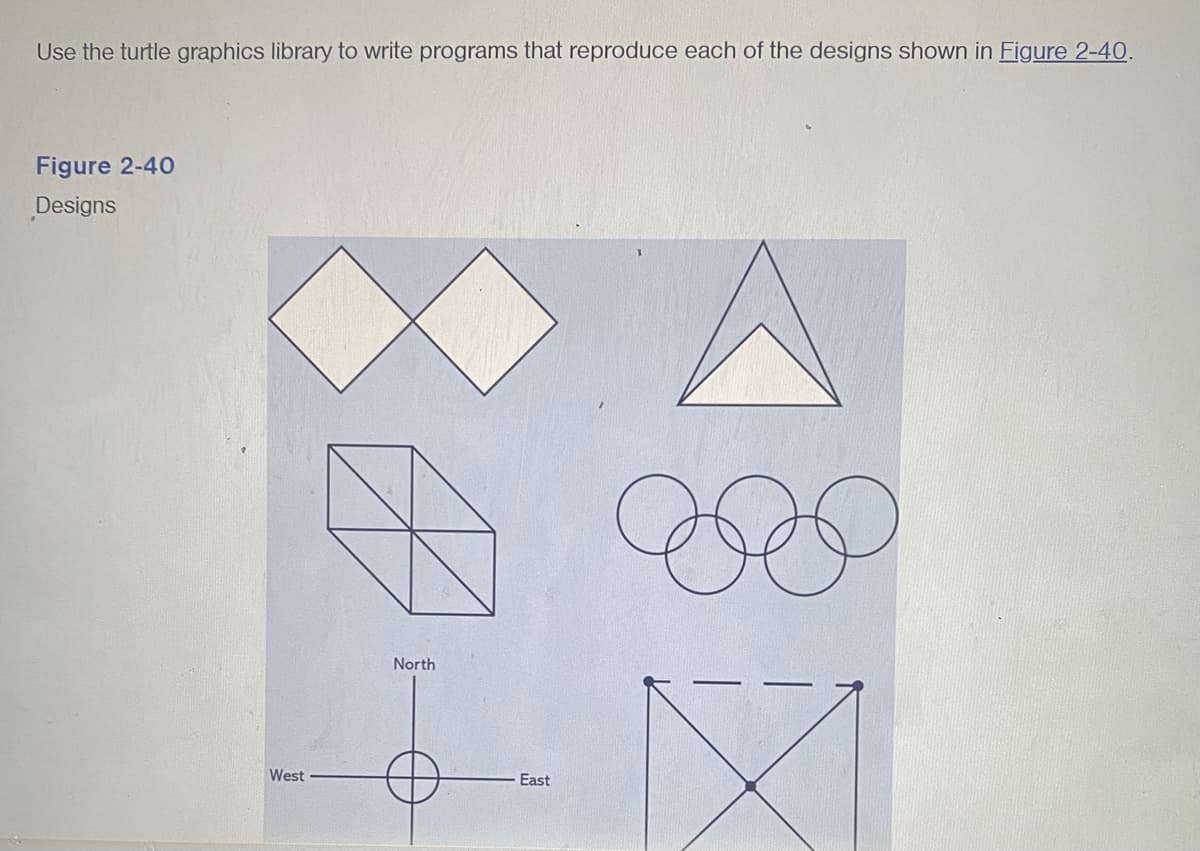
Use the turtle graphics library to write programs that reproduce each of the designs shown in Figure 2-40. Figure 2-40 Designs West North East Se D
Q: Give me at least two uses for convergence.
A: Introduction In this question, we are asked about the two use for convergence.
Q: microprocessors/micro-controllers More than 90% of the applications. Why? Could you explain this…
A: Introduction Microcontroller: In an embedded system, a microcontroller is a tiny integrated circuit…
Q: When and how did it start to become what it is today?
A: Introduction: Protecting computer systems and networks from unauthorised access to or disclosure of…
Q: Are there any downfalls to enterprise-wide networking? Explain the problems and what may be done…
A: INTRODUCTION: An enterprise network comprises physical and virtual networks and Protocols that…
Q: It provides backup for dividing apart a network. Using appropriate illustrations, please explain…
A: Network segmentation: Network segmentation involves dividing a network into smaller networks,…
Q: When does a system reach a deadlock state, and what requirements must be met to get there?
