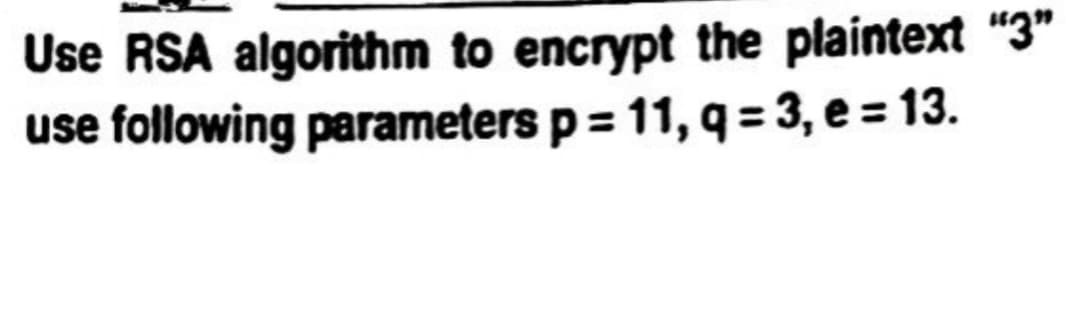
Use RSA algorithm to encrypt the plaintext "3" use following parameters p= 11, q=3, e = 13.
Q: Define a function called equation that calculates the following equation. Write a program that…
A: According to the information given;- We must follow the instructions to define the equation in the…
Q: What is block cipher? Explain counter mode block cipher.
A: Block ciphers encrypt data in blocks using an algorithm and cryptographic key to produce ciphertext.…
Q: Assigning Random Numbers Enter a SINGLE OR MULTIPLE LINES of MATLAB code that accomplishes the…
A: The MATLAB code is given below with code and output screenshot Happy to help you ?
Q: Algorithm OPTIMAL-PARAMETRIZATION. Given F(x, y, z) ∈ Q[x, y, z], an irreducible homogeneous…
A: Algorithm OPTIMAL-PARAMETRIZATION.Given F(x, y, z) ∈ Q[x, y, z], an irreducible homogeneous…
Q: Write a program that prompts the user to enter five test scores and then prints the average test…
A: #include <iostream>#include <stdlib.h>#include <cstdlib> using namespace std; int…
Q: Q.30 Using Playfair cipher encrypt message. "We five in a world full of 'beauty" use key "ANOTHER.
A: The Playfair cipher, Playfair square, or Wheatstone-Playfair cipher, is a manual symmetric…
Q: What is the decimal value of register SO after executing the following code? Consider that the value…
A: Here is the explanation of the above problem. See below steps.
Q: Exercise 6. A binary tree T has height 8. (Recall that the height of a tree is the number of edges…
A: (a) The minimum number of nodes in a binary tree of height h is h + 1. Here, the binary tree T has a…
Q: Part 2: Math and DecimalFormat classes . Read the radius (int) and height (float) of a right…
A: Java introduction:- It is a 1991-era programming language. The Java programming language was created…
Q: Implement an algorithm to delete a node in the middle (i.e., any node but the first and last node,…
A: Solution: Given, Implement an algorithm to delete a node in the middle (i.e., any node butthe…
Q: Write a JavaScript function to sort a list with the insertion sort algorithm, but without mutation.…
A: Insertion Sort: function insertionSort(array) { for(var i = 1; i < array.length; i++) { var…
Q: Write Queue class implementation includes methods for EnQueue, DeQueue, ClearQueue (clearing the…
A: In computer science, a queue which refers to the collection of entities that are maintained in a…
Q: Draw the digraph of the relation R, where the relation R on {1,2,3,4} defined by (x,y) ∈ R if x^2>=y.
A: Consider, A set, S={1,2,3,4}. The cartesian product: S x S={1,2,3,4) x…
Q: The exercise is to input a string from the user, and then output the following information: • Length…
A: F# which refers to the functional-first, general purpose, strongly typed, multi-paradigm programming…
Q: In each iteration of a loop, generate a random number, and use it to determine some attribute of…
A: In this question, it is asked to generate a random number and use it as an attribute for drawing a…
Q: 20) Write a script that reads the content of a file. Then print the number of four-letter words in…
A: Python programming language : High level and wide purpose, Python is an open-source programming…
Q: 6. Please use the "shared folder" option within VirtualBox and successfully transfer a file. Please…
A: VirtualBox:- An open-source virtualization programme is Oracle VM VirtualBox. It enables users to…
Q: Please do it with Python. #Problem 1 #Chip Brownie made a mistake and allowed any value to be…
A: Here is the python code of the above problem. See below steps.
Q: RSA Attacker obtains 9(n) = (p-1) (q-1) = 65,520 public n 1 = 66043 find values of p and १
A: RSA Algorithm:- The RSA algorithm uses asymmetric cryptography. Asymmetric actually refers to the…
Q: is an image file that reduces the number of http requests made by the browser.
A: Hypertext Transfer Protocol (HTTP) is an application-layer protocol for transferring hypermedia…
Q: Can you make it more efficient and paraphrase it in Java import java.lang.Math; import…
A: In this question, it is asked to improve a given java code. For improvements, better comments are…
Q: Select all of statements that are logically equivalent to the statment: if Xavier xylographed then…
A: Logical equivalence: The conditional statement is logically equivalent to its contrapositive…
Q: Queues are often used to simulate situations where people have to wait in line. One scenario we can…
A: program for given scenerio in c# language given in next step:-
Q: How to Installing Kali Linux with the help of VMware?
A: Installing Kali Linux with the help of VMware:-
Q: Use c++ a) write a function that reads a string and returns the character that has the largest ASCII
A: Here is the c++ program of the above problem. See below steps for code.
