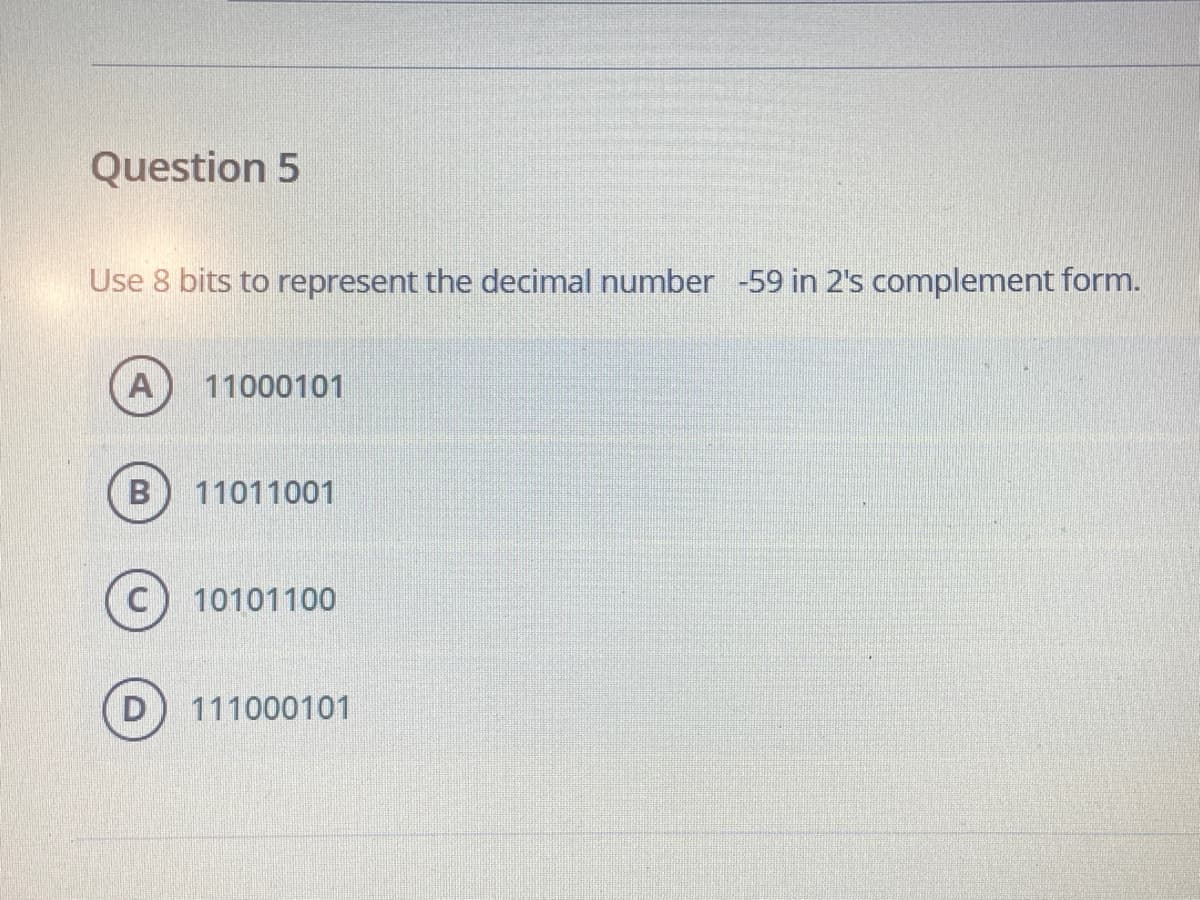
Use 8 bits to represent the decimal number -59 in 2's complement form. A 11000101 11011001 10101100 D 111000101
Q: (a) Identify the errors in the following code and correct them to produce the output shown in the gi...
A: Here are the errors in the code :- --> At the code line 6 the pitch and loudness are the float a...
Q: 9. Follow the comments to insert the missing parts of the code below: // Create a checkAge () method...
A: static void ..........(....... ..........){ ...........(..... ......... ........ ){ System.out.print...
Q: 6. Create a flowchart that will input for two numbers then get the sum,difference,products and qouti...
A:
Q: how would you write an algorithm using pseudocode to calculate the number of bytes in a given number...
A: answer is
Q: Write a program that counts the number of words in a sentence entered by the user #PYTHON
A: Please find the answer below :
Q: While it generally bad practice to hide worksheet, this may be appropriate for some cases. Which of ...
A: The answer of this question is as follows:
Q: Consider the processes P and Q, where P = a.b.0 + a.0 and Q = a.b.0. a) b) c) Does P strongly simula...
A: An automata A over an alphabet Act is a tuple (Q, Q0, Qf,T)whereS(A) = Q = {q0, q1, . . .} is the se...
Q: Given a set of n points, the greedy K-center algorithm takes ___ time. Group of answer choices A. ...
A: Please refer to the following step for the complete solution of the problem above.
Q: Sort the various DNS record types into logical groupings. Explain each one quickly, using real-world...
A: Introduction Sort the many types of DNS records into logical groups. Explain each one briefly, provi...
Q: 1) Which of the following is/are bad reason(s) on using a Google Doc for keeping minutes? (Select al...
A: C. It lets everyone in the meeting contribute if they want to. Because it allows chaos if people all...
Q: t do you f
A: given - Which of the measurements of development do you find logical and acceptable?
Q: scuers with AI robots. a. Design an agent following PEAS properties. b. What will be the benefit a...
A: Artificial Intelligence and Machine Learning systems play role in our society:-as we know that mach...
Q: + n
A: given - PLS SHOW STEP BY STEP OF BOTTOM UP RECURSION SOLUTION TO 1 + 2 + 3 + ... + n
Q: What is the definition of page fragmentation ?
A: Introduction: Fragmentation is an unwelcome condition in the operating system in which processes are...
Q: mpiler, the one that we use for our course. The program will need to calculate the final mark and co...
A: Write a ‘C++’ program (capable of being compiled on any standard ‘C++’ compiler andin particular Blo...
Q: What exactly is "invalid data"?
A: Introduction: Data validation is the process of checking the correctness and consistency of data fro...
Q: What is the Internet Control Message Protocol, or ICMP, and how does it function?
A: Introduction: The Internet Control Message Protocol, or ICMP, serves the following purposes: The pri...
Q: Explain how in-database analytics works.
A: Ans: The database analytics working is: 1) In this first step it is determine the data requirements ...
Q: Why is it that CDMA allows users to communicate at the same time while using the same frequency band...
A: Introduction: Users in the CDMA technique are identified from one another based on their CDMA codes....
Q: What gadget must be installed on a DSL \snetwork to protect the sound quality of \sphone calls?
A: Basics: DSL represents Digital Subscriber Line. A telephone divider jack on a modern phone network p...
Q: Please help me make this code more presentable. Please fix the code for me if there's error. APPLY H...
A: Code: <!DOCTYPE html> <html lang="en"> <head> <meta charset="UTF-8"> ...
Q: set is orthog
A: given - Justify why an instruction set is orthogonal by describing what it means in terms of symmetr...
Q: 2.9 A common measure of transmission for digital data is the baud rate, defined as symbols (bits in ...
A:
Q: Consider the following game between two players: Both players simultaneously declare “one” or "two"....
A: Write a computer program in Java that allows a user to play this game against a computer. The comput...
Q: Task #2 Write a MIPS assembly program that reads a string str (one character at a time) from the use...
A: ANSWER:-
Q: ate class methods (Setters and Getters) that load the data values. The Setter methods will validate ...
A:
Q: What are the advantages of a file system website versus a http website?
A: Introduction: Both the file system website and the HTTP (HyperText Transfer Protocol) website are us...
Q: What distinguishes a mobile app?
A: answer is
Q: 3. Let A = {1, 2, 3} and B = {4,5}. %3D a) Find A x B b) Find B x A
A: A = {1, 2, 3} B = {4, 5} A*B = {1, 2, 3} * {4, 5} A*B = {(1, 4), (1,5), (2, 4), (2,5), (3, 4),(3, 5...
Q: A known distribution company intends to reward it deserving employees with a bonus only for sales ag...
A: Consider the data in excel file. NAME as column A AREA as column B POSITION as column C SALES as co...
Q: write assembly x86-64 language function to take an array of integers and find out average.
A: Assembly x86-64 language function to take an array of integers and find out average DATA SEGMENT ...
Q: Write an algorithm to prompt a number and find the sum of first n whole numbers
A: In step 2, I have provided algorithm--- In step 3 , I have provided C program---
Q: Given: Consider the function below written in Python3: def foo(a, b=[1]): if a <= 1: return b b_new ...
A: Given: Given the function of the code in python 3 We have to answer Worst case time complexity of...
Q: Insert the missing part to call myMethod from main.
A: When we have to call the method we write method name. If there is parameter we pass parameter otherw...
Q: In a Layer 1 frame, what information is normally included?
A: Introduction: It is the physical layer that is responsible for managing the connection between two d...