A: Introduction: - A deadlock is a state in a computer system where two or more processes are blocked…
Q: More disruption is forthcoming as the technological landscape continues to evolve at a breakneck…
A: Your answer is given below.
Q: Find out what the purpose of a file's extension is and how it relates to the document you're now…
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: There are a variety of ways in which Mercy might benefit from having an enterprise data model. As a…
A: Enterprise Data Model:- This model describes the need of entire organization or some major aspect of…
Q: Give an account of the steps involved in creating a video recording and how they relate to the…
A: The steps involved in creating a video recording are: 1. Conceptualization: Determine the goal and…
Q: Do you have any idea which errors are going to be the hardest to fix?
A: According to the inforamtion givne:- We have to define which errors are going to be the hardest to…
Q: There is a standard architecture upon which every software is developed. Identify and explain the…
A: In this question we need to explain different standard architectural patterns or motifs.
Q: Can you provide a brief summary of the compiler and elaborate on the idea of testability?
A: Find the needed response from the list below: Testability: Assessing the software's or unit's…
Q: Implement the 'nx' loop which copies the data from the packet into the local buffer, one character…
A: Please refer to the following step for the complete solution to the problem above.
Q: How well versed are you in the Compiler Phases and their constituent parts? To help me better…
A: Compiler: A compiler is a type of computer program that takes source code written in a programming…
Q: Take the multiprocessor with 30 processors, each processor is capable od max 2Gflops. What is the…
A: Dear Student, The answer to your question with calculations is given below -
Q: Don't just argue on the basis of performance; provide concrete examples of how deep access is…
A: Only when a procedure can be sent as an argument to a function does deep/shallow binding make sense.…
Q: Give the developer's opinion on why deep access is better than shallow access rather than just…
A: Deep access refers to the way of accessing variables that are not local to the programme, and it is…
Q: . Using the graph below, implement the Breadth First Search algorithm considering the final state is…
A: Introduction Breadth first search (BFS): An algorithm for navigating or searching over trees or…
Q: Some individuals who specialise in information technology believe that former computer criminals…
A: Ethical hackers can work in a way to help the IT companies defining their IT security measures. They…
Q: Is there a method to simulate a login on a website?
A: There are several ways to assess a web application's login capabilities: Use a legitimate account…
Q: Could you please provide more information regarding VPN servers?
A: VPN servers are a key technology in modern networking that allow secure remote access to a private…
Q: To what extent may regulations be enforced via the use of password protection and other forms of…
A: In order to increase and keep standards high, enforcement is crucial. Implementation might stop…
Q: In what contexts may we see Overfitting at play?
A: Overfitting is a common problem in machine learning when a model is trained too well on the training…
Q: Take the multiprocessor with 30 processors, each processor is capable od max 2Gflops. What is the…
A: Amdahl's Law is a theoretical model used to predict the performance improvement of a parallelized…
Q: What are the three most important qualities that must be present in a network for it to be effective…
A: Reliability: The network must be able to consistently perform as expected and provide uninterrupted…
Q: Please send me answer of this code from the given output ,just i have written the code but some…
A: Please refer to the following steps for the complete solution to the problem above.
Q: In general, smartphones and other mobile devices employ what kind of computer architecture? Can you…
A: In general, smartphones and other mobile devices use Reduced Instruction Set Computing (RISC)…
Q: To what extent is it possible to distinguish between "many threads" and "many processes" operating…
A: Introduction: The smallest group of programmed instructions that may be independently controlled by…
Q: How do you make sure that the firewall you're managing is as effective as possible? Explain
A: Define: Firewalls prevent illegal access to computers. Unfortunately, today's PC environment has…
Q: We have two men m and m′ and two women w and w′. m prefers w to w′. m′ prefers w to w′. w prefers m…
A: We need to: (a) Use the Gale-Shapley algorithm to find a stable matching of this instance. (b) Show…
Q: 1. A router receives a packet with destination address (222.186.114.16) Show how it finds the…
A: When a router receives a packet, it needs to determine the correct path to forward the packet to its…
Q: Can you provide me an instance of a cutting-edge database system?
A: INTRODUCTION: Database Systems, also known as Database Management Systems or DBMS, are pieces of…
Q: Can a single process get stalled in the middle of execution? Your answers should make sense and…
A: Introduction Process execution is the process of running a program or application on a computer or…
Q: Utilizing a wide range of various approaches may make it much simpler for managers to compare and…
A: Performance Result Analysis: Performance testing's most technical part is result analysis. A…
Q: For protecting sensitive information, what do you think is the most crucial step to take? If data…
A: The answer is given in the below step
Q: What are the benefits of using a firewall, and how do you go about installing one in your computer…
A: Positives of firewalls | Benefits of firewalls: A firewall is a security tool that may help protect…
Q: How exactly should a corporation store and organise its passwords?
A: To secure the sensitive information, corporations should adhere to best practices for password…
Q: 1. Print the Elements of a Multidimensional Array by CodeChum Admin A multidimensional integer array…
A: Below is the complete solution with explanation in detail for the given question in Java Programming…
Q: What simple steps must be taken if you want the computer to first check the CD-ROM for the boot…
A: When a computer is switched on, the procedure that launches its operating system is known as…
Q: Is there a list of necessary conditions to avoid a standstill?
A: IT Project: An IT project is a project that uses information technology to deliver specific…
Q: Fixing the computer disk issue caused by incorrect CMOS settings. Do you mind elaborating?
A: Fixing the computer disk issue caused by incorrect CMOS settings typically involves accessing the…
Q: What exactly is meant by the phrase "Structure" in this statement?
A: Due to this: What does the Structure statement really mean? Explanation: The structure-related…
Q: In what circumstances do you consider tacacs+ to be a more desirable solution than either RADIUS or…
A: 1) Authentication, Authorization, and Accounting, referred to as AAA (Triple-A), provide the…
Q: Describe the basic principles of a key control plan. How can the use of card operated locks enhance…
A: A key control plan is a set of procedures and policies that govern the management and distribution…
Q: When someone refers to "system security," what precisely are they talking about?
A: Introduction: System protection: It is a method for protecting the privacy and security of the…
Q: To what extent do you believe networking to be critical to the development of IT?
A: Introduction: Even if you are not actively looking for job, it may still help you improve…
Q: Can confidentiality and/or integrity be enforced via the use of biometric verification? Discuss
A: Biometric verification is a popular way to enforce confidentiality and/or integrity in various…
Q: What is Moore? What gives him the authority to discuss ICs? What does "debugging" even mean? What is…
A: Objective: This answer needs terminology definitions. Digital electronics terminology. Famous…
Q: Your expectations for managing a team are as follows, correct? Which components of management do you…
A: Software development: Software development is the process of creating, designing, developing,…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Write code (python) to generate and display an image like this. Be sure to get the location of the center correct, the number of rings, and the number of pixels in vertical and horizontal direction. Don’t worry about the exact name of libraries to import in pythonUsing Turtle Graphics, write a program that will produce 2 Zs next to each other. It is irrelevant where these Zs appear and what size they are as long as they are produced NEXT to each other.Write a Python program using Turtle graphics library, that displays a STOP sign, as shown in Figure below. The hexagon needs to be in red and the text needs to be in white colour.
- please draw one using simple graphics functions on Python and show stepsWrite a program that generates the following figures by using the turtle graphics library.programming language is spyder!I need a code for simple image processing/game graphics that is ready to paste in python application for deal or no deal game.
- I am doing a research in astrophysics. I need to deproject the galaxy images to face-on orientation. Please give me a Python code to get the face-on orientation of the images.Given two images, one left and one right do the following: 1.Write a program in Python to stitch the two images with openCV together when two computers are connected to two projectors. Include comments in your codethis code is in (.c) and I need help with what is in the imageI have already done part one and now need help with the second part below is what I have so far /*KL25Z_LED_Blinky.c*/ #include <stdint.h> /* provides fixed width integer types. For example, uint32_t) */#include "derivative.h" /* KL25Z info */#include "mcg.h" /* main clock generator */#include "systick.h" /* SysTick timer */#include "KL25Z_gpio.h" /* GPIO routines */#include "KL25Z_port.h" /* PORT routines */#include "delays.h" /* software based delays */ /* Macro definitions */#define RED_LED_PIN 18 /* GPIO and PORT module "pins", not the device pins */#define GREEN_LED_PIN 19#define BLUE_LED_PIN 1#define LED_OFF 1#define LED_ON 0 /* Globals */volatile uint32_t sysTicks; /* required for SysTick support. Do not delete. */ int main(void) { /* Set of the main clock to run at 48 MHz and turn on SysTick** The student should not make changes here unless instructed to do so.*/pll_init(8000000,0,1,4,24,1); // In mcg.c sets…

