to be placed to prevent the race condition(s). Could we replace the integer variable: int number_of_processes = 0 with the atomic integer:
Q: ***Please write code suitable for Myprogramminglab below: If you have downloaded the source code fr...
A: Introduction ***Please write code suitable for Myprogramminglab below: If you have downloaded the ...
Q: Compute the weakest precondition for each of the following assignment statements and their postcondi...
A:
Q: How can a Linux user get access to Microsoft Office documents?
A: Introduction: Microsoft Office may be installed on Linux using third-party tools like Wine or Cross ...
Q: C++ Programming Lab Write a C++ program to take a string from the user, print a new string made of e...
A: #include <iostream>using namespace std; string test(string s) { string result...
Q: Part I. Create a High-Level Network Topology Design and explain what kind of topology and Network ...
A: Network Topology
Q: Explain what IN AL, p7
A: The IN instruction transfers a string from a port specified in the DX register to the memory byte or...
Q: Q. Big data is explained with 3Vs: Volume, Velocity, and Variety. answer choices True False
A: Answer-True
Q: Compound assignment statements must be defined.
A: Intro Compound Assignment Operator: A smaller syntax for assigning an arithmetic or bitwise operato...
Q: There is 250,000 dollars that you have to divide to x amount of students in a year. Based on quality...
A: Excel IF AND OR functions alone are not very interesting, but combine them with IF statement and you...
Q: What is the point of having strings variables, in your perspective as a Telecom Engineer, since we a...
A: Introduction: A variable is a container that may contain values. The user may control the output of...
Q: What exactly is a wireless infrastructure network, and how does it function? When the network is not...
A: Introduction: A Wi-Fi network in infrastructure mode is one in which a Wi-Fi router produces the net...
Q: What is the IFB directive's purpose?
A: Intro IFB directive The IFB directive is used when the argument is blank. The syntax of IFB direct...
Q: It is currently doing this using a linear search. However, I want to make a hash map which will red...
A: given - JAVA PROGRAMMING I currently have a string method which changes accented letters to just n...
Q: The Turing Machine below starts with the input 0101 with the head on the left most 0. What will be i...
A: According to the question we need to answer:
Q: 1a)Consider prototyping versus SSADM. b)In relation to the completed computer system, briefly def...
A: As per our policy, "Since you have asked multiple questions, we will solve the first question for yo...
Q: Some observers anticipate that if the trend toward increasingly sophisticated CASE tools continues, ...
A: Introduction: CASE tool: Presently, the CASE tools are used to reduce the workload. For example, usi...
Q: Using python display even and odd numbers from 10 to 1(reverse order), Using a while loop. Outcomes ...
A: Algorithm 0. Start 1. Declare variable num = 10 2. if number num is divisible by 2 print "num is an ...
Q: What is normalization?
A: Below is the answer of normalization. I hope this will meet your requirements...
Q: What is the best way to get access to the Visual Studio documentation? What types of resources are a...
A: Introduction: MSDN, formerly known as Visual Studio Subscriptions, is one of Microsoft's most misund...
Q: Agile approaches employ quick development cycles to deliver running versions of the system repeatedl...
A: Intro The "agile" methodology is a type of software development where each phase of the software d...
Q: Write a Java Program to take an int n from the user & print the absolute difference between n and 51...
A: Write a JAVA program to input an integer n from the user and print the absolute difference between n...
Q: The Boolean function F(x, y) = x'y' + x'y + xy is equivalent to: O (xy')" O ylx + x'y') O x(y + xy')...
A: first of all we learn about boolean function Boolean algebra is algebra of logic. It deals with vari...
Q: Create a C++ application that takes three scores from the user and uses a do-while loop to calculate...
A: Create a C++ application that takes three scores from the user and uses a do-while loop to calcula...
Q: Python, using Conjunctive Normal Form formula, find a range of valeus of atomic proporsitions which ...
A: All of the following formulas in variables {\ displaystyle A, B, C, D, E} {\ displaystyle A, B, C, D...
