Please help me match the first image A-F with the second image a-d
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter1: Fundamentals Of C++ Programming
Section1.1: Preliminary One: Unit Analysis
Problem 7E: (Automotive) a. An automobile engine’s performance can be determined by monitoring its rotations per...
Related questions
Question
Please help me match the first image A-F with the second image a-d
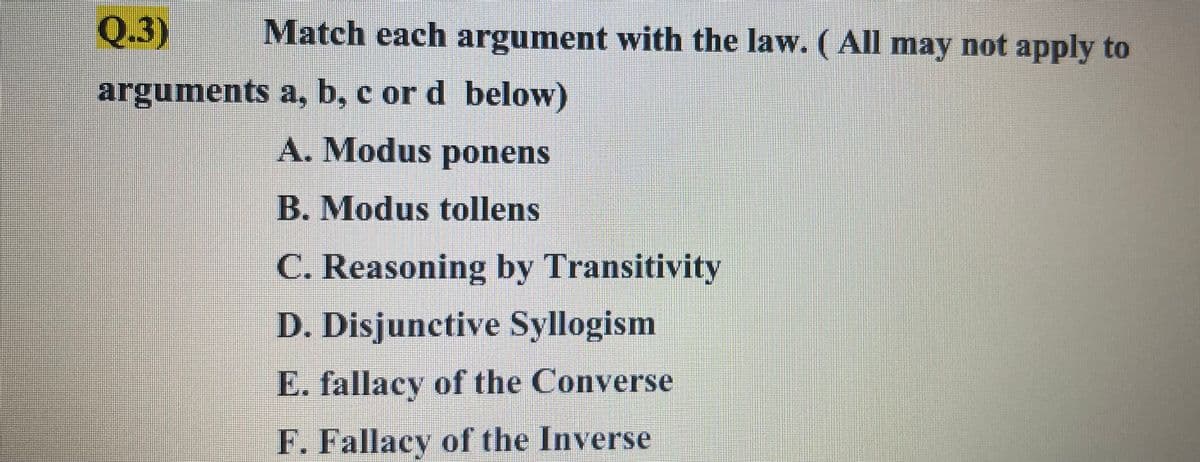
Transcribed Image Text:Q.3)
Match each argument with the law. ( All may not apply to
arguments a, b, c or d below)
A. Modus ponens
B. Modus tollens
C. Reasoning by Transitivity
D. Disjunctive Syllogism
E. fallacy of the Converse
F. Fallacy of the Inverse
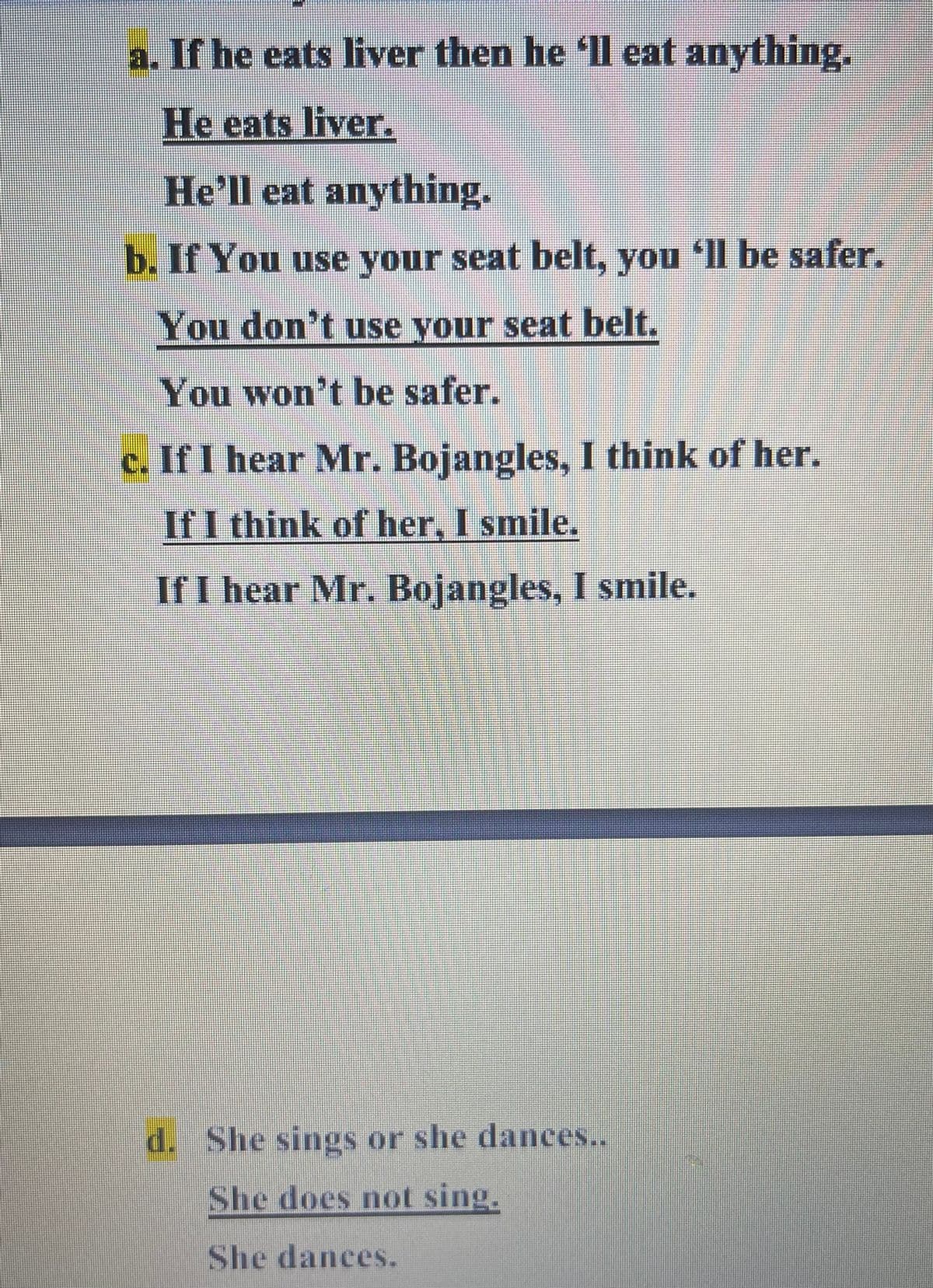
Transcribed Image Text:a. If he eats liver then he 'll eat anything.
He eats liver.
He'll eat anything.
b. If You use your seat belt, you ll be safer.
You don't use your seat belt.
You won't be safer.
c. If I hear Mr. Bojangles, I think of her.
If I think of her, I smile.
If I hear Mr. Bojangles, I smile.
d. She sings or she dances..
She does not sing.
She dances.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr