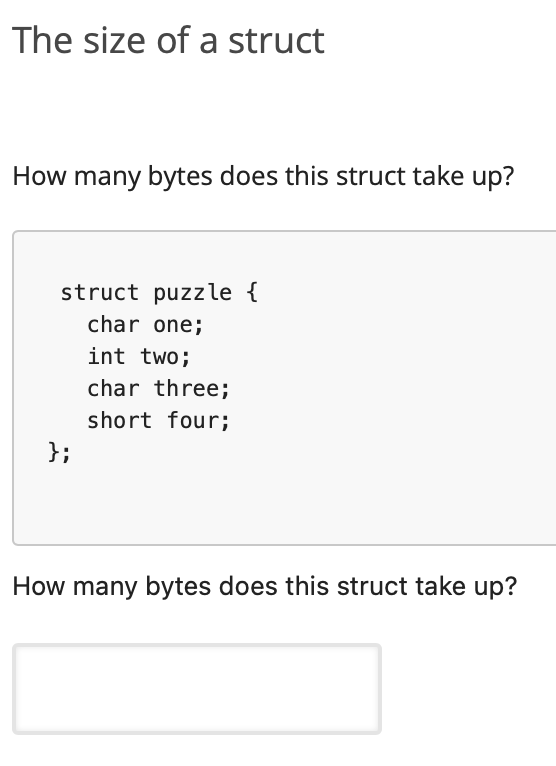
The size of a struct How many bytes does this struct take up? struct puzzle { char one; int two; char three; short four; }; How many bytes does this struct take up?
Q: In this session, we will discuss the idea of testability before quickly outlining the compiler.
A: Testing software is a collection of processes used to determine the completeness and quality of…
Q: What six factors do you think should encourage someone to learn more about compilers and how they…
A: Compilers: A compiler is a software tool that transforms a program from one type of computer…
Q: Activation is a way for instantly bringing remote things into a server (that is, when a client calls…
A: The remote object activation service provides support for persistent remote references that can be…
Q: What does the phrase "information security governance" imply specifically, and can you provide five…
A: Given: In the context of a business, "information technology" (IT) refers to the interconnected and…
Q: List the personal safety rules for the computer.
A: A computer is a digital electronic machine that can be programmed to automatically perform a set of…
Q: Question 1 You are staying in one of the last remaining Great Houses built during the 1700s in the…
A: Answer: The treasure is buried under the flagpole. Solution and explanation in step 2
Q: Take a look at your computer's info. Find and note an illustration of each of the following terms: A…
A: Threats can steal or damage data, interfere with business, or otherwise cause harm. You must be…
Q: 12. What is the function of mode set register in 8257?
A:
Q: use case put order object, create a multilayer sequence diagram. Make sure the design takes into…
A: According to the question, we have to create a multilayer sequence diagram. which takes into…
Q: 2. Create a JSON file named invoice.json and write into it the following diction invoice_dict = {'…
A: Question given: According to the question: We need to Read this file in the dictionary here and…
Q: 4. Write this portion of the code correctly: int x; Switch{x}; case 0; printf("zero"); case 1;…
A: The correct code is given in the below step Happy to help you ?
Q: Describe the procedure for achieving the project's advantages. Discover and describe the five…
A: Project's Advantages. Any given project of interest ought to have certain advantages that makes it…
Q: What is Key bouncing? 1
A:
Q: Avoid relying just on performance to support your case for why deep access is preferable than…
A: The response is Justification: Deep Access: Maintaining a stack of active variables is the…
Q: What kind of ethical conundrum may data brokers produce?
A: Data Brokers: Data brokers are associations that assemble or get data from various associations,…
Q: What benefits may information technology bring to the classroom? What impact does IT have on…
A: Information technology It is the utilization of any PCs, storage, organizing, and other actual…
Q: Explain why deep access is superior from a programmer's point of view, rather than merely claiming…
A: Introduction: Dynamic scope allocation rules are used for non-block structured languages. At…
Q: Problem 1: Given the dataset produce the following tables: a. A table where all rows (samples) with…
A: The Python codes for each question a, b, c, d are given below with code and output screenshot Happy…
Q: What purpose do communication protocols serve, and which one or ones did your department choose?
A: The network protocol which refers to an established with the set of rules that are used to determine…
Q: I am looking for Coral assistance and nothing wlse please. Write a program that first reads a list…
A: Step-1: Start Step-2: Declare an array arr of size 5 and variable searchValue Step-3: Take input for…
Q: What is the function of the repquota command in Linux? Explain. What distinguishes this command from…
A: Please find the detailed answer in the following steps.
Q: Technology is developing at a dizzying speed, which ensures continued upheaval. Talk about any five…
A: Given:- The state of technology is undergoing tremendous transformations, and this trend will almost…
Q: What exactly does someone mean when they claim they have "system security"?
A: Introduction: Protection of the system: It is a method that can protect the secrecy of the operating…
Q: Objectives: Use an Input, Processing and Output (IPO) chart to create a flowgorithm program meeting…
A: The answer below has been developed in a clear step-by-step manner.
Q: How, in your opinion, should the security of data be ensured throughout storage and transportation?…
A: Introduction: Data must be encrypted in order to be protected while it is being used or being…
Q: What does the phrase "information security governance" imply specifically, and can you provide five…
A: computer technology (IT) Computer systems, which often involve networking and telecommunications,…
Q: What safety measures do you believe are absolutely necessary to implement in order to secure…
A: Data security prevents unwanted access to and tampering with data at every step. Data security is…
Q: What safety measures do you believe are absolutely necessary to implement in order to secure…
A: Answer is
Q: Sample program that illustrates the use of scope within a program.
A: Given: A sample program demonstrating the usage of scope within a program.
Q: How does vector imaging operate? What is it? Give an illustration to illustrate your argument. What…
A: In vector pictures, lines, curves, circles, rectangles, and another primary, bold forms are all…
Q: What exactly distinguishes overfitting, underfitting, and generalizing, and when should each be…
A: In machine learning one of the most common tasks is to fit a model to a set of training data, so as…
Q: When someone claims that their company has "many processes," what does it really mean? Is there a…
A: Answer to the given question: A company has many processes that can be an action or set of…
Q: Please write a concise and clear explanation for the following: There are three different ways to…
A: Given: briefly provide three techniques for enhancing audio files for the web.
Q: What does the American digital divide look like in relation to the global digital divide?
A: Digital Inequality An electronic divide is any unequal distribution in the access to, use of, or…
Q: What steps would you take to troubleshoot an error code? What sources do you use to look for…
A: The steps would you take to troubleshoot an error code.
Q: Create a JSON file named invoice.json
A: Given, To create a JSON file named invoice.json and write into it the following dictionary : Read…
Q: Why is it crucial to have a thorough grasp of both the present and future architecture of our system…
A: Cyber attacks: Having a security strategy for a firm primarily serves the purpose of enhancing and…
Q: Examine the Android Toolbar's usage in light of the most recent API update. Written entirely in your…
A: Definition: Toolbar is a ViewGroup type that may be inserted in XML task formats for Android…
Q: Describe the benefits and drawbacks of a SWOT analysis.
A: Strength: Strengths are the aspects of a company that are seen to be crucial for a project's…
Q: What impact does data mining have on people's security and privacy?
A: Data mining: Data mining is a technique that involves exploring and analysing new information from…
Q: Before a compiler can produce code that is trustworthy and effective, a lot of factors need to be…
A: Factors in which the number of passes to be used in a certain compiler include the…
Q: Create a C++ program to build a linked list containing names. The user should enter as many names as…
A: C++ code is below:
Q: Copy-paste code below and save it as XHTML (with extension .xhtml). Find and fix as many errors in…
A: Given data is:- here you have an incorrect code of the HTML page which is <DOCTYPE HTML PUBLIC…
Q: Please provide a brief summary of any two of the aforementioned choices. What prospective uses for…
A: An information system is a carefully planned set of parts that are used to gather, exchange, store,…
Q: my flow chart look for this.
A: in the following section we will be drawing the flowchart for the given python program
Q: When it comes to programming, having access to more information is preferable than having fewer…
A: Start: Deep/shallow binding makes sense when a procedure may be offered as an argument to a…
Q: Evaluate the six core processes? Are there better ways to execute a project? Are the six core…
A: Answer is
Q: What three conditions must a network meet in order to function correctly and effectively? Give one a…
A: Given: Which three requirements must be satisfied by a network in order for it to operate…
Q: Where does the necessity for access restrictions originate in the modern world? Please be sure to…
A: A security technique called access control restricts who or what may access resources in a computer…
Q: What does the naming convention std stand for?
A: In computer programming, a variable is an abstract storage space paired with an associated symbolic…
I know I need to utilize sizeof() and possibly a pointer, but I can't seem to get the syntax right (this is using C). To find the size of this struct in bytes.
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 2 images

- Transcribed Image Text JAVA Programming Problem: In the game of "Assassin's Creed", you control a ship with a cannon which is attacking a large enemy Assassin's Creed, armed with many guns. Your goal is to destroy as many of the guns as possible. The battle field is a 2D Cartesian grid, where your cannon is located at the origin. The enemy Assassin's Creed is a horizontal line segment located from the coordinates (X1, Y) to (X2, Y). There are exactly (X2 - X1 + 1) guns on the ship, located at the integer points (X1, Y), (X1+1, Y), ..., (X2, Y). However, the problem is, you cannot always fire at a gun. There are supernatural rocks located at all points of the battlefield whose X and Y coordinates are both integers. In order to fire successfully at an enemy's gun, the line connecting your cannon and that gun must not go through any rocks. Develop a JAVA code to output the number of the enemy battleship's guns that your cannon can destroy. Test Case Result 1 2 2 -2Develop Method in java which can find the smallest and the largest value from integer int[] TwoExtreamValue(int A[]). Develop Method in java which can sort integer array using bubble Int[] SortArray(int A[]). Vector Multiplication Using two integer Arrays o int VectorMultiplication(int A[],int B[]).Java programming pls A complex number is a number in the form a+bi, where a and b are real numbers and i is √(-1) The numbers a and b are known as the real part and imaginary part of the complex number, respectively. You can perform addition, subtraction, multiplication, and division for complex numbers using the following formulas: a + bi + c + di = (a+c) + (b+d)i (addition) a + bi − (c + di) = (a−c) + (b−d)i (subtraction) (a + bi) * (c + di) = (ac−bd) + (bc+ad)i (multiplication) (a + bi) / (c + di) = (ac+bd) / (c2+d2) + (bc−ad)i / (c2+d2) (division) You can obtain the Absolute Value for a complex number using the following formula: |a + bi| = √(a2 + b2) A Complex number can be interpreted as a point on a plane by identifying the (a,b) values as the coordinates of the point. The absolute value of the complex number corresponds to the distance of the point to the origin, as shown in the example below. (1) Design a class named Complex for representing…
- Problem Description: The international standard letter/number mapping found on the telephone keypad is shown below: Write a pseudocode and program that reads a letter and displays its corresponding digit. 2 3 1 ABC DEF 4 5 6 GHI JKL MNO 7 8 9 PQRS TUV WXYZ 0 Write a pseudocode on how you would solve the problem in your own word. Write a java program called Phone considering the following directions. Practice here first then write answer on the answer sheet. Also, make sure distinguish high and low caps as Java is case – sensitive. Import and declare a Scanner class Ask user for an Upper – case letter Use the switch statement along with case and break Use the System.exit(1) in the default to terminate the program Print the corresponding digitthis is java languege code please right it as a code please just codeIn Java, Arrays are made up only of numbers. True or False
- in c# Write a console app that inputs a sentence from the user (assume no punctuation), then determines and displays ONLY THE DUPLICATE words in alphabetical order. Treat uppercase and lowercase letters the same. [Hint: You can use string method Split with no arguments, as in sentence.Split(), to break a sentence into an array of strings containing the individual words. By default, Split uses spaces as delimiters. Use string method ToLower before calling Split.]Please help with this c++ problem Assignment 6 - Monkey Food In the Gaddis textbook read Chapter 8 sections 8.1-8.9 before starting this assignment. This assignment is Programming Challenge 4 from Chapter 8 of the textbook. A local zoo wants to keep track of how many pounds of food each of its three monkeys eats each day during a typical week. Write a program that stores this information in a two-dimensional 3 x 7 arrray, where each row represents a different monkey and each column represents a different day of the week. The program should first have the user input the data for each monkey from the keyboard. The number of pounds of food eaten by one monkey in one day should be a floating-point value. Input Validation: Do not accept negative numbers. Then your program should create a report that includes the following information: A nicely-formatted table with a row for each monkey and a column for each day of the week showing the amount of food eaten by that monkey on that day. Be…Java programming Problem-3 There are two sorted arrays A and B. First one is of size m + n containing m elements and another one is of size n and containing n elements. Merge these two arrays into the first array of size m + n such that the output is sorted. Hints: Trick is to start filling the destination array from the back with the largest elements.
- Question: Write a program to Simulate a game of tic tac toe. A game of tic tac toe has two players. A Player class is required to store /represent information about each player. The UML diagram is given below. Player -name: string -symbol :char Player (name:string,symbol:char) getName():string getSymbol():char getInfo():string The tic tac toe board will be represented by a two dimensional array of size 3 by 3 characters. At the start of the game each cell is empty (must be set to the underscore character ‘_’). Program flow: Your program must ask for each player’s name and their special symbol or character (usually an ‘X’ or ‘O’). Display each player’s name and symbol. The program must then display the board (the 2 dimensional array). The player whose turn it is has their name displayed and is asked for a row and column number to place their symbol. They can enter -1 -1 as the row and column number to quit. Repeat 2 and 3 until one player enters -1 -1. Your…1. Design a java application that outputs a table with a list of at least 6bstudents together with their first name, last name, score and grade in the following format. First name last name score grade 2 Write a program by entering two integer numbers of your choice and make sure your program works properly. When you are readyvto submit your project enter 24 and 53 as set values and generate 100 random numbers to makecsure all of these numbers are generated within the range of [24.....43] inclusive. Please I need help to write the programs. ThanksCan help in java String [] names = {"Dimo Ivanov", "Yani Yanev", "Ana Popova", "Nelly Angelova"}; 1. Display the array in the console using the Arrays.toString () method 2. Display the names and the number of characters in the name (without the space) as a table (use printf) Name Number of lettersDimo Ivanov 10 3. Get an array first_letters of type char [], containing the first letters of the names. Display it with Arrays.toString () 4. Get the arrays of names and surnames containing initial and second names, respectively (first determine the position of the space in the previous name with the indexOf () method of the String class). Display the arrays. 5. Sort the first_names array