Q: How to make a ceaser cypher in Java with simply loops and parameters
A: Introduction: How to make a ceaser cypher in Java with simply loops and parameters
Q: Explain the purpose of end-to-end testing and why it is required.
A: Introduction: The process of creating objective assessments of how well a system (device) meets, exc...
Q: Write a report on VDL that must include: 1. Applications of VDL 2. Areas which have benefited most ...
A: NOTE :- As per our company guidelines we are supposed to answer only first 3 sub-parts. Kindly rep...
Q: De 8ign a DFA for the following langag L={ w|we {c, b}" and #a (W) iseven W E %3D
A:
Q: What is your opinion of the Internet's value to individuals? How essential do you believe the Intern...
A: Intro The Internet holds a significant value in our lives. We spend most of our time surfing on the ...
Q: state beds baths sq_ft 826
A: The import statement as,
Q: What are the Advantages of Developing an IT Strategy?
A: Intro Benefits of an IT strategy An IT strategy must set out a vision for the future. It helps to...
Q: Include the four properties of a computer in today's educational system, based on "Why computers are...
A: Introduction: In today's educational system, there are four qualities of a computer: This question i...
Q: What are your obligations as a Systems Analyst?
A: Introduction: An information technology system analyst's role is to analyse and create solutions to ...
Q: Write a C++ program to take a string from the user, print a new string made of every other char star...
A: String indexing starts from 0 and the length of string can be obtained using length() method and thu...
Q: he image in the file provided (128 x 128, 2 byte integer format), a disk object is present in each o...
A: It is defined as a programming language developed by MathWorks. It started out as a matrix programmi...
Q: Given a BST, which traversal method would allow you to turn it into a min heap using N heap insertio...
A: Program Explanation: Import the array list class Define a public class for implementing the given l...
Q: A 3-variable K-Map produces the following minterms: x'y'z, x'yz, xy'z, and xyz. What is resultant si...
A: The correct option will be Option(b) z Explanation:- There are 3 variable k-map are used. we need to...
Q: Describe how to validate requirements, including the many sorts of checks that should be performed i...
A: Introduction: Validation of requirements is the process of verifying that the defined criteria fulfi...
Q: What is the ideal social network domain architecture?
A: Introduction: Social networking sites (SNSs) are becoming social gathering places. Users of social m...
Q: What does SHIFT PRESSED stand for?
A: Intro The input from the keyboard is an event which is described by the following structure. type...
Q: Describe portability.
A: Introduction: Here we are required to explain what is portability.
Q: What are the consequences and ramifications of cloud computing in the e-commerce world?
A: Introduction: The implications of cloud computing for e-commerce. Responses to new market issues, de...
Q: Create a CSS style for an H3 element, where: - colour is blue (in RGB format) - text aligned to le...
A: A CSS style for an H3 element, where: - color is blue (in RGB format) - text aligned to left - text...
Q: Opening many offices across the country, a tiny manufacturing company expands. Currently, each perso...
A: The System Development Life Cycle (SDLC) is a term that refers to the process of developing a system...
Q: Assume you are a systems analyst who is putting together a detailed test strategy. Describe the test...
A: Introduction: System Analyst's detailed test plans include: The primary responsibility of a system a...
Q: Explanation of executable file in brief
A: Intro Executable file: An executable code is understood by a machine. Executable files allow the ...
Q: Explain concurrency and examine four design and management issues created by concurrency.
A: Introduction: Concept of Concurrency: Operating System design is concerned with the management of p...
Q: Please right down the steps you would need to take to do the following in a Vitial Machine! In your...
A: Before you can change the desktop background in Student VM, you need to change the following Group P...
Q: When the Categorized button is chosen in the Properties panel, what exactly is it supposed to do?
A: Introduction: The Properties panel show the properties of the item or objects on the canvas that hav...
Q: What approach is recommended for mitigating the majority of failures in distributed systems, and why...
A: Distributed computing systems have their own infrastructure and no shared memory. « They communicate...
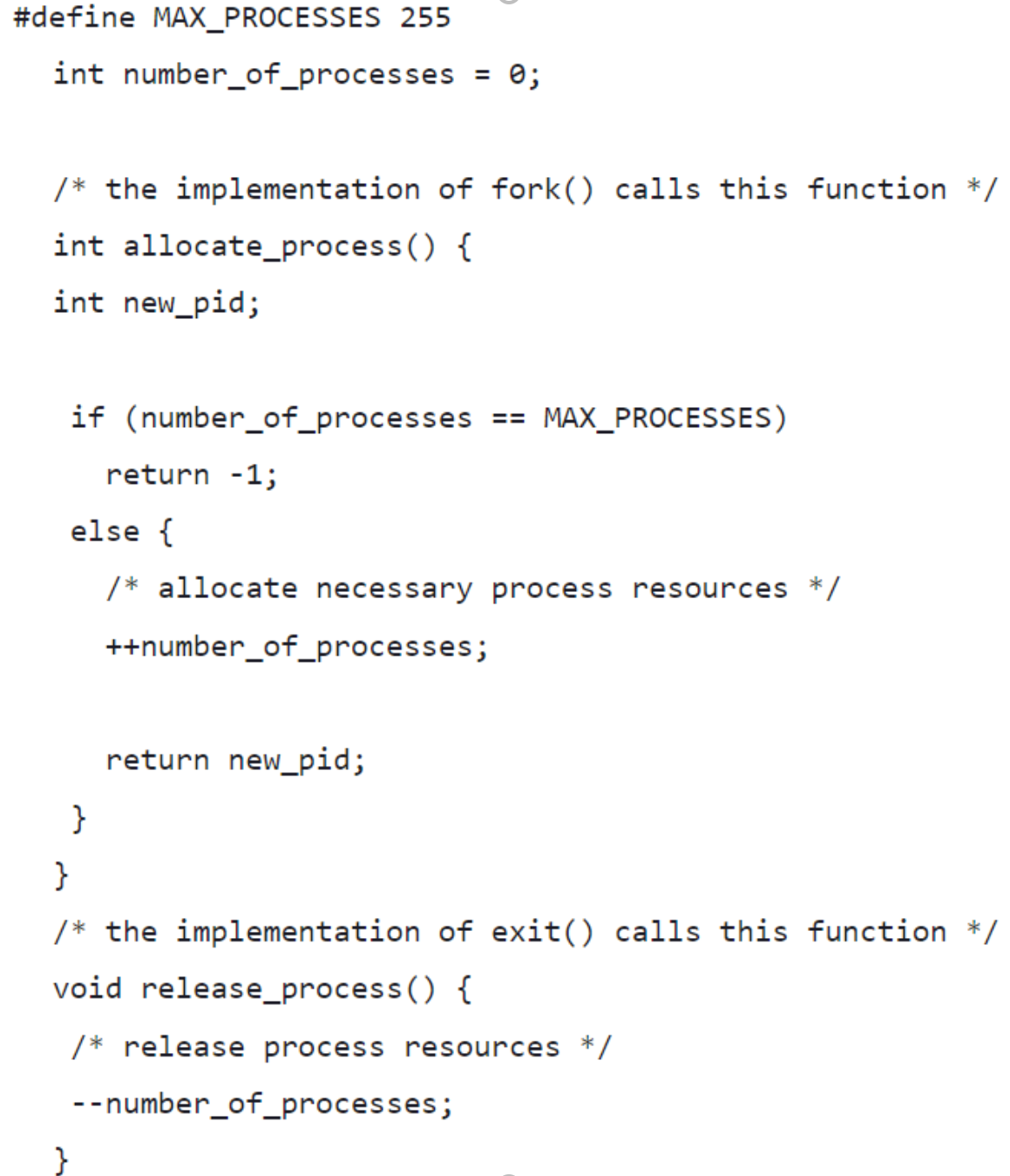
Consider the code example for allocating and releasing processes shown.
- Identify the race condition(s).
- Assume you have a mutex lock named mutex with the operations acquire() and release(). Indicate where the locking needs to be placed to prevent the race condition(s).
Could we replace the integer variable:
int number_of_processes = 0
with the atomic integer:
atomic_t number_of_processes = 0
to prevent the race condition(s)? Explain.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- OZ PROGRAMMING LANGUAGE Exercise 1. (Efficient Recurrence Relations Calculation) At slide 54 of Lecture 10, we have seen aconcurrent implementation of classical Fibonacci recurrence. This is: fun {Fib X} if X==0 then 0 elseif X==1 then 1 else thread {Fib X-1} end + {Fib X-2} end end By calling Fib for actual parameter value 6, we get the following execution containing several calls ofthe same actual parameters.For example, F3, that stands for {Fib 3}, is calculated independently three times (although it providesthe same value every time). Write an efficient Oz implementation that is doing a function call for a givenactual parameter only once.Consider a more general recurrence relation, e.g.:F0, F1, ..., Fm-1 are known as initial values.Fn = g(Fn-1, ..., Fn-m), for any n ≥ m.For example, Fibonacci recurrence has m=2, g(x, y) = x+y, F0=F1=1A reference parameter differs from an output parameter in that a reference parameter ______________________ but an output parameter does not. a. occupies a unique memory address b. must be a simple data type c. receives a memory address d. requires an initial valueYou are required to make changes in the above programs and introduce the use of compaction where required. Write code to simulate Worst-Fit Algorithm TASK2: DESCRIPTION One of the simplest methods for memory allocation is to divide memory into several fixed-sized partitions. Each partition may contain exactly one process. In this multiple-partition method, when a partition is free, a process is selected from the input queue and is loaded into the free partition. When the process terminates, the partition becomes available for another process. The operating system keeps a table indicating which parts of memory are available and which are occupied. Finally, when a process arrives and needs memory, a memory section large enough for this process is provided. When it is time to load or swap a process into main memory, and if there is more than one free block of memory of sufficient size, then the operating system must decide which free block to allocate. Best-fit strategy chooses the block…
- You are required to make changes in the above programs and introduce the use of compaction where required. Write code to simulate Worst-Fit Algorithm TASK2: DESCRIPTION One of the simplest methods for memory allocation is to divide memory into several fixed-sized partitions. Each partition may contain exactly one process. In this multiple-partition method, when a partition is free, a process is selected from the input queue and is loaded into the free partition. When the process terminates, the partition becomes available for another process. The operating system keeps a table indicating which parts of memory are available and which are occupied. Finally, when a process arrives and needs memory, a memory section large enough for this process is provided. When it is time to load or swap a process into main memory, and if there is more than one free block of memory of sufficient size, then the operating system must decide which free block to allocate. Best-fit strategy chooses the block…to design a simulator to simulate the behavior of a CPU scheduler, i.e.,choosing a process from the ready queue based on a scheduling algorithm to execute it by theprocessor. The simulator has to be implemented using C++. The simulator will consists of following classes:(i) Process: The data members of this class should store process id, arrival time in the ready queue,CPU burst time, completion time, turn around time, waiting time, and response time. The memberfunctions of this class should assign values to the data members and print them. A constructorshould also be used.(ii) Process_Creator: This class will create an array of processes and assign a random arrival timeand burst time to each process. Data members, constructor and member functions can be writtenaccordingly.(iii) Scheduler: This class will implement the scheduling algorithm. The class will maintain a readyqueue of infinite capacity (i.e., any number of processes can be accommodated in the queue). Theready queue should…Implement in C programming language: Question 2 Write a c program that will generate the safe sequence of process execution for the situation given below:(Use Banker’s Algorithm). Note: The code can be implemented in several different ways, but make sure the parameter remains the same as shown below. n = 6; // Number of processes m = 4; // Number of resources int alloc[6][4] = { { 0, 1, 0, 3 }, // P0 // Allocation Matrix { 2, 0, 0, 3 }, // P1 { 3, 0, 2, 0 }, // P2 { 2, 1, 1, 5 }, // P3 { 0, 0, 2, 2 }, // P4 {1, 2 , 3, 1 } }; //P5 int max[6][4] = { { 6, 4, 3, 4 }, // P0 // MAX Matrix { 3, 2, 2, 4 }, // P1 { 9, 1, 2, 6 }, // P2 { 2, 2, 2, 8 }, // P3 { 4, 3, 3, 7 }, // P4 { 6, 2 , 6, 5 } }; //P5 int avail[4] = { 2, 2, 2, 1 };…
- PROGRAM 8: SameWrite an HLA Assembly language program that implements a function which correctly identifies when all four parameters are the same and returns a boolean value in AL (1 when all four values are equal; 0 otherwise). This function should have the following signature: procedure theSame( w:int16; x:int16; y:int16; z:int16 ); @nodisplay; @noframe; Shown below is a sample program dialogue.Feed Me W: 215Feed Me X: 215Feed Me Y: 480Feed Me Z: 91Not the same. AL = 0Feed Me W: 0Feed Me X: 0Feed Me Y: 0Feed Me Z: 0Same. AL = 1Feed Me W: 0Feed Me X: 221Feed Me Y: 100Feed Me Z: 40Not the same. AL = 0Computer Science when you run the lottery ticket schedule, the code does not track the percentage of time a given process actually gets on the CPU. Please modify the code so that this is trackable, try to find the best allocation of tickets to processes to get as close as possible to the expected CPU percentage allocation. Please show modification in the code this is C program #include #include #include #include // global ticket count int gtickets = 0; struct node_t { int tickets; struct node_t *next; }; struct node_t *head = NULL; void insert(int tickets) { struct node_t *tmp = malloc(sizeof(struct node_t)); assert(tmp != NULL); tmp->tickets = tickets; tmp->next = head; head = tmp; gtickets += tickets; } void print_list() { struct node_t *curr = head; printf("List: "); while (curr) { printf("[%d] ", curr->tickets); curr = curr->next; } printf("\n"); } int main(int argc, char *argv[]) { if (argc != 3) { fprintf(stderr, "usage: lottery \n"); exit(1); } int…please write with proper explanation. Question half solution is here please write what is main disadvantages of this approach? Half solve questions: Mutual Exclusion: Mutex is an abbreviation for Mutual Exclusion. It is a programme object that prevents multiple users from accessing a shared resource at the same time. When a process accesses a shared variable, it is said to be in the critical section. When no two processes are present in the critical section at the same time, this is referred to as Mutual Exclusion or Mutex. while (true) { semaphore sem = S; while (S <= 0) do no operation { S = S-1; wait (S); } /*critical section*/ while (S > 0) { S = S+1; signal (S); } /*remainder section*/ }
- Problem Statement: (The following problem is based on problem statements in a number of operating systems texts) For this lab, you'll be setting up 2 queues of PCBs. A process control block (PCB) is an internal structure that is used to hold information associated with a process. A process is an instance of a program that is brought into random-access memory (RAM) for execution. To simplify matters, you'll be setting up 2 queues: a ready queue and a wait queue and, PCBs each PCB will have 2 fields: a process ID or PID (a positive integer) a link field to point to the next PCB on a queue The ready queue will have the PCBs for the processes that will be run in a first-come, first-served fashion. The wait queue will have the PCBs for the processes that will be waiting for a resource in a first-come, first-served fashion. If the PCB at the head of the ready queue needs some resource (for example, I/O) then it will be removed from the ready queue and moved to the rear of…Please write a C program. Consider the following code snippet in your main function -a = fork();b = fork();c = fork();Now, write the full program, that will check the children’s PID and if it is odd then the processwill create another child process. Lastly, print how many processes have been createdconsidering the first parent processImplement SRTF (SJF with preemption) scheduling algorithm in C programming. NOTE: Please do not print the average waiting time and the average turnaround time. You are required to compute these for each process and print the values for each process separately. Add comments in the code so that the code is understandable. Take input from the user: the number of processes, their CPU burst times and arrival times for n number of processes. Compute and print the completion Time(CT), Turnaround Time(TAT), and Waiting Time(WT) for each process using C Programming



