The determination to make a context switch is based on which of the follow O illegal operation O reboot O timer O system çal
The determination to make a context switch is based on which of the follow O illegal operation O reboot O timer O system çal
A+ Guide To It Technical Support
10th Edition
ISBN:9780357108291
Author:ANDREWS, Jean.
Publisher:ANDREWS, Jean.
Chapter14: Troubleshooting Windows After Startup
Section: Chapter Questions
Problem 7TC
Related questions
Question
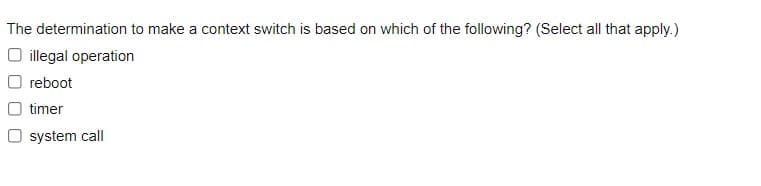
Transcribed Image Text:The determination to make a context switch is based on which of the following? (Select all that apply.)
O illegal operation
O reboot
timer
O system call
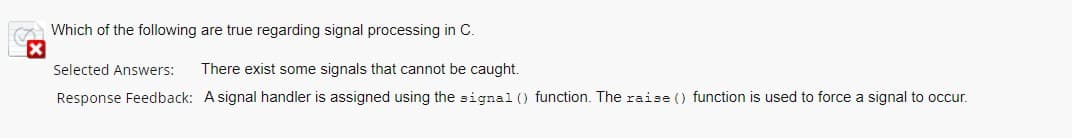
Transcribed Image Text:Which of the following are true regarding signal processing in C.
Selected Answers:
There exist some signals that cannot be caught.
Response Feedback: A signal handler is assigned using the signal () function. The raise () function is used to force a signal to occur.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,