Trace the following recursive method for the function call “multiplyDigits(58746)” and show the output result.
Q: Can you explain the key distinctions between local and wide area networks? If this is the case, how…
A: Computer Network: A computer network is a group of interconnected devices, such as computers,…
Q: For merging two relations that are not physically sorted but share an index on the characteristics…
A: Yes, that's correct. When two relations are not physically sorted but share an index on the…
Q: What are the primary distinctions between a local-area network and a wide-area network in the…
A: Introduction: A local area network, sometimes known as a LAN, is a computer network that is…
Q: Please explain the Dataset object.
A: Introduction: In the field of data science, a dataset is a collection of data that is organized and…
Q: Using a normalized version of the Index metadata relation may lead to subpar performance, and the…
A: Version of the Index metadata relation that is normalized Since the index attribute field comprises…
Q: Why and How Do We Use Linear Data Structures?
A: Since they offer a straightforward and effective approach to organizing and handling data in a…
Q: Hello Classmates, This past week I have sent a ton of emails, text messages, updated status, and…
A: Introduction: The internet has become an integral part of our daily lives, and we use it for a…
Q: I was wondering how the various approaches of categorization and prediction were evaluated.
A: Introduction Writing a proper introduction is a crucial part of any written work. The introduction…
Q: The following record structure describes a movie file: name of the film's director and producer…
A: In computer science, a record (also called a structure, struct, or compound data) which refers to…
Q: There are two kinds of flow charts: logical and physical data flow diagrams. Due to its…
A: Data Flow Diagrams (DFDs):- Data Flow Diagrams (DFDs) are visual representations of the flow of…
Q: Is there ever a time when DML cannot be executed on a simple view?
A: DML stands for Data Manipulation Language which is a sub type of SQL and the commands of DML…
Q: Write a program in Android studio using Kotlin to display the chinese zodiac signs base of the year…
A: Sure, here's an example program in Android Studio using Kotlin that displays the Chinese zodiac sign…
Q: The proliferation of mobile devices including on-board processing power, the use of lightweight…
A: INTRODUCTION: Wireless networking is a way for residences, telecommunications networks, and…
Q: Given string inputString on one line, character userChar on a second line, and integer strIndex on a…
A: Algorithm of the code: 1. Create a Scanner object to take user input2. Create a String variable to…
Q: Object-oriented database management system is the official abbreviation.
A: Solution: The official abbreviation for "Object-oriented database management system" is "OODBMS".
Q: As compared to other devices, what characteristics set computers apart?
A: Introduction: Devices refer to any physical object or machine that is designed to perform a specific…
Q: What does the term "heterogeneous" refer to in the context of a decentralized database?
A: Introduction: A distributed database system is one that covers several computers or locations as…
Q: Besides the firewall we constructed, what are three (3) more major and distinctive points of…
A: The first major point of vulnerability in our program and its surroundings is the lack of encryption…
Q: In which of the six DBLC phases does the data dictionary play a role?
A: Data dictionaries are essential to relational databases. management system (RDBMS) for data…
Q: What is the name of a HTTP DoS technique that sends HTTP GET requests with partial HTTP headers to…
A: The question is asking for the name of an HTTP-based Denial of Service (DoS) technique that is used…
Q: What is the difference between Static, Read Only, Static, and Non-Static variables in C#
A: Below is a breakdown of how they differ from one another: 1. Static Variables: Instead of being…
Q: Consider the following grammar for a simple programming language: ::= | ::= | | ::= = ;…
A: Introduction DFA: DFA originally stood for "Deterministic Finite Automaton," which is a non -…
Q: Provide some details about the class's hidden and visible members.
A: Your answer is given below.
Q: Which highly available DHCP options do you see using at your organization, and why? To what do you…
A: DHCP, or Dynamic Host Control Protocol, is crucial for setting IP addresses of systems transmitting…
Q: Exist any distinctions between scripts and stored procedures? Just how do all of them fit together?…
A: Scripts and stored procedures: Scripts and stored procedures are both used in database programming…
Q: Explain the differences between data, information, and a database.
A: Data is made up of isolated facts and pieces of knowledge that lack context. You have information…
Q: What are the primary distinctions between a wide-area network and a local-area network, and how do…
A: Distributed Database: A distributed database is a type of database that is stored, managed, and…
Q: How did Wi-Fi advance individual technological capabilities? A)it created a way to work outside the…
A: answer is option -
Q: Create a catalog of the various DNS record types. You need to provide a thorough justification for…
A: Your answer is given below.
Q: In this article, we detail the digital signature technique (DSA) that has become the de facto…
A: In this section, we will talk about the digital signature algorithm, also known as the DSA, based on…
Q: computer To what extent did Ada Lovelace's thoughts really come to fruition?
A: He emphasized that Ada was only a "promising beginning" in mathematics rather than a genius in the…
Q: The role that mcommerce and the digital economy have had in assisting Disney World to adapt their…
A: Mobile commerce: M-commerce involves purchasing and selling things online utilising mobile devices…
Q: How would you define LINQ? For what reason is it being done?
A: Framework:- A framework is a set of tools and standards that provide an organized structure for…
Q: A company provides reimbursement of mobile phone subscription charges to its employees belonging to…
A: Given information about the company: A company provides reimbursement of mobile phone subscription…
Q: Let's pretend you're employed by a company that uses a firewall to keep its internal network secure…
A: According to the information given:- We have to follow the mentioned scenario in order to define…
Q: Explain what an optimizing compiler is. While writing code, when would you ever need one? Is there…
A: Introduction Compiler: A compiler is a software tool that converts source code written in a…
Q: As a Database Engineer, you've been given the freedom to choose between using triggers and…
A: Triggers are unique stored procedures in databases that execute automatically when a database server…
Q: The phrase "debugging" seems to be used often; could you perhaps define it?
A: Introduction It is an important part of the software development cycle, and helps developers…
Q: It is important that compiled code be both fast and correct, but how can developers ensure both…
A: Compiler: A compiler is a software tool that translates high-level programming languages into…
Q: In order to demonstrate your argument, please provide a real-world class and object sample.
A: Several identical things exist in real life. There might be thousands of identical bicycles. Each…
Q: How do you access, edit, or search a database of user IDs and passwords using a BST (Binary Search…
A: The solution to the given question is: To access , edit or search the user ID and password database…
Q: vWhere can I find out data's secrets?
A: Introduction: Using algorithms and statistical models, machine learning is a subset of artificial…
Q: In a database system feeding a data warehouse, why can column-oriented storage be useful?
A: Column-Oriented Storage: Since it dramatically decreases the total disc I/O needs and the quantity…
Q: Show that the database values may be altered without prior warning. The idea of longitudinal parity…
A: Introduction: Data is one of the most valuable assets of any organization, and databases are a…
Q: Can you tell me what you think of the FSF?
A: Computer Software Foundation Richard Stallman established it as a nonprofit corporation on October…
Q: How would you define LINQ? For what reason is this a prerequisite?
A: Introduction: The .NET Framework is a software development platform created by Microsoft that…
Q: What are the benefits of using watchdog timers in many embedded systems?
A: Introduction An embedded system is a specialized computer system designed to perform dedicated…
Q: 2. Using the pumping lemma and contradiction, prove that L= (abn>m}! is not regular.
A: To prove that the language L = {a^n b^m | n > m} is not a regular language, we will use the…
Q: In Java, develop a pseudocode algorithm to build an expression tree from a prefix expression.
A: Algorithm: Step 1 Start. Step 2 Define a class "Node" with a string value and left and right…
Q: Use the Play fair cipher to Encrypt the message "meet me at the usual place at ten rather than eight…
A: Introduction Cryptography is the practice of securing communication from unauthorized access or…
Question 1: Tracing Recursive functions
The solution can be handwritten
a) Trace the following recursive method for the function call “multiplyDigits(58746)” and
show the output result.
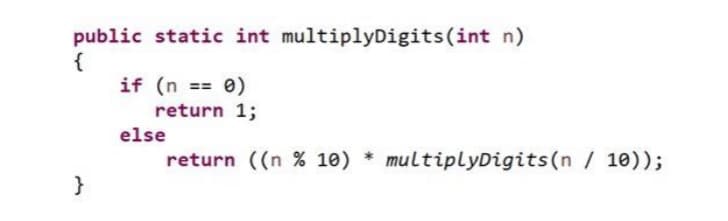
In step 2, I have provided OUTPUT along with purpose of given program----
In further steps, I have provided JAVA CODE along with CODE SCREENSHOT with OUTPUT-------------
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 1 images

- Rewrite the following loops, using the enhanced for loop construct. Here, values is an array of floating - point numbers. a. for (int i = 0; i < values.length; i++) { total = total + values[i]; } b. for (int i = 1; i < values.length; i++) { total = total + values[i]; } c. for (int i = 0; i < values.length; i++) { if (values[i] == target) { save = i; }.Fib(n): IF n equal 0 Return 0 ELSE IF n equal 1 Return 1 ElseReturn Fib(n-1) + Fib(n-2) How many recursive calls does this method have and how can you tell?In java Reprogram the following iterative function with recursion. int f(int N) { int count, sum = 0; for (count = 0; count <= N; count++) sum = sum + count; return sum; }
- Write a recursive method called digitCount() that takes two integers, n and m as a parameter and returns the number of digits in n that are equal to m. Assume that n≥0 and 0≤m≤9 Ex: If the input is: 34443215 4 3 import java.util.Scanner; public class LabProgram { /* TODO: Write recursive digitCount() method here. */ public static void main(String[] args) { Scanner scnr = new Scanner(System.in); int digits; int n= scnr.nextInt(); int m= scnr.nextInt(); digits = digitCount(n, m); System.out.println(digits); }}Java - Write an iterative method that calculates the SUM of all integers between 1 and a given integer N (input into the method). Write a corresponding recursive solution. (return answer, don’t print)Java - Write a method that uses a loop to figure out the factorial (n!). The method will take an integer n and return the value of n! (return answer, don’t print)
- java Write a recursive method largestDigitthat accepts an integer parameter and returns the largest digit value that appears in that integer. Your method should work for both positive and negative numbers. If a number contains only a single digit, that digit's value is by definition the largest. The following table shows several example calls: Call Value Returned largestDigit(14263203) 6 largestDigit(845) 8 largestDigit(52649) 9 largestDigit(3) 3 largestDigit(0) 0 largestDigit(-573026) 7 largestDigit(-2) 2 Obey the following restrictions in your solution: You may not use a String, Scanner, array, or any data structure (list, stack, map, etc.). Your method must be recursive and not use any loops (for, while, etc.). Your solution should run in no worse than O(N) time, where N is the number of digits in the number.Java - Write a method that uses a loop to figure out the factorial (n!). The method will take an integer n and return the value of n! (return answer, don’t print) Take the method above and convert it to a recursive method.Using java Declare an array of integers with size 10 and initialize the array with random numbers between 200-300. A for loop is needed, a random number generator is needed.
- Write a method that displays an n-by-n matrix usingthe following header:public static void printMatrix(int n)Each element is 0 or 1, which is generated randomly. Write a test programthat prompts the user to enter n and displays an n-by-n matrix. Here is asample run: Enter n: 3 ↵Enter0 1 00 0 01 1 1Write java program that generate two integer random numbers between 15 and 43 and printout the result of four operations between the two numbers, addition, subtraction,multiplication, division.The program must have the following methods:1- Method to generate a random number and return it.2- Method for addition operation accept two numbers and return back the result ofaddition operation.3- Method for subtraction operation accept two numbers and return back the result ofsubtraction operation.4- Method for multiplication operation accept two numbers and return back the result ofmultiplication operation.5- Method for division operation accept two numbers and return back the result of divisionoperation.6- Method to display the operation result which accept a string and three numbers.7- Main method to run the program by calling the above methods.Modify the Java CountByFives application so that the user enters the value to count by. Start each new line after 10 values have been displayed. public class CountByAnything { // Modify the code below public static void main (String args[]) { final int START = 5; final int STOP = 500; final int NUMBER_PER_LINE = 50; for(int i = START; i <= STOP; i += START) { System.out.print(i + " "); if(i % NUMBER_PER_LINE == 0) System.out.println(); } } }



