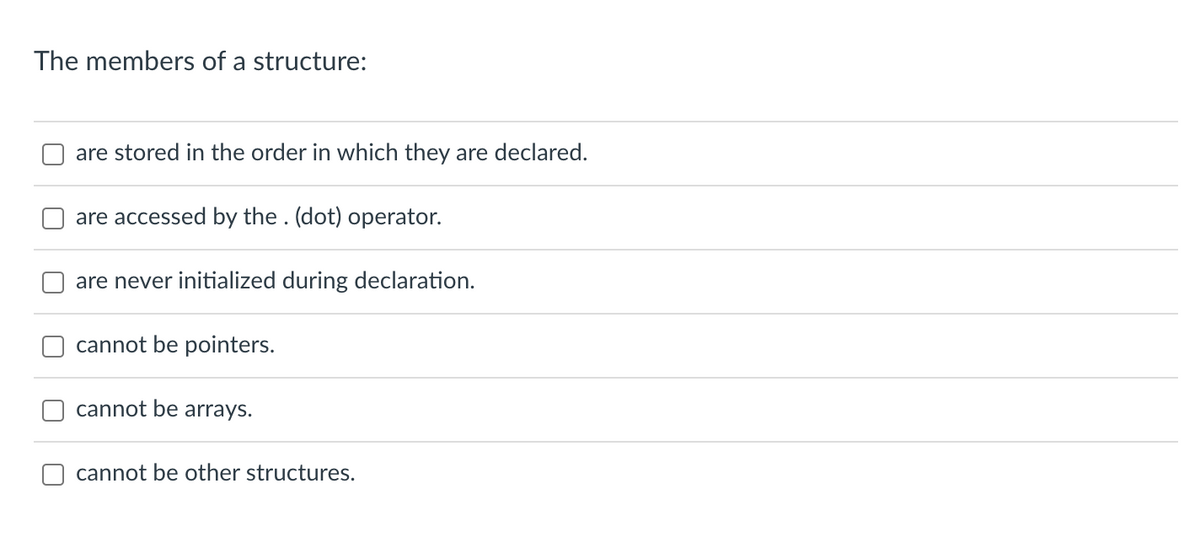
The members of a structure: are stored in the order in which they are declared. are accessed by the. (dot) operator. are never initialized during declaration. cannot be pointers. cannot be arrays. cannot be other structures.
Q: The operations are: 1. Add an "H" to the list 2. Add an "I" to the list 3. Add "100" to the list 4.…
A: Here is the completed program to perform the given operations on a linked list:
Q: Provide two benefits of implementing virtualization on a network as a networking technology.
A: Virtualization is a technology that allows the creation of multiple virtual machines (VMs) on a…
Q: A prescription drug firm has asked for your assistance in repairing a network issue that affects a…
A: In order to keep track of information while you are programming in any given programming language,…
Q: What are the risks and ramifications of a cyber security breach for a business?
A: A cyber security breach can have serious risks and ramifications for a business, both in terms of…
Q: Project managers use webcams for what?
A: WEBCAMS- Webcams have made it possible to have live, face-to-face conversations over the Internet,…
Q: To what end do the various parts of a computer system contribute?
A: The answer to the question is given below:
Q: Define and describe the Software Development Life Cycle as it applies to building software for a…
A: SDLC: The Lifecycle of Software Development is a systematic procedure for constructing software that…
Q: What are the many types of cyber attacks and what defines a breach in cyber security?
A: Cyber security is the practise of defending computer systems, servers, mobile devices, electronic…
Q: What method should I use to place nodes into a data structure to assure that insertion, deletion,…
A: To ensure that insertion, deletion, and searching have a temporal complexity less than O(n), you…
Q: Use this psuedocode to write python code of the Floyd-Warshall Algorithm. Please show all the code…
A: We have to write python code of the Floyd-Warshall Algorithm. BY using the given psuedocode.
Q: When comparing serial and parallel bus data transmission, what are the advantages and disadvantages…
A: Serial and parallel are two different methods of transmitting data over a bus, which is a set of…
Q: DigitalArts is a video gaming service that offers subscription-based access to online video games.…
A: To analyse sales performance for DigitalArts, we need to gather and analyze data related to the…
Q: Machine Problem #2. Write a method-oriented Java program that asks the user to input two numbers and…
A: Step-1: StartStep-2: Declare variable num1, num2 and take input form the userStep-3: Declare…
Q: How is it that an assembler can build whole binary code with only one pass through the source file?…
A: A binary code is a two-symbol scheme that can be used to represent writing, instructions for a…
Q: Why should we worry about information system management and technology?
A: Information system management and technology are essential components of modern organizations, and…
Q: n values of actions that were det las permanent and transient des
A: Introduction: In the context of structural engineering design, actions refer to the loads or forces…
Q: technological advancement
A: As of 2023, we are living in a time of rapid technological advancement. The past few decades have…
Q: Remove all errors from the C++ program given below asap. #include using namespace std; int main(){ }…
A: Algorithm: Declare two variables, sum_o and sum_n, and initialize sum_o to 0 and sum_n to 20. Start…
Q: How are the Standard Access List and the Extended Access List different from one another? How is the…
A: Hello student Greetings Hope you are doing great. Thank You!!!
Q: What are the three distinct types of database critical events that have the potential to trigger the…
A: Given that there are numerous questions, we shall address the first one. If you want a response to…
Q: In the event of a breach of data or cybersecurity in the healthcare industry, what are the most…
A: In the event of a breach of data or cybersecurity in the healthcare industry, the most desirable…
Q: xplain the problems that arise from using serial proce
A: Introduction: Mobility, Maintainability, Reachability, and Simplicity are the inherent features of a…
Q: Make it very obvious what each unit is responsible for, as well as how they communicate with one…
A: Introduction: Arithmetic-logic units (ALUs) and control circuits make up its components,…
Q: As the data packet moves from lower levels to higher ones, the headers are added at the appropriate…
A: The process of adding headers as a data packet moves from lower levels to higher ones is known as…
Q: Explain the steps that are involved in the conversion and changeover of data.
A: Methods for data conversion and transformation: In the field of computing, system implementation…
Q: Who decides how an organization uses data?
A: Organization the executives is the expertise of bringing people together on a common platform and…
Q: Where will the hardware and software necessary for the network's physical and virtual connections be…
A: The hardware necessary for the network's physical connections will typically be stored in a data…
Q: Do you prefer runtime or compile-time error detection
A: IntroductionErrors are an unavoidable part of software development. They can be detected in two…
Q: Will biometrics use encrypted data? When it comes to biometric technology, what part does…
A: The act of encrypting a communication entails transforming the text of the message into a format…
Q: Is it possible to "hack" something? Is it possible to defend oneself from being a victim of hacking?
A: Hacking is an effort to attack an internal computer system or private network. As described, it is…
Q: Please provide a list of the three most prevalent sorts of mistakes that the checkerboard pattern…
A: MBIST Methods Special algorithms are used to evaluate memories and find any flaws that may be…
Q: The Fibonacci series: 0, 1, 1, 2,3,5,8,13,21... begins with terms 0 and 1 and has the property that…
A: The program is written in C Language. Please find the source code and output in the following steps
Q: Which architectural pattern is the most appropriate for computer systems in which one component…
A: MVC architecture pattern is most suited for applications in which information is generated by one…
Q: e) Find the moment of inertia of a hollow cylinder about the axis of the cylinder using a JAVA…
A: Program,explanation and output snapshot is given below
Q: Create at least 3 scenarios (for Google ) using different keywords like Background, Scenario…
A: The three scenarios are:
Q: Create a remark on video files based on your own comprehension of the content.
A: Video The video consists of a series of moving pictures, maybe accompanied by music. Multimedia…
Q: Explain the infrastructure of the business intelligence.
A: Business intelligence, or BI, is the method of providing the appropriate info to the appropriate…
Q: Where will the hardware and software necessary for the network's physical and virtual connections be…
A: INTRODUCTION: Networking hardware, or simply "network devices," are the physical components that…
Q: An explanation of the design values of actions that were determined for the UK design, EQU ultimate…
A: The answer is discussed in the below step
Q: What Linux package management have you tried or considered? Why is it better?
A: Below is the complete solution with explanation in detail for the given question about some of the…
Q: I want to run a C code in Linux. for(int i - 0; i <= degrees; i++) { It is saying to use the option…
A: Solution: Given, I want to run a C code in Linux.for(int i - 0; i <= degrees; i++) {It is…
Q: What should be considered before choosing a DBMS?
A: Choosing the right Database Management System (DBMS) is crucial for the success of your project, as…
Q: What are the key features of Domain Specific Software Architecture?
A: A domain specific software architecture is defined as a set of software components that are tailored…
Q: Write a new viterbi function to calculate the most likely path of a sequence given A, E, and I matri…
A: Here is a Python implementation of the Viterbi algorithm to calculate the most likely path of a…
Q: What are the telltale signs that someone is passively smelling something dangerous, and how can you…
A: Sniffing is a technique for monitoring and collecting all data packets passing through a particular…
Q: Gluconeogenesis is stimulated by elevated amounts of NADH in the liver, which is a necessary step in…
A: Gluconeogenesis is a complex metabolic pathway that allows the liver to synthesize glucose from…
Q: How may one illustrate abstraction in object-oriented programming with the help of a number of…
A: Definition Abstraction: The process of concealing the specifics of how something is implemented and…
Q: Which architectural pattern is most suitable for software systems in which one component generates…
A: The architectural pattern that is most suitable for software systems in which one component…
Q: Show the memory address range (i.e., the first address and the last address) for the 64×8 PROM chip?…
A: To find the memory address range for a 64x8 PROM chip, you need to determine the number of…
Q: Is there a distinction between the many types of firewall architecture?
A: A network security system called a firewall monitors and regulated incoming and outgoing network…
select all options that applies
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Structures, like any other type, may have their own set of pointers. Structures that nest Returning Structure from a Function Structures' pointers Structure of the dataFor accessing a structure element using a pointer, which of the following must be used? (A) Arrow operator (→) (B) Separate the codes code from the constant (C) Delimit a section of (D) Show what code goes in a particular functionWrite program in C. Create a structure called Studentsthat holds information likeRegistration code, name of student and date of admission. Write a program tocreate an array of structures and enter some data into it (15 records at least). Then ask the user to enter current date. Display the names of those Students who are in the school greater than or equal to 5 years.
- The Answer should be in C++ language. please answer it fast my previous questions were answered after due date Write a program to define four structures with structure variables of array types. Enter data into each structure variable that has four records and each record contains five fields.Create a pointer to a Rectangle structure and define it. Assume the structure declaration below exists. Rectangle Structure { length int; width int; };A structure is a collection of values with dissimilar data types, while an array stores values of similar data types. Required: Create a structure to store the student ID, name, course and age in years. Create an array of the above structure to accept and display the values of 5 students.
- In C programming language Question (Array of Structures) a) Write a program that declares a structure student with the following data members; Name (String) RollNo(Integer) CGPA(Float) b) Create an array s1 of 5 elements in main function of type structure student c) Initialize all the structures stored within array. d) Print all array contents.Complete C++ the program provided to read football statistics into a structure array, offers a menu to update statistics, print data, and update a file. The program declares a struct to store the data of a football player and has the following data members. The structure in the header file provided: Name Position Number of Touchdowns Number of Catches Number of Passing Yards Number of Receiving Yards Number of Rushing Yards An array of the structure with 30 components is declared to store the data of football players. A function is provided to open the input file. A function skeleton is provided to read the data in the file “footballdata.txt” into the structure array. An Integer function is provided to search the structure array to find the index of a specific player. A function has been provided to using the index returned from the search, print all information for a player using the index returned from the search. A function has been provided to print all data for all players. A…Declare a student structure that contains : Student's first and last nameStudent IDCreate the following functions: getStudentInfo(void) Declares a single student, uses printf()/scanf() to get inputReturns the single student backprintStudentInfo(student_t *st_ptr) Takes the pointer to a student (to avoid making a copy)Prints out all of the student informationDeclare an array of five studentsUsing a for loop and getStudentInfo() function, get input of all the studentsUsing a for loop and printStudentInfo() function, print all the output of all students.
- Create a structure called Students that holds information like Registration code, name of student and date of admission. Write a program to create an array of structures and enter some data into it (15 records at least). Then ask the user to enter current date. Display the names of those Students who are in the school greater than or equal to 5 years. Note: Use C languageCreate a structure called Students that holds information like Registration code, name of student and date of admission. Write a program to create an array of structures and enter some data into it (15 records at least). Then ask the user to enter current date. Display the names of those Students who are in the school greater than or equal to 5 years. Note: Using C languagec++ programming language given the following variable declaration: double avg; write the required commands to declare a pointer, and then use it to display the value of the variable avg.



