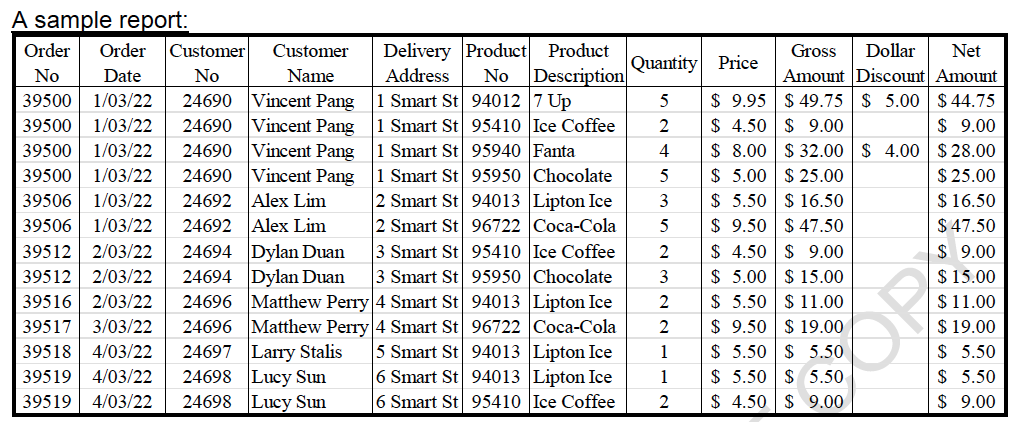
Using the above table structure, create a normalized Entity-Relationship Model (ERM). Identify Primary Key(s) and Foreign Key(s) for all the entities, connectivities and/or cardinalities, and relationships between the entities. As for Chen's ERM notation and the normalization, the level should be in Third Normal Form (3NF) and above. [Note: you do notneed to show the normalization process such as the functional dependency diagram.]
Using the above table structure, create a normalized Entity-Relationship Model (ERM). Identify Primary Key(s) and Foreign Key(s) for all the entities, connectivities and/or cardinalities, and relationships between the entities. As for Chen's ERM notation and the normalization, the level should be in Third Normal Form (3NF) and above. [Note: you do notneed to show the normalization process such as the functional dependency diagram.]
Chapter7: Developing An Excel Application
Section: Chapter Questions
Problem 3.13CP
Related questions
Question
- Using the above table structure, create a normalized Entity-Relationship Model (ERM). Identify Primary Key(s) and Foreign Key(s) for all the entities, connectivities and/or cardinalities, and relationships between the entities. As for Chen's ERM notation and the normalization, the level should be in Third Normal Form (3NF) and above. [Note: you do notneed to show the normalization process such as the functional dependency diagram.]
Transcribed Image Text:A sample report:
Order Order Customer
Customer
Delivery Product
Product
Address No Description
No
Date
No
Name
1 Smart St
1 Smart St
94012 7 Up
95410 Ice Coffee
95940 Fanta
1 Smart St
1 Smart St 95950 Chocolate
2 Smart St 94013 Lipton Ice
39500 1/03/22 24690 Vincent Pang
39500 1/03/22 24690 Vincent Pang
39500 1/03/22 24690 Vincent Pang
39500 1/03/22 24690 Vincent Pang
39506 1/03/22 24692 Alex Lim
39506 1/03/22 24692 Alex Lim
39512 2/03/22 24694 Dylan Duan
39512 2/03/22 24694
39516 2/03/22
24696 Matthew Perry 4 Smart St 94013 Lipton Ice
39517 3/03/22 24696 Matthew Perry 4 Smart St
39518 4/03/22 24697 Larry Stalis 5 Smart St
39519 4/03/22 24698 Lucy Sun 6 Smart St
39519 4/03/22 24698 Lucy Sun 6 Smart St
2 Smart St 96722 Coca-Cola
3 Smart St 95410 Ice Coffee
Dylan Duan
3 Smart St 95950 Chocolate
96722 Coca-Cola
94013 Lipton Ice
94013 Lipton Ice
95410 Ice Coffee
Quantity Price
5
2
4
5
3
5
2322
Gross Dollar Net
Amount Discount Amount
$9.95 $49.75 $5.00 $44.75
$4.50 $9.00
$9.00
$8.00 $32.00 $4.00
$28.00
$5.00 $25.00
$25.00
$5.50 $16.50
$16.50
$47.50
$9.00
$9.50 $47.50
$4.50 $9.00
$5.00 $15.00
$5.50 $11.00
$9.50 $ 19.00
$15.00
$11.00
$19.00
$5.50 $ 5.50
$ 5.50
$5.50 $5.50.
$ 5.50
$4.50
$9.00
$ 9.00
1
1
2
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage