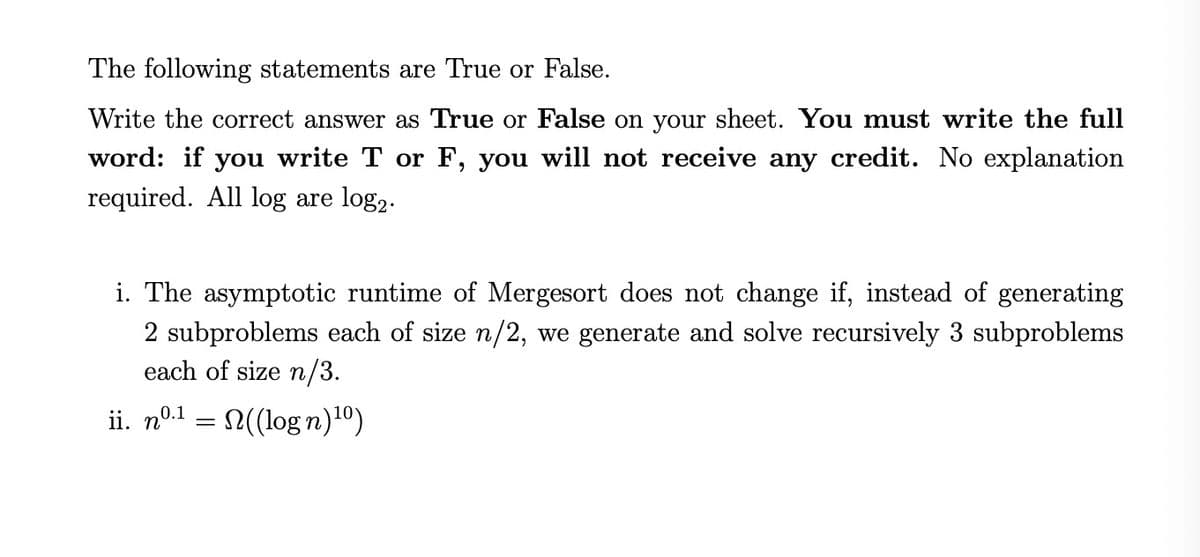
The following statements are True or False. Write the correct answer as True or False on your sheet. You must write the full word: if you write T or F, you will not receive any credit. No explanation required. All log are log,. i. The asymptotic runtime of Mergesort does not change if, instead of generating 2 subproblems each of size n/2, we generate and solve recursively 3 subproblems each of size n/3. ii. nº1 = 2((log n)1º)
Q: Consider a database system for an airline that leverages snapshot isolation. Describe a case in whic...
A: Consider the case of a database for an airline in which the database system makes extensive use of s...
Q: ΡΥTHOΝ Big-O CODING/SOLVING Consider the function below written in Python3: def bar(x, y): if y > 0:...
A: Big O Notation is a way to measure an algorithm's efficiency.
Q: Create the code or a C program and generate the output. A farmer wishes to find the area of his rig...
A: Given Value is : tan A = 3/4 Base = 120
Q: What exactly is the notion of privacy in terms of information security? What distinguishes this defi...
A: Intro Security is all about protecting the data and privacy is safeguarding the user identity. Infor...
Q: Give the complete program of each of the following. 1. Write a program to input eight integer numbe...
A: Note 1 - As per our guidelines, we can provide solution only for one question. Since you have asked...
Q: What are the implications of loading additional features (that might not be necessary for analysis) ...
A: PySpark is one of the interface for Apache Spark in Python. It actively allow python API application...
Q: Can you tell the difference between a slim and a fat client?
A: Introduction : Fat client: It is also called a thick client. It is nothing but software that implem...
Q: 10. Sanguine (symbol Sa) is a fictional name for one of the halogens. According to the naming rules ...
A: The answer of the following according to me is (E).
Q: Write a console application that uses at least five (5) different methods of Math class. Provide a m...
