that calculates the total
Q: System models-how are they defined? What should basic models consider?
A: What does the concept of a system model entail? What considerations should be made while developing…
Q: How would you explain challenge-and-response authentication? (CRAS). This authentication mechanism…
A: A challenge-and-response authentication (CRAS) process involves the exchange of a challenge and a…
Q: What happens if you try to resize a bounding box when your cursor is over its boundary or a corner?
A: The scaling handle, a handle, drag handle, sizing grip, or resize corner, is a graphical user…
Q: Explain any potential issues that could arise when making use of the legal software.
A: Introduction: Copyright laws protect legal software; the publisher may distribute only one copy of…
Q: Who among the authorized users of a two-key authentication system should have access to the private…
A: Keys Public: Everyone who has a copy of the to the SSH server's public key that has been previously…
Q: Is there a specific way in which the internet is an excellent example of ICT? That is easy to…
A: Answer: Introduction of Information and Communication Technology ICT stands for Information and…
Q: one go about selecting the model of the system that is m
A: Introduction: Requirements is one of the most important phase of the development model. Based on the…
Q: Define the GRANT statement and discuss its significance in the context of security. In what ways…
A: The GRANT assertion: To provide users access or privileges to database objects, use the SQL GRANT…
Q: The following lines of code were each run for the same list, I. Match each resulting output with the…
A: To add or subtract two complex numbers, that are used to just add or subtract the corresponding real…
Q: How can one get access to a file using the many techniques available? What are the benefits of using…
A: We have to explain that what are the diffrent techniques are available for accessing the file along…
Q: Cloud storage vs. client storage software: pros and cons? (100 words minimum)
A: Cloud storage and client storage software have their own set of pros and cons, and which one to…
Q: Permission lists must be encrypted and protected since they may be changed. What if these files were…
A: Introduction: Permission lists are important configuration files that define the access levels and…
Q: Rule, model, and case-based reasoning models exist. Show a vulnerability.
A: Introduction: Rule-based reasoning uses induction rules to determine whether a new problem should be…
Q: What criteria are required to ensure that the files are being monitored for their integrity?
A: Answer is
Q: how can we get the mean during the extraction of each audio chroma feature? A python code please.…
A: Answer is given below with updated code
Q: Just what does it mean to "choose numbers at random"?
A: Random: The term "random" denotes a selection from a collection of objects, quantities, numbers,…
Q: This session covered rewriting and editing methods. Your favorite editing tool? Explain why and…
A: making changes and modifying features. The writing process depends on the two jobs of revising and…
Q: How can various kinds of people access the same files in a variety of different ways? What are the…
A: Answer: Introduction: The current global system supports both index and direct file access. It is…
Q: Educators create curriculum in addition to doing so. How would you suggest modifying your curriculum…
A: According to the information given:- We have to define to create curriculum in addition to doing so.…
Q: What are the overarching purposes and objectives of the File Integrity Monitoring program?
A: To be determined: What are the aims and objectives of the program File Integrity Monitoring?…
Q: Answer the given question with a proper explanation and step-by-step solution. At this point, you…
A: To connect a database to a Java application, you will need to import the appropriate JDBC driver…
Q: Why is biometric authentication safer?
A: Definition: Biometric authentication is a security method that uses an individual's unique…
Q: When it comes to a solid-state drive, how do you go about restoring data using forensic techniques?
A: Although a forensic recovery may not exactly replicate the outcomes of a standard recovery, it may…
Q: The CPU performs the subtraction of the two binary numbers 01110011 - 00111101 by adding
A: Answer the above question are as follows
Q: How enforcing IT and network risk regulations may be necessary to prevent workers from violating…
A: Solution: No matter the size of the organisation, it is imperative for all organisations to keep…
Q: Define symmetric and asymmetric multi-processing and explain their differences.
A: MULTIPROCESSING:In computing, multiprocessing is a technique of operation in which two or more…
Q: What exactly are WDE solutions, and when would it be appropriate to make use of them?
A: Whole Disk Encryption (WDE) solutions essentially play the leading role in computer security. It is…
Q: When talking about Linux, what does it imply to say that something is a "distribution"?
A: LINUX DISTRIBUTION: The Linux kernel, GNU tools, optional programmes, and package management make up…
Q: Which method of software licensing is the most cost-effective? In addition to your answer, don't you…
A: Application software is a kind of computer programme that carries out a particular task for a…
Q: for the grammars below, determine if they're ambiguous; and if a grammar is ambiguous, find a string…
A: Answer: We need to explain the which grammar is ambiguous or Unambiguous . so we will see in the…
Q: Multiprocessing may be symmetric or asymmetric. Just what are the pluses and minuses of using…
A: Multiprocessing refers to the use of multiple processors or cores to perform tasks simultaneously…
Q: What precisely is a router?
A: The answer is given in the below step
Q: If someone has never heard of the non-free Linux firewall before, could you perhaps offer a brief…
A: Introduction: The command-line firewall with the largest use is Netfilter. Solution: The…
Q: Consider how salt protects passwords in encryption.
A: Can you explain encryption: Data is encrypted so that only the right key can decode it.
Q: Can you explain the function of a signature file in the context of securing a computer with…
A: Answer A signature file is a database of known malicious software (malware) that antimalware…
Q: Authentication's goals? Comparing authentication techniques' pros and cons
A: Authentication's goals? Comparing authentication techniques' pros and cons answer in below step.
