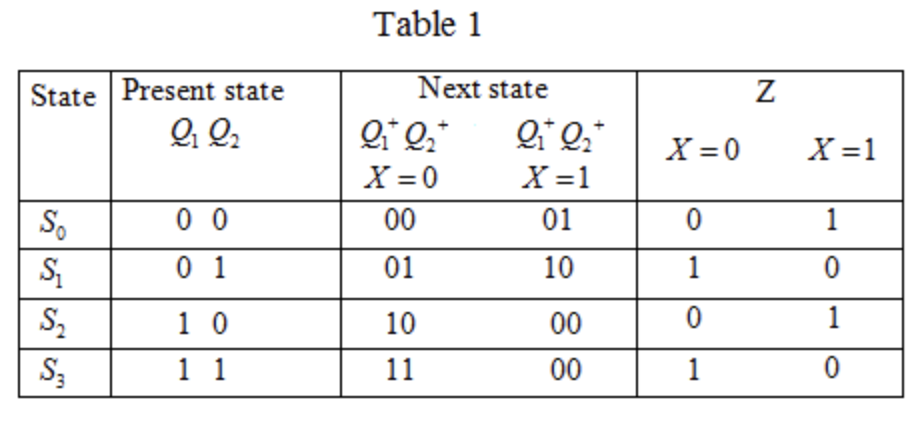
Using the state equations and/or state table in the picture. Present a circuit. Use D Flip Flop along with any logic gate or combinatorial circuit seen in class. Clearly label all inputs and outputs.
Q: Computer science What is the purpose of concurrency control?
A: Introduction: Concurrency Control's Goals Data integrity issues can develop when two update…
Q: Which current trends in cybercrime should you be on the lookout for? Do you know how to respond to…
A: Given: Social engineering assaults and cyber fraud were the most generally reported dangers. This…
Q: What are the advantages of using Firewall rules?
A: Introduction: There Are so many benefits benefits of Firewall.
Q: Why is it so important to know how to work with compressed zip files and folders?
A: ZIP archives and folder compresses A compressed ZIP file is a single file or folder that contains…
Q: In multilevel inheritance one class inherits More than one class O Only one class O As many classes…
A: Inheritance: The mechanism in which one class inherits the property of other class is called as…
Q: What are the primary distinctions between a local-area network and a wide-area network when it comes…
A: Introduction: LAN A local area network (LAN) is a collection of computers and peripheral devices…
Q: Describe the TCP/IP protocol suite's architecture. Consider the ISO / OSI architecture as a…
A:
Q: Migrating a server database has a variety of hazards.
A: Migrating to the cloud: From regulatory violations and contractual breaches to unsecured APIs,…
Q: Computer science Short answer -What do you think about data hiding, data encapsulation and…
A: Introduction: Data are measurable information units gained via analysis. Object-Oriented Programming…
Q: ?following C++ code #include #include using namespace std; class A { float d; public: ACO{…
A: In this question, we have given a C++ code. This code involves class and constructor. We have to run…
Q: Explain the key distinction between recurrent and non-recurrent neural network processing.
A: Recurrent Neural Network: A sort of artificial neural network in which linkages between units are…
Q: f a database is compromised, what would happen as a result? What are the most frequent blunders that…
A: Referential integrity is a property of information expressing that every one of its references are…
Q: What is the significance of wildcards and serialization? Justify your response by providing an…
A: A wildcard character is used to substitute one or more characters in a string. Wildcard characters…
Q: how cybercrime manifests itself in several ways Is there a possibility to stop cybercrime via the…
A: Introduction: Many privacy issues develop when sensitive information is intercepted or disseminated…
Q: For large values of n which statement is true? a. 2n^3 behaves like n^3 b. 2n^3 + 4n^2 + 17n behaves…
A:
Q: Hashing passwords in a file is prefered over encrypting the password file because hashing passwords…
A: Introduction Password encryption is a more secure option than password protection. Because you…
Q: Why is the public-key method of encryption so crucial in internet commerce?
A: We need to explain, why public key method of encryption is crucial in internet commerce.
Q: What are the most popular interior and outside routing protocols in today's networks?
A: Interior Gateway Protocol (IGP): Interior Gateway Protocols (IGPs) routing protocols that are…
Q: How would you describe technology?
A: Introduction: Technology is the application of scientific knowledge to the practical goals of human…
Q: The workings of a computer network are explained here. Numerous components are there in the network?…
A: Computer Networks: In IT(information technology), computer networks are the backbone of…
Q: Computer science What is network protocol? Explain the following network protocols (in your own…
A: Introduction: What is network protocol? Explain the following network protocols (in your own words…
Q: In terms of a number, what does a bit that is turned on represent? In terms of a number, what does a…
A: Introduction: In computers, a bit is the most fundamental unit of data. It stands for binary digit,…
Q: What is the difference between keeping hashed passwords in a file and using a computer to store an…
A: Password Database: The user's password is concatenated with a static salt and a randomly generated…
Q: What are the different layers of abstraction in TCP/four IP?
A: ANSWER:-
Q: What are the advantages of floating point number over integers.
A: Introduction What are the advantages of floating point number over integers.
Q: What was the driving force behind the creation of programming languages for computers?
A: Introduction: Computer programming language, for example, is a language for displaying a certain set…
Q: What are some of the risks faced by consumers who use mobile devices for banking and other financial…
A: Use of mobile devices with internet to carry out the financial transaction from one bank account to…
Q: What is the definition of a popular website? What options are available to small enterprises if they…
A: Enterprise: A for-profit firm or corporation is known as an enterprise, however it is most typically…
Q: Consider the experiment where a penny is flipped, a quarter is flipped, and a 6-sided die is rolled.…
A: In the below step you can find the complete explanation in handwritten.
Q: What is the difference between scripts and stored procedures? What roles do each of these play? What…
A: Introduction: A Stored Procedure is sometimes known as a script.
Q: Three-tier architecture refers to the intermediate layer between the database and the client…
A: Solution: The most appropriate option is to use an application server.
Q: Other parties cannot directly interact with data storage. When constructing Data Flow Diagrams,…
A: Data Flow Diagram: In the data flow diagram, the foreign company is represented by the square box,…
Q: Why should we care about the information management and technology aspects of our information…
A: Information management and technology plays very important role in maintaining a information system.
Q: Find "Announcing the Advanced Encryption Standard (AES)" on the internet. This FIPS 197 standard…
A: Advanced Encryption Standard (AES): The Advanced Encryption Standard (AES) is a set of rules for…
Q: When it comes to healthcare data/cybersecurity breaches, what are the best outcomes?
A: The transformation of the healthcare industry from one that uses the paper-based system to one that…
Q: In the von Neumann paradigm, explain the roles of the: a) processor unit and b) program counter.
A: Von Neumann's architecture is based on the stored-program computer concept, where instruction data…
Q: There is a reason for this: computers have become so advanced. How can we establish that computers…
A: Advanced Computer: Advanced computing refers to a set of abilities that may be applied to personal…
Q: Describe how you use databases or applications connected to databases in your daily life. Consider…
A: A database: A database is the collection of information that is kept on a server. The data is…
Q: List four criteria for comparing the packages used by enterprises to track software development…
A: Given statement: List four criteria for comparing the packages used by enterprises to track software…
Q: The data description language is a notation that is used to express the structure and organisation…
A: A brief introduction : Data description language is a notation for defining the shape and…
Q: Computer science Explain how a Computer may be used by a) A manager of a Shopping mall
A: Introduction: For stock maintenance, official and employee information, displaying data, occasional…
Q: A/An . is the definition of a collection of one or more methods, and zero or more attributes.
A: Understanding through one line definition: Component diagram: It is aspect heard in UML which is…
Q: What are some indicators that a system's useful life is drawing to a close?
A: Answer:- The first indicator of a system's useful life is the system's ability to generate stable…
Q: What are the most popular interior and outside routing protocols in today's networks?
A: Foundation: Its internet layer or network layer offers necessary addressing information to enable a…
Q: Explain normalised form in a few words.
A: Introduction: The process of building a relational database in normalised form is known as…
Q: 1. Economic Policy: The following rules illustrate traditional economic policy theory in terms of…
A: Your C++ program is given below as you required with an output.
Q: If hierarchical inheritance requires to inherit more than one class to single class, which syntax is…
A: Inheritance is the feature of programming language through which one class can acquires/inherits the…
Q: In the Cyclic redundancy check (CRC) decoder, divide two occurrences.
A: Answer:- Cyclic Redundancy Check (CRC): A cyclic redundancy check (CRC) is an error-detection…
Q: A clique in an undirected graph is a subgraph wherein every two nodes are connected by an edge.…
A: A clique is complete subgraph of any graph which means that nodes of the subgraph are connected…
Q: The probability of event A is 0.4. The probability of event B is 0.3. The probability of event A U B…
A: We know the probabilities of the events are as follows: P(A) = 0.4 P(B) = 0.3 P(A ∪ B) = 0.5
Using the state equations and/or state table in the picture.
