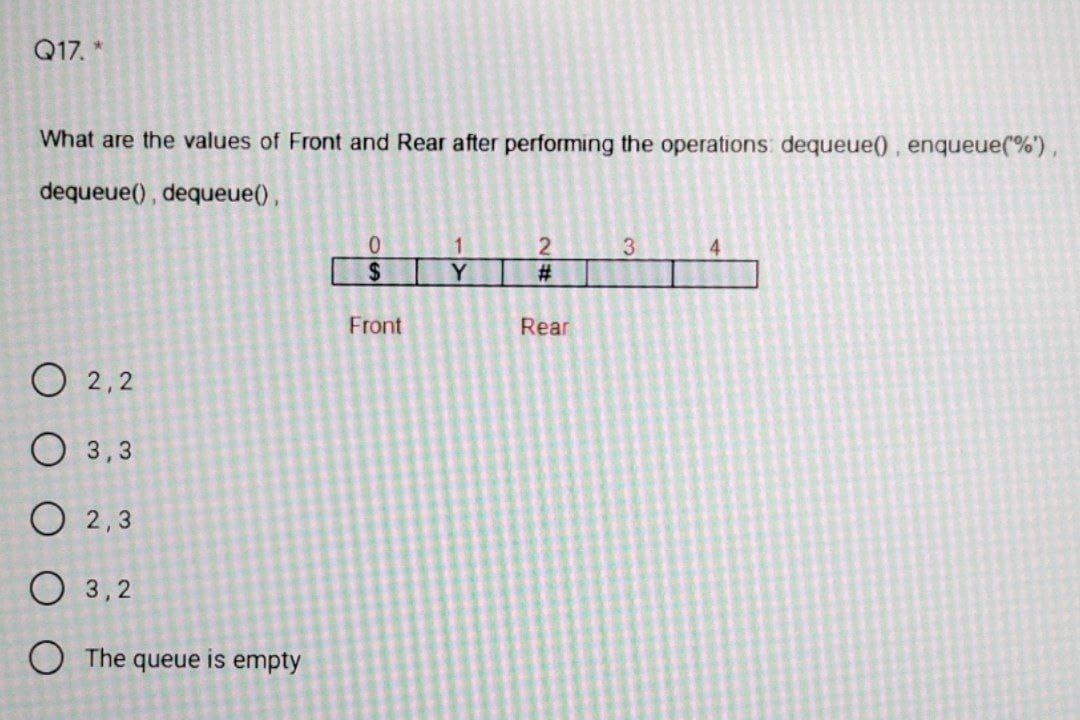
Vhat are the values of Front and Rear after performing the operations: dequeue(), enqueue(%') lequeue(), dequeue(), 3 4. %24 Y 2#: Front Rear D 2,2 O3,3 D 2,3 D3,2 The queue is empty
Q: Are there any products or services that IPSec offers?
A: IPsec is a group of technologies that work together to provide encrypted communications between…
Q: Discuss briefly the system development life cycle (SDLC) and the various methods to SDLC in a…
A: SDLC stands for Software Development Life Cycle: It is a method that the software industry uses to…
Q: What is the time complexity for the given recurrence relation: 2 T(n/2) + ca > 1 cb…
A: Please refer below for your reference: I have applied both the methods masters theorem and…
Q: Python Create a program in python whereas: Given a list ot X objects, u want to perform:…
A: I give the code in Python along with the output and code screenshot
Q: From the greatest to the tiniest component, describe the AWS Global Infrastructure.
A: Global Infrastructure on AWS: AWS is a globally accessible cloud computing platform. AWS is located…
Q: Assume you want to keep an attacker from detecting a hash function collision. The attacker has…
A: Introduction: Consider the case where you wish to prevent an opponent from detecting a hash function…
Q: Comment on how pipelining can make computers faster, how pipeline dangers can be mitigated, and how…
A: Computer pipelining: The process of gathering instructions from the processor via a pipeline is…
Q: Is it possible to explain what an operating system is?