Q: What type of additional training did ChatGPT get compared to GPT2? Select one: a.…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: "Why are authorization lists so prone to unauthorized change that they have to be encrypted and…
A: Introduction In this question we are asked What are authorization lists, and why is it necessary to…
Q: How can the benefits and drawbacks of the various authentication methods, in particular with regard…
A: Authentication methods can be evaluated based on their benefits and drawbacks in terms of security,…
Q: Enterprise-based solutions may provide both benefits and downsides when it comes to deploying ICT in…
A: Introduction Information and communication technology is referred to as ICT. It describes the use of…
Q: Where can I get the design specifications for the system that checks the integrity of the files?
A: Introduction: The system hardening procedure includes a system integrity check to ensure that all…
Q: How does bottom-up information security differ from top-down? To what end does the top-down approach…
A: The answer is discussed in the below step
Q: Explain web application security's importance. Unsecured application issues? Why is SQL injection…
A: Answer the above question are as follows
Q: How do you pick from commercial software? Use which criteria?
A: Retail Software Suite While looking to buy software, it's important to keep in mind the many…
Q: How do hardware and software interruptions vary and work?
A: The solution is given in the below step
Q: Imperfect and unclear models challenge non-monotonic reasoning?
A: The reasoning is the process of generating logical conclusions and making predictions based on…
Q: Why authenticate? Verification methods are being assessed.
A: Authentication's Purposes: Authentication validates that an organization, programme, or person…
Q: How knowledgeable are you about the usage of contemporary computers?
A: Given: Typically, it takes a specific raw form of data as input and processes it using a central…
Q: How can the benefits and drawbacks of the various authentication methods, in particular with regard…
A: Valuing someone is being distinguished. It's normal for great people to be older, smarter, and more…
Q: Why do hashed password files beat encrypted databases?
A: If the passwords are in plain text, you've revealed a piece of private information that your users…
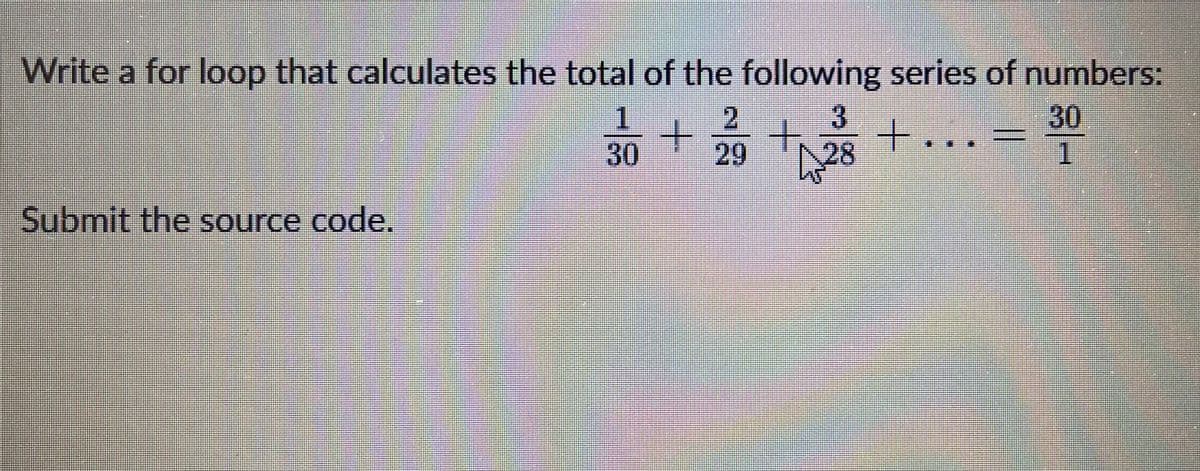
Write a for loop that calculates the total of the following series of numbers:
1/30 + 2/29 + 3/28 + ... = 30/1
Submit the source code.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Write a for loop that displays the following set of numbers:0, 10, 20, 30, 40, 50 . . . 1000Write a for loop that displays the following set of numbers: 4 8 16 32 64 128 256 512 1024Write a for loop that displays the following set of numbers: 0, 20, 40, 60, 80,…..1000 (Note there is a comma between the numbers but not the last one)explain please.
- write a for loop that displays each integer number from 14 to 25 (inclusive) . include any necessary declarationsWrite a for loop that displays the following set of numbers: 0, 20, 40, 60, 80,…..1000 (Note there is a comma between the numbers but not the last one)explain please. C++Ask the user how many integers that he/she wants to enter. Using a for loop, ask the user for that many integers. Then, display all those integers.
- write a loop that calculates the (float) sum of the following series of numbers: 50 + 51 + … + 5000. The numbers should not be pre-calculated, rather the loop should cause the increment/decrement.Write a for loop that does exactly the same thing as the following code: j = 1; while (j < 13) { cout << “the square root of “ << j << “ is “ << sqrt(j); j =j + 2; }assuming the variable num has been defined, write a for loop that displays all the odd numbers from 3 to 23.
- The following 'for loop' will execute its body of code ___________________ times: for (int i=0; i <= 10 ; i+=3)Range for loop should be used even the block code needs to access index. Group of answer choices True FalseThe following while loop should be converted to a for loop: I = ten whereas i250 is equal to I print out I Equals I plus 50

