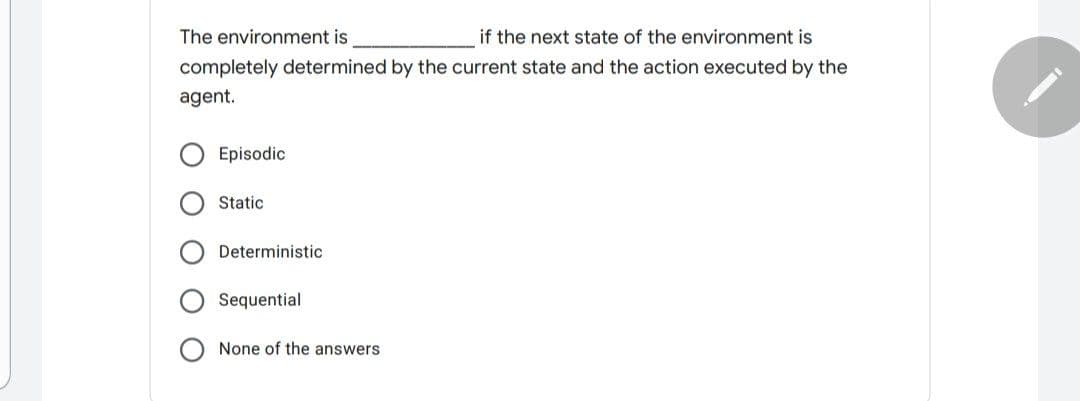
The environment is if the next state of the environment is completely determined by the current state and the action executed by the agent. Episodic Static Deterministic Sequential None of the answers O O
Q: What's the difference between a Structure and a Class in terms of their functionality?
A: Introduction: In C or C++, a structure is a user-defined data type. A system creates a data type tha...
Q: Asks the user to enter the name of your department using Scanner and asks you to enter three numbers...
A: The program is written in Java. Check the program screenshot for the correct indentation. Please che...
Q: + program that ask that takes an array of 5 characters from the user and then output the characters ...
A: 1. C++ PROGRAM FOR PRINTING A CHARACTER ARRAY IN REVERSE ORDER:: #include<iostream>using names...
Q: Explain how numerous access approaches boost the connection line's capacity.
A: Introduction how multiple access techniques improve the capacity of the link line.
Q: Do you think type checking on pointer variables is greater (stricter) in assembly language than it i...
A: Type Checking: Type checking ensures that each operation receives the appropriate amount of argument...
Q: a) What exactly is Big Data and why is it important? b) The Limits and Security Concerns of Big Data...
A: What is Big Data? Massive collections of data, also known as datasets, that are too large and compli...
Q: Consider the following scenario: you have a team of seven to nine people working on a large project ...
A: Introduction: Because the needs are only partially stable, I choose to adopt an incremental model fo...
Q: Many firms are starting to employ big data these days. Discuss it, as well as how and why the organi...
A: Introduction: Big data refers to a collection of unstructured, semi-structured, and structured data ...
Q: Given an Program in c++ unsorted array, find the least difference between the element pairs. Display...
A: Example: given array: arr[ ]={ 1,2,50,80,4,3 }, then find n=30 therefore output will be: pair foun...
Q: rected graph K, with two distinct vertices z, k. And let O be a minimum spanning tree of K. Prove th...
A:
Q: Please and thank you! Convert the following IEEE-754 Floating Point notation (shown in hex) into a ...
A: Here in this question we have given a hexadecimal number and we have asked to convert it into IEEE75...
Q: Perform the layer wise detailed comparison of TCP IP and OSI reference model (note: use diagram for ...
A: Solution: The OSI stand for Open System Interconnection , it is the conceptual model used for the ne...
Q: Explain what the term "portability" means in terms of programming languages.
A: Please find the answer and explanation in the following steps.
Q: 1. Shortly define the three most common error types that happen during pro- gramming. 2 Define and s...
A: Given below are the three most common error in programming
Q: What is greedy perimeter stateless routing, and how does it work?
A: Introduction: GPSR (Greedy Perimeter Stateless Routing) is a mobile, wireless routing technique that...
Q: Make a distinction between assembly code and source code.
A: Introduction: The term "source code" refers to high-level code created by a human/programmer. The so...
Q: ange to HLL I already posted same question but no response. Do quick.
A: I have written the code below as already solved before:
Q: Programming Exercise 5: You are to design a program to create five two-element word arrays (AAA, BBB...
A: Given : You are to design a program to create five two-element word arrays (AAA, BBB, CCC, DDD, EE...
Q: ite a for-loop that will print the pattern xxxxx; the character 'x' may not occur mo
A: Lets see the solution.
Q: Database Indexing What do you mean by buffer management and replacement strategies. Name the ways to...
A: In Database management system, data must be in RAM for DBMS to operate on it. As per memory usage, w...
Q: his exercise will assess how well you understand the various processes or methodologies involved in ...
