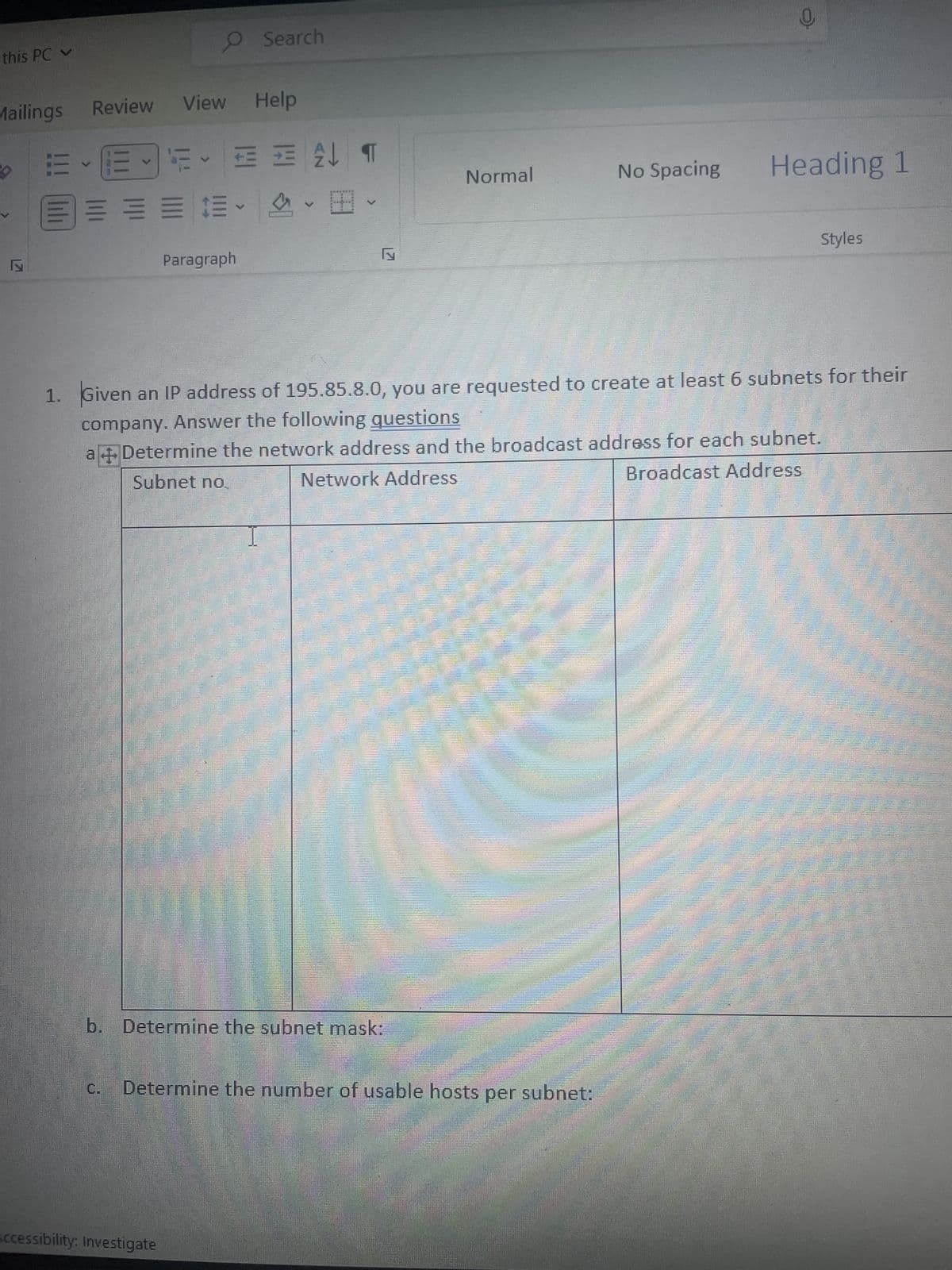
What are 6-7 subnet masks of the ip address: 195.85.8.0
Q: What is a "what you see is what you get" (WYSIWYG) editor, and what are the pros and cons of using…
A: A tool for modifying content is the WYSIWYG editor. Whether it is text or visuals, the information…
Q: Often abbreviated to LAN, this networking technique is used to connect users and devices located in…
A: Introduction: Networking is an essential aspect of modern communication, and LAN (Local Area…
Q: By Carry out a recursive calculation to track down factorial of n, implement a recursive calculation…
A: The Python code is given below with output screenshot
Q: How different are backward integration and forward integration, and what are some ways that this may…
A: Backward integration is the opposite of forward integration. • Forward integration is when a company…
Q: How would you describe the concept of big data in your own words? How does the idea of big data…
A: The term "big data" refers to the large volume of data that is generated by various sources,…
Q: Compared to SSDs used in laptop PCs, what sets enterprise-grade SSDs apart?
A: In this section, we will discuss what sets enterprise solid-state drives different from SSDs that…
Q: The use of wireless networks is not without its challenges. Due to safety issues, should wireless…
A: Introduction: Wireless networks have become an integral part of modern communication, and many…
Q: a.) What does it mean to append data to a file? b.) How do you open a file so that new data will be…
A: We have to explain a.) What does it mean to append data to a file? b.) How do you open a file so…
Q: Indicate what proof technique you'll use to proof this statement then proof the statement. For all…
A: Proof by contradiction.
Q: Critically evaluate the usability of two free music streaming services (YouTube Music and Spotify)…
A: Music streaming services have changed the way people listen to music, and they have become an…
Q: What is the logic behind an associative cache?
A: The question is asking about the logic behind an associative cache, which is a type of cache memory…
Q: A Java virtual machine (JVM) can only execute a single method pe
A: Introduction: JVM uses threads to execute multiple tasks simultaneously, which is a crucial feature…
Q: #include #define NAME_LEN 100 struct part{ int number; char name [NAME_LEN+1]; int on hand; };…
A: Answers:- The correct options are: the location of p is assigned to p1. p1 will not have a…
Q: By Carry out a recursive calculation to track down f of n,implement a recursive calculation to…
A: Code is below: The inquiry comprises of four undertakings, which are to be carried out involving…
Q: Analyze the concept of abstraction by opposing and contrasting it with numerous instances from the…
A: Assigned task: The question centres on the notion of abstraction and its applicability to software…
Q: The data shown was sorted in a Multiple Sort. Which column was it sorted by first and which column…
A: Based on the data provided, we can make some observations that may help us to make an educated…
Q: Do you think that every thread in every virtual machine accesses the same JVM method space?
A: JVM, which transforms Java bytecode into machine language, is the engine that powers Java…
Q: What are some of the most significant cybersecurity threats facing individuals and organizations…
A: Introduction: Cybersecurity is a critical issue in today's world, as businesses and individuals are…
Q: 1. Suppose a knowledge base has the following sentences Sam plays baseball or Paul plays baseball…
A: Given- Sam plays baseball or Paul plays baseballSam plays baseball or Ryan doesn't play baseball We…
Q: Real-world applications are preferred when attempting to persuade others of the value of dynamic…
A: In dynamic programming, we can only proceed with the preparation of each individual component once…
Q: Provide an outline of the two-tier and three-tier architectures for applications. Which is…
A: The functionality of an application is divided into several functional sections, or tiers, in a…
Q: What were the main advantages of DDR over the older SDRAM technology?
A: Introduction :- As comparison to SDRAM, DDR memory has larger bandwidth, faster clock speeds,…
Q: MYSQL 3-Display the last name, job, department number, and department name for all employees work…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!! I…
Q: In what ways are there gaps in the foundational concepts of software engineering? Explain?
A: Software engineering is a rapidly evolving field, and as such, there are several gaps in the…
Q: What is the role of cryptography in cybersecurity, and how do computer engineers design and…
A: Your answer is given below.
Q: In Java what does string method concat used for? Write an example code.
A: In Java, the string data type is used to represent a sequence of characters. Java provides several…
Q: Write a BNF description and a denotational semantics mapping function for the Java do-while…
A: Introduction: The do-while loop is a control structure in Java programming that allows a block of…
Q: Describe a made-up scenario involving login management. Jot down all the many ways you've proven…
A: Scenario management helps handle multiple futures and create customised scenarios. Projects use…
Q: With 8085 Write initialization instructions for the 8259A Interrupt Controller to meet the following…
A: In the below code, the ICW1 (initialization command word 1) is set to 11B, which sets the controller…
Q: While developing application software, what are some of the situations in which you would argue that…
A: Assembly Language is a low-level programming language, as explained. It makes it easier to translate…
Q: Define the term "virtual machine" and explain why it is necessary.
A: Introduction: A virtual machine is created on a physical hardware system (off-premises) that acts as…
Q: How do you recognize when it's a good idea to break up your giant computer's operations and…
A: Introduction: Hardware and software are the two basic divisions of a computer system. The first and…
Q: It is possible for MAC addresses to be used by many interfaces simultaneously. Just why wouldn't you…
A: Introduction: MAC addresses are unique identifiers assigned to network interfaces in computer…
Q: If your kid is utilizing the school's wireless Connection to access the web, they could go to…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Explain each line of haskell code -- function to help double every other element of list…
A: SOLUTION - So, in this Haskell code, there are two functions used doubleDigitsHelper and…
Q: Does software engineering have a single, overarching goal? So please elaborate on what you mean by…
A: According to the information given:- We have to define does software engineering have a single,…
Q: What are some of the key innovations and breakthroughs in the field of computer engineering that…
A: The following are some significant developments and innovations in the field of computer engineering…
Q: What were the main advantages of DDR over the older SDRAM technology?
A: To determine: How did performance-wise DDR outperform SDRAM: In this case, SDRAM is used to refer to…
Q: If you were in charge of a network's management, when would you use static route configuration?
A: Static routing is a method that may be used to provide an exit point from a router in situations…
Q: Consider the snapshot isolation used in the database of a large airline. What are some cases when an…
A: System analysts: The people in charge of creating and designing an information technology system…
Q: ay last name of employees whose manager is KING. 8-Display last name, salary and job title of all…
A: Here are the SQL statements to perform each of the requested queries: SQL (Structured Query…
Q: Consider the snapshot isolation used in the database of a large airline. What are some cases when an…
A: Analysers of systems The people in charge of creating and designing an information technology…
Q: perfonth the hoang ootyorion that dapioy The progra Ask the midde inal and last nam wrOodstudent of…
A: Your solution is given jn next step
Q: For what did people choose for the first commercially accessible computer, the UNIVAC?
A: As we know that the UNIVAC which stands for the universal automatic computer is the first…
Q: transparency features that should be included at a bare minimum in a distributed database management…
A: The question asks about the minimum transparency features that should be included in a distributed…
Q: Write a paragraph contrasting DRAM with SDRAM, taking into account their relative speeds, sizes, and…
A: Dynamic Random Access Memory (DRAM) and Synchronous Dynamic Random Access Memory (SDRAM) are two…
Q: Think of a recent security incident involving authentication or authorization that made headlines.…
A: Your answer is given below.
Q: Write a SQL Query that uses the annual growth to get a projection for total population for the years…
A: Given tables are: table_1: CountryName, Year, AnnualGrowth, CumulativeGrowth table_2:CountryName,…
Q: The question is, how do customers and programmers work together?
A: Why is collaboration necessary? We are aware that software developers collect specifications,…
Q: In what proportion of cases does a good compiler produce code that is superior to that written by an…
A: Let's look at the answer to this problem. In regard to the designs of contemporary microprocessors,…
What are 6-7 subnet masks of the ip address: 195.85.8.0
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- In which of the following applications, UDP is a suitable transport layerprotocol? (a)In SMTP, a user can send a long e-mail message, which may includemultimedia. When a user sends a message, the recipient does not expectto receive a response quickly. (b)A user needs to download a very large text file from the internet. Theuser doesn’t want part of the file to be missing or corrupted when he/sheopens the file. The delay created between the delivery of the parts arenot an overriding concern for him. (c)In DNS, a client needs to send a short request to a server and to receive a quick response from it. The request and response can each fit in one userdatagram.1. Persistent HTTP requires?a. 2(round trip times) + file transmission timeb. as little as two RTT for all the referenced objectsc. one file transmission timed. as little as one RTT for all the referenced objects 2. UDP has no connection between client & server?a. RCVR extracts sender IP address and portb. sender explicitly attaches IP destination address and portc. three other answers are incorrectd. no handshaking before sending data 3. A socket in computer networks is correctly defined as?a. A combination of IP address and port number, connected by a "/" symbolb. sender explicitly attaches IP destination address and portc. RCVR extracts from the socket, sender IP address and portd. A combination of IP address and port number, connected by a"." symbol 4. The data link layer provides?a. the functional and procedural means to transfer data between network entities and the means to detect and possibly correct errors that may occur in the link layer.b. the functional and procedural…Using https://wiki.dd-wrt.com/wiki/index.php/Linking_Subnets_with_Static_Routes as a base, modify the scenario for VLSM based subnets given the following information. Site address (CIDR Notation) = 192.168.10.0/24 Subnet Included hosts Number of hosts required Subnet ID(CIDR notation) 1 Computer Labs 1 and 2 110 ? 2 Computer Lab 3 60 ?
- Which of the following is NOT an argument against using static routing? O. There is no need for more resources, such as additional CPU or bandwidth. O.b. The routing tables are rather compact, and the amount of maintenance required is low. O.c. If the topology is altered in any way, the configuration will be impacted. The path to the goal does not ever diverge from its usual course.There are events from different web server logs (see below). What can you tell about each row? What is happening in each row? What might be interesting in case of incident investigation? timestamp="09/Mar/2016:11:14:34 +0300" client_ip="73.9.84.166" user_agent="Debian APT-HTTP/1.3 (0.8.16~exp12ubuntu10.26)" url="/precise-security/stable/amd64/Packages.bz2"[09/Mar/2016:11:14:35 +0300] wiki-api.company-realm.ru 25.255.240.122 "GET /_api/frontend/.is_readonly?=&__uid=1120000000006167 HTTP/1.1" 200 "-" "-" "ivanovaa" "companyuid=5986251411438764783" - 717 0.022 0.022[09/Mar/2016:11:14:35 +0300] fml.company-realm.ru 202a:6b8:b010:2048:0:d0c0:5:12 "GET /rest/v2/call/collectPoolFromQueriesRatings/32b86116-e409-11e5-bdc7-0025909427cc?ticket=3201127 HTTP/1.1" 414 "-" "Apache CXF 3.0.4" "-"[09/Mar/2016:11:14:35 +0300] 127.0.0.1:443 127.0.0.1 "GET /ping HTTP/1.0" 200 "-" "KeepAliveClient" "-" "companyuid=-" - 273 0.146 0.146[09/Mar/2016:11:14:34 +0300] st.company-realm.ru 127.0.0.1 "GET…Which of the following is NOT a reason to be against using static routing? O. More resources, such increased CPU power or bandwidth, are not necessary. O.b. Since the routing tables are very small, minimal maintenance is required. O.c. Any modification to the topology will have an impact on the configuration. The path never veers from the objective on the way there.
- An attacker tries to do banner grabbing on a remote web server and executes the following command:$ nmap -sV hackme.com -p 80 He gets the following output:Starting Nmap 7.90 ( http://nmap.org ) at 2020-09-26 22:47 ESTNmap scan report for hackme.com (108.58.137.114)Host is up (0.048s latency).PORT STATE SERVICE VERSION80/tcp open http Apache httpdService detection performed. Please report any incorrect results at http://nmap.org/submit/.Nmap done: 1 IP address (1 host up) scanned in 7.36 seconds What did the hacker accomplish? nmap can’t retrieve the version number of any running remote service. The hacker successfully completed the banner grabbing. The hacker should have used nmap -O host.domain.com. The hacker failed to do banner grabbing as he didn’t get the version of the Apache web server.You have launched an Amazon Elastic Compute Cloud (EC2) instance into a publicsubnet with a primary private IP address assigned, an internet gateway is attached tothe VPC, and the public route table is configured to send all Internet-based traffic tothe Internet gateway. The instance security group is set to allow all outbound trafficbut cannot access the internet. Why is the Internet unreachable from this instance?Let’s consider you have a Class C IP address 204.15.5.0/24. You have to determine whether it is possible to createfollowing network with the given IP address? If yes, what could be the possible ranges of IP addresses for thesubnetworks?
- Say that the Top Level Domain .gov were to suddenly lose all its name servers due to a system crash. Now say that a user on a host example.school.edu wants to FTP to a machine called host51.defense.gov, with which they have never communicated. a. Explain the process that would occur starting with the user’s host until something goes wrong, and explain what would go wrong. b. Now, say that the user had already FTPed some files from host51.defense.gov 10 minutes before the nameservers at .gov crashed. Would connecting again likely work? If so, how would the process that occurred be different?Let’s consider you have a Class C IP address 204.15.5.0/24. You have to determine whether it is possible to createfollowing network with the given IP address? If yes, what could be the possible ranges of IP addresses for thesubnetworks? Let’s consider the above network. If you are using VLSM /CIDR, determine what subnet mask numbers allow therequired number of hosts.For the given IP address 193.105.1.60/27, find the network address, First Address, Last address for the host, Broadcast address and next subnet address. please tery to anser in differnt way coz i dont same this answers to avoid plag try to do it in diffrent way with same answers Step 1 Given IP address 193.105.1.60/27 is a Class C address with CIDR /27 /27 means that the subnet mask is 255.255.255.224 Default subnet mask of Class C is /24 or 255.255.255.0 Here the CIDR is /27, so 3 bit subnetting is used, ie, 3- bit is borrowed from host part to network part. Number of hosts/subnetnetwork = 2m - 2, where m is the remaining bits in the host part, here m=5 =25 - 2=30 hosts Given IP 193.105.1.60/27 is in the network range 193.105.1.32 - 193.105.1.63 Step 2 Network address: It is the first address in the network range. So, 193.105.1.32 is the network address First Host address: It is the first valid host IP address which is…