A: Introduction: Write a console application that uses at least five (5) different methods of Math clas...
Q: Write a Python program to find the largest number in a list(size 11) without using built-in function...
A: Required:- Write a Python program to find the largest number in a list(size 11) without using built-...
Q: Explain the following statement with example: "in a project, the communication complexity increases ...
A: In a project, the communication complexity increases with the increase of people working for it" is ...
Q: Write a function prototype and a header for a function named distance. The function should return a ...
A: function body example according to given condition: double distance(double rate, double time){ ...
Q: Explain the ethical difficulties that a business manager must handle or that a firm may encounter, a...
A: Business leaders face ethical issues in accounting, inequality and discrimination, social media and ...
Q: What distinguishes a HashSet from a TreeSet
A: Distinguishing HashSet from a TreeSet
Q: What data type may a 32-bit signed integer be stored in?
A: Please find the detailed answer in the following steps.
Q: Identify the four components of an assembly language instruction.
A: Introduction: The abbreviation for assembly language is "ASM."It is any low-level programming langua...
Q: Establish wireless standards.
A: IEEE 802.11 is part of the technical standards for IEEE 802 Local Network (LAN) sets of protocols fo...
Q: What is one of the most important applications of pre-order traversal in binary search trees?
A: Introduction: The binary search tree is a sophisticated algorithm that analyses the node, its left a...
Q: Explain the ring topology with advantages and disadvantages
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful. Tha...
Q: Binary numbers are inconvenient because they're too long and not easy to read. Write C+ code that co...
A: Here I have created a function named binaryToDecimal(), which takes the input parameter as a binary ...
Q: Should you attempt to adjust your hardware (b
A: Q)Should you attempt to adjust your hardware (by adding drives or RAM) first, or your transactions (...
Q: BFF 2:37 p.m. TODAY 2. Consider the following Java statements. int a = 1, b = 5; x = -(a = 3)b + b-(...
A:
Q: The code to be run is c ... and it is e into a file that is c
A: given - The code to be run is called a........ and it is enteredinto a file that is called a
Q: Computer Science For each of the code snippet given below, identify the error and then write code a...
A: Errors in the snippet: * in the code they haven't specified the buff_size * they haven't used the h...
Q: Write a complete C++ program that prompts the user to entel a string, and prints out a message based...
A: Task :- Write a C++ program to take user input for a string and print the output message accordingly...
Q: How can the concept of data be defined in our neural network model? O variable patterns O variable n...
A: Neural Network model can be defined as the series of algorithm in which it generally points out the...
Q: Consider the following clauses: a. John likes all kind of food. b. Apple and vegetable are food c. A...
A: Step 1: Facts to FOL ConversionWe'll start by converting all of the given statements into first-orde...
Q: explain what a stub zone is and how it might be used
A: Stub Zone It is the copy of a zone that contains only those resource records necessary to identify ...
Q: QUESTION 20 What is the depth of this tree? 100 46 68 12 34 29 QUESTION 21 The time complexity for r...
A: Find the answer given as below : As per company guidelines we are supposed to answer first three que...
Q: Is it wise to provide a user process access to a database system's shared memory area? Explain your ...
A: Introduction: Users accessing the database's shared memory area User databases for clients may be st...
Q: business process works when trying to develop a new information system?
A: given - 3. Why is it so important to understand how a business process works when trying to develop ...
Q: What exactly is RAM? Give examples of two categories. Is it appropriate for storing programmes in em...
A: Introduction: While RAM may seem strange, it is an essential component of computers. In the next fe...
Q: lem #1: Write a program that reads from the user the name of a student, the grades of two midterms a...
A: According to the Question below the solution: Output:
Q: Explain network topologies.
A: Answer: Network topologies define the physical and logical arrangements of links in a network. Two o...
Q: Simplify the expression using Boolean algebra theorem and postulates: F=(X+Z')(Z+WY)'+(VZ+WX')(Y+Z)'...
A: Introduction: Boolean Algebra: It is used to analyze and simplify the digital (logic) circuits. It u...
Q: Make a list of three technologies that have made the transition from analog to digital. What was the...
A: A digital signal is a signal that represents data as a sequence of discrete values at any given time...
Q: What are some of the features of a computer?
A: Introduction: Some characteristics of computers are: 1. speed 2. accuracy 3. reliability 4. automat...
Q: What may be causing connections to stall in state FIN WAIT 2?
A: INTRODUCTION What may be causing connections to stall in state FIN WAIT 2?
Q: Write a Java program to display all the elements of the given array with their index in the output i...
A: Write a Java program to display all the elements of the given array with their index in the output i...
Q: Create a protocol based on timestamps to prevent the phantom effect.
A: In the article, two approaches for dealing with the phantom phenomenon's bemeans of locking are disc...
Q: Refer to the snippet, what gets printed?
A: The $var (single dollar) is a typical variable with the name var that stores any worth like string, ...
Q: Name the four different kinds of RAM that have been discussed in this chapter.
A: Introduction: It stands for Random Access Memory. It is used to efficiently and effectively store an...
Q: When you use a Hadoop installation, you may benefit from the high amount of computational redundancy...
A: A Hadoop installation, you may benefit from the high amount of computational redundancy that it prov...
Q: What exactly is cold booting?
A: Introduction: Cold booting is the process of resuming the regular operation of a computer after it h...
Q: Consider a system that keeps track of people using their names, social security numbers, birthdays, ...
A: Hence the answer
Q: Insert a piece of assembler code into the C-program to calculate the sum of two variables. Tip: You...
A: A assembler is a program which takes basic computer program or instructions than it converts them in...
Q: Not only for information technology system development, but for all endeavors. Is logical process mo...
A: The detailed requirements of an application system are modelled using a logical level process model....
Q: Flowchart 1 Download starting file: SecretWordPartial.fprg Submit completed file: SecretWord.fprg In...
A:
Q: Design and implement a class representing a circular sorted linked list. The class must have the fol...
A: Introduction Solve it in Standard Template Library (STL) Design and implement a class representing a...
Q: Create a recursive function in C++ to compute the power of a positive integer.
A: To write C++ program to compute the power using recursive function.
Step by step
Solved in 2 steps

- Which is the base case of the following recursion function: def mult3(n): if n == 1: return 3 else: return mult3(n-1) + 3 else n == 1 mult3(n) return mult3(n-1) + 3Which of the following statement(s) is/are correct about recursion? Group of answer choices A.indication of good use of recursion: difficulty to trace down the sequence of recursive calls B.gives cleaner code but has high cost C.never be used as substitute for a simple ‘for’ loop D.bad idea to use it to evaluate simple mathematical functions. E.All of the aboveGiven a positive integer 'n', find and return the minimum number of steps that 'n' has to take to get reduced to 1. You can perform any one of the following 3 steps:1.) Subtract 1 from it. (n = n - 1) ,2.) If its divisible by 2, divide by 2.( if n % 2 == 0, then n = n / 2 ) ,3.) If its divisible by 3, divide by 3. (if n % 3 == 0, then n = n / 3 ). Write brute-force recursive solution for this.Input format :The first and the only line of input contains an integer value, 'n'.Output format :Print the minimum number of steps.Constraints :1 <= n <= 200 Time Limit: 1 secSample Input 1 :4Sample Output 1 :2 Explanation of Sample Output 1 :For n = 4Step 1 : n = 4 / 2 = 2Step 2 : n = 2 / 2 = 1 Sample Input 2 :7Sample Output 2 :3Explanation of Sample Output 2 :For n = 7Step 1 : n = 7 - 1 = 6Step 2 : n = 6 / 3 = 2 Step 3 : n = 2 / 2 = 1 SolutionDp///.
