The following question supports the attainment of Course Intended Learning Outcomes (CILO): Identify the components, features, characteristics and uses of C++ Language in various applications; and Design computing-based solution using control structures, functions, array and other statements.
The following question supports the attainment of Course Intended Learning Outcomes (CILO): Identify the components, features, characteristics and uses of C++ Language in various applications; and Design computing-based solution using control structures, functions, array and other statements.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter6: Modularity Using Functions
Section6.1: Function And Parameter Declarations
Problem 11E
Related questions
Question
COPY PASTE THE SOURCE CODE
PRINT SCREEN THE OUTPUT
thank you :)
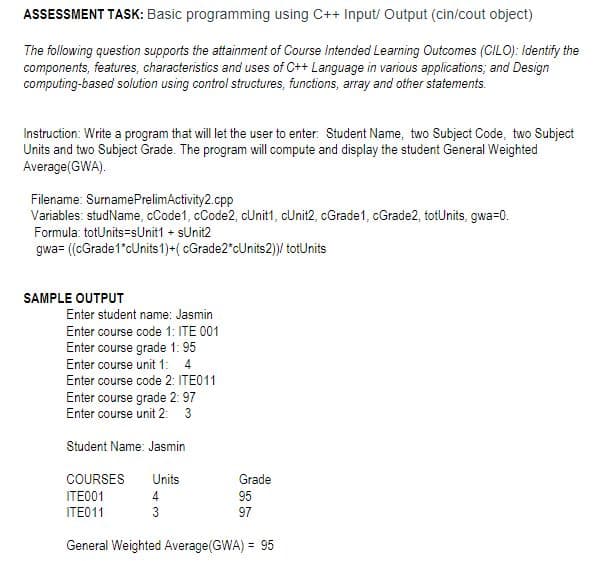
Transcribed Image Text:ASSESSMENT TASK: Basic programming using C++ Input/ Output (cin/cout object)
The following question supports the attainment of Course Intended Learning Outcomes (CILO): Identify the
components, features, characteristics and uses of C++ Language in various applications; and Design
computing-based solution using control structures, functions, array and other statements.
Instruction: Write a program that will let the user to enter: Student Name, two Subject Code, two Subject
Units and two Subject Grade. The program will compute and display the student General Weighted
Average(GWA).
Filename: SurnamePrelimActivity2.cpp
Variables: studName, cCode1, cCode2, cUnit1, cUnit2, cGrade1, cGrade2, totUnits, gwa=0.
Formula: totUnits=sUnit1 + sUnit2
gwa= ((cGrade1*cUnits 1)+( cGrade2*cUnits2)/ totUnits
SAMPLE OUTPUT
Enter student name: Jasmin
Enter course code 1: ITE 001
Enter course grade 1: 95
Enter course unit 1: 4
Enter course code 2: ITE011
Enter course grade 2: 97
Enter course unit 2: 3
Student Name: Jasmin
COURSES
Units
Grade
ITE001
4.
95
ITE011
3
97
General Weighted Average(GWA) = 95
%3D
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning