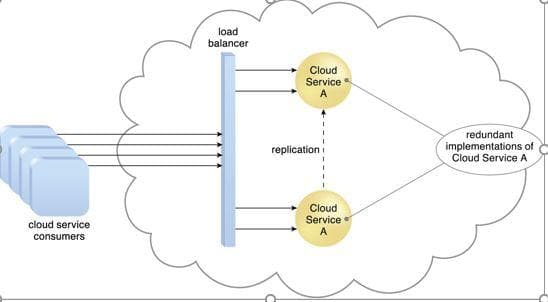
Using this image, explain how you would use this configuration for an email system to a new cloud customer or the executive committee approving the cloud environment
Q: Discuss the purpose of the ICT Development Index (IDI) in relation to the digital divide. What are s...
A: answer is
Q: Code a C program of input an x integer and display is divisible by 3 or not
A: #include <stdio.h> int main(){ int x = 0; printf("Enter an integer: "); scanf("%d", &...
Q: Convert 7654321g to X2. O 111100101100111010001 111110101110011010001 O 111110101100011010001 O 1111...
A: The answers to both questions can be found in the photographs below. The answer to the first questio...
Q: Identify the addressing mode of this assembly language, MOV[BX+SI + 1234H], AL Select the correct re...
A: MOV [BX+SI+1234H], AL In this addressing on base register BX, index register SI and 1234H displacem...
Q: Write in the programming language SWI Prolog the following predicate: The intersection of two sets....
A: Here I am considering the example for simplification to find the intersection ([3,1,9,2] , [7,2,5,1,...
Q: the different binary codes? Briefly describe
A: Lets see the solution.
Q: When it comes to computer communication systems, there are six components. Explain how each of the c...
A: Introduction: It is possible for two or more computers to communicate with each other by exchanging ...
Q: What was changed as a result of the amendment to the Computer Fraud and Abuse Act of 1986, and which...
A: Introduction: Computer Fraud and Abuse Act-1986: The Computer Fraud and Abuse Act (CFAA)—Title 18 U....
Q: ased on One-Time algorithm, if we have used Uppercase, space, ., and ? Now the plaintext “THERE ARE ...
A: The plain text is THERE ARE TWO TYPES OF ENCRYPTION. the cipher text is MLBKMILOQBXMLQEHAVGLHCCSB?G...
Q: how to set up a KMS system in any organization so that employees can utilize it but not rely on it
A: The Knowledge Management System (KMS) is a corporate knowledge repository that helps employees do th...
Q: The size of a full-featured modern Operating System, and the difficulty of the problem it addresses,...
A: Here is the answer with an explanation:-
Q: To utilise computers at college, do you need to develop a set of remote access policies?
A: Introduction: A document that discusses and specifies permitted ways of remotely connecting to the i...
Q: Write a program that prints an nxn multiplication table, given a positive integer n. Input Each test...
A: Python Program: # Taking the number n as user inputn = int(input("Enter the number n: ")) # Display ...
Q: Mention the deployment model of big data
A: The big data is larger, more complex data sets, especially from new data sources.
Q: What must the attacker perform in order for a sniffer attack to be successful? Is it possible for an...
A: Intercept or record data sent across a network by using a Snooping or Sniffing attack. Network issue...
Q: Using Codeblock. Make a program that asks the user to enter the marks of a student in a subject. If ...
A: I have provided C CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT-------
Q: 3. More Boolean a) 10111100 OR 11100011= b) 11110010 AND 00110011= c) Implement xy+x'y'+y'z with NAN...
A: Please upvote me/like me. Please. Please. I am providing you the correct answer below. Here I am...
Q: Consider the relation R (AA, Bb, Cb, Yy, Ee, Ff, Gg, Hh, Jj, Kk) for Naim Furniture Company with the...
A: Answer:- (C) FD3: Partial Dependency.
Q: Expalin with an illustration What is the necessity for software engineering? Given its significance ...
A: Introduction: Developing, designing, implementing, maintaining, and retiring software are all part o...
Q: What exactly is a Device Controller?
A: Introduction Under the context of computing, a controller is a small hardware device or a software ...
Q: The price of a certain combo meal at different franchises of a national fast food company varies fro...
A: fast food company varies from $5.00 to $17.38 Standard deviation of $2.13. A sample of 29 students ...
Q: Check if there is a path in an 8x8 matrix starting in the upper left corner, and ending in the lower...
A: // A C++ program to count all possible paths// from top left to bottom right
Q: Explain CAN message format? Explain the Hardware setup / connections using the CAN interface? Able t...
A: Q1). Data Frame, Remote Frame, Error Frame, and Overload Frame are the four types of CAN messages, o...
Q: Write the Java statement for the following. Declare an array of String named jleague with values “C...
A: Your java program is given below as you required with an output.
Q: Define the term multicore microprocessor.
A: Introduction: Define the term multicore microprocessor.
Q: 1. What are the different number system? Briefly discuss each.
A: The solution for the above given question is given below:
Q: The specifications of a GPON network of 20 km single mode fibre (SMF) with three connectors and a 1:...
A: Below is the answer to above question. I hope this will meet your requirements....
Q: What exactly do you mean by static data member and static memberfunction?
A: In the C and C++ programming languages, the keyword static is used. Inside and outside of the class,...
Q: Draw the Enhanced Entity–Relationship (EER) model and the relational schema for the case study below...
A: Answer: There are total 6 Entities which are: Entities: branch, supervisor, staff, member, rent, vid...
Q: CODE USING C++ 2. A, e, i, o, u? by CodeChum Admin We've had enough about numbers, so why don’t we...
A: Code :- #include <iostream>using namespace std; int main(){ char character; char str[5]; ...
Q: What are routing metrics, and how can they be utilised effectively?
A: Introduction: Routing is the process of selecting a path for traffic within a network or between or ...
Q: Consider the possibility that there is a database system that is impenetrable. Is it necessary to ha...
A: In the case of a failure, a database's proper (consistent) state must be restored, Restoring a datab...
Q: Is there a reason to use plain text protocols in the 21st century?
A: Lets see the solution.
Q: Which entities in 5G cellular can request a retransmission of received information? Explain the rati...
A: 5G cellular: The fifth generation of cell towers, or 5G, is predicted to be one of the most advanced...
Q: ead the text from the file and put it into parallel arrays in c++ For example lest assume fo
A: To be able to work with the file, fstream, and vector header files are used. Every word of the file ...
Q: Activities: I. Write the proper method declaration/ method call for the following (Java Programming)...
A: Answers: 1. public static void CS(){ // statement } 2. CS(); 3. public static int IT(){//statement r...
Q: parent process. o ie. no grandchildren o Your process must clearly display that each forked process ...
A: Answer is in given below.
Q: What are the steps in solving basic mathematical operations on different number system?
A:
Q: Consider a rectangle with perimeter 28 (units) Let the width of the rectangle be w (units) and ler t...
A: Actually, given information regarding perimeter 28(units).
Q: List the eight most important design principles for user interfaces. How would you rank them in term...
A: Eight fundamental rules for user interface design, ranked in order of importance.
Q: ysis and de
A: given - Establish a clear understanding of systems analysis and design, as well as the function of a...
Q: We need to write a C program that generates sorne statistics about salaries of employees. First, the...
A: ALGORITHM:- 1. Take input from the user about the number of employees. 2. Take input for the salarie...
Q: d. Distinguish between the following pairs of Big O notations and give practical examples to illustr...
A: Time complexities are measured using the Big O notation.
Q: If we use direct RGB value coding with 10 bits per primary colour, how many potential colours do we ...
A: Introduction: Each pixel's color options The RGB picture is in 8-bit form, which implies there are t...
Q: Write a program that computes the GCD of two positive numbers a and b. The program should handle non...
A: The python code has the following steps: First two numbers a and b are inputted and then both are c...
Q: editable source code: instructions are on the photo #include int main(void) { int a, b, c, d; ...
A: C Program: #include<stdio.h> /* Function getBest() of return type int with 4 parameters and re...
Q: is the difference between worms and viruses? Do Trojan horses take viruses or worms with them when t...
A: Types of Malware VirusesThey are malicious executable codes that are attached to another executable...
Q: IoT and WSN involve devices that ca be connected to the Internet true or false
A:
Q: Add a JTextField and a JTextArea to the frame. Initialize the field to an empty string and the text ...
A: Add a JTextField and a JTextArea to the frame. Initialize the field to an empty string and the text ...
Q: This question is on heapsort. (a) We aim to construct a max heap based on an array A. When we call h...
A: maxHeapify(array, size, k) set k as largest leftChild = 2k + 1 rightChild = 2k + 2 if lef...
Step by step
Solved in 2 steps

- Reuse of an existing Enterprise application that is developed in programming language other than java such as php. And develop an Enterprise application that include the web application• Client side Jsf or jsp , sevlet,css, image etc..),o Build the front-end interface for the homepage including login and registration formo Note : You can add any Client side script language/script/technology• Server side – communicate with client and database• Database that stores data in a persistent manner, and it must communicatewith your server.o Entity-JPA or DAOo JavaDB/MySQL/Oracle or other suitable relational database• EJB, shared libraryIdentify Testing Types c. While doing Beta testing, a customer noticed a hectic delay in the page loading ofan application. He was so frustrated and went to the feedback page of thecompany site and complained about the lazy loading issue. Garreth, a supportspecialist of the company, looked into the incoming issue he received from thecustomer who wrote about the page loading issue. Garreth logged into the defecttracking tool and started writing details about the new issue reported by thecustomer and it has a field to enter the type of issue. So, help Garreth identifytesting types.Simple algorithem please explain everystep thank you!
- NEED THIS DONE IN ANDROID STUDIO (JAVA AND SQLITE PLEASE) Create a waiting list management app for the computer science department administrator, K. Johns. Mrs. Johns prefers to use paperless tool to keep track of the course registration waiting list/s. Your app should allow Mrs. Johns to:........ add a new student on the waiting list for a certain course. assign a priority (graduate, 4th year, 3rd year..). remove student from the list. edit student information.User support is offered at the session, presentation, and programme levels. How?Subject/Course: Computer ScienceTitle: Java Application Question: Specifications: Users: Seller should be able to add/edit/delete different products should be able to view all the sales/users who bought the products Buyer should be able to view/search all available products should be able to add to cart should be able to buy products The application should also have a login page where the user can sign-in or sign-up for an account. Additional feature Upon registration of any user they will be sent a verification email. The email contains the verification code where the user can input in the registration page to verify his/her account. The email also contains a link which the user can use to automatically verify his/her account. A user with an unverified account should not be able to login.
- Project detail:Design the layout of users, domains, trusted domains, anonymoususers, etc for a start-up open source software company ABC. Theyshould have an internal CVS server, which only internal developerscan access, an anonymous CVS server for outsiders to downloadsource code, WWW servers (one for internal and one for external),and a mail server. Outsiders should not be able to access eitherinternal CVS or internal WWW servers. You should finish the following parts:a) The topology diagram for the different servers and locations andtrust domains. For example, where are the firewalls, and whereare the users located in the topology.b) The assumptions that you make for your design and the securitypolicy to achieve this assumption. Project Part 2Your final document should include the following parts:1. Network topology diagram and the domains of trust.2. Security related assumptions in your design, and security policy tomake this assumption valid.3. Trust assumptions about users (e.g.,…Project detail:Design the layout of users, domains, trusted domains, anonymoususers, etc for a start-up open source software company ABC. Theyshould have an internal CVS server, which only internal developerscan access, an anonymous CVS server for outsiders to downloadsource code, WWW servers (one for internal and one for external),and a mail server. Outsiders should not be able to access eitherinternal CVS or internal WWW servers..You should finish the following parts:a) The topology diagram for the different servers and locations andtrust domains. For example, where are the firewalls, and whereare the users located in the topology.b) The assumptions that you make for your design and the securitypolicy to achieve this assumption.Project Part 2Your final document should include the following parts:1. Network topology diagram and the domains of trust.2. Security related assumptions in your design, and security policy tomake this assumption valid.3. Trust assumptions about users (e.g.,…“Online Doctor Search and Appointment System “ is a smart appointment booking system that provides patients or any user an easy way of searching a doctor as per doctor’s specialization and booking a doctor’s appointment online. This project also provides a platform for doctors to create their profile so that a user or patient can search them and book an appointment. This is a web based application that overcomes the issue of managing and booking appointments according to user’s choice or demands. The task sometimes becomes very tedious for the doctor himself / herself in manually allotting appointments for the users as per their availability. Hence this project offers an effective solution where users can select a doctor and view various booking slots available and select the preferred date and time for the selected doctor. The already booked space will be marked yellow and will not be available for anyone else for the specified time. This system also allows users to cancel their…
- “Online Doctor Search and Appointment System “ is a smart appointment booking system that provides patients or any user an easy way of searching a doctor as per doctor’s specialization and booking a doctor’s appointment online. This project also provides a platform for doctors to create their profile so that a user or patient can search them and book an appointment. This is a web based application that overcomes the issue of managing and booking appointments according to user’s choice or demands. The task sometimes becomes very tedious for the doctor himself / herself in manually allotting appointments for the users as per their availability. Hence this project offers an effective solution where users can select a doctor and view various booking slots available and select the preferred date and time for the selected doctor. The already booked space will be marked yellow and will not be available for anyone else for the specified time. This system also allows users to cancel their…# Lab 2 ## Scenario Code&Code is a small company dedicated to Software Development. Their engineering team, to which you belong, is working on writing a Web Application as an MVP for a new customer. The code name for this App is “Loggy”, which is meant to offer functionality for a personal journal where users can log their daily activities through text, voice and video. The first step will be to write the main functionality, which is essentially a Microblogging System where all the posts are automatically annotated with voice, video or text. As an initial step, you must create the skeleton of the back-end service for performing the automatic closed captioning under these assumptions: - The closed captioning is performed through an external service (AWS or GCloud). - There should be an internal controller that: - Receives the recordings to be processed from a requester - Sends the recordings to the external service - Receives its response - Updates the recoding with the resulting…Create a Vaccination System using Php that has the following features:1. Add client record(such as firstname, lastname, middlename, category, address, date of first dose, date of second dose) The codes you given don't display anything Thank You



