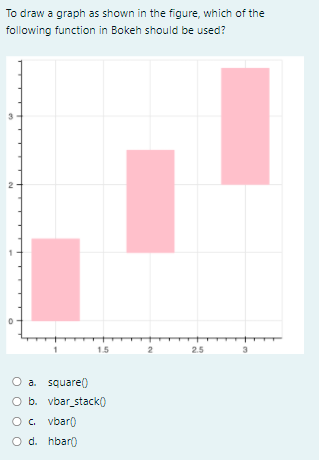
To draw a graph as shown in the figure, which of the following function in Bokeh should be used? 15 25 O a square() O b. vbar_stack) O. vbaro O d. hbaro
Q: A compiler that is both efficient and accurate must take into consideration a number of parameters.…
A: A compiler is a computer program that helps you transform source code written in a high-level…
Q: This section will discuss the best approaches to resolving some of the most pressing issues in…
A: Introduction: Because: Discuss some of the most critical information system issues to be aware of,…
Q: 6. Perform the following operations= a) 91B16 + 6F216 b) 2F0016-1536,6
A: The operations to be performed are: a) Hexadecimal Addition 91B16 + 6F216 b) Hexadecimal Subtraction…
Q: Information technology Explain Software Testing Life Cycle (STLC)
A: Introduction: Information technology Explain Software Testing Life Cycle (STLC)
Q: What are the benefits of a file system website over a http website?
A: Introduction: It is possible to communicate or transmit data over the internet from one system to…
Q: escribe data structures used to represent disjoint sets and provide algorithms for performing…
A: Each set is represented as a pointer-based data structure, with one node per element. Each set has a…
Q: Use Java to create a Binary Search Tree Class with the following Operations: Insert(int n) : add a…
A: public class BinarySearchTree { public class Node { //instance variable of Node class…
Q: When it comes to optimising compilers, what precisely are they? As a software engineer, when would…
A: Optimizing compilers may be built in such a manner that they are a critical component of…
Q: computer science - What does good feedback mean in the computer components industry? How can a…
A: Introduction: What does good feedback mean in the computer components industry? How can a parts…
Q: What the heck is a Microsoft Azure Domain?
A: Azure is a cloud computing stage and an internet based door that grants you to get to and oversee…
Q: The critical role of information technology in newly established firm functional areas
A: Introduction: The use of computers to generate, process, store, retrieve, and share all types of…
Q: What is a choropleth map? O a. A map of region with different divisions coloured to indicate the…
A: The solution to the given question is: A choropleth map is a thematic map used for a predefined set…
Q: Make a list of the key advantages and disadvantages of computer use.
A: Given: The computer is one of the most important innovations ever made to benefit humanity. A…
Q: What are the arguments against the use of a universal programming language? ге
A: Introduction: For any coder, the C programming language is a great resource.
Q: try: f-open("demofile.txt", "r" ) f.write("Lorum Ipsum") except: print("Something went wrong when…
A: Here the given file demofile.txt cannot be opened and is not writable. It is read only file. Hence…
Q: Translate LDUR X19, [X21, #40] to the corresponding LEGV8 machine language code:
A: LEGv8 This repository provides two LEGv8 CPU implementations, as well as some AWK-based tools for…
Q: Web design involves a lot of distinct stages. Each step should be accompanied by a concise…
A: Definition: In this part, we'll go through each of the processes involved in web design and why…
Q: gle machine situation, how can a computer a sking?
A: Introduction: Below the In a single machine situation, how can a computer accomplish multitasking
Q: The critical role of information technology in newly established firm functional areas
A: The Answer is in step2
Q: What constitutes a web application?
A: In computer system, a web application is a client-side and server-side software application in which…
Q: What are some of Azure Domain's characteristics? You are not need to utilize Microsoft. What are the…
A: Introduction Azure domain provides managed services which includes group policy, domain join,…
Q: o programming langua
A: Introduction: Below how two programming languages different
Q: Computer monitors are configured in a WIMP fashion. The majority of WIMP configurations have a…
A: The format icon on Windows is a graphic of a hard drive with a broom, which conveys a great deal…
Q: Write the following programs in Julia. Assume there are no duplicates in the list of numbers. Write…
A: Wev will use the concept of nested list. First loop,i starts from 1 till the length of the input…
Q: which security control is a countermeasure against vendor lock-in and lock-out?
A: Offsite backups: These backups are used off-ste servers. In this backup there are two types of…
Q: What is a software development approach known as "prototyping"?
A: Prototyping: The process of software prototyping is the creation of partial versions of software…
Q: What Exactly Is Virtualization, and What Are Its Advantages and Disadvantages?
A: Introduction Virtualization is the method of executing a computer system's virtual instance in a…
Q: Cons. # Program to perform set operati # definé sets A = (0, 2, 4, 6, 8) %3D B = (1, 4, 5} C = (3,…
A: Code to perform set operation # Program to perform set operation # define sets A = {0,2,4,6,8}B =…
Q: Write a detailed remark on each of the NCS's fourteen main programs.
A: Given: It positioned Pakistan's socio-economic growth within the perspective of a national…
Q: paradigm, VLIW or superscalar, is more challenging for compilers
A: Given :- In the above given question, the paradigm, VLIW or superscalar is mention in the above…
Q: How may concerns arise from the usage of a non-integrated information system?
