Using the Use Case Diagram and Class Diagram modeling a food delivery system, create a context diagram for the system.
Q: Discuss the importance of responsive web design and its role in the development process.
A: Responsive web design is the cornerstone of a user-centric and adaptable online experience. Imagine…
Q: Perform Heapsort for the below input. Show all steps clearly for full score A = [35, 57, 46,…
A: SOLUTION -Pseudocode for the Heap Sort algorithm:1function heapify(arr, n, i): 2 largest = i 3…
Q: Please help with detailed explanation for problem C, don't copy solutions from other sources.…
A: In a direct-mapped cache, each block in main memory maps to exactly one block in the cache. Given…
Q: Explain the deployment phase in web development and the considerations involved in launching a…
A: The deployment phase in web development marks the transition from the development environment to…
Q: Design an algorithm to solve the given problem: You are given an integer array coins representing…
A: Decision Tree and Repeated Sub-Problems:Create a decision tree to represent all possible…
Q: memory
A: Computer systems' memory is essential for both storing and retrieving data. Computer memory is…
Q: Provide an overview of the file system architecture in macOS, detailing its key components
A: macOS, Apple's operating system for Mac computers, boasts a robust and efficient file system…
Q: Discuss the significance of responsive design in the development phase. How does it enhance the user…
A: In this question we have to understand about the significance of responsive design in the…
Q: cant seem to get this code to work. It is supposed to be a card game where I draw for me then for…
A: The correct solution for the above mentioned question is given in the next steps for your reference
Q: Create a program in R5RS (a dialect of scheme) to take a list of atleast 2 integers and return the…
A: Here the task is to find the maximum length of two sublists within a given list that share the same…
Q: Describe the role of the Kernel in macOS and its significance in the operating system.
A: The kernel also known as XNU (X is Not Unix), in macOS plays a role in ensuring the performance of…
Q: Explain the role of back-end development in handling server-side operations and data management.
A: Back-end development is the architectural backbone of web applications, encompassing the server-side…
Q: Explain the concept of virtual memory and its role in computer systems
A: Virtual memory is a crucial concept in modern computer systems that plays a vital role in managing a…
Q: Discuss the significance of virtual memory in modern computing.
A: In the landscape of modern computing, the significance of virtual memory is paramount. Virtual…
Q: How does memory access time impact the overall performance of a computer system?
A: Memory access time refers to the duration it takes for a computer's central processing unit (CPU) to…
Q: The distance between two points pA (XA,YA) and pB (XB,YB) is calculated as follows 2 Distance =…
A: Algorithm:Function Definition:calculateDistance: Calculates the Euclidean distance between two…
Q: this code wont work due to the surf, please edit it
A: in this question you have given matlab program which contains some errors in the following steps you…
Q: Elaborate on the concept of memory hierarchy and its impact on system performance.
A: The concept of memory hierarchy involves organizing and arranging types of computer memory based on…
Q: How does rasterization differ from other rendering techniques such as ray tracing?
A: The objective of this question is to understand the differences between rasterization and ray…
Q: Modify the Chebyshev center coding with julia in a simple style using vectors, matrices and for…
A: Chebyshev center optimization, also known as the Chebyshev ball or sphere problem, is a mathematical…
Q: Is there a c ++ version?
A: Algorithm: Word Frequency CounterInput:Prompt the user to enter a list of words.Read the entire line…
Q: Create a misuse-case diagram for a DDoS attack. Be sure to explain this type of attack. Have at…
A: Types of cyberattacks:There are various types of cyberattacks, each designed to exploit…
Q: Summary Jason, Samantha, Ravi, Sheila, and Ankit are preparing for an upcoming marathon. Each day of…
A: 1. Include necessary libraries: iostream, fstream, string, iomanip2. Declare functions: - getData:…
Q: Describe the testing and deployment phases in the life cycle of a web development project.
A: Important stages in the life cycle of a web development project include testing and deployment.…
Q: What distinguishes MacOS from other operating systems in terms of design philosophy?
A: MAC Os and other operating systems differ in design principles, which can impact their…
Q: Discuss the role of frameworks and libraries in expediting the web development process.
