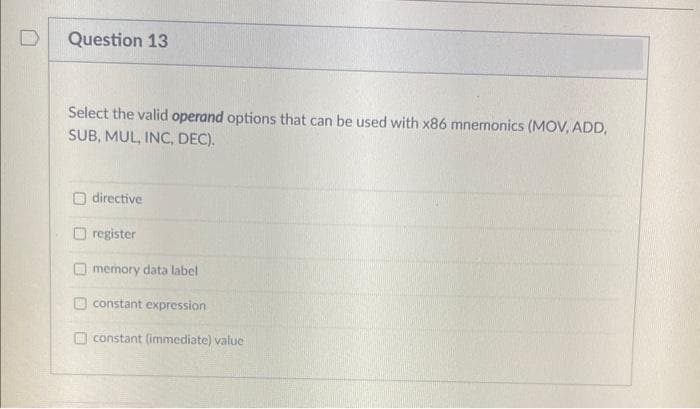
the valid operand options that can be used with x86 mnemonicsi ING DrC
Q: be allocated le
A: Given as, sign × mantissa × baseexponent
Q: Write a function definition called, sigma, that takes an input file reference and two integer refere...
A: answer: writing this code in java : main function:public static void main(String[] args) { Scanne...
Q: A single processor system has to execute six jobs L, M, N, O, P and Q having priorities 4, 7(high), ...
A: Given :- A single processor system has to execute sixjobs L, M, N, O, P and Q having priorities 4,7(...
Q: re how to use test-path, we look at its syntax in the Help file. Using the first syntax example give...
A: test-path Cmdlet Syntax: This cmdlet is used to test now not most effective a record exists however...
Q: 1. Design a Windows application named Wallpaper App to calculate the number of single rolls of wallp...
A: Answer :-
Q: organize your desktop.Name the folders below and organize your own desktop given files accordingly
A: Given: organize your desktop.Name the folders below and organize your own desktop given files accord...
Q: Problem 5 :Recursion Tree Time Complexity Find the Worst case time Complexity of the following recur...
A: In this question, we are asked to proof the time complexity for the given recursion function Given: ...
Q: Java Virtual Machine is a platform independent tool in Java that can be circulated through various m...
A: Java is a platform independent language. Every Java program is compiled into bytecode which is an in...
Q: 6. Create a function called word_intersection that prompts the user for two English words, and displ...
A: The user input will be string and then we have to parse them to set and then we can use intersection...
Q: Solve for the following: (Use the for..next, do..loop and while..loop for the solution) In VB.Net Pr...
A: C++ code or the first * sequence #include <iostream>using namespace std; int main(){ int ro...
Q: In the context of switches the term “sticky” is used to describe: a. A port security mode, where le...
A: In the context of switches the term “sticky” is used to describe: a. A port security mode, where ...
Q: What is data mining and how does it work? Compile a list of data mining tasks?
A: Introduction: Data mining is the process of collecting information from data by identifying patterns...
Q: Finding subtotals is a three-step process that begins with spell-checking. True False
A: Finding subtotals is a three-step process that begins with spell-checking. True False
Q: What does the Maple command mean?
A: Introduction: Maple command: The maple command is used to automatically finish the work of specific ...
Q: What is DNS scavenging, and how does it work? Describe the advantages.
A: Introduction: To avoid the accumulation of unwanted records, the DNS scavenging feature allows you t...
Q: Type the program's output Input 6 4 target = int(input()) n = int(input()) while n <= target: ...
A: Type the program's output Input 6 4 target = int(input()) n = int(input()) while n <= target: pri...
Q: for the following: (Use the for..next, do..loop and while..loop for the solution) In VB.Net Program ...
A: Input : Input the string Output : Change the case of every character except e and x.
Q: Detail the components of the spheres of security paradigm. The document must have a sufficient quant...
A: Introduction: Information security is primarily concerned with preventing unauthorized access to dat...
Q: Generate orthogonal codes for use in this system. Use the minimum possible number of chips per bit.
A: Walsh codes are orthogonal codes used extensively in cdmaOne and cdma2000. Spread factor or process ...
Q: Whenever FANUC picks up an item, it will read the UPC. Sometimes when analysing the UPC, the item ge...
A: According to the information given:- we have to follow the instruction to construct/ draw a use case...
Q: e a function called multiplyMe which has a variable number of integers as arguments and returns the ...
A: It is defined as the function definition starts with the keyword def. It must be followed by the fun...
Q: Write a php script to display 1! 2! 3! 4! 5! 6! 7! On one line There is no! At starting and ending p...
A: Algorithm: Start Iterate through the loop from x=1 to x=7 If x<7, print "$x!" Else print "$x" St...
Q: Why are computers and smartphones not adaptations, and why is that?
A: “Adaptation is the physical or behavioural characteristic of an organism that helps an organism to s...
Q: 2. Impact Assessment Consider the simplified model for risk shown in class. Assume the following par...
A: Answer :-
Q: the for..next, do..loop and wh
A: We need to read in user input and compute the Vowel count and display the result.
Q: Write a Normal Polish Notation program WITHOUTusing standard java libraries for stacks, queues etc.Y...
A: JAVA Program: import java.util.*; public class Polish{ static boolean ifOperator(String ch) { ...
Q: Create an ERD with the following Entities and Attributes. Entity: USERS - Attributes: Name of User,...
A: Create an ERD with the following Entities and Attributes. Entity: USERS - Attributes: Name of User, ...
Q: Instruction: Write a VB.Net Program that will use a function to identify the highest value based on ...
A: Start Take the three numbers as input. Find the largest number Print the result Stop
Q: What is the main advantage of the microkernel approach to system design? How do user programs and sy...
A: The microkernel is a piece of software or code that has just enough functions, data, and features to...
Q: A new information system that will be used by the company's finance department has asked for your th...
A: Answer: Suggestions for increasing the likelihood of a new information system being adopted successf...
Q: How many children is each node allowed to have in a binary search tree? Answer all that apply. I k...
A: binary search tree: is a binary tree, means every every node can have at most 2 nodes as childs.
Q: What is the difference between an argument and a return value? How many arguments can a method c...
A: Argument in JAVA: An Argument is a value passed to a function when the function is called . Return v...
Q: Define the concept of a unified memory architecture.
A: The goal of unified memory is to reduce data redundancy by copying data between separate areas of me...
Q: Multiple Calls (C PROGRAMMING ONLY) by CodeChum Admin After not being so clear with what I wanted...
A: As per the requirement program is written. Algorithm: Step 1: Write main() method Step 2: Write two ...
Q: 1) use the tag selector to select all of the elements with an h1 tag and turn them green 2) use the...
A: As per our company guidelines, we are supposed to answer only the first 3 sub-parts. Kindly repost o...
Q: Write a c++ code that takes a 4-digit binary number as an input and converts it into decimal then ou...
A: Input : 4 digit binary number Output : Print the number in decimal Programming Language : C++ Exa...
Q: What traversal method is used on binary search trees for deleting all of the nodes in the tree? The ...
A: To delete all nodes in binary search trees, we must traverse each every node, and traversal method i...
Q: 1. Give an advantage of half duplex over full duplex mode of communication. 2. Explain how can a net...
A: Advantage of half duplex over full duplex mode of communication - 1. Half duplex is easy to implemen...
Q: What style is better for use
A: Below are the leadership style and their advantages and disadvantages :- 1) Democratic leadership In...
Q: Consider the following edge-weighted graph G with 9 Vertie 40 60 90 50 70 20 30 80 10 130 150 120 10...
A: Steps: 1. Sort all the edges in non-decreasing order of their weight. 2. Pick the smallest edge. Che...
Q: Let G be a directed graph possibly with positive edge length. Let v + vz V3V4 be one shortest path f...
A: Let G be a directed graph possibly with positive edge lensth. Let be one shortest path from vt to ,....
Q: Consider the following formula in propositional logic. The knowledge base from (1) to (10) is given....
A: Propositional logic, also recognized as sentence logic or statement logic, is a branch of reasoning ...
Q: 1 Which of the following is the best description of a SAN (Storage Area Network)? It normally uses t...
A: I'm providing the correct option with proper explanation. You can understand easily. I hope this wi...
Q: How does a computer monitor render colour using the RGB approach of handling images?
A: Given :- How does a computer monitor render colour using the RGB approach of handling images?
Q: Create a recursive function and program for following equation using C++ f(5) = 5*(4/2)*3*(2/2)*1 ...
A: A recursive function consists of 2 cases: 1. Base case(i.e condition where recursion stops) 2. Recur...
Q: IDPSS have been added to IDS systems by a number of companies. Describe them.
A: Answer: In data centres, the cloud, and in the workplace, McAfee Network Security Platform (NSP) s...
Q: Create a link element that loads the myprint.css style sheet file but only for printed output.
A: Create a link element that loads the myprint.css style sheet file but only for printed output.
Q: Computer Science need a html code that creates 3 boxes 1st box has (first name last name ). second b...
A: Task : Define 3 text fields with labels First name Last Name Class/Section Professors Submit bu...
Q: Lucky Pairs Richie and Raechal are participating in a game called "Lucky pairs" at the Annual Game...
A: Since no programming language is mentioned, I am using python. Algorithm: Start Read A,B,N values S...
Q: average(double X, double y, double 2), returning he average of the arguments
A: Given 1. Write the following methods and provide a program to test them . b. double average(double x...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- What is the name of the Intel technology that allows a processor to handle two threads at the same time?Most Intel CPUs use the __________, in which each memory address is represented by two integers.Can someone help explain in detail what is going on with this Assembly Code - MASM x86 mGetString MACRO one, two, three push edx push ecx mov edx, one call WriteString mov edx, two mov ecx, three call ReadString pop ecx pop edx ENDM
- 2. X86 calling convention is about? a. How parameters are transferred through stack b. How interrupt vectors are used to find handlers c. How to make a phone call on an x86 computer d. None of the aboveThe term "Slack" refers to one of the many different types of memory that may be found in an 8086 microprocessor. You are need to perform some study on the issue and provide answers to the questions that are below. Use any illustration that involves stack memory and the commands that go along with it (PUSH, POP).Write a time delay program to generate a delay of 05 minutes in an 8086-microprocessor based system that runs on a 10-MHz frequency clock. Please send correct solution to this question. I will surely upvote.
- 1. Briefly explain the following terms used for Intel 8086 microprocessor with appropriateexample(s):a. PUSHb. POPc. SubroutinesAnswer the given question with a proper explanation and step-by-step solution. PLEASE PAY ATTENTION TO THE DATA TYPES AND FOLLOW THE CODE AND DIRECTIONS EXACTLY Convert the following C++ program into an x86 assembly language program.Comment the start of each "code block" that performs one of the listed mathematical calculations.Comments go to the right of the actual code, all starting on the same column.Post ONLY your ASM file here to Blackboard when complete. // Global variableschar a = 5;char b = 6;char c = 7;char d = 8;char e = 2;char f = 3;char g = 1;char h = 4;// Codeint main(){ --h; c = g + h; d = e + 22 - c - b; g = -h; ++b; a = g + d - 15; b = a + 92 - b; h = d + (-f) - d; // Move a into the eax register // Move b into the ebx register // Move c into the ecx register // Move d into the edx register // Call the DumpRegs function // Move e into the eax register // Move f into the ebx register // Move g into the ecx register…What makes interrupt-driven I/O different from configurable I/O?
- Please this question answered by this website but not appropriate answer because in c++ I want to answer in Assemly language to 8086 processor and 16 bit registers only Please solve it and send me please ? This question: Write a program to find the factors of a number and store the result at address 200 in memory.Sample Answer: I wrote a program to store factors of 60 at 200. (you should choose anynumber but greater than 20.WOLcUID wwreyg-100Ax-0060 BX=0030 CX-000 DX-0000 SP-0OFD BP=0900 SI=0000 DI-0209DS-073F ES-073P SS=073PF CS-973F IP-0110 NU UP EI PL ZR NA PE NC073F:011C CCd 2873F:020002 03 04 06 08 OC 10 18-20 00 00 00 00 00 00 00073F:0210 00 00 00 00 00 00 00 00-00 00 00 00 00 00 00 00973F:0220 00 00 00 00 00 00 00 0-00 00 00 00 00 00 00 00073F:0230 00 00 00 00 00 00 00 00-00 00 00 00 00 00 00 0873F :0240 00 00 00 00 00 00 00 0-00 00 00 00 00 00 00 00o73P:250 00 00 00 00 08 00 0 00-00 00 00 00 00 00 00 00073F873F:0270 00 00 00 00 00 00 00 00-00 00 00 00 00 00 00 00f 400 40c…Please explain the question and answer, please. Language is x86 assembly. Is Str like a variable name, and they put DWORD there. I'm very new to this language. Thank you 10. Declare a string variable containing word "TEST" repeated 500 times answer: Str DWORD 500 DUP("TEST")*************ASSEMBBLY LANGUAGE****************** In this practice program we all learn a few important things.1. How to validate that an incoming number really is a float number2. How to store a constant in your program3. How to multiply and divide float numbers stored in xmm registers. Program specificationMake a hybrid program where the active module is written in X86 assembly. A person plansto drop a marble from a known height measured in meters. The person wishes to know inadvance how many seconds the marble will be in free fall before reaching earth.Make a program that will input the height (64-bit float number) from a keyboard and thencompute the free fall time in seconds. We will disregard uncontrollable factors such ashorizontal wind and air resistance.



