Tuliskan satu aturcara mengarahkan pengguna memasukkan satu ayat dan seterusnya menghitung dan mempaparkan bilangan vokal (A, E, I, O, U sama ada huruf besar atau huruf kecil) dari ayat berkenaan. Write a program to prompt the user to key in a sentence and then count and display the number of vowels (A, E, I, O, U, both uppercase and lowercase) in the sentence.using array. Contoh Example: Please key in a sentence = I am a UMS student Output: The number of vowels is as follows: A: 2 E I OU U : 1 0 2
Tuliskan satu aturcara mengarahkan pengguna memasukkan satu ayat dan seterusnya menghitung dan mempaparkan bilangan vokal (A, E, I, O, U sama ada huruf besar atau huruf kecil) dari ayat berkenaan. Write a program to prompt the user to key in a sentence and then count and display the number of vowels (A, E, I, O, U, both uppercase and lowercase) in the sentence.using array. Contoh Example: Please key in a sentence = I am a UMS student Output: The number of vowels is as follows: A: 2 E I OU U : 1 0 2
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter2: Basic Elements Of C++
Section: Chapter Questions
Problem 24SA
Related questions
Question
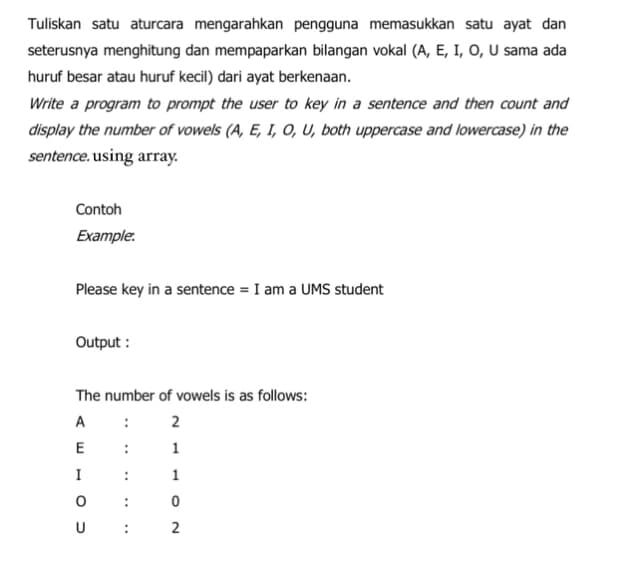
Transcribed Image Text:Tuliskan satu aturcara mengarahkan pengguna memasukkan satu ayat dan
seterusnya menghitung dan mempaparkan bilangan vokal (A, E, I, O, U sama ada
huruf besar atau huruf kecil) dari ayat berkenaan.
Write a program to prompt the user to key in a sentence and then count and
display the number of vowels (A, E, I, O, U, both uppercase and lowercase) in the
sentence. using array.
Contoh
Example:
Please key in a sentence = I am a UMS student
Output:
The number of vowels is as follows:
A: 2
1
1
0
2
E
I
OU
:
:
:
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 2 images

Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning