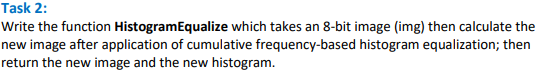
Write the function HistogramEqualize which takes an 8-bit image (img) then calculate the new image after application of cumulative frequency-based histogram equalization; then return the new image and the new histogram.
Q: Which of the following is NOT a walk from A to D? B E F Figure 1 O A) AEFEBCD В) АВCD O C) AFEBCD O ...
A: Answer the above questions are as follows:
Q: Programming Paradigms Description
A: Below is the answer to above question. I hope this will be helpful for you.......
Q: Why is it that effective anomaly-based intrusion detection systems are fundamentally more difficult ...
A: To mange the robust and resilient security feature by a user Intrusion detection systems are used.
Q: Design a recycling, MOD25, down counter using an HDL. The count sequence should be 11000 to 00000.
A:
Q: Identify the devices used in a small network. Identify the protocols and applications used in a sma...
A: The Answer is
Q: Provide examples of three intriguing new applications that are becoming feasible as a result of the ...
A: The Internet is a vast network that connects computers all over the world.
Q: What exactly is a problem domain?
A: Intro Problem Domain: It refers to all the information available which defines a problem and the con...
Q: What is the difference between static and dynamic memory allocation?
A: Introduction: The memory in static memory allocation cannot be altered while a programme is running....
Q: t is not a good plan if it hasn't been tried. Give examples of the many testing strategies that coul...
A: Introduction: Testing is required to uncover any faults in software that might cause damage. Without...
Q: 3. Old McDonald has a farm with 30 chickens. The chickens comprise 40% of his farm, and the rest of ...
A: Actually, given information Old McDonald has a farm with 30 chickens. The chickens compromise 40% of...
Q: What role will Artificial Intelligence play in the future? Do you have any Artificial Intelligence s...
A: Introduction: Artificial intelligence (AI) is a set of technical tools developed in the field of com...
Q: antages of three-tier appl
A: The main advantages of three-tier applications
Q: Question 1 Simplify 22 O4 3 4 % = (mod 4) %3D
A: Find the answer with calculation given as below :
Q: MICROPROCESSOR: Simulate the program and find the final answer. Identify the purpose of the Program...
A: Statement: Add the contents of memory locations 6000H and 6100H and place the result in memory locat...
Q: For this assignment *c++ & no ifstream, you need to build a class that contains basic information ab...
A: Here I have provided code in which you can do changes as per your need. Code:- // Include all the n...
Q: At the IT consulting firm where you work, there is a heated dispute going on. Some members of the te...
A: Introduction: Problems may develop at first due to reluctance to change, but strong analytical skill...
Q: Explain the XML (Extensible Markup Language) language's fundamental concepts.
A: Introduction: The text-based markup language Extensible Markup Language (XML) establishes a set of r...
Q: Use the encoding formula y = x + 18 (mod 26). (TYPE WITH NO SPACES) 1. Encode: DWN 2. The decoding f...
A: Shift Cipher: It works by using modulo operator to encrypt and decrypt the messages. It has a key K ...
Q: What are the benefits and drawbacks of including greater redundancy in a message?
A: Introduction: The benefits of including greater redundancy in a message
Q: What are the basic interfaces of Java Collections Framework?
A: Below is the answer to above question. I hope this will be helpful or you...
Q: What is the definition of a base class access specification?
A: Intro the above question is about What is the definition of a base class access specification ...
Q: Unless you supply a seed value, a Random object will utilize whatever it finds as its seed value.
A: Introduction: .Random numbers are helpful in various applications that need the generation of random...
Q: Is it possible that the development and deployment of new information technologies will have an impa...
A: Introduction: Internet banking: With online banking, users can conduct financial transactions throug...
Q: Is it acceptable to use cyber attacks against an organization or group in certain circumstances, and...
A: Is it acceptable to use cyber attacks against an organization or group in certain circumstances, and...
Q: DNS User's browser CDN 10 Load Balancer Cloud storage 9b Copy of data 9a Database Web app servers 9c...
A: The given modern architecture of web is called web application architecture. The web application arc...
Q: What are Hadoop's Edge Nodes?
A: Hadoop's Edge Nodes Hadoop edge nodes are the computer that provide the interface between Hadoop cl...
Q: What is it about documentation that is so critical to a successful criminal investigation? Make a li...
A: The following is the response: The Importance of Documenting Criminal Investigation ProceduresWhile ...
Q: What are the main functions of an operating system?
A: Introduction: A collection of programmes that coordinates the activities of computer hardware and so...
Q: Define the concepts of information system analysis and design.
A: Introduction Define the concepts of information system analysis and design.
Q: Before you may delete the programme folder containing background-running software, what must you do ...
A: Introduction: We should conduct the following before removing the programme files of the software th...
Q: What are the six stages you can follow to solve any computer issue?
A: Introduction: The stages involved in resolving a computer issue. Because it is a step-by-step approa...
Q: What are some of the most prevalent tools used in mobile app development?
A: Introduction: Surpasses Xamarin for developing native apps. Because it's a Microsoft product, you'll...
Q: Which of the following are important distinctions between TCP and UDP transport protocols? O TCP pro...
A: Let us see the answer: "Since you have asked multiple question I am solving first one for you if you...
Q: Give state diagrams of DFAS recognizing the following languages. In all parts the alphabet is {0,1} ...
A: Dfa for x0101y.
Q: Explain why a batch operating system would not be able to handle modern applications like airline re...
A: Note: According to our standards, when numerous questions are posted, we should only answer the firs...
Q: Give state diagrams of DFAS recognizing the following languages. In all alphabet is {0,1} parts the ...
A: Here, we are going to draw a DFA for given language. I have provided a handwritten DFA here, you ma...
Q: Given: Language L2 = {w ϵ {a,b}* | w contains substring aab} Construct the DFA representing the giv...
A: Solution:
Q: Give an overview of how the gradient mesh tool operates and how it is utilized at a fundamental leve...
A: Introduction: Gradient mesh tool is used in vector graphics software that allows you to generate and...
Q: describe the cache protocol
A: Cache protocol is explained below :
Q: Is it usual or unusual for TCP SYN and ACK segment to carry data during the three-way handshake conn...
A: answer is
Q: Computer science What if I use the Outline panel to create a numbered list?
A: Introduction: The components of a list can be numbered in a variety of ways, including Arabic and Ro...
Q: High-level programming languages are used to provide English-like programs that are executed on comp...
A: ALGORITHM:- 1. Take input from the user for 3 numbers. 2. Find the sum and average of the numbers. 3...
Q: Explain and describe anti-forensics techniques and procedure
A: Anti-forensics means any strategy or software to thwart a computer investigation. People can hide in...
Q: What GUI tool can you use to end a hung programme?
A: Introduction: Use the keyboard shortcut Alt + F4 to swiftly force a Windows shutdown. When you press...
Q: Search the web for a research report on thediscovery of a spurious relationship. Give theweb address...
A: Search the web for a research report on thediscovery of a spurious relationship. Give theweb address...
Q: What are the most efficient techniques of firewall administration? Explain.
A: Introduction: The Best Firewall Practices and How to Implement them. Every change to a firewall rule...
Q: What are some of the application are as where a LAN can be an effective tool
A: The LAN is locally networked in the ecosystem, which means It is a collection of many devices who al...
Q: Give five different examples from each Regular Expression and explain in words what does everyone do...
A: 1. Consider the regular expression (1+0)* (1+0) (1+0) (1+0) The set of strings that satisfy given...
Q: Is there any technology that is used by massively multiplayer games that could be repurposed for ano...
A: The majority of today's online games typically simulate a spatial virtual world which is conceptuall...
Q: 1. (a) Explain the one difference between validation check and verification check. (b) Decribe,...
A: I'm providing the answer of both parts, I hope this will be helpful for you...
Step by step
Solved in 3 steps with 5 images

- C++ How do I create a main and insert function to insert this sequence of integers :{ 138, 99, 16, 134, 42, 0, 6, 9, 4, 53, 47, 66) using a table of size 17? How do I Implement my own rehashing algorithm of choice and run the same sequence of input using a table of size 7? Code in imageWrite a C function which takes three integer inputs, corresponding to RGB components of a colored pixel, and coverts them to the YUV color space. The function should have the following prototype.Write a function that receives a two-dimensional array, prints out the data by row along with the sum of the row values. Each value should be printed separated by a space. After the last element in the row has been printed, the sum should be printed on the same line, followed by a newline.
- Find and replace problem You will implement a replica of find and replace option available in the word document !!! (attached below) Input: An initialized one dimensional character array of size 100 and the strings that would be found and replaced with. Output: The input character array after being replaced by the requested string. Sample Input: a:"A quick brown fox jumps over the lazy dog." Find: "fox", Replace: "tiger" Sample Output: "A quick brown tiger jumps over the lazy dog." Define a separate function that accepts three arguments as input string, find and replace string and implement the find and replace inside that function. You can use the strcmp() function for the string comparison along with other necessary libraries. You need to call that function from the main function and print the result in the main function. (e.g. use the pointer concept)Create a function that translates a sentence into pig Latin. To convert a word to pig Latin, remove the initial character, move it to the rear of the word, then add the characters "ay" to the word. In pig Latin, "hello world" is "ellohay orldway." Your function can presume that each word has at least two characters and is separated by a single space with no punctuation marks.use c#The code for a function that is similar tofunction vfunct (a). We used vfunct toillustrate the use of a frame pointer in managing variable-sizestack frames. The new function aframe allocates space forlocal(a) C code1 #include <alloca.h>23 long aframe(long n, long idx, long *q) {4 long i;5 long **p = alloca(n * sizeof(long *));6 p[0] = &i;7 for (i = 1; i < n; i++)8 p[i] = q;9 return *p[idx];10 }(b) Portions of generated assembly codelong aframe(long n, long idx, long *q)n in %rdi, idx in %rsi, q in %rdx1 aframe:2 pushq %rbp3 movq %rsp, %rbp4 subq $16, %rsp Allocate space for i (%rsp = s )5 leaq 30(,%rdi,8), %rax6 andq $-16, %rax7 subq %rax, %rsp Allocate space for array p(%rsp = s )8 leaq 15(%rsp), %r89 andq $-16, %r8 Set %r8 to &p[0]⋮array p by calling library function alloca . This function issimilar to the more commonly used function malloc, except thatit allocates space on the run-time stack. The space isautomatically deallocated when the executing…
- Define a function named posterize. This function expects an image and a tuple of RGB values as arguments. The function modifies the image like the blackAndWhite function developed in Chapter 7 and shown below, but it uses passed in RGB values instead of black.TODO 3: Invoke the gaussian() function, which accepts x_values, mu, and sig. Save the results in the variable y_values. # TODO 3 y_values = display(y_values) todo_check([ (y_values.shape == (120,),'y_values does not have the correct shape of (120,)'), (np.all(np.isclose(y_values,…Please answer the "function" I already did the code. thank you this is my code : A = [2,1,0;-1,1,1;1,1,-1] [ss,li,bas] = splibas(A) function [ss,li,bas] = splibas(A) % Initialize outputs to false ss = false; li = false; bas = false; % Get Dimension of vectors dim = size(A(:,1),1); % Get number of vectors n = size(A,2); % Calculate Rank of A r= rank(A); % If rank is equal to number of vector % Vectors are linearly independent if(r==n) li = true; end % Calculate row echelon form of A RE = rref(A); % Find number of non-zero rows span = 0; for i=1:dim if(~isequal(RE(i,:),zeros(1,n))) span = span + 1; end end % If number of non-zero rows equals vector dimension % Vectors form a spanning set if(span==dim) ss = true; end % If vectors are both spanning set and linearly-independent % They form Basis if(ss==true && li==true) bas = true; end end
- Write a c++ function is called IsContain Given two arrays A and B with equal size n, write a C++ function that returns true if every element of A is found in B; otherwise returns falseFollowing the Function Design Recipe, create a complete functionnamed get_consonant_cluster that returns a tuple of the consonant phonemes atthe BEGINNING of a word pronunciation. The parameter is of type PHONEMES. Inthe example word pronunciation ('G', 'UW1', 'F', 'IY0') from above, thereturned tuple would be ('G',). If a word pronunciation begins with a vowelphoneme, the empty tuple would be returned. Use the image attached as a helper function."""Task 3 Largest PO2 LE: Implement the largest_po2_le function as directed in the comment above the function. If the directions are unclear, run the code, and look at the expected answer for a few inputs. As specified in the comment, you may not use multiplication or some sort of power function, and should instead rely on bitwise operations. Consider how binary numbers are structured, and how you might find the largest power of 2 of a binary number. Code: #include <stdio.h>#include <stdbool.h>#include <stdlib.h> // BEGIN STRINGBUILDER IMPLEMENTATION // This code is a very rudimentary stringbuilder-like implementation// To create a new stringbuilder, use the following line of code//// stringbuilder sb = new_sb();//// If you want to append a character to the stringbuilder, use the// following line of code. Replace whatever character you want to// append where the 'a' is.//// sb_append_char(sb, 'a');//// Though there are some other functions that might be…