A: AS PER OUR POLICY “Since you have posted a question with multiple sub-parts, we will solve the first...
Q: Blinking: Fix the below code. Using the display property, create it so that it will flash the loadin...
A: Asked corrected javascript code is provided in the next step.
Q: What exactly is Big Data and why is it important?
A: As per company guidelines we are suppose to answer only first 3 subparts of the question. Kindly re-...
Q: Is Assembly Language a portable programming language?
A: An assembly language is low level programming language that is intended to communicate directly with...
Q: Describe the term decomposition and provide two (2) reasons why it is relevant to the systems analys...
A: Given that Describe the term decomposition and give two (2) reasons why it is important to the syste...
Q: Write a C program using cin and cout codes that input and output name, address, and age to an approp...
A: Due to company policies I am compelled to solve only one question and that is the first question. Pl...
Q: #include #include using namespace std; int main(int argc, char const *argv[]) { char s1[6] "Hello"...
A: Let's see the output below
Q: What is the difference between a set of test criteria and a set of test requirements?
A: Answer:
Q: What is A. I. and what does it mean
A: artificial intelligence (AI), the capacity of a computerized PC or PC controlled robot to perform un...
Q: List at least 10 ways to protect your network from malicious and harmful attacks.
A: List at least 10 ways to protect your network from malicious and harmful attacks.
Q: What happens if you leave the parameter for a key partition empty (in SQL)?
A: key partition is empty in sql answer for is above step
Q: 3. Consider the following graph for question a and b. B E (a) What is the highest-cost path for find...
A: Given graph contains 7 vertices that includes: S, A, B, C, D, E and G. There are edges between the n...
Q: Introduce a method or strategy that you would implement to determine the area of a hexagon without u...
A: The answer is given below.
Q: f solve(a, b): return b if a 0 else solve(b % a, == int(solve(20, 50))
A: Output of the above code snippet will be 10 solve(50%20,20) 50%20--->10 10%20---->10
Q: The figure below shows an arrow diagram of a partial order R. R b a d e f List the maximal elements ...
A:
Q: Build or Prototype an arduino-based solution for: the need to determine the soil temperature Program...
A: The Soil Moisture Sensor measures soil moisture grace to the changes in electrical conductivity of t...
Q: What is the significance of SUS to Linux?
A: Answer is given below:
Q: Computers utilize the Post Office Protocol (also known as CPOS), which is a compressed version of th...
A: Introduction: The Post Office Protocol (POP) is the Internet Protocol (IP) network protocol that ena...
Q: Question 2: Write and XHTML source code corresponding to the given webpage using inline CSS. Re-do t...
A: According to the Question below the Solution: Output:
Q: Create a c program that would ask a user to input 10 different numbers and outputs the sum and avera...
A: 1) Below is C program that would ask a user to input 10 different numbers and outputs the sum and av...
Q: Discuss the services that operating systems offer, as well as the three interfaces that operating sy...
A: Serives that operating system offer anf=d three interfaces explain in below step
Q: What are an operating system's two modes and two primary functions? What is the file system's primar...
A: Introduction: An operating system: OS is a software program that connects a computer user to the har...
Q: Consider a scenario where a "Class C" network is divided into 7 subnets of fixed length. Design each...
A: Lets see the solution.
Q: What are static members, and what do they do? Consider a variety of qualities. in the c++ language
A: Introduction: When a user specifies a class member as static, it indicates that no matter what propo...
Q: What are two use cases for a VIP (virtual IP address)? How is licensing an important concern when us...
A: What are two use cases for a VIP (virtual IP address)? How is licensing an important concern when us...
Q: What is multifactor authentication, and how does it work? What role does it play in protecting again...
A: Introduction: When it comes to establishing trust, authentication is the process of identifying whet...
Q: Distinguish between CSMA/CD and CSMA/CA. With flowchart elucidate the working scenario of Pure ALOHA...
A: CSMA/CA transmit or transfer the intent to send the data first and once there is an acknowledgement ...
Q: Create a pseudocode and flowchart for this c++ program #include using namespace std; int main() ...
A: Find the required code given as below and output :
Q: Please answer it in Python write a function word_vers_dictionary(word), which takes a word (string...
A: According to company guidelines we are supposed to answer only one question. Kindly repost other que...
Q: With the assistance of an example, distinguish between polymorphism and overloading.
A: Polymorphism can be said as the fact that something exists in multiple forms. Polymorphism, in simpl...
