thon code for this graphics.
Q: Consider the following two sequences of integers • Sequence A: 10000, 9990, 99, 9997, 21 • Sequence:…
A:
Q: n of DDoS mitigation with encryption hashing What is TCP/IP? What is the point of doing DNS…
A: SUMMARY What Is DNS Tunneling? DNS tunneling is one of the most dangerous DNS attacks. What is…
Q: What distinguishes Ubuntu from other server operating systems, and what features does it share with…
A: In this question we need to explain what makes Ubuntu different from other server operations systems…
Q: What is a violation of the DRY principle? Where may they typically be found?
A: The following are instances of DRY principal violations. WET (Write Every Time) AHA (Avoid Hasty…
Q: How does it make sense for a software development lifecycle to be used in conjunction with the idea…
A: The software life cycle model (also termed process model) is the pictorial and diagrammatic…
Q: Global positioning system is shortened to "GSM." Why do you need a SIM card for your cell phone?
A: Note : As per our guidelines we are allowed to answer only the first question from multiple…
Q: When two stations are visible at once, or if one station is hidden from view, wireless networking…
A: Data is sent wirelessly through a wireless network. sent wirelessly. sent from one host to another…
Q: The nature of wireless networks causes a variety of complications. List three of these problems and…
A: Introduction to a wireless network Computer networks known as wireless networks are those that are…
Q: In what other ways has the use of ICT benefited us, and what ways has it hindered us?
A: ICT is an abbreviation for Information and Communications Technology. It is an umbrella term for…
Q: In linear programming problems, the object function is more important than the constraints; why is…
A: The most optimal solution to a problem whose constraints have been specified can be determined with…
Q: When written out in full, what does GSM stand for? The little SIM card is an essential part of…
A: 1) GSM Stands for Global System for Mobile communication:- 2) It is a standard developed by the…
Q: Information systems that are fragmented may have a variety of drawbacks and issues.
A: There are a few key issues that may arise from having fragmented information systems within an…
Q: Give a little history of how wireless LAN standards came to be.
A: A local area network (LAN) consists of a series of computers linked together to form a network in a…
Q: Can technology be utilized in some manner to enhance learning? My outlook on many different issues…
A: ICT is an acronym for "Information and Communications Technology." ICT improve education in the…
Q: hild process utilizes unnamed pipes to read the parent's message buffer, what happens norma
A: Introduction: Below describe child process utilises unnamed pipes to read the parent's message…
Q: might be unclear what we mean when we ontext of telecommunications. There is mor
A: Introduction: In terms of speed, the 5G communication system can deliver up to 100 gigabits per…
Q: What is a violation of the DRY principle? Where may they typically be found?
A: "Don't repeat yourself" (DRY) is a principle of software development aimed at reducing repetition of…
Q: When and why do ict's benefits and drawbacks become apparent to the public?
A: Information and communication technology, or ICT, is essentially a computer-based technology for…
Q: What does Windows Service Control Manager accomplish, and what is its function?
A: Introduction: The Windows NT series of operating systems has a special system feature called Service…
Q: In this talk, you'll elaborate on the role that architectural design plays in the software creation…
A: Architectural definition Architecture-related adjective 1: adhering to architectural principles. 2:…
Q: You've discovered that an unauthorized user or users accessed sensitive customer data from your…
A: Security lapses happen when unauthorized access is granted to a computer's data, applications,…
Q: A virtual private network (VPN) is the best option for protecting the perimeter of a network. Can…
A: Introduction VPN is crucial for network security, and the following are a few reasons why VPN is the…
Q: In-depth discussion of architectural design's significance in software development.
A: Introduction Design, documentation, programming, testing, and continuous maintenance of software…
Q: software development.
A: There are many factors that can affect the quality of software architecture. In particular, the…
Q: We don't know enough about operating systems to comment on how they really execute processes.
A: Operating System: An operating system (OS) the software that controls all other application…
Q: The value of architectural design in creating high-quality software is discussed in this lecture.
A: Identification of essential system components and their communications. The architectural design…
Q: Give an illustration of what we mean by "code norms"
A: According to the information given:- We have to define the illustration of code norms.
Q: When it comes to a local area network, what precautions should be taken to ensure its availability…
A: Solution: Several steps can be taken to ensure local area network (LAN) reliability and…
Q: Discuss whether AFS and NFS provide the following: (a) location trans- parency and (b) location…
A: Introduction In the event of location transparency, the file name offers no indication of the file's…
Q: Think about the benefits and drawbacks of introducing wireless technology. To ensure smooth…
A: Advantages of wireless networking Increased efficiency Improved data communications lead to faster…
Q: There are several possible layouts for the OS's internal structure. The advantages and disadvantages…
A: A Multi-Level ApproachThe layered approach to operating system architecture divides a system into…
Q: I am interested in learning more about the many wireless networking protocols, topologies, and…
A: connecting wirelessly: Wireless local networks are suitable for workgroups and users who are not…
Q: A young programmer wrote his first testing system. He was so happy it compiled that he invited his…
A: Here is the c++ program. See below steps for code & output.
Q: What does Windows Service Control Manager accomplish, and what is its function?
A: Introduction:Service Control Manager (SCM) is a distinct system function in the Windows NT family of…
Q: Which of the following statements about Python is true? A. Python only supports object oriented…
A: High level programming languages used extensively in the creation of applications include procedural…
Q: Operating systems may be sorted into classes according to the kinds of functions they perform.
A: Provided: Is given statement true? Operating systems may be categorized based on the tasks they…
Q: There is a technological divide between wireless access points and bridges.
A: INTRODUCTION: In the given problem statement, we are asked the difference between the wireless…
Q: Think about how you may describe processes that aren't addressed in a systems analysis using…
A: A system analysis may be described as "the act of researching a technique or firm to determine its…
Q: It is important to examine the relative advantages of synchronous data replication and partitioning.
A: According to the information given:- We have to define the relative advantages of synchronous data…
Q: How does it make sense for a software development lifecycle to be used in conjunction with the idea…
A: Software life cycle models provide graphical representations of the software life cycle (called…
Q: a) let p, q and r be propositions. Simplify the following o proposition: ((r) ^ p ^ q) v ((-r) ^…
A: HERE IS COMPLETE SOLUTION REGARDING YOUR PROBLEM
Q: Give particular examples from your experience and describe the certification and training procedure.
A: Will be clarified: Training And Certification Are Important (offer): If a person, thing, or…
Q: When and how was the abacus first employed?
A: The abacus, sometimes known as the "World's First Computing System," was used to perform…
Q: Think critically on the state of wireless security and share your thoughts.
A: Discuss and evaluate how well you understand wireless security: The prevention of illegal access to…
Q: Analyze the differences and similarities between cellular, wireless, and wired data transfer.…
A: Portability depicts how far you can travel despite everything have the option to get to arrange…
Q: What is a violation of the DRY principle? Where may they typically be found?
A: DRY Principle: DRY stands for "Don't Repeat Yourself," a fundamental software development guideline…
Q: With this talk, you'll delve into the topic of architectural design and analyze why it's important…
A: Software Development Software development is a procedure used to generate standalone or independent…
Q: doesn't make sense People with the digital skills it means where we can go on Facebook and those…
A: You are right previous answer doesn't make sense. How has your digital understanding changed because…
Q: When it comes to computers, architecture and computer-based organization couldn't be more unlike
A: Introduction Architectural design: Architecture design refers to the method of integrating hardware…
Q: Give an illustration of what we mean by "code norms"
A: Code Norms:- Norms means standard so the code norms is the coding standard we need to follow while…
Python code for this graphics.
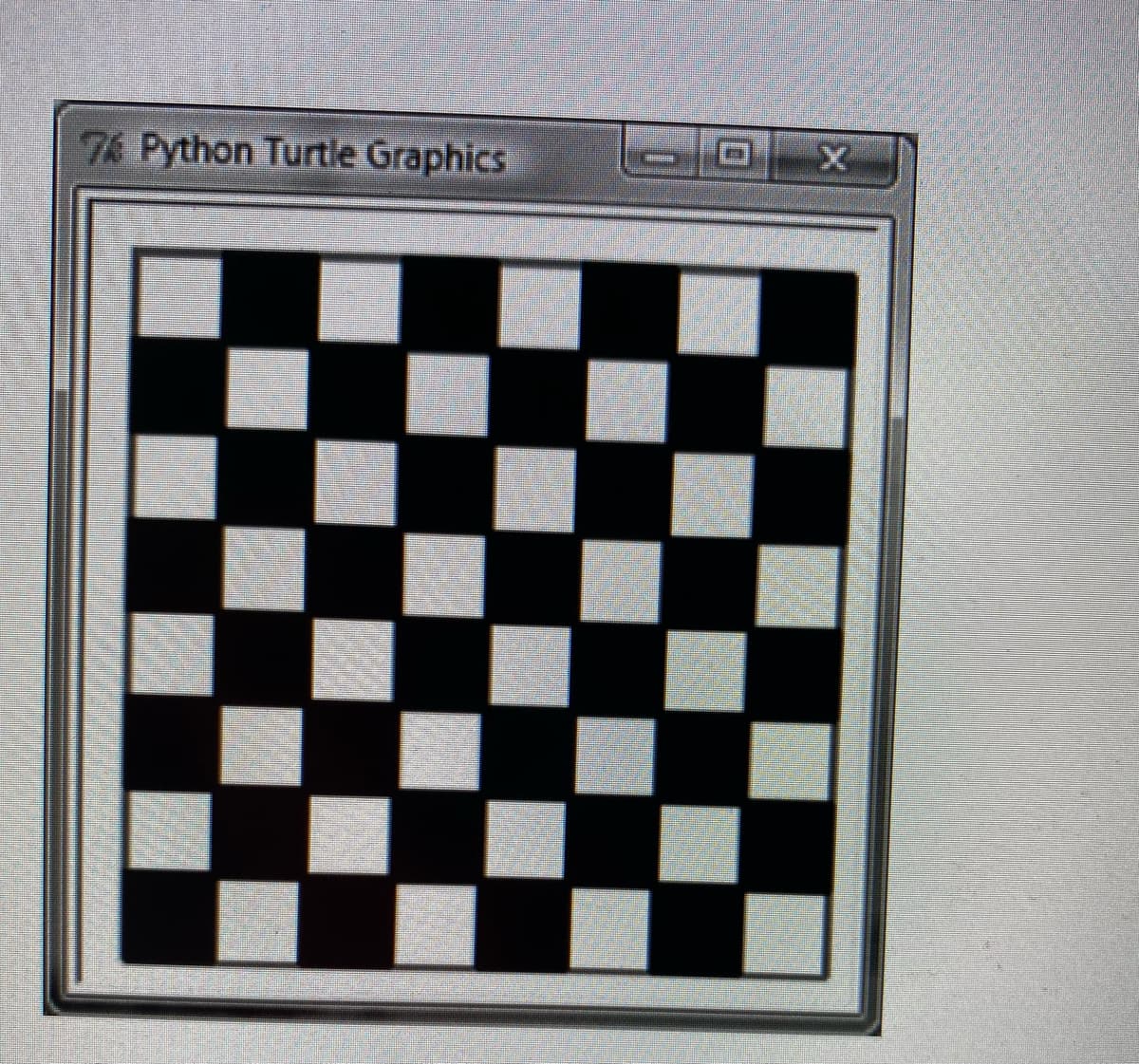
Step by step
Solved in 3 steps with 1 images