Q: In your own words describe what are XML files?
A: The World Wide Web Consortium (W3C) released XML, also known as "eXtensible Markup Language," in…
Q: 3/4
A: The answer of this question will be 0
Q: Complete the table for optimal page replacement. 0 1 2 3 1 4 1 5 3 4…
A: Best page replacement is the optimal page replacement algorithm. This is because this algorithm…
Q: Please make a code that will convert text to Huffman mode and vice versa. Consider the following…
A: Description: The following step is a Java code for generating the Huffman code given a set of…
Q: The expression =IF(A1 > 8, 12*A1, 7*A1) is used in a spreadsheet. Find the result if A1 is 5 Find…
A: We have expression IF(A1>8, 12*A1, 7*A1) When A1>8, then the result = 12*A1 Else A1≤8 then the…
Q: Prime number p = 3, q = 11, e = 3, m = 00111011 (m-message) then calculate private key d and cipher…
A: The question has been answered in step2
Q: What are the differences between ext2, ext3 and ext4 filesystem?
A: What are the differences between ext2, ext3 and ext4 filesystem ?
Q: Imagine you have a 20 GB file with one string per line. Explain how you would sort the file.
A: solution is given below:-
Q: Suppose we have 10 tasks for CPU1 to perform, and CPU1 takes 3 units of time to perform a task. o…
A: Answer) a) Throughput would be 1/3 of one task per unit time, or 0.33 tasks per unit time.
Q: 1 5 2 4 3 Adjacency Matrix Adjacency List 1 4 2 5 3 6 Adjacency Matrix Adjacency List
A: Adjacency matrix:- A 2D array called an adjacency matrix has the dimensions V x V, where V is the…
Q: Create a Java program to input integer from 1 to 9,999 (Range) and to output the inputted number in…
A: The question answer is as follows,
Q: Create an activity diagram to document the process of “withdrawing money from your account in the…
A: Introduction The actions that actually happen whenever a client or teller chooses Transfer Money…
Q: When looking at this code making recursive calls, how would I identify how many recursive calls are…
A: A recursive function is a function that repeats or uses a previous term to compute a subsequent term…
Q: For tax purposes an item may be depreciated over a period of several years, n. With the straight…
A: With the straight line method of depreciation, each year the item depreciates by 1/nth of its…
Q: A bit stream "1101011011" is being given as an input to a CRC
A: The answer is
Q: What is block cipher? Explain counter mode block cipher.
A:
Q: ANSWER THE FOLLOWING QUESTIONS Debug the given C program to read and print N array elements. Find 10…
A: Below I have provided a program for the given question. Also, I have attached a screenshot of the…
Q: A cell type might split into two or three every hour, or might die. The likelihood for splitting…
A: Below I have provided a program for the given question. Also, I have attached a screenshot of the…
Q: A multiprocessor has a 3.3 GHz clock (0.3 nsec) and CPI = 0.7 when refe
A: The answer is
Q: Things to consider before installing Linux?
A: Things to consider before installing Linux:-
Q: Q.30 Using Playfair cipher encrypt message. "We five in a world full of 'beauty" use key "ANOTHER.
A:
Q: Problem Description Use this project to write and run a C program that performs the following: O…
A: Array A grouping of related data types is called an array. For instance, if we need to store all…
Q: Pick a major company that you use on a regular basis. |List 5 items that would be signficant to an…
A: These question answer is as follows
Q: What problems are faced by SVM when used with real datasets?
A:
Q: Describe the steps that transform a program written in a high-level language such as C into a…
A: convert a text-based assembly language program from the C programming language (still in text…
Step by step
Solved in 2 steps

- Use S-DES to encrypt the plaintext block m = 00011010 using the key K = 1011000101. Show your work, labeling the result after each step and circling the final ciphertext cUse a Caesar Cipher with digraph coding to encrypt the following plaintext: ‘buffer’ with a key ofK=100. (Show your intermediate calculations and formulas used)Hint: Table below help you to find the code equivalent to each letter.Use the RSA cipher with public key n = 713 = 23 · 31 and e = 43 to encode the messages HELP into their numeric equivalents and encrypt them. Performs all step. Use pencil and paper to write the answer. show your work as well.
- Use a Caesar Cipher with digraph coding to encrypt the following plaintext: ‘buffer’ with a key ofK=100using RSA algorithm. Given two prime numbers, p.17, q=11, and e =7, generate a pair of public key and private key for Karen and Jeeny. Subsequently, encrypt the message "88'.Using the RSA algorithm, perform an encryption and decryption of:i. Message M=15 using prime numbers p=7 and q=5 ii. Message M=13 using prime numbers p=11 and q=7
- Use the modified Caesar cipher described in the assignment instructions to encrypt the following:Plaintext: UNDERSTANDKey: 8Use the modified Caesar cipher described in the assignment instructions to encrypt the following:Plaintext: ELECTRONICKey: 6Find the cipher text using RSA algorithm for the following information: Public key: {e, n} = {11, 221}Private key: {d, n} = {35, 221}Plain text: 8Decrypt the calculated cipher text using the above key and verify that the plaintext was 8. Writedown complete calculation procedures.
- Q5) Using RSA algorithm, Assume: p= 7 , q = 13, e = 5, d = 29.c) What is the ciphered text if the encrypted message = “P”?a) In RSA, given p = 7, q = 13, and e = 17, find n, Φ(n), and d. Further, find the ciphertext corresponding to plaintext 8 using RSA encryption algorithm.Use RSA encryption to post a message. Use the RSA scheme with p = 3 and q = 11.

