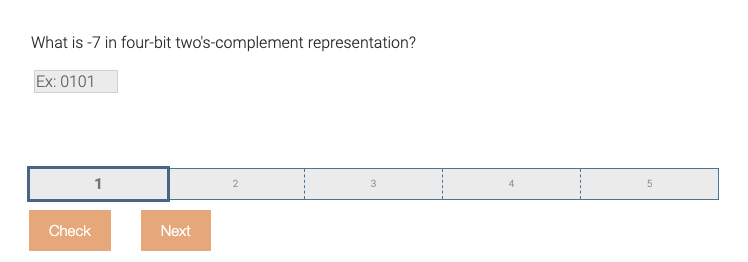
What is -7 in four-bit two's-complement representation? Ex: 0101
Q: How to modify exitstatus.sh to print a message for each of the three exit statuses described in man ...
A: How to modify exitstatus.sh to print a message for each of the three exit statuses described in man ...
Q: you need to fill in the table with the inputs you choose for testing and justify your selection. You...
A: Here we need to provide 7 distinct test cases for binary search program . The array should be in sor...
Q: When dividing a 4-TB hard disc, which partitioning method should you use?
A: Introduction: If you wish to partition a 4TB hard drive in Windows, you must first learn about the f...
Q: Alice and Bob use the ElGamal scheme with a common prime q = 131 and a primitive root a = 6. Let Bob...
A: ANSWER:-
Q: Show that the language {ambn| m ≠ n} is context-free.
A: Context free grammar is a formal grammar which is used to generate all possible strings in a given f...
Q: Describe the processes and outcome of a preliminary inquiry.
A: Introduction: A preliminary inquiry is when a judge evaluates the facts in your case to determine wh...
Q: What is the location and name of the Windows paging file used for virtual memory?
A: The answer is given below:--
Q: What kind of error messages may you get if you try to login using the ssh-i option?
A: Introduction: Ssh-i : SSH is an abbreviation for Secure Shell. The command is used to log in to a s...
Q: types of intruders.
A: First let's understand what is intruder: An intruder is a person who attempts to gains unauthorized ...
Q: Provide me with the MATLAB code to swap the first and last row of the matrix given below, mat = 1111...
A: Here we have given the code in Matlab which swaps the first and last row of given matrix
Q: What effect will the internet of things (IoT) have on our daily lives? Justify your viewpoint using ...
A: the answer is given below:-
Q: Which fibre is utilised to protect the inner core and prevent the cable from straining in fiber-opti...
A: Introduction: Fiber optic cable is a form of network cable that is commonly used to carry data. It i...
Q: What are the difficulties and issues raised by the use of non-integrated information systems?
A: Given :- What are the difficulties and issues raised by the use of non-integrated information system...
Q: How many cells are in RAM in a 32-bit computer?
A: A 32-bit system can access 232 different memory addresses, i.e 4 GB of RAM or physical memory ideall...
Q: bout Errand Assistance Service Applications (Ease App)
A: An Errand Assistance Service Application (EASE App) is an application that is used for the delivery ...
Q: Describe an attack against a web cookie-based authentication scheme??
A: Introduction: Allows an attacker to utilise an automated process of trial and error to guess a perso...
Q: What is a technology activator?
A: The term, “activator” means an agent that accelerates a process. In other words, it renders another ...
Q: How many Matlab seat licenses are required for there to be a ~1% steady state probability that no li...
A: what is Matlab? Engineers and scientists use MATLAB® to research and develop systems and technologie...
Q: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let Bob'...
A: Key generation Common prime q=131 primary root αα = 6 Bob's public key YBYB =3 Random integer chosen...
Q: The following statements describe the computer arithmetic. Select all the TRUE statements. a XOR re...
A: Defined the given statements true or false
Q: As an example, choose a specific operating system.
A: Introduction: To handle a problem, a computer system requires a range of hardware and software resou...
Q: Describe what makes a mobile app special.
A: There are so many features that make an app special.
Q: . Draw state diagrams of the control software for: A telephone answering system that records inco...
A: According to the information given:- We have to draw a state diagram of the mentioned instruction.
Q: What is a palindrome? A palindrome is a string that is the same when read left to right as when read...
A: I have provided C++ CODE along with CODE SCREENSHOT and also provided OUTPUT SCREENSHOT--...
Q: 3. In the following indicate all Write Before Write hazards. Circle the offending registers and conn...
A: Indicate all Write Before write hazard.Circle the offending registers and connect them with a line.A...
Q: Complete the code where it says Your code here. When you are done enter ONLY the code you added in t...
A: Algorithm: 1.Include header files 2.Read prefix and sufix 3.Print the ouput as required 4.end
Q: Architecture that has more than one core is called multicore
A: SUMMARY: - Hence, we discussed all the points.
Q: What is the code for DI/BH?
A: Registers DI and BH: DI, or Destination Index, is a 16-bit index register that pokes the currently w...
Q: What is the next step in deploying the GPO that has been created?
A: GPO stands for group policy object As the name suggest is the group of policies which are in the fo...
Q: In CORAL LANGUAGE please and thank you! Summary: Given integer values for red, green, and blue, sub...
A: integer r integer b integer g integer min r = Get next inputb = Get next inputg = Get next inputmin...
Q: Define a splitstream upgrade, patch, release, and version in terms of system upkeep.
A: Introduction: System maintenance is used to help users and organizations achieve their objectives. ...
Q: Consider the following weighted undirected graph with 7 vertices and 11 edges. А C 7 8 9. 15 E D 8. ...
A: According to the information given:- We have to consider undirected graph and with the help of Dijks...
Q: In matlab Using doc function, determine what the dot-forward slash (./) operator does
A: Here is the explanation about the doc function:
Q: and individual networks. This can be achieved by dividing the 32-bit IP addres into two parts: an in...
A: The answer is
Q: 2) Build your portfolio applying HTML and CSS and submit both of the files.
A: The required portfolio website files are provided in the next step.
Q: In traditional file processing, the structure of data files is stored in the catalog separately from...
A: So Actually in the DBMS file are actually stored in the seperate from the actual location. Beacuse o...
Q: Hello, can you tell me the work mode of adobe
A: SUMMARY: - Hence, we discussed all the points.
Q: write shortnotes on a. firewall b, need of cryptography c. types of attacks
A: Explain a. firewall b. need of cryptography c. types of attacks
Q: A GSM system uses 124 channels and each dhannelis dded into time siots. What is the maximum number o...
A: The answer is
Q: Will apps eventually make the web obsolete? What is your justification?
A: Introduction: Will apps eventually make the web obsolete? What is your justification?
Q: How would you differentiate between unicast and multicast addressing? It is required to add an examp...
A: Let's see about the unicast and multicast addressing. Unicast addressing Unicast addressing are used...
Q: Define the concept of Resource allocation ?
A: According to the question useful resource for the allocation this is a method of planning, managing,...
Q: Input alphabet = {a,b} 1. write the CFG for the language of palindromes 2. Convert this into PDA (st...
A: Below is the answr to abobe questions. I hope this will meet your requirements.
Q: write a java program to print the mirror image of right angled in x-direction after taking number of...
A: Required:- Write a Java program to print the mirror image of right-angled in x-direction after takin...
Q: Create a mind map with the word Information Technology as the center
A: The figure of mind map is given in second step.
Q: do you think that OWASP Dependency CHeck is a bet
A: Solution 1: OWASP actually refers to the Open Web Application Security Project and it is an online...
Q: Proof: Let A and B be any sets. (A − B) ∩ B = (A ∩ Bc ) ∩ B by the _______ law
A: Please upvote me Please. I need it badly. Please. I am providing the correct answer below. We need...
Q: 1. Enumerate three apps that you use and identify them based on their type, implementation and licen...
A: Mobile Apps can be categorized depending on a plethora of factors such as: The Technologies they ar...
Q: Question :) 02 Recall the problem of finding the median of an array of an unsorted list. How fast ca...
A: the answer is given below:-
Q: e) Find the moment of inertia of a hollow cylinder about the axis of the cylinder using a JAVA progr...
A: To write java code to find the moment of inertia of a hollow cylinder about its axis.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- A(n) _____ operation transforms a 0 bit value to 1 and a 1 bit value to 0.What is the equivalet 2's complement representation for -15 in 16-bit hexadecimal representation? a) FFFE b) 7FFE c) FFF1 d) 7FF1How does an ALU manage negative numbers, especially in the context of two's complement representation?
- Using 2's complement representation, what is the binary representation of -15 if you use 7 bits in total?What is two's complement representation, and how is it used to represent negative integers in binary?Find the representation x of the following numbers listed below in the base specified on the right; 1.- (10100110)2=(x)10 # both signed and unsigned for a eight-bit binary representation 2.- (207)10=(x)2 3.- (-135)10=(x)2 # In a two-complement representation 4.- (2D7)16=(x)2 5.- (-3.3125)10=(x)2 #IEEE 754 standard, 32 bit representation

