The result of the logic gate is * A A BC+AB+AB AB+AC +ABC ĀC+ABC+AB O BC+AB+ABC CO
Q: The sequential and binary search algorithms each have their own set of benefits, but what are the gu...
A: Let's see the solution in the next steps
Q: Explain the importance of e-commerce security and encryption.
A: eCommerce security These are the rules that govern safe internet transactions. It has measures in p...
Q: The following table is in 1NF. Convert it to 2NF using proper notation:
A: Facilitator (FacilitatorID, LastName, FirstName, Street, City, ZipCode, (ForumNum, ForumDate, Custom...
Q: Find the Histogram and Negative of the following 8-bits Image
A:
Q: Consider the following subtraction operation assuming the values are in S2C form and select the corr...
A:
Q: g through multi-dimensional arrays, functions, function overloading Instructions: 1) Write a S...
A: the code is an given below :
Q: A memory location might be sequential or direct. Why do key gadgets utilize direct access now? How c...
A: Your answer is given below in detail with explanation. Introduction :- Sequential access, often kn...
Q: Write a function combine(names, ages) that takes in two lists, names and ages and returns a list of ...
A: Given :- Write a function combine(names, ages) that takes in two lists, names andages and returns a ...
Q: MASM ASSEMBLY include irvine32.inc .data ARRAY word 205, 89, Please write a program segment i...
A: Actually, program is an executable software that runs on a computer.
Q: In a normal database context, there should be at least nine unique subjects to address.
A: Introduction: The DBMS software works as a wrapper around the database, storing, reading, and updati...
Q: Explain protected mode briefly.
A: Introduction: the question is about explaining protected mode briefly. and here is the solution in t...
Q: What is a learning system? Give an example of a learning system and explain
A: A learning system is basically an assortment of antiques that are 'united', in a proper way, to esta...
Q: 3 Proof Prove or disprove that the context-free languages are closed over the reverse operator, i.e....
A: We want to show that if L is a context-free language, then LR is a context-free language. So let G b...
Q: Q3 In the IPv4 Header format following information is given in decimal number system , with respect ...
A: Lets see the solution in the next steps
Q: How is Binary Heap usually implemented?
A: NOTE :- Below i explain the answer in my own words by which you understand it well.
Q: What is the function of en able an input multiplexer chip 2 a To apply Vec (2) To connest graunc/
A: the answer is an to active the entire chip
Q: Decision making can only be made through "intuitive" decision process. true or false?
A: We are going to see if intuitive is the only process for decision making.
Q: Describe two applications that might be better suited to assembly language than than a high-level la...
A: Applications that suited to assembly language:
Q: What are the benefits of data mining?
A: Let us see the answer:- Introduction Data mining is the process of examining massive volumes of data...
Q: All leds are on at the beginning. Bit 6’s button OR Bit 7’s button has to pressed. Second step: Bit ...
A:
Q: Why is top-down data security superior than bottom-up data security?
A: Introduction: The top-down strategy has the benefit of allowing choices to be made and executed rapi...
Q: What are the steps for making a list?
A: Introduction: Lists, like other HTML5 components, are simple to create:
Q: C++language
A: Program Code: #include<iostream>#include<string.h>using namespace std;main(){ char p[30]...
Q: What is the definition of an information system? Define and describe in your own terms.
A: Introduction: An integrated set of components for collecting, storing, and processing data as well a...
Q: not sure what you mean when you say "operating systems for resource-constrained devices." Explain it...
A: Solution:-
Q: A camera rental shop has heard about your expert software engineering skills and wants help with a p...
A: Actually, given question regarding class diagram.
Q: Explain the various ways for implementing integrity controls to ensure database security.
A: Introduction: Data integrity is an important aspect of information security that is handled by integ...
Q: Example-3: Write a program to calculate the Area and volume for a sphere. Sol. -The area of sphere =...
A: Given: The program is written in C language to find area and volume of sphere.
Q: Guice is a dependency injection library that is commonly used in the Java programming language. Howe...
A: In order to enable multiple configurations, an application or class must be able to independently bu...
Q: A local pizza shop is selling a large pizza for $9.99. Given the number of pizzas to order as input,...
A: import java.util.Scanner; public class LabProgram{ public static void main(String[] args) { Sc...
Q: Processor P has 2 real CPUs A and B. Each of these CPUs has one silicon hyperthread HA and HB. Two s...
A: Answer: Given Process P has CPUs A and CPUs B Hyper thread HA and HB Software threads T1 and T2
Q: Deep learning. Implement the Forwardpass and backwardpass from scratch with math equations. Plot ...
A: Note: Code has been developed in r studio software. Follow my screenshot to avoid errors in code. I ...
Q: What does it mean to encode a signal?
A: Hello student Greetings Hope you are doing great. Thank You!!!
Q: Explain two reasons why a national educational technology standard is required.
A: National Educational Technology Standards(NETS) are now known as the International Society for Techn...
Q: If I am building a circuit in Logisim, how would I use a single left shifter component to compute a ...
A: In the software development model, necessities are kept on the left side of the arrangement, and the...
Q: Q4 17. Determine the output expression of the LUT for the internal conditions shown. Suppose input A...
A: An LUT (Look Up Table) contains storage cells that are used to. implement small logic functions. Eac...
Q: Describe the downsides of the OSI Model.
A: Introduction :- The International Organization for Standardization (ISO) developed the open systems ...
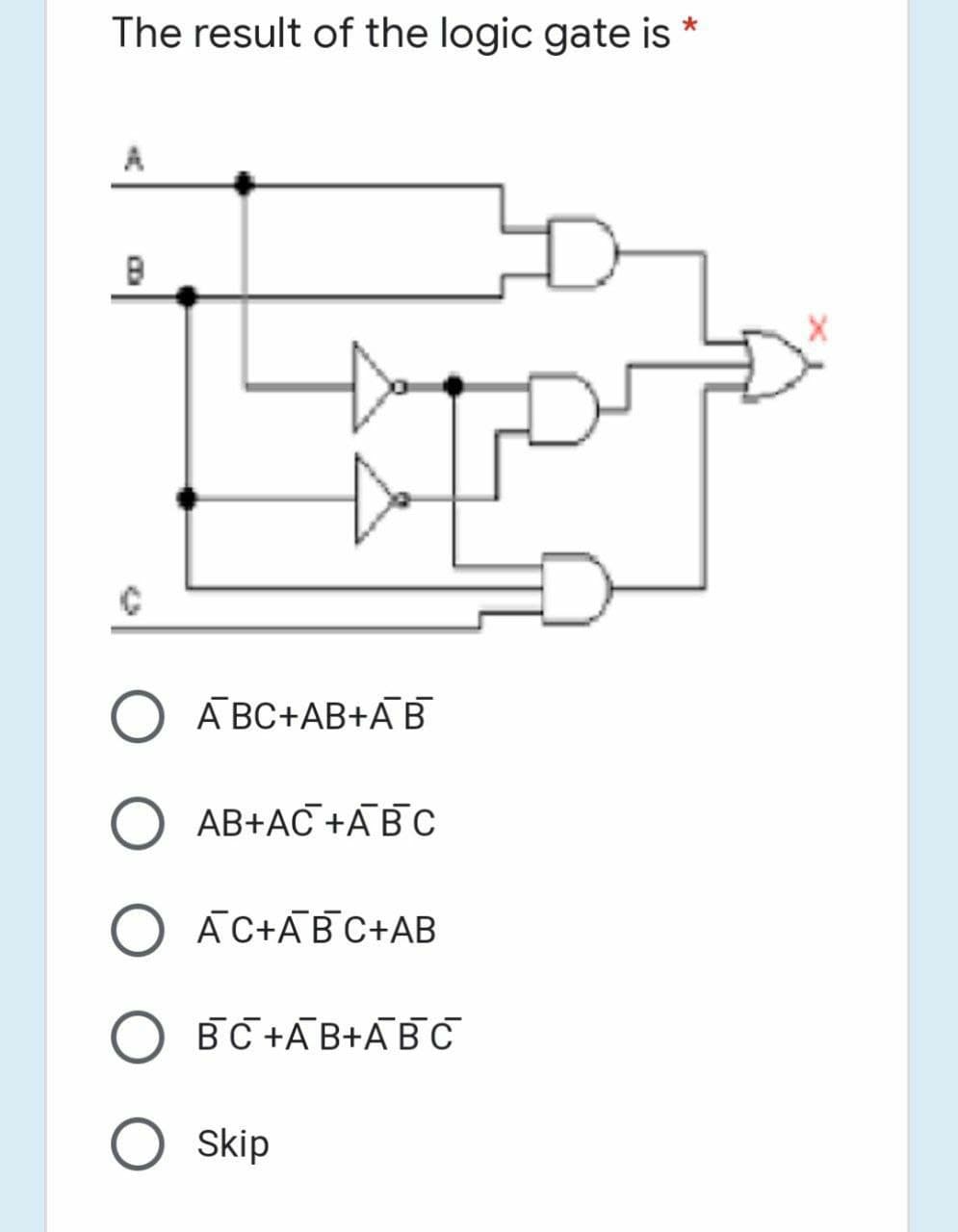
Q: The result of the logic gate is A
A: A'BC+AB+A'B'
Q: Is there a built-in JAVA method that accepts two arrays as parameters and returns true if both array...
A: Introduction: Is there a built-in JAVA method that accepts two arrays as parameters and returns tru...
Q: Write a program that uses a switch statement as follows: If game contains the letter p , or P the fu...
A: C++ Program: #include <iostream>using namespace std; // Function print the words Play Station ...
Q: program to implement and solve the N-queens problem using heuristic A* Algorithm
A: /* Java program to solve N Queen Problem usingbacktracking */public class NQueenProblem { final int ...
Q: The following strcopy.function uses the C++ traditional pointer-based array declaration for its para...
A: source code #include<iostream> using namespace std; void strcopy(char dest[], const char src...
Q: keys 53, 27, 75, 25, 70, 41, 38, 16, 59, 36, 73, 65, 60, 46, 55, 33, 68, 79, and 48 build a balance...
A: Each node stores at most 3 valuesEach internal node is a 2-node, 3-node, or 4-nodeAll the leaves are...
Q: Assume you apply a functional dependence in the BCNF decomposition technique to deconstruct a relati...
A: Intro Assume you apply a functional dependence in the BCNF decomposition technique to deconstruct a ...
Q: Explain the process through which computers represent data.
A: INTRODUCTION: Computers' storage units are capable of storing enormous amounts of data. Each charact...
Q: Q15. What is the first (rightmost) digit in the expansion base 6 of 82?
A: Ans: The first (rightmost) digit in the expansion base 6 of 82 is 4.
Q: c) Given graph G=(N,E), where N is the set of routers and E is the set of links. Using Dijkstra's li...
A: Here, we are going to calculate the least cost path from Node U to all others and also will show the...
Q: Assume you have a client who has never utilized a network. Explain the function of network servers a...
A: Introduction: Client-Server Architecture is a computer architecture in which the server hosts, provi...
Q: How is it possible for Wireshark to automatically extract the Network Interface Card vendor from the...
A: answer is
Q: Find the first address, last address and the number of addresses of a network whose one of the IP ad...
A: Let's see the detailed solution in the next steps
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- If a two-input logic gate produces an output of logic HIGH, only if both inputs are different, then the logic gate IC isIC 7432O IC 7486IC 7400IC 7408Q4 Draw logic gates for the function F. F (A, B, C, D) = (B'D) (A'+ C°D) + (BC'+ D'A)A combinational circuit is defined by the following three Boolean functions. Design the circuit with a decoder and external gates. F1 = x' y' z' + xzF2 = x y' z' + x'yF3 = x' y' z + xy
- A 1bit 4 to 1 multiplexer, the 4 inputs of the multiplexer will be the output of another combinational circuit with A and B as an input:00 = 1bit Adder01 = 1bit Subtractor10 = 1bit Comparator (equals)11 = XOR • truth table• Boolean Expression• Logic Circuit Here is the truth table guide:Negative OR Gate is 0 IC 7400 O IC 7432 O IC 7408 OIC 7402A combinational circuit has 3 outputs F1, F2 and F3. Design the circuit with a decoder and external gates.
- The output of a two - input nand gate is HIGH , when the any of inputs areThe combinational logic circuit required for this system is only 4x1Design using data selectors (mux) and logic gatesThe following circuit is: a. 2-input Static CMOS nor gateb. 2-input Static CMOS nand gatec. 2-input Dynamic CMOS nand gated. 2-input Dynamic CMOS nor gate

