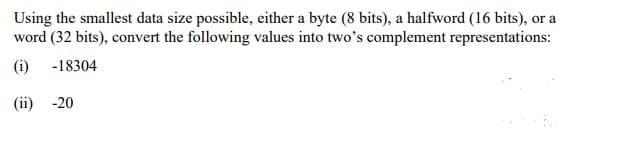
Using the smallest data size possible, either a byte (8 bits), a halfword (16 bits), or a word (32 bits), convert the following values into two's complement representations: (i) -18304 (ii) -20
Q: The Springfork Amateur Golf Club has a tournament every weekend. The club president has asked you to…
A:
Q: time domain specification? define corner frequency ?
A: The answer for the above mentioned question is given in the following steps for your reference.
Q: Suppose we have a matrix A of dimension n x n of rank n - 1. Explain two numeri cally stable ways to…
A:
Q: Write a program that takes an integer as an input and returns whether it is a prime number or not.
A: Q. Write a program that takes an integer as an input and returns whether it is a prime number or…
Q: In this problem, you will write a solution to the Fizz Buzz problem (description to follow) within…
A: Here is c++ program with implement of code:
Q: Suppose a switch is built using a computer workstation and that it can forward packets at a rate of…
A:
Q: d) Show how the decimal floating point number -76.310 is stored in the computer's storage using…
A: The IEEE Standard for Floating-Point Arithmetic (IEEE 754) is a technical standard for…
Q: n closing a TCP connection, why is the two-segment-lifet out not necessary on the transition from…
A: Introduction: Below describe When closing a TCP connection, why is the two-segment-lifetime timeout…
Q: When it comes to cloud security, what is the "shared responsibility" paradigm like?
A: Answer: The industry has coined the term "Shared Responsibility" to describe the tasks and…
Q: signal.. Each time slot contains 148 bits. Just 114 of these 148 bits reflect speech or other info.…
A: The answer is
Q: Please provide me a C program that prints the message "C Programming." in the output 10 times using…
A: The question has been answered in step2 successfully
Q: 1.Accept a command line argument which is the purchase data file in the following format: Here is an…
A: File content: 200 CSCO 24.00 50 IBM 130.00 100 AAPL 94.28 Program: #include <iostream>#include…
Q: (x) Show the most popular destination for all passengers. (xi) How many passengers can be…
A: x. A query that gives the most popular destination for all passengers: SELECT TO FROM RIDE GROUP BY…
Q: When closing a TCP connection, why is the two-segment-lifetime timeout not necessary on the…
A: Introduction: TCP is nothing but connection-oriented, and an association between client and server…
Q: Apex Assignment: Create a apex class called addition and then create a method to add the 2 integer…
A: Apex is a program language which is used to create the salesforce Backend and mostly Salesforce…
Q: . Suppose a 10-Mbps Ethernet hub (repeater) is replaced by a 10-Mbps switch, in an environment where…
A: Ethernet hubs are multiport repeaters that help expand the physical medium and give network devices…
Q: *From now and on yourLastName will be changed to your last name. *Your program should change White…
A: PSEUDO-CODE: Declare variables Input employee_name, hourly_salary, working_hours annual_salary =…
Q: in c# please Write method QualityPoints that inputs a student’s average and returns 4 if the…
A: As per the requirement program is developed. Algorithm: Step 1: Write the main method. Step 2:…
Q: used: (a) Circuit switching; (b) Virtual circuit and datagram packet switching. The stati hops (1…
A: The answer is
Q: O Discuss THREE (3) difficulties in implementing law enforcement on cybercrime.
A: 1. Data Loss Law enforcement changes, such as the GDPR, may deny access to data or severely…
Q: In C program. implement list_find( list_t* list, int targetElement ) function /* * dataStructure.h *…
A: The answer is given below.
Q: .2.2 function call with parameter: printing formatted measurements
A: The answer is given below.
Q: 1.4 What output would be produced from the following C++ code fragment: vector myList (4), mylist…
A: C++ Many people believe that C++, an object-oriented programming (OOP) language, is the finest…
Q: I am getting the following error in my C Program.
A: After fixing the code, I have provided C CODE along with CODE SCREENSHOT and OUTPUT…
Q: Discuss THREE (3) key features of digital watermarks.
A: A digital watermark is a process of embedding digital data into the photograph or other media that…
Q: Consider the following scenario: Universiti Tun Hussein Onn Malaysia (UTHM) is planning to…
A: A technology that is use to identify the information which is embedded into the data carrier in ways…
Q: What security flaws are exploited and how may these issues be addressed in the future in the case of…
A: Introduction: Data damage is defined as any decrease in data integrity or availability. Damage to a…
Q: c) A control protocol is used alongside the IP to support its operation: i) What is the name of the…
A:
Q: Using python, consider the following function: f(x)= sin (4(x-1/4)) for x€[0,2]. 1. Plot the…
A: Answer:- Given Function :- f(x)= sin (4(x−1/4)) for x∈[0,2] The expression in Sin() function can be…
Q: X; cout << Y; Z = X + Y; cout
A: Given below.
Q: {O <a | u_z+u4L+ue } }
A: Each transition represents (from State, symbol, stack1Top, stack2Top) -> (to State, symbol,…
Q: When it comes to cloud security, what is the "shared responsibility" paradigm like?
A: Answer: The industry has coined the term "Shared Responsibility" to describe the tasks and…
Q: Suppose a bridge has two of its ports on the same network. How might the bridge detect and correct…
A: It has been configured like, having two of its ports on the same network. So we have to create a new…
Q: Suppose a bridge has two of its ports on the same network. How might the bridge detect and correct…
A: The question has been answered in step2
Q: Make a superclass called Language,then a child class called Node to extend it. Create a method…
A: Make a superclass called Language,then a child class called Node to extend it. Create a method…
Q: An online warehouse provides features for their customers to browse and search products and to place…
A: Solution:: Package diagram, a kind of (related to what holds something together and makes it…
Q: Apex Assignment: Create a apex class called addition and then create a method to add the 2 integer…
A: The Salesforce Backend was built using the programming language Apex, and most of the functionality…
Q: Q2) A) Using the RSA Public-Key Cryptosystem with: n=77 0(n)-60, and e=37 1) Find the privet…
A:
Q: Justify the requirement for a trained project manager to oversee complicated tasks.
A: According to the question the project manager always has power to conduct something explain everyone…
Q: This program was run once and the output was 15. If we run this program another 100 times how many…
A: Here we have a code written in C++ programing language. Inside the main block, we have used rand()…
Q: (a) Young's double-slit experiment is performed with 525-nm light and a distance of 2.00 m between…
A:
Q: Consider an ARQ protocol that uses only negative acknowledgments (NAKS), but no positive…
A: Introduction ARQ is only a programmed recurrent solicitation that depends on acknowledgment and…
Q: When it comes to cloud security, what is the "shared responsibility" paradigm like?
A: Introduction: One type of cloud security model is the shared accountability paradigm. In order to…
Q: 28. In stop-and-wait transmission, suppose that both sender and receiver retransmit their last frame…
A:
Q: Suppose you are designing a sliding window protocol for a 1-Mbps point-to-point link to the…
A:
Q: 1. Consider the network shown in Figure 4.28, in which horizontal lines represent transit providers…
A: Below is the answer to above question. I hope this will be helpful for you..
Q: In a Python program, how do you convert data entered at the keyboard into a whole number? a. Just…
A: Dear Student, When we take input in python its in string (str) format to convert it to whole numbers…
Q: Please do it with regular expression. Don't use loops please. Do fast, I have no time left Write a…
A: //java code given below:
Q: d. Apply the Binary Search Algorithm, as performed during class, show Use the Algorithm presented…
A: The given List = [ 2 , 4 , 7 , 10 , 11 , 34 , 50 , 59 , 60 , 66 , 69 , 70 , 79 ] and we have to…
Q: Briefly explain DBMS
A: Database Management Systems(DBMS) are software systems used to store, retrieve, and run queries on…
Step by step
Solved in 3 steps

- Data represented in ________ is transmitted accurately between computer equipment from different manufacturers if each computer’s CPU represents real numbers by using an IEEE standard notation.1) Assume we have 8 bit (1 byte) 2's complement system with a 3-bit fractional. Find a decimal representation of 2's complements binary number 1011 0101.001 2) Assume we have a byte system for the fixed number representation (the whole number is presented with 8-bits (one byte) and the fractional part is presented with 2-bits), find the 2's complement of 0110 0010.01Suppose an 8-bit data word stored in memory is 11000010. Using the Hamming algorithm, so determine: - what check bits would be stored in memory with the data word. - Show how you got your answer.
- Calculate (3.41700875 *10-3 + 6.34005625*10-3)* 1.25625* 102 by hand, assuming each of the values are stored in the 16-bit half precision format describedin in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to thenearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.a) A digital sound recorder captures sound from the real-world, processes the audio and stores it in binary form. Using the principles of digital signal processing, practically explain how this phenomenon occurs. b) Use the two’s complement binary representation to represent each of the following integers as 10-bit binary numbers.i) -13710 ii) 14510 iii) -15810 iv) 16710 v) -11510 c) If an 8-bit binary number is used to represent an analog value in the range from 0 to 100kg, what does the binary value 011001002 represent?Convert each of the following base ten representations to its equivalent two’s complement form using patterns of 8 bits: 6 = -6 = 13 =
- Assume we have 16-bit (2 bytes) 2's complement system with a 2-bit fractional. Find a decimal representation of 2's complements number 1111 1111 1110 0111.11 It will display your answer with commas every third digit No hand written and fast answer with explanationRepresent the following decimal numbers in binary using 8-bitsigned magnitude, one’s complement, two’s complement, andexcess-127 representations:1. a) 972. b) −973. c) 444. d) −44Short questions: Q. If 8 Bits are equals to 1 byte then how many bytes can be formed in 67464 Bits?
- Calculate (4.41762275 *10-3 + 6.34225625 *10-3) * 1.05225 * 102 by hand, assuming each of the values are stored in the 16-bit half precision format described in in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to the nearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.Please explain step by step. Double precision of 64 bits, where 11 bits are exponents, and 52 bits of mantissa. a) Explain the magnitude of 2^(2^10-1) or 2^1023 for overflow and 2^(-2^10) or 2^(-1024). b) find how many digits are there in 2^52, the mantissa..How many redundant bits are needed for code in comparison to how many bits are needed for data?