A: An operating system is a piece of software that acts as a bridge between the end-user and the…
Q: What is the most important goal of normalization? What part do determinants play in the process of…
A: Normalization: The technique of efficiently structuring data in a database is known as…
Q: Consider the declaration int "ptr; what is difference between ptr and "ptr??
A: According to the question the *ptr contain the pointer of address with the help of the asterisk key…
Q: How do professional codes address issues from the viewpoint of computing profession?
A: Computing professionals' actions change the world. To act responsibly, they should reflect upon the…
Q: Write a Java program that calls a method from main and passes it two integer parameters called…
A: The answer to the following question:-
Q: In this c language program. Please fixed the date and show the output of the program. Source Code:…
A: Please refer below code and output: Below is the corrected code I have made changes on line 18 and…
Q: What are the advantages and disadvantages of various authentication procedures in terms of security?
A: Start: Users are commonly recognized by a user ID, and authentication occurs when the user offers a…
Q: Q19. * The Preorder Traversal of the following Binary Search Tree is: 8. 3 (10) 1 6. (14) 4 7) (13 O…
A: INTRODUCTION: Algorithm Preorder(tree): Visit the root. Traverse the subtree on the left. Traverse…
Q: Computer Science Show that every infinite Turing-recognizable set ?? contains an infinite decidable…
A: Let L be an infinite Turing recognizable language. We know that “A language is Turing…
Q: A conditional test in a flow chart or pseudocode may cause results to differ. Why is this so?
A: INTRODUCTION: Here we need to tell a conditional test is a flow chart or pseudocode that may cause…
Q: Discuss CSMA/CA/CD. Describe each one's function and intended network. Describing the benefits and…
A: CSMA -(Carrier Sense Multiple Access) is a method of managing communication when more than one user…
Q: Students can use four distinct alternatives or procedures to transfer files from school DVDs to…
A: Various methods for transferring data from DVDs to a laptop include the following: -
Q: Explain why creating functions is important in programming.
A: Function : Functions are one of the basic building blocks of programming; they consist of statements…
Q: Create a structure that consist of four fields, {array, max, min, sum} File in these fields with: o…
A: Start create structure and assign fields with values. Find maxValue and assign its index to max Find…
Q: What is the most important goal of normalization? What part do determinants play in the process of…
A: Introduction: Normalization is a significant in information base administration. It is an…
Q: The objective of Electronic Data Interchange in a fictional supply chain. Three instances of…
A: The Electronic Data Exchange or EDI is an innovation that assists exchanging associations and…
Q: If you needed to send data from a remote client to a server quickly, would you choose UDP or TCP?…
A: If you needed to send data from a remote client to a server quickly, would you choose UDP or TCP?…
Q: Why would a 100OOMB CAT6E cable be a terrible choice for a 328-foot length pull for high data…
A: Introduction: The speed is not slowed by using an ethernet wire. The cable's maximum length is 328…
Q: From the greatest to the tiniest component, describe the AWS Global Infrastructure.
A: Global Infrastructure on AWS AWS is a globally accessible cloud computing platform. AWS is located…
Q: What exactly is information privacy? Describe five different ways to keep your personal information…
A: answer is
Q: From the greatest to the tiniest component, describe the AWS Global Infrastructure.
A: Global Infrastructure AWS AWS is a global cloud computing platform. Global infrastructure is a term…
Q: The three stages that are employed in the physical design stage should be identified and described…
A: The three stages that are employed in the physical design stage should be identified and described…
Q: It has been attached to your new MacBook Pro with a storage device that the operating system does…
A: The Answer is in step-2.
Q: Explain three scenarios in which a surrogate key for a relation's primary key should be generated.
