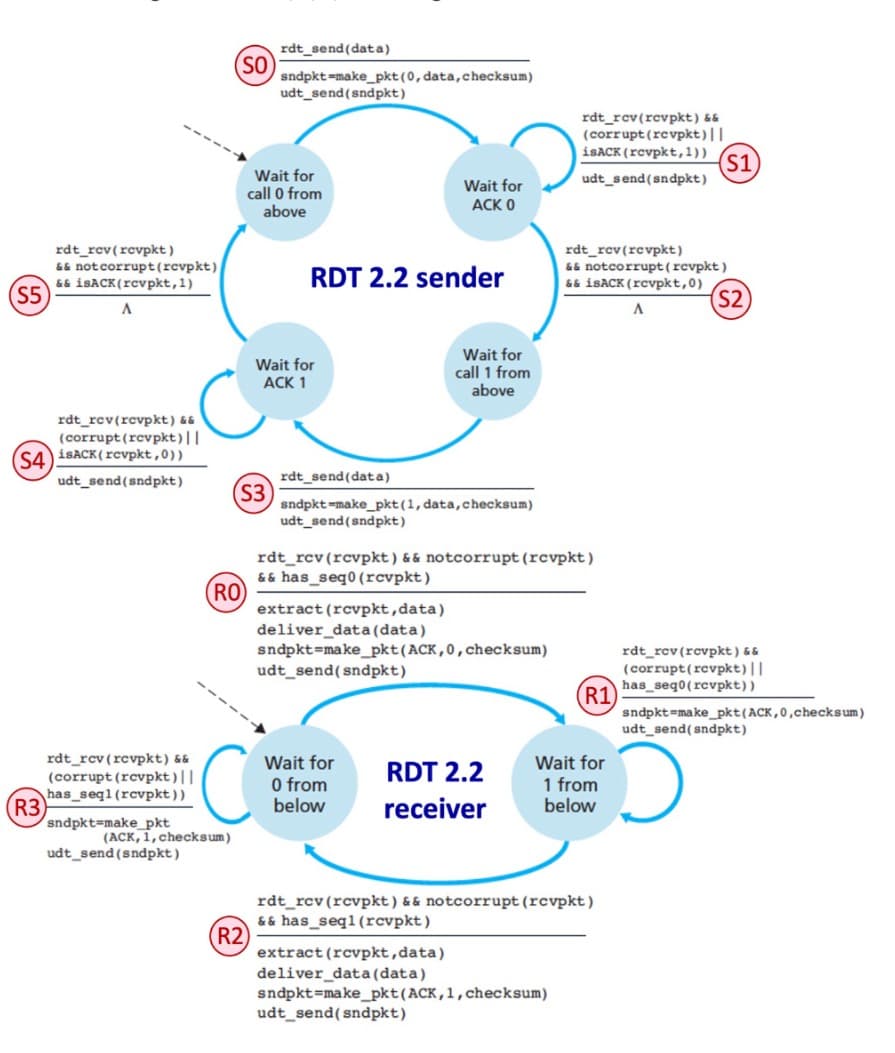
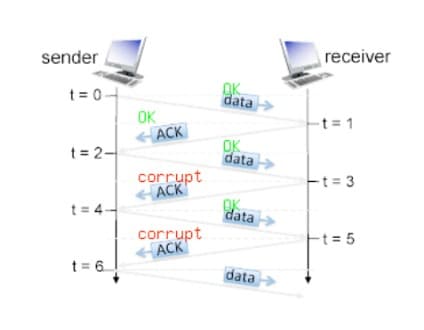
The RDT 2.2 protocol. Consider the rdt 2.2 sender and receiver below, with FSM transitions labeled in red. Also consider the sender and receiver timeline following the FSMs, where a green OK label indicates a message that is not corrupted, and a red corrupt label indicates a message that is corrupted. We are interested in the sequence number (0 or 1) of a data message, and the ACK number (0 or 1) of an ACK message for the messages sent at t= 2, 3, 4, 5 in the figure below. Which of the following sequences of interleaved data sequence numbers and ACK numbers corresponds to those in the messages sent at t=2 (data sequence number); t=3 (ACK number), t=4 (data sequence number), and t=5 (ACK number)? Only one sequence is correct. explain 1, 1, 1, 1
The RDT 2.2 protocol. Consider the rdt 2.2 sender and receiver below, with FSM
transitions labeled in red. Also consider the sender and receiver timeline following the
FSMs, where a green OK label indicates a message that is not corrupted, and a red
corrupt label indicates a message that is corrupted. We are interested in the sequence
number (0 or 1) of a data message, and the ACK number (0 or 1) of an ACK message for
the messages sent at t= 2, 3, 4, 5 in the figure below.
Which of the following sequences of interleaved data sequence numbers and ACK
numbers corresponds to those in the messages sent at t=2 (data sequence number); t=3
(ACK number), t=4 (data sequence number), and t=5 (ACK number)? Only one sequence
is correct. explain
1, 1, 1, 1
0, 0, 0, 0
1, 0, 1, 0
0, 1, 1, 0
1, 1, 1, 0
1, 1, 0, 1
1, 0, 0, 1
1, 0, 1, 1
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images









