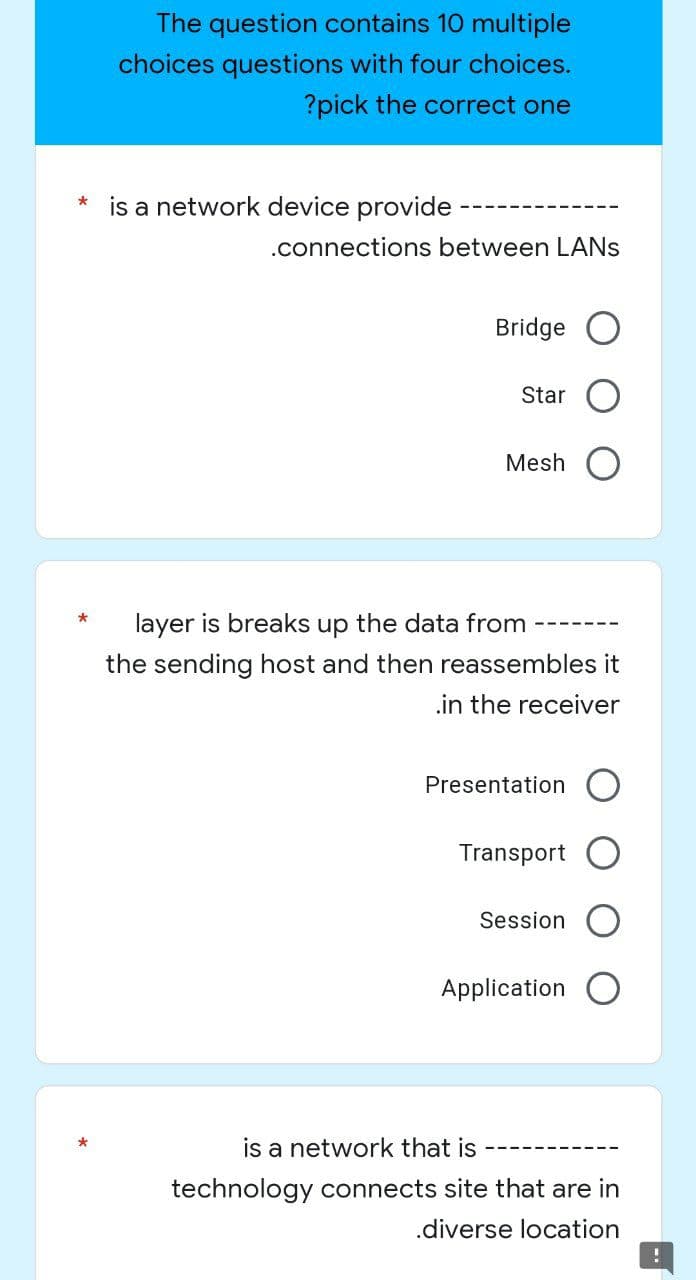
* is a network device provide .connections between LANS
Q: array-based unbounded queue implementation.
A: To implement a queue…
Q: When people talk about Linux being a "distribution," what exactly do they mean?
A: Answer: The term is Linux distribution (or distro in short structure) in light of the fact that an…
Q: What exactly are sequence access files and where can I get them?
A: A sequence access file is a file that contains the next sequence of bytes from a file. By…
Q: The traditional Software Development Life Cycle has been used in a number of fruitful system…
A: It is a given that, according to the findings of the annual State of the Agile report, the Agile…
Q: What Cyber threats or problem of computer have you already encountered? Cite atleast three. Explain…
A: Introduction: Network security specialists should have a thorough understanding of the following…
Q: Using your own words, describe the problems that can arise from engaging in plagiarism in technical…
A: Answer: ConsequencesThe act of passing off the work of another person as one's own is known as…
Q: Explain the various kinds of database queries and transactions.
A: Given: Big data is characterized by two fundamental characteristics: speed and variety. 1.…
Q: In terms of programming, it is preferable to have a deeper level of access rather than a shallower…
A: Intro Creating a series of instructions that describe to a computer how to carry out a task is…
Q: computer science - What are the various stages of test management?
A: Answer: Test management process separates into a few phases which incorporate test analysis, test…
Q: Describe the network monitor 3.1 programme, including its features and the many sectors in which it…
A: Intro Network Monitor 3.1 software: Microsoft's Unclick software. *Download, install, and run are…
Q: Describe what social networking, online discussion groups, and online chat rooms are, as well as how…
A: Solution: Social networking is a platform that allows people to interact with their friends,…
Q: What are the key distinctions between the operating systems found on a mainframe and a laptop? In…
A: Given: What's the difference between a mainframe operating system and one for a laptop?In what ways…
Q: First, you should define and describe the components of the core of the operating system that are…
A: Introduction: Components of the Operating System's Kernel that Make Up the Operating System The…
Q: How is computer forensics different than data recovery?
A: The above question is solved in step 2 :-
Q: Where can I get the finest software deals?
A: Introduction: These days, a great deal of software may be obtained free of charge.
Q: Discuss the increasing amount of dangers emanating from within an organisation, as well as the…
A: Introduction: Insider threats are dangers that might come from inside an organization's workforce.…
Q: Provide some concrete examples of the top five most typical applications of system design and…
A: The whole response is provided below: 1. Simulation and Production The popularity of simulation…
Q: Explain the importance of firewalls in terms of the security offered by networks and the internet.…
A: Fencing your property protects your house and keeps trespassers at bay; similarly, firewalls are…
Q: It is essential to provide an explanation of how a challenge–response authentication system operates…
A: Define: How likely is the challenge answer? Question and answer are used to verify a challenge's…
Q: It is crucial to keep track of the technological advancements that have become significant in your…
A: Technology is everywhere: Humans are reliant on technology. You like calculators, save friends' and…
Q: there a specific reason why an operating system must always have a microkernel? In many ways, the…
A:
Q: Why does hashing a file that includes user passwords make more sense than encrypting the passwords…
A: If the hashed password is compared against y, and if y = h(x), then the user is validated, and the…
Q: Consider the benefits and disadvantages of sequential search algorithms against binary search…
A: Solution: Algorithm is, in fact, a step-by-step procedure. Without jumping, a sequential search…
Q: In the context of the fields of business and information technology, please provide two instances of…
A: information technology is defined as the user computers, physical devices, infrastructure, store,…
Q: ways to make the protection of personal information more effective?
A: Methods for enhancing data privacy include:- 1) Keep your data source (computer, mobile) virus-free:…
Q: Consider these five critical ethical issues concerning computer systems.
A: Intro The five moral dimensions of information systems are as follows: 1. Responsibilities and…
Q: Having all of a company's data and information maintained in one area presents a number of issues,…
A: Answer: Data redundancy happens when similar piece of data is put away in at least two separate…
Q: Explain the outcomes of Information and Communications Technology (ICT) in relation to their…
A: Introduction: In order to communicate, generate, bar, store, and manage data, schools use a wide…
Q: How exactly can businesses go about analyzing the various cloud solutions available?
A: When evaluating cloud technologies, companies should take a number of factors into consideration,…
Q: When you speak about the goals of authentication, can you be more specific about what you mean?…
A: Servers use authentication when they need to know who is accessing their data or website and when…
Q: What are some of the things that you may put in the abstract for the purpose of developing your own…
A: The question has been answered in step2
Q: By examining their similarities and differences, unstructured data and structured data may be…
A: Given that: Compare and contrast unstructured and structured data to determine which kind of data is…
Q: Analyze and have a conversation about the many approaches to artificial intelligence. Provide…
A: Introduction Analyze and have a conversation about the many approaches to artificial intelligence.…
Q: Do you anticipate any difficulties in the sphere of healthcare relating to the sharing of data as a…
A: Big Data: Data is the fuel for the majority of enterprises nowadays; data is increasing with time;…
Q: Discuss a situation in which you had difficulty interpreting numbers (Information). What are some…
A: What are the obstacles to comprehending the data? The framework The extent The proportions (in…
Q: In order to show the five applications for system design and modeling that are used most often,…
A: Encryption: System Design encompasses design, modelling, and simulation services that allow rapid,…
Q: Authentication is put to use for a wide range of reasons; what are some of the more typical…
A: Authentication: Servers will employ authentication to identify who is accessing their data or…
Q: To further demonstrate the five most common uses of computer-aided system design and modeling,…
A: System Design: System Design encompasses a wide range of design, modelling, and simulation services…
Q: To what extent is it necessary to maintain the privacy of one's personal information? List five…
A: What is the definition of data confidentiality? Create a list of five ways to safeguard your…
Q: In the case of a security breach, how does your company intend to communicate information?
A: Intro provided - What are the company's policies for disclosing information in the event of an…
Q: a. Assume the following 32-bit binary represents a floating-point number using single precision IEEE…
A:
Q: How can one get application software in the most efficient manner? In your answer, you should…
A: The above question is solved in step 2 :-
Q: Give an example of how each of the three big data characteristics pertains to the data that…
A: Introduction: The term "Big Data" refers to a large volume of data that may be structured,…
Q: If you delete a file by accident and then later decide that you want it back, what steps should you…
A: Here we have given a brief note to get your files back in windows system. You can find the solution…
Q: What is the term that is used to describe the part of the process of problem solving that requires…
A: Given that: The subject is the phrase for the element of issue solution that is judgmental or…
Q: The repercussions of technological advancement include the erosion of societal values and the…
A: A decent utilization of innovation is one which works on human physical, mental, profound, and moral…
Q: Where can I upload music, photos, and movies to the internet?
A: Introduction: Many things all over the world have been altered as a result of the proliferation of…
Q: Discuss the protection of personal information and the many ways in which it may be made more secure
A: There isn't anything more significant than keeping your own data secure with the goal that you can…
Q: Write statements that perform the following one-dimensional-array operations in C#: a) Set the three…
A: ANSWER:-
Q: What are the different relational operators used in selection structures in the Python programming…
A: Find the required answer given as below : As per company guidelines we are supposed to answer only…
Step by step
Solved in 2 steps

- Which of the following is not an issue addressed by Spanning Tree Protocol? Select one: a. Gateway redundancy b. Broadcast storms c. Constant updating of the MAC filter table d. A device receiving multiple copies of the same frame1. Which of the following layer is a combination of application, presentation, and session layer in the TCP/IP reference model? a. Transportb. Physicalc. Application d. Network 2. What is the network that tpically interconnects devices with network capabilities located anywhere on earth? 3. How are the interactions between a user and a service provider ecpressed as an abstract representation? 4. What is the size of MAC Address? 5. What is the RFC? a. a database of internet service b. a numeric linking system used by your text c. a numeric listing of TCP/IP protocols d. A tracking system for network development requirements. 6. Which transmission mode should be used to send information from a single point to another point? 7. A LAN typically interconnects devices located where? 8. Which of the following is characteristic of the TCP Address?Connectionless, bidirectional, authenticated, unreliable? 9. An element of the WWW protocol is:Java, Javascript, xml, html 10. A service provided by…What distinguishes the three protocols known as Simple Mail Transfer Protocol (SMTP), Post Office Protocol (POP), and Internet Message Access Protocol (IMAP) when it comes to sending and receiving electronic mail over the web? To provide a complete picture, it's helpful to describe the agents on both the sending and receiving nodes.
- When it comes to electronic mail sent over the web, what key distinctions can be identified between the three protocols known as Simple Mail Transfer Protocol (SMTP), Post Office Protocol (POP), and Internet Message Access Protocol (IMAP)? Describe the agents on both the node transmitting the data and the node receiving the data to provide a full picture of the situation.Using an example from your own school, please explain what happens when a student surfs to www.google.com on their laptop while it is connected to the school's LAN. Incorporate routing within the same AS, as well as ARP, BGP, DHCP, DNS, and HTTP, in the proper order?Create a network map based upon the below specifications: Build a LAN (1 switch, 5 PC's, 3 servers, an access point, Firewall/Router, and a cloud to represent the internet)
- Imagine you are the network administrator of University X having ? campuses in Towson, Maryland. Youwant to build a connected network of servers (each server is either a regular or a routing one), one at each campus,and want to choose some of them to be the designated routing servers. A routing server will serve regular servers whoconnect directly to it via high speed cables, and every regular server must connect to at least one routing server. Yourgoal is to minimize the total length of high speed cable that you must purchase. Given the geographic locations ofthe ? campuses, design a plan that requires (1) the shortest length of cable and (2) the least number of routing servers.Analyze the time and space complexity of your procedure.Using an example from your own school, please explain what happens when a student surfs to www.google.com on their laptop while it is connected to the school's LAN. Including, sequentially, routing inside the same AS, ARP, BGP, DHCP, DNS, and HTTP?i. Describe the steps invloved in a distributed coordination function using a simple carrier sense multiple access algorithm with interframe space delay to transmit frames in a wireless LANii. Describe the four abstraction layers of TCP/IP iii. Descrive a typical scenarion invloving 2 Computer Devices transferring a video file using an unsecured ftp connection where TCP three-way handshake is susceptible to vulnerabilityiv. Describe four units that makes IEEE 802.11 Architiecture
- 11.Which of the following is not the standard producing organization? IEEE ITU IETT ANSI 12.Which is the largest network when the networks are classified according to their size? MAN LAN PAN SOHO 13.Which one is the subnetmask for class B IP address? 255.0.0.0 255.255.255.0 255.255.0.0 255.255.255.255 14.Which one is true for Go-Back-N protocol ? In case of errors, receiver sends negative acknowledgement for the packet with error. There is no buffer area in the receiver The packets reach to the receiver without any errors. The packets are received in the order that they send 15.For the device with IP address 194.80.26.110 , what is the network address ? 255.255.255.0 194.80.26.110 194.80.0.0 194.80.26.0THINKING CRITICALLY Which of the following hosts on a corporate intranet are on the same subnet? a. b. c. d.q16- A network has grown too large for technicians to configure network addresses. Which application layer service should be added to the server to allow this needs to be satisfied dynamically? Select one: A. DNS B. HTTP C. DHCP D. SMTP

