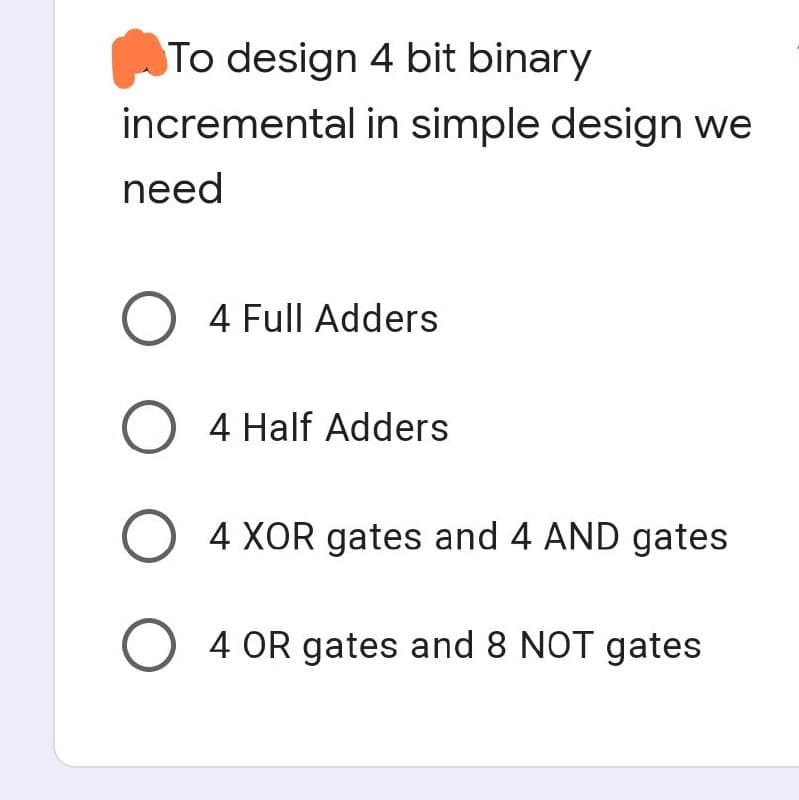
To design 4 bit binary incremental in simple design we need O 4 Full Adders O 4 Half Adders O4 XOR gates and 4 AND gates O 4 OR gates and 8 NOT gates
Q: After you have compiled a list of the various mathematical processes, sort them in a manner that is…
A: Introduction: In mathematics, evaluating a mathematical statement requires following a certain…
Q: Joe, one of your systems analysis team members, made the following entry for the data dictionary…
A: Data dictionaries:- Data dictionaries are defined as metadata which means data about data. It is…
Q: Exercise 7-4 Symbolize the following sentences, letting Px = “x was U.S. president”; Ix = “x is…
A: 1. All U.S. presidents have been well informed.
Q: This section should cover the most popular VPN protocols, configurations and services used in VPN…
A: Virtual private network (VPN): Vn offers anonymous internet access. Password, biometric security,…
Q: Could you elaborate on the four most important advantages that continuous event simulation offers?
A: Integrating Continuously: Continuous integration (CI) makes it easier, faster, and safer for…
Q: How does Direct Memory Access (DMA) operate to make the system more concurrent? To what extent does…
A: Given: In this section, we are supposed to explain how DMA increases system concurrency and in what…
Q: Click the arrows to display the destination .folder, and then click the folder :Select one O O O O…
A: (a) destination
Q: Is there a way to conduct a Linux OS backup?
A: Introduction: Execute the dd command to backup a full copy of a hard drive to another hard disc…
Q: Would you be able to provide a more in-depth explanation of each of the following four primary…
A: Introduction: Password authentication has several limitations; it is the most often used…
Q: After you have compiled a list of the various mathematical processes, sort them in a manner that is…
A: Launch: In mathematics, evaluating a mathematical statement involves following a precise sequence of…
Q: 1. What are the uses of various components of motherboard of a computer? List at least four output…
A:
Q: Which of the many factors has an effect on the way the netw functions?
A: Introduction: Below the describe the many factors has an effect on the way the network function
Q: Investigate the impact that wireless networks have on nations with a low standard of living. Why are…
A: Introduction: This paper examines upcoming technologies that may help bridge the digital divide,…
Q: 2011a On explain Encoding and Becording with for. AS CH85. #16 315 1000 X
A: Encoding is defined as the process of converting the data into a specific format. For example,…
Q: What do the terms "splitstream upgrade," "patch," "release," and "version" mean in terms of system…
A: Upkeep: User and organisation objectives are met via system maintenance. It involves updating…
Q: Direction: List down five(5) system software, application software and programming languages you are…
A: The above question is solved in step 2 :-
Q: Find out how people respond when they have difficulties with the software or apps on their computers…
A: Situations in which individuals respond to software issues: When software is not kept up-to-date,…
Q: a Design a frame in HTML that would look like the following .2 av j 20 30 40
A: I have provided HTML CODE along with CODE SCREENSHOT and OUTPUT…
Q: Describe what is meant by a Ethernet segment.
A: The above question is solved in step 2 :-
Q: Consider purchasing a pre-installed Linux PC from a computer manufacturer. Do you have the choice of…
A: Several computer manufacturers sell PCs with Linux pre-installed, confirming one computer producer.…
Q: What precisely does the term "Big Data" mean? What are the benefits of Big Data in terms of gaining…
A: Big data is a trending technology which contains data of greater variety, arriving in the increasing…
Q: A system has 4 components, A, B, C, and D, with reliability values of 0.98, 0.89, 0.94, and 0.95,…
A:
Q: Describe real-time systems and include illustrations to back up your response, please.
A: The question has been answered in step2
Q: In the context of the data hierarchy, what are the key distinctions between a data item and a data…
A: A hierarchical organization is one that is structured using various levels of authority and a…
Q: A number of questions arise as a result of the inherent characteristics of wireless networks.…
A: The above question is solved in step 2 :-
Q: Exercise 7-5 Symbolize the following sentences, using the indicated symbols as abbreviations. Some…
A: “Since you have posted a question with multiple sub-parts, we will solve first three subparts for…
Q: Click the arrows to display the destination .folder, and then click the folder :Select one O O O O…
A: Answer is given below:
Q: Is it necessary to run a simulation on a computer in order for it to have any value? Explain.
A: Explanation: The management is able to both measure and watch the behaviour of the system via the…
Q: Why is SQL so popular among database programmers?
A: SQL is utilized so much in light of the fact that from little to an extremely enormous association,…
Q: Give an explanation of what is meant by the term "cybersecurity," and discuss the significance of…
A: Start: Cyber security is the process of preventing harmful attacks on electronic systems, networks,…
Q: When there are problems with software and applications, it is important to keep in mind the various…
A: Start: Any portable computer may be referred to by this term; they are designed to be tiny enough to…
Q: The contents of the shell script even_sum.bash is shown below. Write down the output on when you…
A: In the given code the value of the $1 will be set to 10 as while running the statement 10 is passed…
Q: If random access memory (RAM) and cache memory both consist of transistors, then why do we need…
A: Introduction: In terms of speed, cost, and proximity to the CPU, both RAM and cache offer benefits…
Q: The performance of the network might be impacted by a large variety of different circumstances.
A: Given: The time that elapses between a data request being made and that request being fulfilled is…
Q: If random access memory (RAM) and cache memory both consist of transistors, then why do we need…
A: Introduction: In terms of speed, cost, and proximity to the CPU, random access memory (RAM) and…
Q: Design a form with four text boxes and three commands. Design the VB program so that the values of…
A: program Form1.vb : Public Class Form1 'VB Form 'btnCalculate click Private Sub…
Q: What exactly is the main distinction between computer architecture and computer organisation?
A:
Q: In memorization optimization technique, the following approach is used to find the optimal solution.…
A:
Q: During the execution of each of the solutions that you propose for the framework, you are required…
A: Introduction: On demand and in real-time, cloud computing offers resources like data or storage.…
Q: There are positive and negative aspects associated with implementing a gateway on your network.
A: Introduction: An essential resting place for data travelling to or from other networks is a gateway,…
Q: Direction: Choose from a peer-to-peer or client-server network. In each case you must provide an…
A: First of all let us understand some of the basics of peer-to-peer network and client server network.…
Q: Specifically, how should one go about dealing with the ethical difficulties that are brought up by…
A: Given: What strategy should be used to address the ethical issues that computer, information, and…
Q: Give folks the opportunity to discuss how they use tablet computers and cellphones in their…
A: Here are some instances of tablet and smartphone use in the workplace: Information Access Anywhere…
Q: Do subsystems of huge computer processes and programmes make sense when broken into smaller…
A: Breaking os subsystems of huge computer processes and programmes is called decomposition.…
Q: Direction: Compare the following operating systems OPERATING SYSTEM DESCRIPTION OF THE SYSTEM…
A: Stand alone operating system: Description: It is an operating system which runs on the devices like…
Q: What does it mean for data to be stolen?
A: Sensitive information: Sensitive information is the data that must be protected from the…
Q: How closely are science and technology intertwined, and how does this impact the way we go about our…
A: Overview: A wide range of potent technologies have been developed for usage in homes and…
Q: Operating systems go to great lengths to ensure that consecutive blocks of a file are stored on…
A: Intro: To be decided: Operating systems make an effort to put successive file blocks on consecutive…
Q: Consider the difficulties you will have when constructing the framework, and after that, analyse the…
A: Encryption: The management may measure and watch the system's behaviour using simulation.…
Q: What precautions can you take to safeguard your computer against potential dangers such as power…
A: Power Surge: The term "power surge" refers to sudden increases in the amount of energy that is…
Step by step
Solved in 2 steps

- Digital Logic and Computer Design The following picture is a 1-bit ALU that performs AND, OR and addition on a and b or a and not(b). Draw the required gates for the addition box and a truth table for the 1-bit ALUCreate a 4-bit AND and a 4-bit OR using logic gates(I need an asnwer for Q 1.4, Q2, and Q3 Question 1 Design the following circuits by using only 2x1 MUXs and NOT gates. 4X1 MUX 8X1 MUX 2-inputs AND GATE 2-inputs OR GATE Question 2 Design a JKFF by using only a DFF and logic gates. Question 3 Design a sequential modulo 3 accumulators for 2-bit operands. Definition:Accumulator - a circuit that “accumulates” the sum of its input operands over time - it adds each input operand to the stored sum, which is initially 0.
- A multiplier is to be designed for two 2-bit inputs using the algorithm. (Draw schematic, truth table, and write Verilog HDL code) (Use: and, not, xor gates)A result will be written at 7-segment on the Altera FPGA board. (Draw schematic, truth table) (Use: and, or, not, xor gates)Q4 Draw logic gates for the function F. F (A, B, C, D) = (B'D) (A'+ C°D) + (BC'+ D'A)Draw a 4-bit decrement circuit (subtracts 1 (i.e., z = x − 1)) that does not use not gates.
- 1. Construct the function F2 using only NAND gates. F2 = (AB' + A' B)(C + D') 2. Construct the function F2 using only NOR gates. F2 = (AB' + A' B)(C + D')a. Draw a circuit which produces Sum and CarryOut from inputs A and B (this circuit is known as a half adder). You should use exactly one AND gate and one XOR (exclusive or) gate. b. Give the truth table for a full adder (which incorporates a carry-in bit to the sum of A and B):Write a Verilog code using combinational logic gates to design an 8 by 8 signed bit multiplier
- Design a 4-bit arithmetic circuit, with two selection variables S1 and S0, that generates the arithmetic operations in the following table. Draw the logic diagram for a single bit stage. Note that B’ represents “Not B”. Please write down an optimized equation for Xi and Yi,A 1bit 4 to 1 multiplexer, the 4 inputs of the multiplexer will be the output of another combinational circuit with A and B as an input:00 = 1bit Adder01 = 1bit Subtractor10 = 1bit Comparator (equals)11 = XOR • truth table• Boolean Expression• Logic Circuit Here is the truth table guide:Design Mod 70 counter using IC # 74293. You can use other logic gates if necessary.

