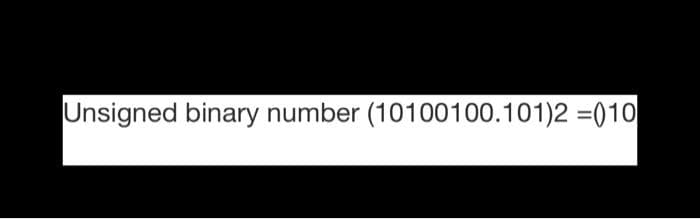
Unsigned binary number (10100100.101)2 =010
Q: Explain the difference between Word Processing, Presentation, Open Source, and Proprietary Software.…
A: Given: An application software, sometimes known as a "App," is a computer programme that allows end…
Q: Q27 for java programing: public static void main(String[] args) { Dog[] dogs = { new…
A: Find the required answer with explanation given as below :
Q: T(n): [T()+n_n>1 n≤1 [0(1) Answer: Display response =
A: The recurrence relation is solved using the substitution method.
Q: What exactly is meant by the term "dynamic memory," and how does it contrast with the concept of…
A: Given: Memory is allocated while the program is being executed. During the time that a program is…
Q: Explain why it's possible that certain automated transactions that use credit card numbers might be…
A: Introduction: Credit card data may be kept in some cases, such as written authorizations for mail…
Q: Input: a string and a charecter. create a python program to remove a occurence of that charecter…
A: ALGORITHM:- 1. Take input for the string and the character from the user. 2. Traverse the string…
Q: Declare an array of ints named scores and assign it the values 90, 80, 70 using static…
A: Array An array is collection of same type of elements which means collection of numbers, character…
Q: In the context of cloud security, what exactly is meant by the phrase "shared responsibility…
A: Given: Cloud security encompasses policies, methods, and procedures aimed at safeguarding data,…
Q: PINs, or personal identification numbers, are used to safeguard debit cards that are issued by…
A: Given: Since the beginning of time, financial institutions have been in possession of a significant…
Q: Many large organisations have had their database systems hacked, resulting in the theft of client…
A: Introduction: When working with data, one of the most important considerations is security. A…
Q: F=b+ãē+ +abe F=b+ãē+ +abe Q: In the Table below given the logic function F. (A) Sketch the function?…
A: A. Given function F = b+a'c'+ab'c' Logic circuit:
Q: 1-1 did not attend O some O any 2-can you give me O a little a few college conference. * help *
A: Please check step 2 for the answer. This shall help you. Thanks.
Q: Ex(5): Write a computer program using FORTRAN 90 to read (m) marks of (n) students using a…
A: program test real, dimension(m,n) :: matrix real :: average integer :: num m = 5n = 3 do i = 1, n…
Q: This is wrong. Suppoeed to four method and call everything in main method. You can look at the…
A: We need to write a Java program for the given scenario.
Q: What's the difference between main and secondary storage in terms of performance and price?
A: Main and Secondary storage: when you save a Word document, the information about the file is…
Q: What are the three essential operations involved in cryptography?
A: Three essential operations explained given below:
Q: What exactly is computer science, and how does it differentiate itself from other areas of study? In…
A: Computer science is the study of computers. Computer science is an area of study that focuses on the…
Q: processes and th
A: Introduction: A process is a program that is currently operating or a functioning project. An…
Q: Describe the difference. moug $0x8000, % rax movq between i 0x8000, rax
A: We need to answer questions related to given assembly code. *As per the guidelines only 1st question…
Q: Choose the name of any one business organization that makes use of any information system, and then…
A: Given: Recent advances in PC-based data technology have led to a variety of decision-making…
Q: To put it another way, what's the difference between a theoretical and a practical data flow…
A: Data Flow Diagram: A data flow diagram is a graphical depiction of the movement of information…
Q: Write a MATLAB program that used to plot the given functions. a) separately i.e. each function in…
A: hold on x = -2:0.1:2; % x from -2 to 2 y = -1:0.1:3; % y from -1 to 3 z = 100 * (y - x.^2).^2 -(1 -…
Q: S→ SSAB A → Aala B → Bb|b
A:
Q: When putting into practice cryptography that is reliant on public keys, what is the absolute bare…
A: Introduction: In the case of public key encryption, deciphering the information requires a separate…
Q: The article claims that the information system is significant in many organisations and the main…
A: An information system combined the all the components hardware, software,telecommunication network,…
Q: Input: a string and a charecter. create a python program to remove a occurence of that charecter…
A: Python program where we input the string and the chracter to be rremoved in that string and print…
Q: Solve Quick sort (element (8) as the pivot) algorithms by illustration for the following input: 1 2…
A:
Q: Describe the significance of using encryption and secure protocols while doing business online.
A: eCommerce safety is important. These are the guidelines for conducting secure online transactions.…
Q: What are some of the difficulties that are encountered by educational technology?
A: Top 10 Technology Challenges in 2021 What are the most recent IT issues?... Cyber security threats…
Q: When it comes to storing passwords in a safe place, why is it better to hash them rather than…
A: Let's first know about the hashing and encryption. Encryption It is the process to replace the…
Q: Please provide a summary of the nonvolatile solid-state memory technologies that are seeing…
A: Given: memory in solid state devices that is not volatile Memory that is not subject to random data…
Q: This kind of data flow diagram does not really show how the information is flowing.
A: A conceptual data flow diagram and an actual data flow diagram are two different things. A logical…
Q: What are the key distinctions between on-premises data center security solutions and cloud security…
A: On-Premises Data center security solutions: On-premises data stays on-premises, which eliminates the…
Q: Explain the output Why only Sara and Rumi apper in the output 3. Find the details of the Customers…
A: In part 2, we are seeing only Sara and Rumi only as other customers doesn't have any refunds and…
Q: Which method of obtaining application software offers the most return on investment? When you…
A: Introduction: Your computer's operating system provides the foundation for all of your actions and…
Q: Using comparisons between magnetic secondary storage devices and solid state secondary storage…
A: Given: A solid state storage device, such as USB memory sticks, is one of three forms of main…
Q: What is the optimum file access pattern for a chained disk allocation of files??
A: Disk allocation: The allocation techniques determine the manner in which the files are saved inside…
Q: Jump to level 1 valsTable: o 70 1 2 30 3 14 5 6 46 7 37 8 18 4 S Empty-since-start…
A: Find the required answer with explanation given as below :
Q: What exactly is meant by the phrase "shared responsibility paradigm" when referring to cloud…
A: Cloud security: Cloud security, also known as cloud computing security, is a set of rules, controls,…
Q: eline with stage dela ns. A pipelined processor requires n pair of consecutiv 5. no.. The op in
A:
Q: How is the rise in the usage of smartphones and tablets, which have smaller screens, influencing…
A: 1. Due to the reduced screen sizes of mobile phones and tablets, there are a number of difficulties…
Q: Taken from chegg, please provide orginal non plagarised work.…
A: We need to write a Java program for the given scenario.
Q: What key distinctions exist between the information technology security solutions used in a…
A: Given: On-premises systems may be modified in every way imaginable, however cloud computing provides…
Q: How you can assure re-usability of integrated modules E.g. If module is integrated with several…
A: The Answer is in step-2.
Q: Provide an explanation of how salt is used in cryptography to make it more difficult to crack…
A: salt: Salt is used by users who keep their passwords the same. There is a possibility that the…
Q: he name "Index.html" is notable for a number of differe
A: Introduction: Html is merely an extension for the index file, indicating that the index file is an…
Q: Explain the primary distinction between how symmetric encryption and asymmetric encryption function,…
A: Symmetric cryptography is faster to run because the keys used are much shorter than they are in…
Q: What are the benefits and drawbacks of a batch system with direct file access?
A: Answer: benefits: Simple to gauge an opportunity to get done with a given task Simple to oversee…
Q: The Internet has affected our society. The Internet offers perks and downsides. What are the…
A: Introduction: One of the most powerful innovations is the Internet, which provides people with…
Q: What academic subjects are similar to computer science, and what differentiates it? How they work…
A: Computer science: Computer science is the study of computers and algorithmic processes, including…
6
Step by step
Solved in 2 steps with 2 images


