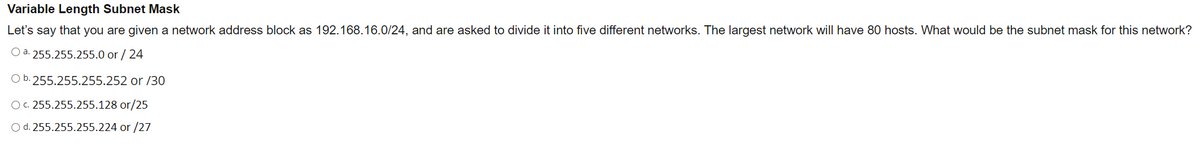
Ob.255.255.255.252 or/30
Q: Why do we utilize MATLAB to tackle issues in computational geometry?
A: The advantages of MATLAB are: For starters, and maybe most importantly, MATLAB is quite intuitive.…
Q: Write (in pseudocode) an implementation of virtual clocks, including the queuing and management of…
A: Pseudocode Pseudocode is a made-up, informal language which programmers use to create algorithms. A…
Q: Microsoft and Sun have engaged in a number of public disagreements about the design of Microsoft's…
A: Delegates are a brand-new language feature Microsoft: Visual J++ 6.0. In other languages, such as…
Q: Is it safe to use the SSTF disc scheduling method, and if not, why not?
A: SSTF disc scheduling algorithm: Shortest Seek Time First (SSFT) determines how data is read from the…
Q: distinguishes more advanced computers from other sorts of computers?
A: Flynn's taxonomy expanded and distinguishes more advanced computers from other sorts of computers…
Q: When explaining the software structure review process, could you provide some concrete examples of…
A: When explaining the software structure review process, could you provide some concrete examples of…
Q: Create an application that contains an enumeration (enum) that represents the days of the week.…
A: Program Plan: Define an enum Days with the days of the week. For each day, assign an integer value…
Q: In the context of software engineering, how are the concepts of cohesion and coupling related to one…
A: The answer of this question is as follows:
Q: This variable defines the number of instructions necessary to execute each statement at the source…
A: Machine code Machine code is written in the language of the machine. Consequently, a machine, that…
Q: List all cases when inline functions have the opposite effect.
A: Inline function is the optimization technique used by the compilers.
Q: Is it possible that linking offline and online with intelligent technology might compromise privacy?
A: Introduction: Next, the tone of the following part is very different from what was said above about…
Q: The five risk-reduction measures should be outlined concisely and succinctly.
A: Risk is the likelihood that something will go awry due to an occurrence or a chain of events. Five…
Q: In what sequence would you recommend carrying out the steps of the ABC system?
A: Sequential quadratic: Programming (SQ) is a class of methods used to solve non-linear optimisation…
Q: Detail the software structure review method using examples.
A: the answer of the question is given below
Q: C programming task Analyse pgmEcho.c to identify how it should be improved, then rewrite it so that…
A: Explanation : - Include the necessary header files. - Then pass the argument vector in the main…
Q: What happens if the CPU has forwarding but the hazard detecting unit has not been developed?
A: Definition: Operand forwarding, also known as data forwarding, is a pipelined CPU optimization that…
Q: The lack of spare storage capacity is the primary distinction between embedded and general-purpose…
A: the answer of the question is given below
Q: 1: get_nodes_in_range Test non-empty BST Your output Test feedback 8 10 12 15 20 60 80 100 Test…
A: I understand your problem. You just need to change the Python compiler. Because, some of the online…
Q: To what extent does the idea of portability apply to the various programming languages?
A: In various programming languages, the idea of probability is used for various models and interfaces.…
Q: See what categories of books are available now. Only one item per category is appropriate.
A: The Answer is in step-2.
Q: Why was the RISC architecture first proposed?
A: Given: The RISC architecture, which stands for Reduced Instruction Amount Architecture, is a…
Q: Design and implement a Version-Queue data structure. A Version-Queue maintains a version number…
A: Let's understand step by step : 1. Because every version of the queue should be maintained so each…
Q: What aspects of information system architecture contribute to scope creep?
A: The scope-creep is the continuous growth or change in the scope of a particular project beyond its…
Q: There is some uncertainty as to whether or not the rise of sentient robots with the ability to make…
A: Introduction: Due to the following workplace risks related with robotics, the emergence of…
Q: Microsoft Excel provides some alternatives to consider. Provide an explanation of how the following…
A: Please refer below for your reference: I am answering the explanation of excel functions asked by…
Q: If Al has inherent prejudice, how can we fix it? What methods exist for making Al less prejudiced?
