_lived(birthdate):... current_date = datetime.now()... time_lived = current_date - birthdate... return time_lived.total_seconds()... >>> calculate_seconds_lived(datetime(1997, 6, 25)) Traceback (most recent call last): File "<stdin>", line 1, in <module>NameError: name 'datetime' is not defined
- Please help me with this Operating systems principles homework project (NOT GRADED) CHECK ATTACHED IMAGES FOR PROJECT SPECS Job Object Class ATTRIBUTES (Make “friendly” / “protected”) -arrTime -random 1-250 -cpuBurst -random 2-15 -priority -random 1-5 (5 is highest) -exitTime -algorithm result -turnAroundTime -algorithmresult -remainingTime -updated in algorithms METHODS: -constructor(s) -toString (to display initial jobs and algorithm results) -compareTo (general, by arrival time) //Note: different algorithms may need a different compare. i.e. by priority, etc. Those can be defines in the algorithm methods.Name at least three attributes that might be appropriate for each of the following classes: TVShow party JobApplication CheckingAccountWhat must be done for making application to perform better any meaningful actions?
- Question: Given the following values, compute function point when complexity adjustment factor (CAF) is significant and weighting factors are complex. User Input = 50User Output = 40User Inquiries = 35User Files = 6External Interface = 4? (After this See the Picture) Subject: Software Engineering. Note: write in own words. copy from internet will unhelpful for me.I am creating simple window money changer via microsoft visual studio and am encountering errors(refer to the picture) I hope you can help me solve this one. this is my code using System;using System.Collections.Generic;using System.ComponentModel;using System.Data;using System.Drawing;using System.Linq;using System.Text;using System.Threading.Tasks;using System.Windows.Forms; namespace Act3_AggaraoMikael_608{ public partial class Form1 : Form { public Form1() { InitializeComponent(); } private void label3_Click(object sender, EventArgs e) { } private void button1_Click(object sender, EventArgs e) { // Declares a variable double amount, converted = 0, exchange = 0; char currency; // Sstores the value of each textbox into variable amount = Convert.ToDouble(txtAmount.Text); currency = Convert.ToChar(txtCurrency.Text); // Uses Nested if…C Sharp Text to Morse Code Converter using System;using System.Collections.Generic;using System.ComponentModel;using System.Data;using System.Diagnostics;using System.Drawing;using System.Linq;using System.Text;using System.Threading.Tasks;using System.Windows.Forms; namespace Morse_Code_Chapter__8//Create a struce for Morse Code { [DebuggerDisplay("{" + nameof(GetDebuggerDisplay) + "(),nq}")] public partial class Form1 : Form { public Form1() { InitializeComponent(); } private void converterButton_Click(object sender, EventArgs e) {// key type = A and value type = .- Dictionary<char, string> letters = new Dictionary<char, string>(); letters.Add('A', ".-"); letters.Add('B', "-..."); letters.Add('C', "-.-."); letters.Add('D', "-.."); letters.Add('E', "."); letters.Add('F', "..-."); letters.Add('G', "--.");…