- case #5 int i , p =1; for(i=1;i<=n;i++) p = p*i case #6 int rec(int r) { if(r==0) return 1; else return r*(rec(r-1); } Compare the two methods (#5 and #6 above) and answer the following: What is the “stopping” case for each (what causes the methods to “end”)? How do you guarantee that the methods will “stop” (infinite loop, infinite recursion)? Which method one is “better”? Why?The Tower of Hanoi is a puzzle where n disks of different sizes arestacked in ascending order on one rod and there are two other rods with nodisks on them. The objective is to move all disks from the first rod to thethird, such that:- only one disk is moved at a time- a larger disk can never be placed on top of a smaller oneWrite a recursive function that outputs the sequence of steps needed tosolve the puzzle with n disks.Write a test program in C++ that allows the user to input number of disks andthen uses your function to output the steps needed to solve the puzzle.Hint: If you could move up n−1 of the disks from the first post to thethird post using the second post as a spare, the last disk could be moved fromthe first post to the second post. Then by using the same technique you canmove the n−1 disks from the third post to the second post, using the firstdisk as a spare. There! You have the puzzle solved. You only have to decidewhat the nonrecursive case is, what the recursive…Given is the code to print numbers from 1 to n in increasing order recursively. But it contains few bugs that you need to rectify such that all the test cases pass.Input Format :Integer nOutput Format :Numbers from 1 to n (separated by space)Constraints :1 <= n <= 10000Sample Input 1 : 6Sample Output 1 :1 2 3 4 5 6Sample Input 2 : 4Sample Output 2 :1 2 3 4.
- Remove the left recursion from the productions: S ->A a |b A ->A c |S d | €The sorted values array contains the sixteen integers 1, 2, 3, 13, 13, 20, 24, 25, 30, 32, 40, 45, 50, 52, 57, 60. How many recursive calls are made by our binarySearch method given an initial invocation of binarySearch(45, 0, 15)? A. 3. B. 1. C. 4 D. 2. E. 0 A recursive definition is a definition (choose the best answer): A. that is recursive. B. in which something is defined in smaller terms of itself. C. which uses a mathematical equation. D. where a base case is defined. E. that repeats itself. Recursion is implemented by the system: A. using run time storage allocation. B. using static storage allocation. C. using a single static "stack frame". D. using compile time storage allocation.Choose the correct one for the following recursive method when n is 3 int recursiveSum(int n) { if (n==0) return 0; return n+recursiveSum(n-1); } a. First and Last recursive call share the same copy of parameter n in memory. b. Every recursive call shares the same copy of parameter n in memory. c. There will be a separate copy of parameter n in memory for each recursive call. d. none of these e. Only First and Last recursive call have separate copies of parameter n in memory.
- Please solve the following recursion question in Java.The goal is to rewrite the function, below, such that passes in a different list of parameters, particularly eliminating the need to pass low and high for each recursive call to binary_search. defbinary_search(nums,low,high,item): mid=(low+high)//2iflow>high:returnFalse #The item doesn't exist in the list!elifnums[mid]==item:returnTrue# The item exists in the list!elifitem<nums[mid]:returnbinary_search(nums,low,mid-1,item)else:returnbinary_search(nums,mid+1,high,item) The new function should be prototyped below. The number of changes between the given version, and the one requested is not significant. defbinary_search(nums,item):pass# Remove this and fill in with your code Tip: If you consider that high and low are used to create a smaller version of our problem to be processed recursively, the version requested will do the same thing, just through a different, more Pythonic technique.The Binary Search algorithm works by testing a mid-point, then eliminating half of the list. In this exercise, you are going to take our binary search algorithm and add print statements so that you can track how the search executes. Inside of the recursive binary search function, add print statements to print out the starting, ending, and midpoint values each time. Then as you test a value, print out the results, either too high, too low, or a match. Sample Output Starting value: 0 Ending value: 9 Testing midpoint value: 4 Too high! Starting value: 0 Ending value: 3 Testing midpoint value: 1 Too low! Starting value: 2 Ending value: 3 Testing midpoint value: 2 Match!