A: bias in AI Artificial intelligence bias (AI bias) is an abnormality in the results of machine…
Q: How do science and technology effect our lives? How can we defend hum rights with cutting-edge…
A: Here in this question we have asked that how do science and technology effect our lives .how can we…
Q: Specify what you mean by "unit-by-unit testing," and provide an example
A: "An application's most minor testable components, known as units, are separately and independently…
Q: When it comes to creating software, how closely related are the concepts of cohesion and coupling?
A: Coupling: The coupling among the modules depends on the complexity of the interface, from where the…
Q: Differentiate between divide-and-conquer and dynamic programming and explain how each works.
A: Given: A set of instructions that instructs the computer on how to carry out specific activities is…
Q: What happens if the CPU has forwarding but the hazard detecting unit has not been developed?
A: ANS: - Because the hazard detection unit must insert a one-cycle stall whenever a value is supplied…
Q: Explain the process of reviewing the program structure in detail and back up your claims with…
A: Throughout the early phases of the Software Development Life Cycle, Software Review is a systematic…
Q: What will be the output if the given C code is compiled on a php compiler? #include int main() { }…
A: Find the output if the given C code is compiled on a php compiler. About the given code: In the…
Q: For what reason do so many embedded systems need watchdog timers?
A: The watchdog timer is used for the protection of the device.
Q: What does "reduced" imply when referring to a computer with a constrained set of instructions?
A: A computer with a central processing unit (CPU) that follows to the processor design idea of…
Q: Jessica is pondering establishing a new programming language. The programming language makes…
A: Specifications and their interpretation The design objectives are as follows: The language will be…
Q: With the convergence of physical and digital worlds and intelligent technologies, will we have a…
A: Are we on the verge of experiencing a problem with personal privacy as the real and digital worlds…
Q: What justifies making a process exception?
A: The operating system has a procedure called process scheduling, which is used to schedule different…
Q: Specify what you mean by "unit-by-unit testing," and provide an example
A: Introduction: Unit Testing: Unit testing is a software development process in which the smallest…
Q: Robots may be programmed to do tasks that humans may find harmful, offensive, or tedious. I'd want…
A: Please find the answer below :
Q: To what extent does the idea of portability apply to the various programming languages?
A: Portability is the feature in the programming languages that enables an application to execute in a…
Q: Describe the technologies and techniques used to define project management in the IT industry.
A: Every business domain places a significant level of responsibility on project management. It's…
Q: What ethical and social impacts do robots and Al have? Would making all jobs robot-friendly make our…
A: The promise of social robotics is that, in the near future, we will be able to have a lasting…
Q: Question Someone must be assigned to handle escalated calls each day. What are the first 3 dates in…
A: First find all date to the assigned. 1. To George: All Wednesday & all weekends. So, the dates…
Q: To what extent does SIMD benefit from data or control parallelism? Where does MIMD shine in terms of…
A: Program-level parallelism refers to the practice of distributing a single program such that it may…
Q: It doesn't seem as if ICMPv6 Neighbor Solicitations are transmitted as a broadcast.
A: Introduction: ICMPv6: The Internet Control Message Protocol Version 6 (ICMPv6) is a new version of…
Q: What are the four pillars around which extreme programming is built?
A: Extreme programming which refers to the programming languages it is the software development…
Q: List all cases when inline functions have the opposite effect.
A: The inline keyword does not issue a command but rather only a request to the compiler. The compiler…
Q: Prim's MST uses a weighted network.
A: Prim's algorithm find the minimum spanning tree. A minimum spanning tree contains all the vertices…
Q: But what exactly is it about virtual memory that makes its implementation in embedded systems so…
A: Virtual memory regulates and supervises of virtual address spaces and transforms virtual addresses…
Step by step
Solved in 2 steps

- An IP address can be written as a 32-bit number. For a class B network, the two most significant bits are set to 10. The 16 most significant bits are used as a network ID, and the 16 least significant bits are used as a host ID. However, the host ID cannot be all 0's or all 1's. How many hosts (i.e., host IDs) can there be on a class B network?An IP address can be written as a 32-bit number. For a class B network, the two most significant bits are set to 10. The 16 most signi cant bits are used as a network ID, and the 16 least signi cant bits are used as a host ID. However, the host ID cannot be all 0's or all 1's. How many hosts (i.e., host IDs) can there be on a class B network?A network configuration of a modem is given as following:LTE interface IP = 77.110.156.22 MASK 255.255.252.0Default GATEWAY = 77.110.156.1Masquerade NAT, and DNS address = 1.1.1.1Local IP setup: 192.168.128.1 MASK 255.255.255.0And, ip route 192.168.128.0 255.255.252.0 192.168.128.254 Devices numbered R1, R2, R4, R5 are routers. PC is a computer.Image of network with interface names such as f1/0 are added. You must use only static IP addreses and static IP routes to configure the network and make PC able to connect (ping) to Modem.
- Consider the following non-default subnet masks: (a) 255.255.248.0, (b) 255.128.0.0 . To which IP address class do they pertain?Write down the following in CIDR notation: (a) IP: 150.160.170.180, Subnet Mask:255.255.224.0; (b) IP: 75.80.85.90, Subnet Mask: 255.252.0.0 Three stations A, B, C and D are connected to a common Ethernet hub. Their IPaddresses and subnet mask are respectively: 200.100.50.67, 255.255.255.252;200.100.50.7, 255.255.255.248; 200.100.50.138, 255.255.255.240 and 200.100.50.1,255.255.255.254. Determine which among these stations can communicate with eachother. You need to show all detailed workings.Computer Science In Python, I am trying to make a client and server code that passes the payload with the requirements. The client has to specify the length of the data packet, up to max, specify how many times to pass the data packet, and specify the server IPv4 address. Both the client and the server need timer functions and compute the time needed to perform the number of sends both the Client and the server need to display the local and remote IPv4 addresses, total time, and bytes per second. Please help, Thanks.. Assume: Your laptop's Ethernet address is 0a:0b:0c:0d:0e:0f, DHCP server address is 131.111.7.3, your IPv4 address will be 131.111.7.121, the gateway's IP address is 131.111.7.1, and Ethernet address is 00:01:02:03:04:05, the network subnet mask is 255.255.255.0.Write the series of protocol/packet exchanges that occur on the wired Ethernet link, up until you can send a single packet to 128.232.0.20. You do not need to describe packets after this packet has left the link. Include ARP and DHCP
- For example, let say that your Network 1 needs 30 hosts and you are in a class C network, you would start with 192.168.0.1 till 192.168.0.32 because the closest you can get to 30 that is more is 32 (2exp5) so my begin address would be 192.168.0.1, end address would be 192.168.0.32 (not 192.168.0.30 because we only need 30 hosts) and subnet mask would be 255.255.255.224. The next range will start at 192.168.0.33!!! Use the example to answer: We are going to use the private range for a class A network. What is its standard subnet mask? A) Network 1 needs 250 hosts B) Network 2 needs 230 hostsUsing packet tracer, implement a network that has the following components: 1- At least five routers 2- At least 7 subnets 3- At least 12 PCs 4- At least 4 switches 5- Use RIP routing protocol To assign IP addresses of the routers and PCs, use the IP address from your ID as follows Assume your id is 118zyxw, Consider the numbers z, y, x and w as deciemal You have the subnet 118.0.0.0/24 If your ID is 1181234 then the IP is 118.0.0.0/24 Use this subnet to get at least 7 subnets.Choose a set of class C, /24 addresses that could be successfully combined into a supernet that supports 3000 hosts.
- Berkeley Computer Science example (CS-168): Picture this: there are two hosts (A and B). The two hosts are connected by 50 msec of propagation delay. The bandwidth is equal to 106 B/sec. Note that the hosts use a sliding window where (W = 4, and packet size = 1000 Bytes) with (Selective Repeat). We will ignore the size of ACK and assume that the timer value for each packet is set as (send time + RTT) and retransmission occurs immediately after a timer expires. Make sure to assume that the packets are sent in sequence starting at time 0. How long does it take to successfully receive all 4 packets (P_0, P_1, P_2, P_3). Your answer should be in milliseconds. 1. When there is no packet loss. 2. When the P_1 packet becomes lost, but there is no further packet lossGiven a Class C subnet Mask 255.255.255.192. what will be the subnet address and host number for a machine with IP address 197.1.2.67. Select one: a. second subnet and host 2 b. Third subnet and host number 3 c. second subnet and host 4 d. First subnet and host number 3 e. None f. Second subnet and host number 3Write aprogram to find the ip dotted decimal notation conversion from decimal to binary,octal and hexadecimal and vice versa also find the result of NOT and AND operation of ipv4 adresses. a. 114.34.2.8 Find the result of each operation: a. NOT (22.14.70.34) Find the result of each operation: a. (22.14.70.34) AND (255.255.0.0) ALso develop a program to find classes of ip adress and first and last address,subnet mask also. Develop in java