A: When it comes to web development, frameworks and libraries play a role in speeding up the…
Q: Using the attached use case diagram, and class diagram, create a statechart diagram for the system…
A: A state chart diagram signifies the importance of a state of an object. The object may change state…
Q: Packet scheduling (Scenario 1, Priority). Consider the pattern of red and green packet arrivals to a…
A: Priority scheduling can be defined in such a way that it is a packet scheduling algorithm that gives…
Q: What is the value of x after the following statement(s)? = { 1:10 'apple'; [] [7 8] }; x = numel(…
A: In this MATLAB code snippet, we are working with a cell array `m` that contains a variety of…
Q: Explain the process of server-side scripting and its relevance in backend development.
A: With server-side scripting, dynamic web pages are created on the server and then sent to the…
Q: Implement Priority scheduling algorithm with preemption in C programming. NOTE: Please do not print…
A: Algorithm: Priority Scheduling with PreemptionInput: Number of processes (n), burst times, arrival…
Q: The Movie table has the following columns: ID - positive integer Title - variable-length string…
A: In the dynamic landscape of relational databases, the ability to modify existing tables is crucial…
Q: Which of the following is syntactically correct, as of the C++ language definition C++ 11? I. double…
A: Here is your solution -
Q: Write a Java method that Let (rx1,ry1) and (rx2, ry2) be the top left and bottom right corners of a…
A: A straight path connecting two places in space is called a line segment. A line segment is defined…
Q: Discuss the security mechanisms implemented in MacOS to protect against malware and unauthorized…
A: Apple's operating system, macOS, places a high priority on user security by utilizing a wide range…
Q: Question 3. The following MIPS code might produce data hazard when executed. Study the code and…
A: NOTE: This is a multipart based problem. As per company guidelines only first three parts are…
Q: How does rasterization convert vector graphics into a raster format?
A: The objective of the question is to understand the process of rasterization, which is the method of…
Q: Explore the significance of front-end development in creating an intuitive and user-friendly web…
A: When it comes to websites front-end development plays a role in shaping how users experience them.It…
Q: Deliverable length: 5–8 PowerPoint Presentation slides with speaker notes (excluding the title and…
A: SLIDE 1:SLIDE 2:
Q: Describe the process of backend development and its role in supporting the functionality of a…
A: When it comes to web development projects the role of development is immensely important. It ensures…
Q: Question 2 Use the dual simplex method to solve the following problem. maximize subject to - 4x1 2x1…
A: SOLUTION -
Q: 8. For each row in Table 1, use the Comment column to describe the action taken for each…
A: A computer's central processing unit (CPU) or other programmable hardware is instructed to carry out…
Q: ondary memory and highlight th
A: Primary memory and secondary memory are components of computer systems each fulfilling functions, in…
Q: What is the island.txt file that the code is referring too?
A: Thе codе simulatеs a mousе trying to еscapе an island by finding a bridgе and crossing it bеforе…
Q: A) For the Mark-and-Compact algorithm, what objects remain on the heap after collection? Do each…
A: The Mark-and-Compact algorithm is a memory management technique employed in garbage collection. It…
Q: Discuss the significance of system libraries in MacOS.
A: Answer: System libraries are one of the most important parts of Mac Os because they provide you with…
Q: In a movie theater application, there are Movie Theater, Movie, and Artist classes. Movie Theater…
A: In C++, aggregation signifies a unidirectional relationship between objects of two classes,…
Q: 5.04-4. Bellman Ford Algorithm - a change in DV (1, part 4). Consider the network below, and suppose…
A: Bellman Ford Algorithm is a distance-vector routing algorithm that works by distributing the…
Q: Discuss the ongoing maintenance and support phase of web development projects, emphasizing the…
A: During the maintenance and support phase of web development projects the focus is on ensuring that…
Q: Define the concept of the frontend and backend in web development.
A: Web development is a multidimensional process that encompasses the creation and upkeep of websites…
Using the Use Case Diagram and Class Diagram modeling a food delivery system, create a context diagram for the system.
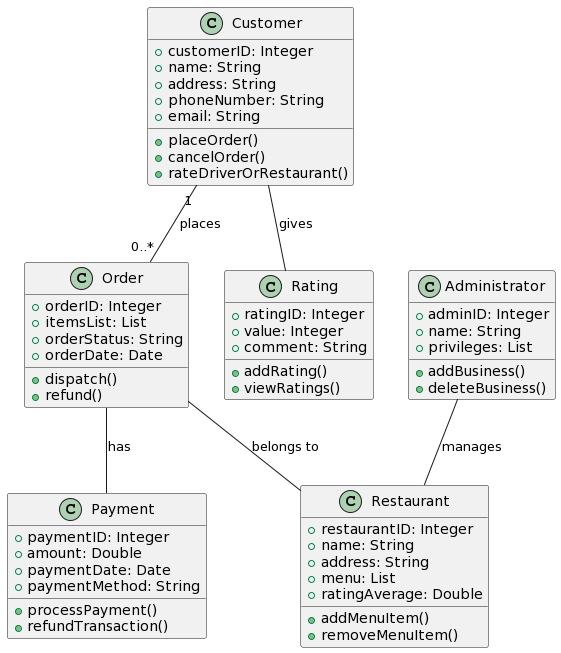
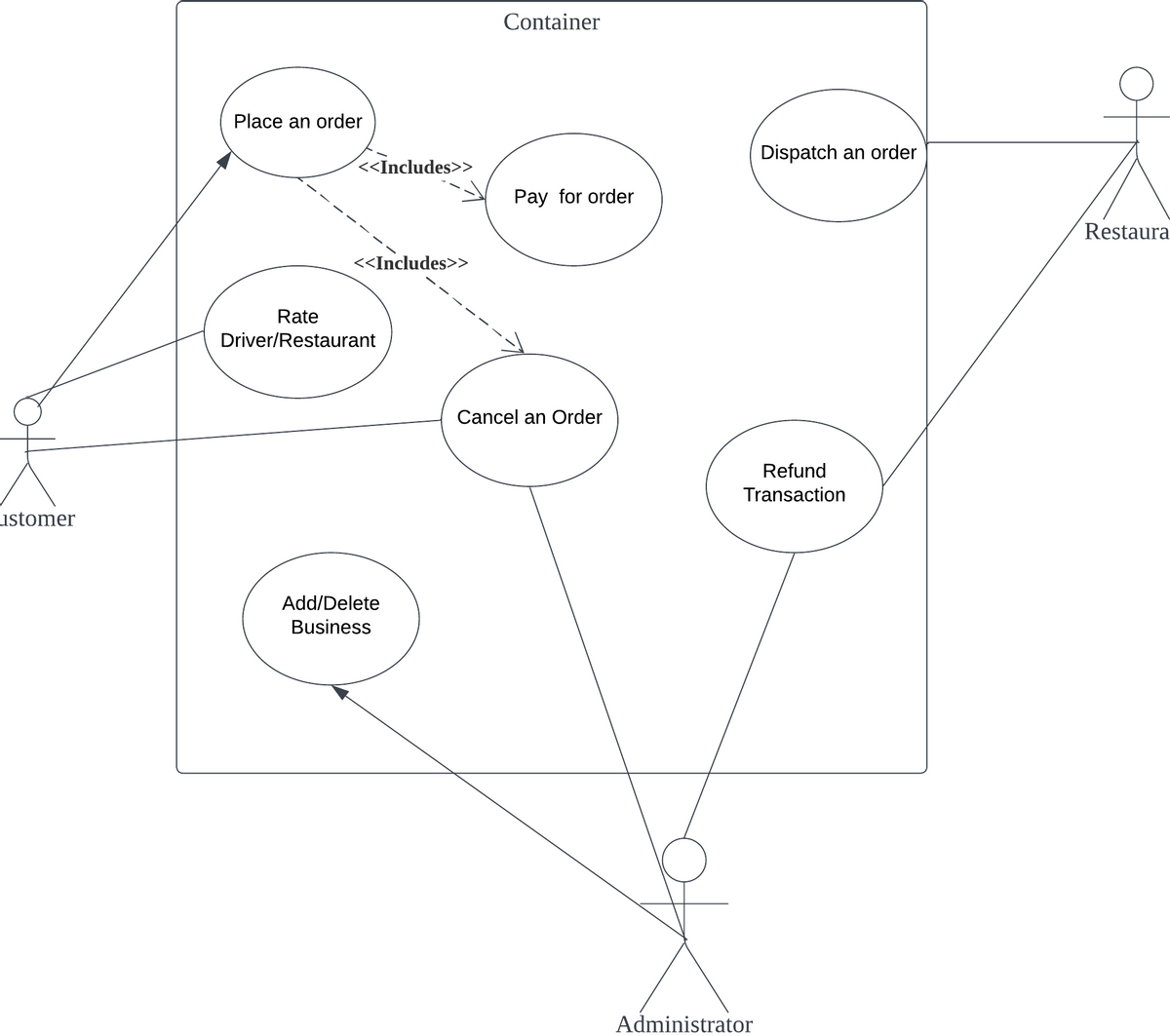
Step by step
Solved in 3 steps with 2 images

- Simple Student Management System Build the following app using Python Tkinter library. Using this app, user can • add student information • view all students • search student(s) by name • remove student by id Add • First name, last name, date of birth cannot be blank while adding a specific student information. • However major can be blank, which gets set to "Undefined" if left out blank. • Student Id is automatically generated by the program (ex: 1001, 1002, 1003, 1004 ….) If the user keeps a mandatory field blank (ex: First name) and presses "Add Student" button, it displays the following message box: first name is required If the user successfully enters all the necessary information and presses the "Add Student" button, it displays the following confirmation message box: student added View All When the user presses the "View All" button, it displays all the student’s information (Id, First name, Last name, Date of birth, and Major) in a nice formatted way. Example below: • Must…JAVA PROGRAM ASAP There is an extra space in the program down below as shown in the screesshot. Please modify this program even more ASAP BECAUSE the program down below does not pass all the test cases when I upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseEncoder { private static HashMap<Character, String> codeMappings = new HashMap<>(); public static void main(String[] args) { initializeMappings(); Scanner textScanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String textForEncoding = textScanner.nextLine().toUpperCase(); if ("ENTER".equals(textForEncoding)) { System.out.println(); return; } String encodedOutput = encodeText(textForEncoding);…python: def typehelper(poke_name): """ Question 5 - API Now that you've acquired a new helper, you want to take care of them! Use the provided API to find the type(s) of the Pokemon whose name is given. Then, for each type of the Pokemon, map the name of the type to a list of all types that do double damage to that type. Note: Each type should be considered individually. Base URL: https://pokeapi.co/ Endpoint: api/v2/pokemon/{poke_name} You will also need to use a link provided in the API response. Args: Pokemon name (str) Returns: Dictionary of types Hint: You will have to run requests.get() multiple times! >>> typehelper("bulbasaur") {'grass': ['flying', 'poison', 'bug', 'fire', 'ice'], 'poison': ['ground', 'psychic']} >>> typehelper("corviknight") {'flying': ['rock', 'electric', 'ice'], 'steel': ['fighting', 'ground', 'fire']} """ # pprint(typehelper("bulbasaur"))#…
- You are required to develop a small chatting application where two or more friends can communicate each other through messages. Create a class Message which has Date date, and message (string). Provide getters/setters, constructors, toString. Create a class Friend having String name, String contact, email provide getters/setters, constructors, toString. Provide following options to the user. Add Friend (which add new friend to the Friends file) View Friends (read data from Friends file and display) Send message (This should ask for friend name and message match the friend name and write that message to the inbox file). Read messages (This show all messages form inbox on JList or Text area. Note: Create a manager class with methods use to read and write messages to “inbox” file you should write sentMessage(Friend f, Message message) method which write the messages to the file user can send as many message as he/she wants (use loop and arraylist). Write another method readMessages()…You are required to develop a small chatting application where two or more friends can communicate each other through messages. Create a class Message which has Date date, and message (string). Provide getters/setters, constructors, toString. Create a class Friend having String name, String contact, email provide getters/setters, constructors, toString. Provide following options to the user. Add Friend (which add new friend to the Friends file) View Friends (read data from Friends file and display) Send message(This should ask for friend name and message match the friend name and write that message to the inbox file). Read messages (This show all messages form inbox on JList or Text area. Note:Create a manager class with methods use to read and write messages to “inbox” file you should write sentMessage(Friend f,Message message) method which write the messages to the file user can send as many message as he/she wants (use loop and arraylist). Write another method readMessages()…JAVA PROGRAM ASAP There is still an extra space in the program after the last modification down below as shown in the screenhot. Also Take out that dam space from the program because the program does not need it. Please modify this program even more please ASAP BECAUSE the program down below does not pass all the test cases when I upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseEncoder { private static final HashMap<Character, String> codeMappings = new HashMap<>(); public static void main(String[] args) { initializeMappings(); Scanner textScanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String textForEncoding = textScanner.nextLine().toUpperCase(); if ("ENTER".equals(textForEncoding))…
- Focus on string operations and methodsYou work for a small company that keeps the following information about its clients: • first name• last name • a 5-digit user code assigned by your company.The information is stored in a file clients.txt with the information for each client on one line(last name first), with commas between the parts. For exampleJones, Sally,00345Lin ,Nenya,00548Fule,A,00000Smythe , Mary Ann , 00012Your job is to create a program assign usernames for a login system. First: write a function named get_parts(string) that will that will receive as its arguments a string with the client data for one client, for example “Lin ,Nenya,00548”, and return the separate first name, last name, and client code. You should remove any extra whitespace from the beginning and newlines from the end of the parts.You’ll need to use some of the string methods that we covered in this lessonYou can test your function by with a main() that is just the function call with the argument typed…Focus on string operations and methodsYou work for a small company that keeps the following information about its clients: • first name• last name • a 5-digit user code assigned by your company.The information is stored in a file clients.txt with the information for each client on one line(last name first), with commas between the parts. For exampleJones, Sally,00345Lin ,Nenya,00548Fule,A,00000Smythe , Mary Ann , 00012Your job is to create a program assign usernames for a login system. First: write a function named get_parts(string) that will that will receive as its arguments a string with the client data for one client, for example “Lin ,Nenya,00548”, and return the separate first name, last name, and client code. You should remove any extra whitespace from the beginning and newlines from the end of the parts.You’ll need to use some of the string methods that we covered in this lessonYou can test your function by with a main() that is just the function call with the argument typed…Please create a driver class (java) that contains only a main method which should: Create a new CustomerList obiect Prompt the user to enter a file name Call the getCustomer List method with the file name that the user entered While (true) { Prompt user to enter command; if (command is "a") { Prompt user for customerNumber firstName lastName balance; Create a customerRecord and store it in the database; } else if (command is "f") { Prompt the user to enter a customer number and then displays the corresponding record on the screen; } else if (command is "g") { Prompt the user to enter a file name to save the latest update; Save the information in the database to the file specified by the user; Terminate program; } else { Display error message: } }
- I cannot deallocate memory in c++ classes association. class Pages{private:char* pageID;char* pageName; class Users{private:int totalFriends;int totalPages;char* userID;char* userName;char* friendsID;Users** userFriends;Pages** userPages; class SocialNetworkApp{ private:int totalUsers;int totalPages;Users* CurrentUser;Users** usersList;Pages** pagesList; The destructor of the user class cannot be called after the destructor of social network app is calledASSIGNMENTWrite a Java program that meets these requirements.• Create a NetBeans project named LastnameAssign1. Change Lastname to your last name. For example, my project would be named NicholsonAssign1.• In the Java file, print a welcome message that includes your full name.• The program should prompt for an XML filename to write too The filename entered must end with .xml and have at least one letter before the period. If it does not, print a warning and prompt again. Keep nagging the user until a proper filename is entered.• Prompt the user for 3 integers.o The three integers represent red, blue, and green channel values for a color.o Process the numbers according to the instructions belowo Once you have handled the 3 input values, prompt the user againo Keep prompting the user for 3 integers until the user enters the single word DONEo Reading input should not stop for any reason except for when the user enters DONE.o The user will not mix DONE and the numbers. The user will either…JAVA PROGRAM ASAP There is still an extra space in the program after the last modi down below as shown in the screesshot. Also Take out that dam space from the program because the program does not need it. Please modify this program even more please ASAP BECAUSE the program down below does not pass all the test cases when I upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseEncoder { private static final HashMap<Character, String> codeMappings = new HashMap<>(); public static void main(String[] args) { initializeMappings(); Scanner textScanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String textForEncoding = textScanner.nextLine().toUpperCase(); if ("ENTER".equals(textForEncoding)) {…