Q: A DBMS provides support for concurrency control and integrity constraints. True or Flase
A: Yes, A DBMS provides support for concurrency control and integrity constraints
Q: How can you protect yourself from coremelt attacks?
A: Introduction: Coremelt is a new attack mechanism in which attackers only transfer traffic amongst th...
Q: Implement an immutable class MyBigInteger using String Provide methods toString, add and su...
A: Step 1 The answer is given in the below step
Q: With the assistance of appropriate examples, discuss memory representations of 1D and 2D arrays
A: 1D Array Memory Representation of 1-D array: One-dimensional arrays are allocated in a contiguous...
Q: Explain cloud computing, IoT, and the wireless revolution.
A: Cloud Computing and IoT are both connected to each other with the Internet so let's talk about Inter...
Q: Write a single C++ program that performs following: Takes three input strings from a user, convert i...
A: In this question, we are asked to write a C++ program to sum of three string after conversion Explai...
Q: Explain how caching is used in Web access in two different ways.
A: Introduction: Web caching is the process of saving data for later use, such as a copy of a web page ...
Q: 5.) Create a flowchart to compute and display the gross pay and net pay by taking employee number, e...
A: Algorithm : start Declare variable grossPay,noOfhours and ratePerhour Read number of hours worker...
Q: The following hex string has been XOR'd using a one-character key; decrypt it to get this flag's val...
A: What they meant in the above hex string was that they XORed each byte of the message against this "k...
Q: Find the simplified SOP expression for F(V,W,X,Y,Z)=summation of MAXTERMS (2,3,4,7,10,11,13,16,18,19...
A: From the given MAXTERMS the minterms are (0,1,5,6,8,9,12,14,15,17,20,21,22,25,28,30) The K-Map is:
Q: If the result is as follows: >> C=A\B C = 26.2500 17.5000 8.7500 17.0000 What should be the command ...
A: Answers is D2 = C(3,:);
Q: I need a C code of this: Input 1. Number of rows Constraints The value is guaranteed to be >= 3...
A: Please refer full code with output screenshot: #include<stdio.h> int main() { int r,...
Q: sum(n) if n=0 return; return n+ sum(n-1) store intermediate values build a bottom up solution ...
A: answer is
Q: Practice problem: use DFS version of topological sort for the following DAG J6 DFS(G) I for each ver...
A: The Answer is
Q: A string is called a palindrome if it reads the same when reversed. That is, the string x1 x2 ... xn...
A: The solution for the above given question is given below:
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- A(n) __________ is an integer stored in double the normal number of bit positions.Question 14Use 8 bits to represent the decimal number -45 in 2's complement form. 10101000 11010011 11011010 10000011What decimal value does the 8-bit binary number 10011110 have if (Please show the calculation process): It is on a computer using one’s complement representation? 2.It is on a computer using two’s complement representation?
- By using 2’s Complement arithmetic, write the following decimal numbers to equivalent8-bit signed numbers and perform the addition. Write the final result after the addition by showing yoursteps. (check the image for reference) i. 6 ii. 14 iii. 15 iv. -6+ 3 + (-5) + (-25) + ( -9)1. Represent the following decimal numbers in 8 bits: (+94)10 and (–124)10 by (a) Sign-magnitude, (b) one’s complement, and (c) two’s complement representation 2. Express the following decimal numbers in Excess-3 code form: 24510, 73910, and 456710. 3. Express the following Excess-3 codes as decimals: 1000001101102 and 01111100100101102.What is the decimal representation of the following signed 2’s complement binary numbers 1011 0101, 0010 1010, 1111 0000, 1010 0111?
- The following 6-bit number 100110 What is the decimal value in case of b) 1's complement representation c) 2's complement representationRepresent the following decimal numbers in binary using 8-bitsigned magnitude, one’s complement, two’s complement, andexcess-127 representations:1. a) 602. b) −603. c) 204. d) −20Represent the following decimal numbers in binary using 8-bitsigned magnitude, one’s complement, two’s complement, andexcess-127 representations.1. ◆a) 772. ◆b) −423. c) 1194. d) −107
- What are the 16-bit 1’s and 2’s complements of the following binary numbers? 01100 100111100001001Represent each of the following integers as 10-bit two’s complement binary numbers.i) -18510 ii) 15610 iii) -20510 iv) 16910please answer with proper explanation and step by step solution. Question What decimal number does the bit pattern 0xC2280000 represent if it is: A two's complement integer? An unsigned integer? A floating point number assuming the IEE 754 single precision format