A: Given: Computer failure and loss are severe computer problems that result in unnecessarily large…
Q: Explain the concepts of pair programming and refactoring
A: Introduction Explain the concepts of pair programming and refactoring.
Q: Computer science Identify any ten-risks related with IT project management.
A: The answer is given below.
Q: Describe how the boots function in bullet point style.
A: Answer:-) Booting is a startup grouping that initiates the operating system of a computer when it is…
Q: What are some of the most critical features and use cases for Azure Monitor?
A: Introduction: Azure Monitor can help you improve the availability and performance of your apps and…
Q: Which of the following entities in the Von Neumann model corresponds to which component: flash…
A: DVD-ROM or DVD-RW: CD-RW media may not be usable if it was generated in a drive other than the one…
Q: How does an Azure Domain operate?
A: Introduction Azure overview Azure is a cloud computing stage and an internet based gateway that…
Q: ses serve a variety of purposes. Desc
A: Below the Compiler Phases serve a variety of purposes
Q: omputer science - In terms of system concepts, what does the term "interdependence" signify, and…
A: Introduction: Interdependence is described as mutual reliance or dependency on one another (Woolf…
Q: What qualifications would someone need to do a good job in your position?
A: Introduction: The following are some of the abilities that someone needs in order to do successfully…
Q: Make a list of the functional and non-functional requirements for the "lost and found" app for kids.
A: Requirements: Profile Picture may be any of the picture formats.A user's status may be up to 65206…
Q: Explain each of the following benefits of continuous event simulation in detail. (a) Low-risk…
A: (a) Low-risk environment: Hazard examination will turn out to be more significant in defining…
Q: What are the basic desktop icons, and how do they get customised automatically?
A: Introduction: Icons such as the recycling bin will be presented frequently during the installation…
Q: What exactly is animation?
A: Introduction: Animation is a phrase used in multimedia to describe the quick display of a sequence…
Q: Question 1 Derive the minimized Boolean equation for the function F shown in the K-map below. Draw…
A:
Q: What is the role of a computer programmer?
A: The role of a computer programmer is discussed in next step
Q: What is the significance of coding conventions? Examine the coding rules used by the Java…
A: Definition: Coding standards aid in the comprehension of the code or, to put it another way,…
Q: In what sense does the phrase "software scope" apply here?
A: Software Scope: The scope of a software project is a well-defined boundary that encompasses all of…
Q: Computer science What Is application program?
A: Introduction: Application Programming Interface (API)
Q: Compare and contrast procedural versus object-oriented programming languages. What is Python and how…
A: Given: Procedural languages were used before OO languages. Object oriented programming languages…
Step by step
Solved in 2 steps

- Write a program to traverse various nodes of a given graph using stack as an intermediate data structure (DFS). IN JAVAImplement a queue with three stacks so that, in the worst-case scenario, each queue operation requires a fixed number of stack operations. High level of difficulty alert.Create a process to leave the other items of a linked stack unaltered while removing the nth member (from the top).
- Establish a library. Along with GETMAX, MAXSTACK provides PUSH, POP, and EMPTYSTACK ADT procedures and functions like a typical linked stack. The biggest element in the stack is recorded by the GETMAX function. Can the collection be built with GETMAX requiring only O(1) time complexity?Suppose that stack is an object of type stackType<int>. What is the difference between stack.top and stack.top - 1.Given the desired order in which the manatees are to arrive down south, how do I dermine if there is any way Hugh can use the drainpipe to achive the desired order? This problem can be solved by using a stack. A stack is an ordered collected of elements that operations to push(), peek(), pop(). In Java the interface Deque has those operations. The ArrayDeque class implements the Deque Interface. Input All input is to be read from the standard input stream. The input consists of several blocks of lines and is terminated by a line with just 0. The first line of each block indicates the number of manatees 0 < N < 100,000. In each of the next lines of the block there is a permutation of the numbers 1, 2, ..., N. For N=3, the permutation 2 3 1 means that the first manatee needs to be placed at the end of line and that the second manatee needs to be placed at the front of the line. The last line of each block contains just 0 signaling the end of the block. Output For each permutation…
- Suppose x is a linked-list node and not the last node on the list. What is the effect of the following code fragment?x.next = x.next.next;In Java please create a generic stack code and implement these methods peek() returns a reference to the item at the top of the stack without removing it from the stack contains(T t) is a boolean method that returns true if the stack contains t, the parameter, otherwise returns false. The stack contains t if at least one T on the stack is equal to t using the equals() method. Note that there is always an available equals() method in Java, because Object, the common parent of all classes, contains one. Implement this method without using the contains()method of the list.Implement a method transfer in class LinkedStack. This method should transfer all elements of a stack sourceS to another stack targetS so that the element that starts at the top of sourceS is the first one to be inserted in targetS, and the element at the bottom of sourceS ends up at the top of targetS. The operation should result in sourceS being an empty stack. Test this method in the main method of LinkedStack.
- By using JAVA, write a recursive display function, that print a linked list in reverse order.Consider that you have a stack S and a queue Q. Draw S and Q after executing the following operations (Op). You have to indicate for each operation, the stack or the queue content in addition to the index value of the top (stack) or the front and the rear (queue) Stack S; Queue Q; int a=3, b=7If a linked stack is implemented as a doubly linked list, provide a process to flip the stack such that the top and bottom places are now the bottom and top, respectively.A connected stack S and its reversed counterpart Srev, for instance, are displayed as follows:

