Using python, Write a program that generates a list of 10 valid lottery tickets and then prints out the tickets, 1 per line. Valid lottery tickets in Indiana have 6 values: 5 numbers from 1 to 69 (represented by white balls) 1 number from 1 to 26 (representing the red Powerball) A valid lottery ticket might look like: 29-1-65-44-39-PB5 Sample output:
Using python, Write a program that generates a list of 10 valid lottery tickets and then prints out the tickets, 1 per line. Valid lottery tickets in Indiana have 6 values: 5 numbers from 1 to 69 (represented by white balls) 1 number from 1 to 26 (representing the red Powerball) A valid lottery ticket might look like: 29-1-65-44-39-PB5 Sample output:
Chapter6: System Integration And Performance
Section: Chapter Questions
Problem 3PE
Related questions
Question
Using python, Write a
Valid lottery tickets in Indiana have 6 values:
- 5 numbers from 1 to 69 (represented by white balls)
- 1 number from 1 to 26 (representing the red Powerball)
A valid lottery ticket might look like: 29-1-65-44-39-PB5
Sample output:
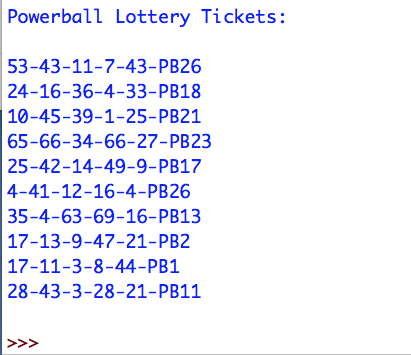
Transcribed Image Text:Powerball Lottery Tickets:
53-43-11-7-43-PB26
24-16-36-4-33-PB18
10-45-39-1-25-PB21
65-66-34-66-27-PB23
25-42-14-49-9-PB17
4-41-12-16-4-PB26
35-4-63-69-16-PB13
17-13-9-47-21-PB2
17-11-3-8-44-PB1
28-43-3-28-21-PB11
<<<
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning