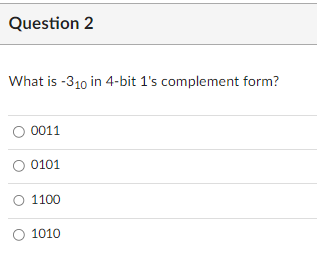
What is -310 in 4-bit 1's complement form? O 0011 ○ 0101 O 1100 O 1010
Q: the difference between TKIP and C
A: Solution - In the given question, we have to specifies the differences between TKIP and CCMP.
Q: Provide a rundown of all the available cloud computing assets. What kinds of companies are using…
A: Asset in Cloud Computing: Cloud-based asset management is a software system that manages the data…
Q: Write an application using c++ classes that Asks for the name of a student asks for the name of a…
A: Step 1 : Start Step 2 : Create the class Academics which contains the private data fields. Step 3 :…
Q: Explain Product of Sum Form ?
A:
Q: What are the expectations for the verification process to achieve? When compared, why do certain…
A: Authentication determines whether someone or something is who or what it says it is. Authentication…
Q: What is singleton class in oops ? Please explain in brief
A: As the name suggests that a singleton class is that class which have only one object at a time.…
Q: Differentiate between JDK and JRE.
A: In this question we have to differentiate between JDK and JRE Let's understand
Q: Differentiate between JDK and JRE.
A: The solution to the given question is: INTRODUCTION The Java Development Kit (JDK) , together with…
Q: The way the router's boot procedure is defined.
A: The purpose of the component of artificial intelligence known as an artificial neural network is to…
Q: Input is greater than or equal to three. Example: INPUT: Enter array size: 7 Enter element 1:…
A: Here in this question, much has been given as the explanation above. We are asked to create a…
Q: In the field of computer science, one often resorts to using a programming language in order to…
A: Definition: It is possible to do a wide number of jobs using programming languages such as Basic,…
Q: What is join in SQL?
A: Given To know about the SQL join.
Q: Convert (125.62)g to binary.
A:
Q: What core concepts of software engineering are being ignored, if any?
A: Core Concepts of Software Engineering: There are four fundamental principles in software…
Q: Explain what you mean when you say "computer."
A: Computer is a electronic device or machine which performs different operations, calculations and…
Q: s to be no need for a modem to be placed between a phone line and a communic
A: Introduction: Telephones are incredible devices that, by causing electricity to flow down a line,…
Q: Please written by computer source
A: As a general rule, a source is the area from which data is assembled. For instance, on the off…
Q: What steps are taken in the creation of a new programming language?
A: An programming language is a one type of language which can consist of set of instructions.
Q: Explain the Decimal Number system?
A: Given To know about the decimal number system.
Q: locations prone to collisions This Cisco switch command may be used to investigate issues with VLAN…
A: Introduction: Use the show interface trunk command to see if the peer-native and local VLANs are…
Q: For what reason is it required to use a modem to connect a telephone line to a communication…
A: A modem has just two components: the modulator and the demodulator. It converts digital signals to…
Q: Should software developers always provide their employers code that can be easily updated?
A: Software Developers: Typically, software engineers do the following tasks: Analyze the demands of…
Q: Using the primary key definitions from the 2NF and 3NF, order the generic definitions. Give a…
A: 2NF: This states that a relation that is in first normal form and it should not have any non-prime…
Q: What is Normalization in SQL?
A: SQL Working with databases is possible with SQL. There are numerous SQL dialects, despite the…
Q: What happens when you hover the mouse over a box's corner or edge when a scaling handle has been…
A: Answer: Introduction: First, you have to understand the scaling in CSS. In CSS, the transform…
Q: Ask yourself this: Is there anything that doesn't adhere to the principles of software engineering.…
A: Software Development: Software engineering is characterised as a methodical, disciplined, and…
Q: What is join in SQL?
A: In SQL, JOINS is the command which is used to combine rows from two or more tables, based on a…
Q: How to create a table in SQL?
A:
Q: What are two common techniques used to protect a password file?
A:
Q: What is N
A: Introduction:Programmers use the domain-specific language SQL to manage data stored in relational…
Q: Do a search in Google (or your favorite search engine) and find at least 5 other vendors that…
A: What exactly IKEv2 is? IKEv2 stands for Internet Key Exchange version 2 which is one of the VPN…
Q: How do you go about selecting the ready-made software that will be used? Which sorts of criteria…
A: Software off-the-shelf: Software purchasing involves various elements and particular concerns.…
Q: What is SQL?
A:
Q: CONVERT THE CODE TO JAVA: #include using namespace std; int main(void) { char input;…
A: Please find the answer below :
Q: 23) What is mutual exclusion, what problem does it solve?
A: Mutual exclusion is a property of process synchronization which states that “no two processes can…
Q: What use does the term "acceptable" serve in the context of software development?
A: Encryption: We need to talk about the importance of successful application development and the…
Q: What is Normalization in SQL?
A: Introduction: Normalization: Normalization is the process of organizing the data in the database.…
Q: When you think about email, what do you see? I was wondering what the best manner of sending an…
A: Answer: Email stands for electronic mail which means it is simply a process of delivering or…
Q: Write a C program that accepts an integer and determines whether the number is divisible 2, 3 or 5.…
A: Answer:
Q: Discuss about the Blockchain adoption so far.
A:
Q: Is it necessary to become proficient in a programming language?
A: The process of creating a set of instructions that tells a computer how to perform a task is known…
Q: What is ETL in SQL?
A: Extract, Transform, and Load is referred to as ETL. To extract data from a database, alter it, and…
Q: Description Inheritance
A:
Q: List and briefly define four techniques used to avoid guessable passwords.
A: Introduction: Four techniques are used to avoid guessable passwords. Make use of a combination of…
Q: What happens when you hover the mouse over a c ontains size handles?
A: With regards to image processing for projects including image and video comment, bouncing boxes are…
Q: If at all feasible, the metrics that were utilized in the process of developing the program should…
A: Introduction: Metrics for software development are quantitative measurements that may be used to…
Q: What core concepts of software engineering are being ignored, if any?
A: Introduction: When confronting a new topic, it is important to first examine how similar problems…
Q: If at all feasible, the metrics that were utilized in the process of developing the program should…
A: Introduction: Software development metrics quantify a product's performance, quality, or team…
Q: What is ETL in SQL?
A:
Q: Do you have any ideas about email that you'd like to share? How does information go from one…
A: Solution given for above question, Introduction:
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- WHAT IS THE 16-BIT BINARY (2’S COMPLEMENT) REPERESENTATION OF EACH OF THE FOLLOWING SIGNED INTEGERS? A. -18 B. -12 C. +129 D. +64 E. -256How the decimal number 107 is coded as a 32 bits number, big endian, using the 2’s complement representation? • Same question with -19 instead of 107. • How 107 is coded using 1’s complement?Using 8-bit representation, what is the 2’s complement of the result of ((45 base 10) + (44 base 10))?
- WHAT IS THE 16-BIT BINARY (2’S COMPLEMENT) REPERESENTATION OF EACH OF THE FOLLOWING SIGNED INTEGERS? A. -18 B. -12 C. +1291. Convert −1710 to 8-bit 2’s complement. (Show your work.) 2. Convert 50026 to decimal. (Show your work.) 3. What is the largest 3 digit number we can represent in Octal? Give the octal representation and convert to decimal. 4. Convert 101101110112 to hexadecimal.What is 4365 - 3412 when these values represent unsigned 12-bit octal numbers? The result should be written in octal. Show your work.
- Part 1: What integer is represented in 8-bit two’s complement as 10110010 . Circle your final answer. Part 2: Convert the integer -103 to 8-bit two’s complement. Circle your final answer.What is the decimal value of this 16-bit 2's complement number: 1111111111111001twoWhat is the negative representation of 110100110010 represented with 18 bits in Two's complement is: __________??? Please explain thoroughly 001011001110 is NOT correct
- What is the hexadecimal value of the number 1019 assuming two’s complement representation in 12 bits?If the bit pattern 0xffff_ffff_ffff_ffff_ffff_ffff_ffff_ffbd is used for a 128-bit two's complement integer, what number does it represent? show your answer in base ten.How many different values can be represented using 16-bit two’s complement representation? What’s the largest and smallest possible value? Answer the two questions again for n-bit 2’s complement. Please show all steps.