Present a circuit. Use D Flip Flop along with any logic gate or combinatorial circuit seen in class. Clearly label all inputs and outputs.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Which of the following can contain repeating groups?a. unnormalized datab. 1NFc. 2NFd. 3NFThe following table shows a list of pets and their owners that is used by a veterinarian service. P_Name Type Breed DOB Owner O_Phone O_E-mail Kino Dog Std. Poodle 3/27/97 M. Downs 5551236 md@abc.com Teddy Cat Chartraux 4/2/98 M. Downs 1232343 md@abc.com Filo Dog Std. Poodle 2/24/02 R. James 2343454 rj@abc.com AJ Dog Collie Mix 11/12/95 Liz Frier 3456567 liz@abc.com Cedro Cat Unknown 12/10/96 R.James 7865432 rj@abc.com Woolley Cat Unknown 10/2/00 M. Trent 9870678 mt@abc.com Buster Dog Collie 4/4/01 Ronny 4565433 ron@abc.com a. Describe 4 problems that are likely to occur when using this table. b. Break the table into two tables in a way that fixes the four problems.BookID CustID Name Phone DateTimeRented DateTimeReturned 1 10 Henry Lawson (802)218-7318 (802)584-8249 7/22/2006 7:00:00 PM 7/23/2006 10:00:00 PM 2 3 Bob O'Connor (802)918-7565 7/21/2006 1:00:00 PM 7/22/2006 5:00:00 PM 3 6 Cary Jones (603)536-8739 7/21/2006 6:00:00 PM 7/22/2006 10:00:00 AM 4 4 Harry Salomon (603)536-7565 7/12/2006 10:00:00 AM 7/13/2006 9:00:00 AM 5 5 Mary Combs (603)536-3632 7/17/2006 4:00:00 PM 7/18/2006 3:00:00 PM 6 7 Mary Tyler (603)669-7431 7/10/2006 8:00:00 PM 7/11/2006 10:00:00 AM 7 2 Bonnie Artest (603)819-0387 7/1/2006 5:00:00 PM 7/2/2006 11:00:00 AM 8 9 Bobby Lamson (603)347-5592 7/11/2006 4:00:00 PM 7/12/2006 10:00:00 PM 9 1 Lorry Kovacs (603)536-0987 (603)536-1294 7/23/2006 7:00:00 PM 7/24/2006 6:00:00 PM 10 4 Harry Salomon (603)536-7565 7/20/2006 5:00:00 PM 7/21/2006 4:00:00 PM 11 8 Johny Milano…
- So here VRC will be last row: 01110011 and LRC will be last column- 00000000110001100 or we can write it as:110001100 Follow up Question: What will be the indicate the character that should be given the VRC and LRC above. ThanksPopulate the CUST_NUM, INV_DATE, and INV_AMOUNT fields with the following customers: CUST_NUM INV_DATE INV_AMOUNT 1000 2016-03-23 235.89 1001 2016-03-23 312.82 1001 2016-03-30 528.10 1000 2016-04-12 194.78 1000 2016-04-23 619.44Normalize the following table to the 3rd Normal form: Student Student Phone Course Term Grade Instructor Instructor Phone Lauren Fernell 555-7771 MIS 350 F12 A Hess 555-2222 Lauren Fernell 555-7771 MIS 372 F12 B Sarker 555-2224 Lauren Fernell 555-7771 MIS 426 F12 A Fuller 555-2227 Lauren Fernell 555-7771 MIS 375 F12 B+ Wells 555-2228 Brigit Schnieder 555-2215 MIS 350 F12 A Hess 555-2222 Brigit Schnieder 555-2215 MIS 375 F12 B+ Wells 555-2228 Brigit Schnieder 555-2215 MIS 372 F12 A Sarker 555-2224 Brigit Schnieder 555-2215 MIS 374 F12 B Clay 555-2221 Jackie Judson 555-1245 MIS 350 F12 A Hess 555-2222 Jackie Judson 555-1245 MIS 372 F12 B+ Sarker 555-2224 How many tables did you create after normalizing the table? List each of…
- You need to show detail work on how you get the answer. Dont use answers from other websites please! Please type your answer not picture 1. Using the CRC polynomial 1101, create the CRC code word for the information word 01010101. 2. Compute the Hamming distance of the following code words: 0011010010111100 0000011110001111 0010010110101101 0001011010011110Please complete this code for the attache question: List P = 16F877A PORTA EQU h'05'TRISA EQU h'85'PORTC EQU h'07'TRISA EQU h'87'STATUS EQU h'03' BSF STATUS,5MOVLW h'FF'MOVWF TRISCCLRF TRISABCF STATUS,5 ... ... .. ENDWite a python program to display a table in the browser that shows the total number of cases for each state in the USA from COVID19Py API. A sample table is provided below State Total Number of cases Alaska 448737 Alabama 98987 .......

