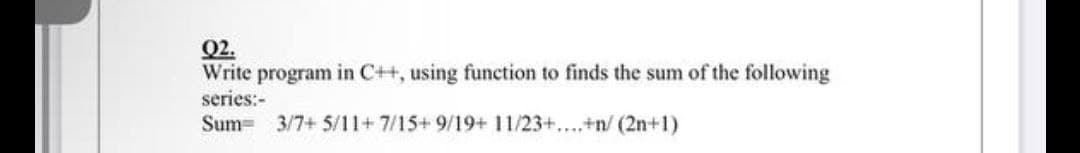
Write program in C++, using function to finds the sum of the following series:-
Q: Please do it with regular expression. Don't use loops please. Do fast, I have no time left Write a…
A: Your answer is given below in three steps:- Required:- Please do it with regular expression.…
Q: What systems lend themselves well to agile development?
A: Agile development is an iterative software-development methodology which teams use in projects.
Q: Discover everything there is to know about social media. What is autonomous computing, and how does…
A: Introduction: Social networking is described as the use of social media websites and programmes,…
Q: What exactly is the purpose of doing a technical analysis? Describe how it is used by technicians,…
A: Introduction: Technical analysis is a technique. Methods of Valuation There are three basic…
Q: What are some of the most frequent computer programs that are used to solve the issue of the least…
A: Definition: List some of the most common computer applications of the minimal spanning tree issue. A…
Q: Which of the following four kinds of information systems are the most frequent, and how can you tell…
A: There are primarily four different types of information systems, which are as follows:
Q: Are you familiar with the applications of dynamic programming?
A: Define: The method of dynamic programming is one that is used in the process of issue optimization.
Q: ad data of an array, it must be read one component at a time. True Fal
A: Introduction: An array will contain various values below one name, and therefore the things will be…
Q: Why do we need a data model, and how exactly will it assist us in achieving this objective?
A: A data model is a strategy for defining and organising database data structures. It also aids in the…
Q: Analyze the similarities and differences between AVL Trees and Binary Search Trees. Is it feasible…
A: Binary search tree is a binary tree in which the the the left child contains less value than parent…
Q: Why are there firewalls in place, and what are they for?
A: Introduction: A firewall is a network security device that analyses incoming and outgoing network…
Q: Please explain in detail how hybrid cloud systems like Dropbox work.
A: Intro “Cloud” is short for “cloud computing,” and it refers to tasks and services provided or hosted…
Q: For int x[5] = {2, 6, 3, 1, 8}; the value of x[4] = 8? True False
A: Yes it is True => x[4] = 8
Q: What are some of the various software testing techniques that are utilized in the creation of…
A: Required: Describe the many types of software testing methods used in software development. Perform…
Q: You need to be completely familiar with the word's connotations in order to comprehend the meaning…
A: What precisely is Critical Concern? Consideration may manifest itself in a number of ways. Examining…
Q: What is the function of a firewall, and how do you set one up?
A: Given: What is a firewall's purpose, and how do you set one up?
Q: Nanotechnology has the potential to have a large influence on the treatment of sickness, the mending…
A: Introduction: If nanotechnology could help humans live longer than they do now, then it would…
Q: in what RAID 5 is? When compared to the other available RAID configurations, why would you choose to…
A: RAID 5 is an overabundance show of independent circles plan that usages plate striping with…
Q: draw a D flip-flop that has the same characteristics as the one shown , but instead of using NAND…
A: Draw a D flip-flop that has the same characteristics as the one shown , but instead of using NAND…
Q: When it comes to doing research on certain topics, are there any discernible variations between the…
A: Definition: A search engine, such as Google or Bing, searches the Internet using computer algorithms…
Q: Why are software standards called "Process Standards" as opposed to "Product Standards"?
A: A product is any software developed in response to a customer's request: It might be a…
Q: Does it make sense to investigate the many ways that businesses put information technology to use?
A: Businesses also use organizational information systems, enterprise resource planning systems,…
Q: In the realm of covert flow control, what kind of functions may the SEH be put to work performing?
A: SEH (Structure Exception Handling) (Structure Exception Handling: Structure is represented by the…
Q: Which four primary categories of information systems are there to choose from?
A: We must discuss four different sorts of information systems: There are several kinds of information…
Q: What is the function of a firewall, and how do you set one up?
A: Intro A firewall is a type of security equipment that can be either hardware or software. It can…
Q: Give the regular expression for the set of all strings having odd number of 1's
A: INTRODUCTION: Here we need to give the regular expression for the set of all strings having odd…
Q: In a research that looked at how long it took patients to get to their doctors' offices, it was…
A: Given: Under the title "Academic Publications Reviewed and Discussed in This Edition of the Health…
Q: How can we classify the many kinds of information systems?
A: Information System A collection of various pieces of equipment used in the collecting, processing,…
Q: What are the four most important characteristics to look for in a software developer? Describe how…
A: Introduction: We must demonstrate the four most important attributes to seek for in a software…
Q: What applications, devices, and gadgets are part of the IOT around you? What are you doing with it?…
A: Introduction: Here, we must explain which applications and devices/gadgets are considered part of…
Q: Recognize the differences between ternary and three binary connections.
