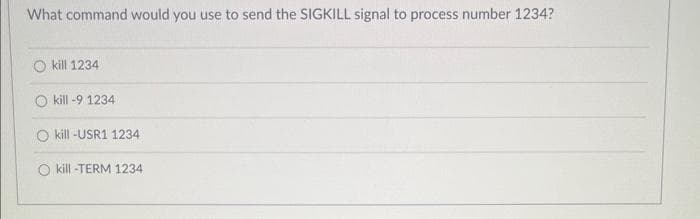
What command would you use to send the SIGKILL signal to process number 1234? 104004
Q: City: Colors: Red Green Blue Black
A: Dear Student, The answer to your question is given below -
Q: A wide variety of diagnostic tools and fundamental utilities are available for use in network…
A: Given: Common utilities and tools aid in managing and identifying network issues. Describe the…
Q: Consider the following example: MOV AL, -5 SUB AL, +125 After executing these two lines of…
A: The first instruction in given piece of code make sure that AL= -5 second instruction perform…
Q: In order to function correctly and efficiently, what are the three conditions that must be met by a…
A: Dear Student, The three required conditions is given below -
Q: Besides HR, at least three other divisions' policies should be considered when developing a plan to…
A: Below is the response: The purpose of having comprehensive plans established is to provide clarity…
Q: Give us a term that you can use to describe "application security."
A: To guard against dangers like illegal access and alteration, application security is the process of…
Q: Why would anyone want to make file extensions visible if they are trying to protect themselves from…
A: The file extensions are crucial since they inform your computer and you about the file's icon and…
Q: Information technology's short- and long-term effects on people, groups, and communities Is it not…
A: Definition: Information Technology: Impacts on Society and Our Daily LivesPresent arguments from…
Q: When a hard drive is formatted, all of the partitions inside that drive must utilize the same…
A: The naming conventions, storage locations, and access methods for files on a storage device are all…
Q: Professionals in the field of cyber security may use a variety of methods to effect positive change.
A: Cybersecurity refers to defending internet-connected systems from online threats, some of which are…
Q: The Access Security Software protects your data by doing what exactly?
A: Definition: The intention is to provide users access to just the information that has been…
Q: What is the overarching concept that must be adhered to when developing the microkernel of an…
A: Given: What is the overarching philosophy that the microkernel adheres to? What is the most…
Q: Why did people come up with the idea of a RISC architecture?
A: The Instruction set architecture is a part of processor architecture that is necessary for creating…
Q: Explanation of the OS's two main functions.
A: Introduction: Once a boot programme has loaded the necessary system files, the remainder of the…
Q: What is the overarching concept that must be adhered to when developing the microkernel of an…
A: Given: What is the fundamental principle of the microkernel? What distinguishes modular the most?…
Q: Do you know why all the threads running in a JVM share the same method area
A: Dear Student, The answer to your question is given below -
Q: Rewrite the following nested if-else statement as a switch statement that accomplishes exactly the…
A: To convert into switch case, consider the set of values for each of the cases where f1, f2, f3, and…
Q: Correct and detailed answer will be Upvoted In C Question: How can the function,…
A: The function, matrix_initialize_unopt, be optimized in the given below code in C programming.
Q: You'll find concise explanations here of the two most crucial elements of operating system…
A: Software constitutes the computer's operating system. An operating system is the software that…
Q: Understanding the system's authentication and access methods is crucial for reasons of data safety.
A: Introduction: Authentication is the process of determining whether or not someone or something is…
Q: Perform the Encryption for the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".
A: The solution is given below with step by step explanation
Q: Make a case brief on Brand v. Hyundai Motor America, 226 Cal.App.4th 1538 (2014). Please include…
A: Hyundai Motor, currently ranked fifth globally and aiming to sell five million vehicles in 2015,…
Q: The show cdp neighbor command is run on multiple network nodes by a network engineer for the purpose…
A: Introduction: Keith McCloghrie and Dino Farinacci developed the Cisco Discovery Protocol (often…
Q: Examine the difficulties brought on by data integration technology.
A: Solution: Information system characteristics: insufficient planning choosing a tool joining forces…
Q: In the process of designing the microkernel of an operating system, what should serve as the guiding…
A: What principle underlies the development of the microkernel in an operating system? What…
Q: The meaning of a file extension must be kept distinct from its visual representation in a file.
A: Introduction: Document file extension purpose must be discussed. The machine should have different…
Q: You are given the following class definition for an array-based List ADT: public abstract class List…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: Discuss 3 different assumptions ImageJ makes and 3 different potential sources of error from ImageJ…
A: Assumptions for the ImageJ --> 1) There are the two important things in the ImajeJ that is the…
Q: The Springfork Amateur Golf Club has a tournament every weekend. The club president has asked you…
A: Solution: Given, (1) A program that will ask the user how many golfers will be entered, read…
Q: In the process of designing the microkernel of an operating system, what should serve as the guiding…
A: The answer to the question is given below:
Q: To "explain?" is to be recognized as someone who can motivate technical experts to give their…
A: Introduction: You are regarded as explain when you have the ability to motivate technical people to…
Q: Perform the Encryption using the Vigenere cipher for the following: Messege= "discovery", and…
A: Vigenere cipher Vigenere Cipher is a method of encrypting alphabetic text that uses a simple form of…
Q: C Programming Language Task: Deviation Write a program that prompts the user to enter N numbers and…
A: Algorithm of the code: 1. Start 1. Declare three double variables: sum, avg, and maxDeviation, and…
Q: How sure can you be that your private data will remain safe? How can we safeguard the authenticity…
A: Any organization that gathers, handles or maintains sensitive data must have a data protection…
Q: Write a C++ Program to Find the Sum Above and Below of Main Diagonal Matrix + 7 2 LO 00 3 main…
A: iterate from i=0 to i<n iterate from j=0 to j<n if j>i…
Q: Can you name a specific use case for authentication? Consider the pros and cons of the various…
A: Below are the advantages and disadvantages of different authentication methods Authentication allows…
Q: How often does a network administrator use a static route, and why?
A: Network administrator: A Network Administrator is a person responsible for maintaining an…
Q: c.This part provides you with an opportunity to demonstrate your understanding of the…
A: The answer is given in the below step
Q: Write a program that asks the user to enter the size of a triangle(an integer from 1 50). Display…
A: Please find the answer below :
Q: Problem 4: For each degree sequence below, determine whether there is a graph with 5 vertices that…
A: Graph: Graph is a non-linear data structure. It consists of vertices and edges. A graph can be…
Q: In the process of determining the number of unknowns for link support, how many unknowns do you…
A: The answer is given in the below step
Q: ption and decryption using the RSA algorithm for t
A: I have answered below: The RSA algorithm is used to encrypt and decrypt the data, it is the concept…
Q: Please provide me with a list of the top five security holes in my network and the top five threats…
A: Network security faults or holes are found in the system's software, hardware, or administrative…
Q: Apart from overseeing the operations it regulates, what are the other two primary responsibilities…
A: Given: What are the other two main jobs of an operating system, besides managing processes? Answer:…
Q: In what ways can clients and programmers work together?
A: Introduction: Why is collaboration necessary?We are aware that software developers collect…
Q: What is the overarching concept that must be adhered to when developing the microkernel of an…
A: Given: What is the fundamental of principle of the microkernel? What distinguishes modular the most?…
Q: What should happen if the processor issues a request that triggers a cache hit while it is in the…
A: The cache will be able to fulfill the request because, if it were not for the fact that it is idle…
Q: How can workers make sure that the information they have learned stays within the company? Let's…
A: Definition: The case study that is offered describes the organization's internal information assets…
Q: Is there a comprehensive list, ordered by frequency of occurrence, of all known danger categories,…
A: all known threat types and order threats with URL evidence from more commonly encountered to least…
Q: Before using a file extension, make sure you understand what it is and how it will affect your work.
A: Introduction File extension:The suffix at the conclusion of a computer file is known as a file…
Step by step
Solved in 2 steps

- What does genrsa and des3 refer to on the following terminal command: openssl genrsa –des3 –out server.key 1024#write code for the server #write code for the client the Card number = 1000987 password number = 2222 then check password correct or not thrn appy transcation processs # code must must use so socket library (import socket) #tcp connection # python language pleasepenetration programming Modify the .sh script so that it also works interactively. Specifically, if no hostname is given on the command line, the program should interactively ask for a hostname, starting port, and ending port with three separate prompts, and carry out its scan using those values. After scanning finishes, the program should loop to receive another set of values, stopping only when the user enters a blank host name. If this feature is implemented properly, it will also allow you to run the script in ’batch’ mode, by “piping in” a plain text file with the hostname on the first line, start port on the second, stop port on the third, and repeating for as many hosts as you wish to scan. For example, if a file named hosts_to_scan.txt contains a list of hosts and ports in the proper format, the program should now work as follows: cat hosts_to_scan.txt | ./portscanner.sh The timeout argument should still work in this case as well: cat hosts_to_scan.txt | ./portscanner.sh -t 3…
- Datagram socket is the connectionless socket which uses FTP. Question 2 options: True FalseYour DHCP server's configuration now includes these alternative DNS servers. In general, what is the best way for your clients to get the new settings? * Double-click the Restart button. Just do ipconfig /registerDNS on the client's machine. Watch for the DHCP client to request a lease renewal. O Input ipconfig /renew into the client's terminal. Do not forget to clear the server's DNS cache.you are supposed to develop one client and two servers. The client registers (sets username and password) itself on server1. Server1 passes this information to Server2. Now client can login to Server2 and perform a full-duplex chat. Note: Only username and password combination set at Server1 can be used for login at Server2.
- Please I need help ASAP. You will complete the TRACERT.EXE in windows machine or tracepath in Linux / Mac machine analysis of each of the ip-address . Write a C program that completes step 1 and stores the results in an output file (e.g. tracert.txt) having the columns as ip-address, hop-time1, hop-time2, hope-time3, destination-ip . You can do it manually. ThanksWhat does the command “sudo nmap –script=smb2-security-mode.nse -p 445 10.0.0.2-255”?You have just configured a DNS server. Your security team mandates that you cannot use the root hint servers for external lookups. Instead, all external lookups must go through the OpenDNS servers 208.67.220.220 and 208.67.222.222. What mechanism in the DNS server setup lets you specify a specific DNS server to query for external lookups ?
- Pseudocode Port Scanner INPUT : IPv4 address with its port range TASK/function : Try the Internet Protocol address with its a port range The software will attempt to find open ports on the particular pc within having a connection to every one of them as well as having any successful connection ports, trace a port as open. OUTPUT : status of port (open/closed)Execute the command to show the files that are needed for routing operation. Get theinformation about the various drivers and interfaces present in your PC.linux commands Set your windows machine to receive IP address from DHCP server. From a windows client open an SSH session to server1 as root From a windows client open an SSH session to server1 as normal user configure the SSH server to deny remote root login and allow only the two users user1 and user2 From a windows client verify if you can access to server1 as root From a windows client verify if you can access to server1 as user1 From a windows client verify if you can access to server1 as user2