Step by step
Solved in 2 steps with 2 images

- The last callback in the lifecycle of an activity is onDestroy(). The system calls this method on your activity as the final signal that your activity instance is completely removed from the system memory. Usually, the system will call onPause() and onStop() before calling onDestroy(). Describe a scenario, though, where onPause() and onStop() would not be invoked.A parent may terminate a child process at any time. What is the transition will be involved? Select one: a.Running --> Exit b.Ready --> Exit c.Ready --> RunningQuestion1: Consider the MyReader class as given below. Identify any two problems (Problem 1, Problem 2) avoiding MakeTableand Centre the Name of the Class in the class design and provide fixed/correct version of this diagram. Also point out/mention/highlightyour fixes for identified Problem 1 and Problem 2, respectively. MyReader validateLocation() checkFTP() ping() readFromDisk() readFromWeb() readFromNetwork()
- Draw the context level and 1st level DFDSoftware is to be developed to find the average marks of people in a class. The user interacts withthe software via a special panel that lets him enter the required information. Initially, the softwareasks for number of students in the class by displaying a message on the panel screen. Once thisinformation is entered, the software displays a message to enter names of students and marks. Ifnegative marks or marks greater than 100 are entered, an error message is displayed. If marks arecorrectly entered the software calculates the average marks, stores them and also displays them onthe screen.Correct the given statement for implementing inheritance from applet and action listener class to Manager . public class Manager implements applet extends actionListenerCreate a java class to represent a log message. The log message should include the following attributes:a. The severity of the message from least to most severe: DEBUG, INFO, WARNING, ERROR, or CRITICAL.b. The name of the module that has created the log.c. The timestamp at which the log was created in the format“YYYY/MM/dd HH:mm:ss.SSS” (see java.text.SimpleDateFormat).d. The message to be logged.e. A toString() method that returns a string in the format:[severity][timestamp][name] message
- What must be done for making application to perform better any meaningful actions?Multiple Choice:Update the time taken for zebraZirly for each of the following behaviors, using the updateTimeTakenForBehavior below A behavior named "Eat 1 pound of bark": 22 public void updateTimeTakenForBehavior(String behaviorName, int timeToComplete) { for(int i = 0; i < this.behaviorList.length; i++) { Behavior tempBehavior = this.behaviorList[i]; if( tempBehavior.getBehaviorName().equals(behaviorName)) { tempBehavior.setTimeToComplete(timeToComplete); } } Choose one of the following from the above choices (A, B, C or D within the code). //A zebraZirly.updateTimeTakenForBehavior(22, "Eat 1 pound of bark"); // B zebraZirly.updateTimeTakenForBehavior("Eat 1 pound of bark", 22); // C zebraZirly.updateTimeTakenForBehavior("Eat 1 pound of bark"); zebraZirly.setTime(22); // D zebraZirly.updateTimeTakenForBehavior(22); zebraZirly.setBehavior("Eat 1 pound of bark");Define an Animal method that updates the time to complete a particular behavior based on its name. Choose one of the following from the above choices (A, B, C or D within the code): public class Animal { // Other instance variables, constructors and methods // omitted for brevity // A public void updateTimeTakenForBehavior(String behaviorName, int timeToComplete) { for(int i = 0; i < this.behaviorList.length; i++) { Behavior tempBehavior = this.behaviorList[i]; if( tempBehavior.getBehaviorName().equals(behaviorName)) { tempBehavior.setTimeToComplete(timeToComplete); } } } // B public void updateTimeTakenForBehavior(String behaviorName, int timeToComplete) { for(int i = 0; i < this.behaviorList.length; i++) { Behavior tempBehavior = this.behaviorList[i]; if( !tempBehavior.getBehaviorName().equals(behaviorName) ) {…
- Java task Based on PercolationProbability.java (provided below), write a program that uses both versions of percolation (provided below) and compute the probability that a system percolates, but does not percolate directed downward, you need N and p from the command line. PercolationProbability: https://introcs.cs.princeton.edu/java/24percolation/PercolationProbability.java percolation: https://introcs.cs.princeton.edu/java/24percolation/Percolation.javaFor Scheduled Job, we can preset a time or an action with this to run the scheduled job: Group of answer choices Job Trigger Timer Preset ScheduleDog.java publicclassDogextendsPet { privateStringbreed; publicvoidsetBreed(StringuserBreed) { breed = userBreed; } publicStringgetBreed() { return breed; } } Pet.java public class Pet { protectedStringname; protectedintage; publicvoidsetName(StringuserName) { name = userName; } publicStringgetName() { return name; } publicvoidsetAge(intuserAge) { age = userAge; } publicintgetAge() { return age; } publicvoidprintInfo() { System.out.println("Pet Information: "); System.out.println(" Name: " + name); System.out.println(" Age: " + age); } } PetInformation.java import java.util.Scanner; public class PetInformation { publicstaticvoidmain(String[] args) { Scannerscnr = newScanner(System.in); PetmyPet = newPet(); DogmyDog = newDog(); StringpetName, dogName, dogBreed; intpetAge, dogAge; petName = scnr.nextLine(); petAge = scnr.nextInt(); scnr.nextLine(); dogName = scnr.next(); dogAge = scnr.nextInt(); scnr.nextLine(); dogBreed = scnr.nextLine(); // TODO: Create…