A: The most common sort of relationship that contains instances of two entity types is a binary…
Q: What is the best way to explain a data structure that employs a double linked list?
A: Doubly Linked List is the variant of Linked List that allows traversal in both ways, forward and…
Q: Q4) Test the continuity of the finction fx -251 <0 OS X<1 X=1 F(x) = 3x -2 2x +1 3.
A:
Q: 3. Remove one edge (any edge), then show Prim's algorithm to create the MST for the following graph.…
A:
Q: Use the encryption congruence C = (3P + 7) mode 26 to encode the message EASY
A: Given C=(3p+7) mod 26 Given message EASY A B C D E F G H I J K L M N O P Q R S T U V W X Y Z 1…
Q: Why may stack systems represent arithmetic expressions in reverse Polish notation?
A: Notation in Polish Done Backwards: It is a method of encoding arithmetic expressions in which the…
Q: Then, create a Java program named Main.java that consists the main fnction with the following value…
A: First, create 3 classes:- public class Document { private String authors; public String…
Q: What image of e-mail do you have in your mind? How does a message travel to its intended recipient…
A: The Answer is in step 2:
Q: How well do you understand the basic concepts behind the management of firewalls? Explain.
A: The following are some of the most successful firewall management practices: traffic is blocked by…
Q: Another major approach of controlling and safeguarding the Internet and other networks is to use…
A: Two different kinds of firewalls are described in genera: host-based firewalls, which manage the…
Q: Two (2) significant Youler functions are nome and ducribe. Rou lers are essential Compukr neluorky…
A: Intro Routers and Switchers are the most common devices used in networking. With Router and…
Q: How are the members of the base class sent down to the classes that are derived when using public…
A: Given: The access-specifier tells us about the type of inheritance, as we've seen above. Public…
Q: What are the benefits and drawbacks of having data processing carried out in a decentralized…
A: Define: A distribution system is a collection of networked computers that works together to solve a…
Q: Which four primary categories of information systems are there to choose from?
A: Introduction: We must discuss four different sorts of information systems. There are several kinds…
Q: Describe a Greedy Algorithm in Data Structure and give an example.
A: An algorithm is a computer programmed that seeks for the best solution to a problem. On the basis of…
Q: = { w : w = CAjGnTmC, m = j + n }. For example, CAGTTC ∈ L; CTAGTC ∉ L because the symbols are not…
A: given : ∑ = {C,A,G,T}, L = { w : w = CAjGnTmC, m = j + n }. For example, CAGTTC ∈ L; CTAGTC ∉ L…
Q: Why do we need a data model, and how exactly will it assist us in achieving this objective?
A: In this section, we are needed to describe what precisely a data model is and what it is utilized…
Q: For an array declartion of int number [25];, what will be the ending index? 0 1 24…
A: Elements of an array is stored in contiguous memory location. Indexing of an array starts from 0.
Q: Define the term Protocol
A: A network protocol is a set of established rules that dictate how to format, transmit and receive…
Q: In the context of software engineering, provide three compelling reasons in favor of the necessity…
A: why is software design crucial in software engineering: Software design is the process of laying the…
Step by step
Solved in 2 steps with 2 images

- 5. Write a C function that takes a positive integer n as an argument and returns 1 if n is prime, and 0 otherwiseWrite a c++ function int calculate(int x) which returns the value of 2x2 + 10sin(x) -12.Problem 3. write a C++ function that finds as many primes of the form 2n + 1, where n is a positive integer, as you can.
- Write a C++ function that accepts a double typed number and return back the fractional part of the number. For example, if the number is 789.123, the number 0.123 should be returned.What is wrong with the following C++ function? void Maximum(int a, int b, int& max) { if (a > b) max = a; else max = b; return max; }Write a complete c++ program that does the following: - Creates a function called 'convertDistance' that takes an integer input representing a value in miles, converts it to its decimal kilometer equivalent, and returns the result. - Use this function in main to compute and print the kilometer-equivalents of all mile- distances from 10 to 100. - You may use the following conversion: 1 mile = 1.6 km
- Write a C++ function weird_sum that takes two integer parameters, n1 and n2. The function returns the sum of n1 and n2, as long as their sum is not a multiple of 13. If their sum is a multiple of 13, the function returns 3 less than the sum of n1 and n2.Write a C++ function: int cube(int ); This function takes an Integer parameter and return the cube of that number.// Description: Write a program that outputs a root of a given function f(x) by using a bi-section method. // f(x) = x3 + 5x2 +7x +2 // IN C++ Please! not using #define EP 0.01
- .Write a function: int calculate(int x); In c++, the function returns value of 2%x + 3.In c++, Write a function that returns the greatest common divisor of 2 integers.Write a function called multiplyMe in c programming which has a variable number of integers as arguments and returns the product of the integers ie input | output (3, 2, 3, 4)) 24