A: Introduction Explain three scenarios in which a surrogate key for a relation's primary key should be…
Q: A motorcy tion. The PASCAL km
A: Ac. to given: Let us take 3 variables, m for milage= 48 c for cost of petrol per liter= 20.30 d for…
Q: There is no Level 1 DFD for the activity Approving Supplier Invoices. If you were to draw one, what…
A: Data-flow diagrams (DFDs) represent a view of the system that is most easily understood by users:…
Q: 1. Who does the data visualization? 2. What are the tools for the data visualization? 3. What…
A: Data visualization is the representation of data through use of common graphics, such as plots,…
Q: What are the three different kinds of backups that may be used to restore a database? Define each…
A: Your answer is given below in detail. Introduction :- Database is a used to store the data.…
Q: Premier University's admissions process is well-known to you. Students can access the enrollment…
A: 1. Introduction -The student admission is one of the most important activities within a university…
Q: 7- Reduce the function specified in the truth table in figure below to its minimum SOP form by using…
A: Below is the answer to above query. I hope this will be helpful for you..
Q: In what ways does troubleshooting make security breaches and data loss more likely?
A: Security breach: Any incident that leads in unauthorized access to computer data, applications,…
Q: Converting an offline firm to an internet business (in any industry or area). You must plan…
A: Thus, a systems methodology is primarily a process that incorporates system-scientific approaches,…
Q: Determine three unique smartphone applications that would be extremely useful in your present or…
A: Numerous smartphone apps are available nowadays that help you be more productive at work. You can do…
Q: The objective of Electronic Data Interchange in a fictional supply chain. Three instances of…
A: Interchange of Electronic Data The goal of EDI is to guarantee that business papers are sent between…
Q: What if VoIP suffers from the same challenges with the firewall that streaming audio does?
A: Answer : VoIP is a Stream of Video or Audio. Having a Firewall implies you need to design what's…
Q: What exactly is a restartable instruction?
A: Institution: LDM, STM, PUSH, POP, and, in 32-cycle a multiplier implementations, MULS are…
Q: Why would a 1000MB CAT6E cable be a terrible choice for a 32 for high data throughput? What would be…
A: Cat6e is a shortened form for "cat6 upgrade." Cat6e link has the property of accomplishing 600 MHz…
Q: When using public key cryptography, what is the bare minimum number of keys required?
A: Public key Cryptography: A public key and a private key (a public key pair) are used in public-key…
Q: import __________________; public class Exercise1 { _________________________ main(String[]…
A: import __________________; public class Exercise1 { _________________________ main(String[] args)…
Q: What are the most important things to keep in mind while creating a physical database?
A: The most important things to keep in mind while creating a physical database are discussed below:
Q: What procedures, in your opinion, are required to guarantee the security of data in transit and at…
A: Statement: Protecting networks from malware assaults while data is being transferred is made…
Q: sin 2ax 5. Given ſ cos?(ax)dx = x . Calculate the following definite integral f, cos2 (0.5x)dx. со…
A: We can use the integral Matlab function. The function parameters are the function handle, lower…
Q: What distinguishes malware from a viral program?
A: Malware is a word that refers to malicious software that is created with the intent of causing harm…
Step by step
Solved in 2 steps with 1 images

- Java adt Draw the contents of the queue after the following statements execute. Clearly label the front and back of the queue. QueueInterface bankLine = new LinkedQueue<>(); bankLine .enqueue("John"); bankLine .enqueue("Matthew"); String next = bankLine .dequeue(); next = bankLine .dequeue(); bankLine .enqueue("Drew"); bankLine .enqueue("Heather"); next = bankLine .dequeue(); bankLine .enqueue("David"); next = bankLine .dequeue();A number means to push and a dash means pop in the following sequence. Give the sequence of values returned by the pop operations when this sequence of operations is performed on an initially empty queue. 1 4 5 - - 6 7 8 - - - 2 6 - 12 10 - - -Using python 1. Create a stack class using linked list. 2. Provide samples of push, pop; and 3. Using your new class, add a method that reverses a given string without using any built-in reverse methods. Use string below as an example. str_sample = 'Did Hannah see bees? Hannah did.' 4. Create a queue class using linked list. 5. Provide samples of enqueue, dequeue; and 6.Zack and Aerith are set to be married. Lined up in front of them will be the entourage of their closest friends composed of 5 pairs. Biggs and Jessie will march first. Announce their names by pair using queues (i.e. use print)! Make sure to use enqueue and dequeue methods! men = ['Zack', 'Cloud', 'Barret', 'Vincent', 'Cid', 'Biggs'] women = ['Aerith', 'Tifa', 'Marlene', 'Lucrecia', 'Yuffie', 'Jessie'] # Example # "Zack and Aerith!" # "Cloud and Tifa!"
- 1a. What is a stack? b. Write an algorithm for all operations in the stack? 2a.What is a queue? b. Write an algorithm for all operations in the queue?USING PYTHON Create a queue class using Python lists under the hood. Make sure built-in list methods are not accessible when using the new queue object so its properties are not violated. Zack and Aerith are set to be married. Lined up in front of them will be the entourage of their closest friends composed of 5 pairs. Biggs and Jessie will march first. Announce their names by pair using queues (i.e. use print)! Make sure to use enqueue and dequeue methods! men = ['Zack', 'Cloud', 'Barret', 'Vincent', 'Cid', 'Biggs'] women = ['Aerith', 'Tifa', 'Marlene', 'Lucrecia', 'Yuffie', 'Jessie'] # Example # "Zack and Aerith!" # "Cloud and Tifa!"Suppose the following operations are performed on an empty queue:enqueue(5);enqueue(?);dequeue();enqueue(9);enqueue ( 12);dequeue();enqueue(10);Insert numbers in the following diagram to show what will be stored in the staticqueue after the operations have executed .front rear
- Assume q1 is a queue created in the main and q2 is created in a block scope and we write q2=q1 and in the main function we print the items of the q1, if no operator= overload method then then Select one: a. The q1 has the same items of q2 b. The q1 items becomes rubbish c. The q1 becomes empty d. The q1 was not changedclass Queue { private static int front, rear, capacity; private static int queue[]; Queue(int size) { front = rear = 0; capacity = size; queue = new int[capacity]; } // insert an element into the queue static void queueEnqueue(int item) { // check if the queue is full if (capacity == rear) { System.out.printf("\nQueue is full\n"); return; } // insert element at the rear else { queue[rear] = item; rear++; } return; } //remove an element from the queue static void queueDequeue() { // check if queue is empty if (front == rear) { System.out.printf("\nQueue is empty\n"); return; } // shift elements to the right by one place uptil rear else {…1. Suppose you have a circular queue of size 6 (1 to 6). Initially the value of thefront and rear is 0. Now show the state of the queue if the following operationis performed on the queue. Also find the value of front and rear in each step.insert (10); insert (5), delete (), insert (9); insert (9); insert (7); insert (5); insert(8); insert (10); insert (11).
- In C++, Write a program which is menudriven ( i) Enque, ii) Deque, iii) Peek iv) Print). It will create a circularQueue of integer type data using array. You have to implement the followingoperations.a. Enqueue (Insert a data to the queue)b. Dequeue (Remove an item from the queue and printit)c. Peek (Print the item at the Front)Print (Print the elements present at the queue)Implement a Queue using a vector or the STD ::queue:: class Note the difference in what it takes to implement using a char[] array vs a vector or the STD ::queue:: class The user will input a string and the program will return the string with each letter in the string duplicated. Displaying correct Queue implementation. Utilize the conventional methods as needed. Sample Execution Please input String: happy Program will produce the output string. Only use the enqueue(), dequeue(), empty(), etc hhaappyy26( How many Elements are there in the Queue? What will be the output of the following Algorithm on the given Queue? Algorithm() { ENQUEUE(“$“) WHILE(X <> 0)THEN { DEQUEUE() X - - } ENQUEUE(“%“) } Data structures and algorithm

