The TCP/IP _layer is equivalent to combined session, presentation, and application layers of the OSI model. data link network physical application
Q: When data is transmitted from device A to device B through the Internet protocol stack, the fifth…
A: The above statement is false. When data is transmitted from device A to device B through the…
Q: Protocols for the transport layer The difficulties that arise naturally from using TCP and UPD in…
A: Introduction: Transport layer protocols typically handle point-to-point communication, which…
Q: the combi
A: Structural testing is a sort of "white box" testing in which a calculation or code is utilized.…
Q: Protocols that operate at the transport layer level. The difficulties associated with the use of TCP…
A: Transport layer protocols: The Transport layer is in charge of establishing an end-to-end connection…
Q: This section explains the distinction between network applications and application layer protocols…
A: The OSI model's top layer, which some people assume refers to using apps like MS Word, Notepad, and…
Q: The transport layer major protocols are TCP and UDP. Give a justification of why an application…
A: Transmission Control Protocol (TCP) is connection-oriented, meaning once a connection has been…
Q: What is the difference between the data plane and the control plane of the network layer?
A: There are many different things that make up the control plane. These are the things that decide…
Q: TCP/IP application layer refers to the OSI model's session, presentation, and application layers…
A: The TCP/IP model is a simplified version of the OSI model. This model contains four layers, as…
Q: When contrasted to connection-based protocols, the advantages and disadvantages of connectionless…
A: Intro This question explains about compared to connection-based protocols, connectionless protocols…
Q: The connection process between network devices in a physical layer is only point- to -point True…
A: Computer networking refers to interconnected computing devices that can exchange data and share…
Q: Compare and contrast connectionless vs connection-based protocols.
A: The Answer is
Q: The TCP/IP application layer is the name given to the combined session, presentation, and…
A: TCP/IP application: The Transmission Control Protocol/Internet Protocol (TCP/IP) is a set of…
Q: The distinction between network applications and application layer protocols is explained in detail…
A: Lets see the solution.
Q: The next sections go over network applications and application layer protocols in detail.
A: An application layer is a kind of abstraction layer that defines the common communication protocols…
Q: TCP/IP application layer refers to the OSI model's combined session, presentation, and application…
A: Explanation:-Structural testing is a kind of "white box" testing in which an algorithm or code is…
Q: the architecture of the TCP/IP protocol suite
A: Given :- The term TCP/IP or Transmission Control protocol / Internet Protocol suite and the OSI…
Q: TCPIP layer corresponds to the OSI models to three layers O Transport O Presentation O Session O…
A: TCP/IP APPLICATION layer corresponds to the OSI models to three layers.
Q: Transport layer functions are implemented primarily at the interconnecting devices in the network. A…
A: Ans: True Transport layer functions are implemented primarily at the routers and switches in the…
Q: The Internet Protocol (IP) protocol offers a function known as "best effort." Describe the services…
A: The IP( Internet Protocol) is the fundamental communications protocol in the Internet protocol stack…
Q: The following sections of this document go over network applications and application layer protocols…
A: Introduction: Any programme that operates on a single host and communicates with another programme…
Q: The next sections describe network applications and application layer protocols in further depth.
A: The network applications are the lifeblood of a computer network. If we couldn't conceive of any…
Q: The following sections describe the difference between network applications and application layer…
A: The outermost seventh layer of the Open Systems Interconnect (OSI) Model is the highest layer, also…
Q: Protocols that work at the transport layer. The issues connected with using TCP and UPD in modern…
A: Given: Layer 3 or the Network layer employs IP or Internet Protocol, a connectionless protocol that…
Q: 1. State six(6) functions accomplish at the transport layer of the TCP/IP model.
A: Transport Layer is the second layer of the TCP/IP model. It is an end-to-end layer used to deliver…
Q: a) Identify within the TCP/IP protocol suite, all the layers that can have either circuit switching…
A: What is TCP/IP?TCP/IP stands for Transmission Control Protocol/Internet Protocol and is a suite of…
Q: Draw a message passing diagram for the message exchanges between the IOT device and the data server…
A: Architecture:-
Q: a network layer that deals with media * .access control addressing physical layer network layer data…
A: Answer: Third option is correct. data link layer
Q: The sections that follow explain the distinction between network applications and application layer…
A: Introduction: An application layer is the OSI Model's outermost and seventh layer, and it is the…
Q: a network layer that deals with media * .access control addressing physical layer network layer data…
A: The OSI model's data link layer is made up of two sublayers such as the Media Access Control (MAC)…
Q: What are the main responsibilities of the Network layer in the TCP/IP protocol suite? The protocols…
A: The Network Layer's primary function is to provide connectivity. At Layer 3 of the Open Systems…
Q: Compare the advantages and disadvantages of connectionless protocols to those that require a…
A: Introduction: A connectionless protocol demonstrates communication between two business endpoints in…
Q: Network applications and application layer protocols are discussed in further detail in the next…
A: A network application is any program that runs on a single host and communicates with another…
Q: What are Interior Gateway Protocols?
A: Interior gateway protocols (IGP): The IGPS are routing protocols used inside the independent…
Q: Contrast the layered architecture of IoT with the TCP/IP approach.
A: The TCP/IP stack is a new addition to the OSI (Open-Systems-Interconnection) architecture. It really…
Q: Further discussion of network applications and application layer protocols will be provided in the…
A: Network Application: Any programme operating on one host that communicates with another application…
Q: (Information technology and computer networking) Explain the similarities and differences between…
A: Introduction: When network difficulties hinder IP packet delivery, ICMP (Internet Control Message…
Q: What are Exterior gateway protocols?
A: The protocol which is used to exchange net-reachability information between Internet gateways…
Q: What is the transport layer (TCP/IP stack)?
A: GIVEN: What is the transport layer (TCP/IP stack)?
Q: TCP/IP transport protocols are those that operate on the network's "transport" layer. The use of TCP…
A: The tranport layer along with their protocols udp and tcp is well defined in the given page
Q: Subject - Data Communication Networks Q4) 4. In TCP, ECE and CWR flags are used for congestion…
A: let us see the answer:- Introduction:- TCP (Transmission Control Protocol) is a network protocol…
Q: As the message enters the data link layer, it is defined in O a. Segments O b. Frames OC Packets O…
A: Please find the answer below :
Q: Network applications and application layer protocols are discussed in length below.
A: Network applications:- New applications are needed to support network functions as they become…
Q: Transport layer protocols are protocols that operate at the transport layer. The challenges…
A: Introduction: Protocols for the transport layer
Q: Explain the meaning of TCP connection. Does the notion of TCP connection contradict the fact the…
A: TCP (Transmission Control Protocol): This is a connection oriented protocol and is used at the…
Q: The subsequent sections differentiate between network applications and application layer protocols.
A: The application layer is the seventh: And final layer in the OSI Model. It is also known as the…
Q: The OSI model's session, presentation, and application levels are together referred to as the TCP/IP…
A: TCP/IP entails the collection and management of packet transport, media access, session interaction,…
Step by step
Solved in 2 steps

- TODO 1: To determine how many extra columns or features were added as a result of the one-hot encoding, obtain the form of the one hot df. Put the output into the one_hot_df_shape variable. # TODO 1 one_hot_df_shape = print(f"Shape of one_hot_df is: {one_hot_df_shape}") todo_check([ (one_hot_df_shape == (517,30),'one_hot_df shape did not match (517, 30)') ]) Expected output:How would the following string of characters be represented using run length encoding? What is the compressionratio? AAAABBBCCCCCCCCDDDD hi there EEEEEEEEEFFQuestion 5 You are given a cover image with the following nine bytes of data. Hide the payload 110101000 in the cover image. How many bits did you have to change? 11010011 00001111 00110011 10101010 00110010 01010101 10010010 00010001 10010011 Full explain this question and text typing work only thanks
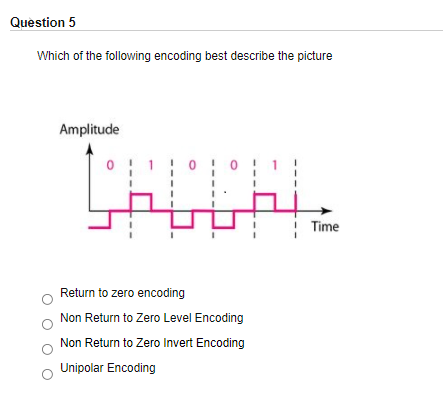
- Which of the following encoding methods does not provide for synchronization? a. NRZ-L b. RZ c. NRZ-I d. Manchesterthe main different between normalization to Standard interval and Normalization to zero mean O The interval range of normalize value brightness and over darkness in an image in local image O contrast adjustment wight and black color No one above The command imshow in MATLAB use to O display image O display color O display intensity O No one aboveCHOOSE THE CORRECT OPTION If each pixel of an acquired image is represented by 11 bits, the number of distinct gray intensities that are available in the image is given as A. 2048 B. 2047 C. 1023 D. 1024
- a) How many bits would be needed to store a photo with 256 pixels horizontal and 256 pixels vertical using 64 grey levels? b) How many bits would be needed to store an audio music on a CD that can play for 3 hours?Using any of the following programming languages, design the interface and write the required code to build a simple image compression application. After selecting any raw "grey-scale" image, your program should output a compressed version of the input image. This simple interface should only apply DCT and Quantization to compress the selected image. You should consider the following in your code: - The transformation process should be done using the Discrete Cosine Transform (8x8 block size). - The user must be able to choose either a coarse quantization or fine quantization. - After the quantization process is applied, rescaling and IDCT should be applied inorder to display the compressed image. In addition to your code, you are requested to submit a documentation that illustrates your application and discuss the results. Suggested programing languages: Matlab, Python, Java, Visual C#Suppose you are one of the hobbyists trying to decrypt the encoded message on the sculpture, and one of the lines on the sculpture is written: PSTEN OITNS ASCNO YRSOI EEIFO MRKIY YNTTM 2.1 Assuming it was recently learnt that Sanborn used double columnar transposition with keys APPLE and FARAD respectively when encrypting message inscribed on the sculpture. Decrypt this message
- Please write a MIPS code to draw the below shape on a bitmap display. Consider the square to have m size and draw the two black diagonal lines inside the square as shown. Please keep it simple and do it as a MIPS code on bitmap display. thank youYou are requested to perform image compression using Huffman coding. You have 6 possible symbols {a1, a2, a3, a4, a5, a6}. The probability for each symbol is [0.15, 0.25, 0.05, 0.05, 0.4, 0.1,0,0]. Create the Huffman code for the following sequence: {a1, a3, a3, a4, a2, a5, a6, a7, a8}. Calculate the average word length of the 8 possible symbols. Calculate the coding efficiency.Which of the following are true regarding signal processing in C. The list of supported signals is usually defined in signal.h. Many of the signals can be caught by using the raise() function to assign a handler. There exist some signals that cannot be caught. A program's ability to perform signal processing increases the likelihood better witten software.

