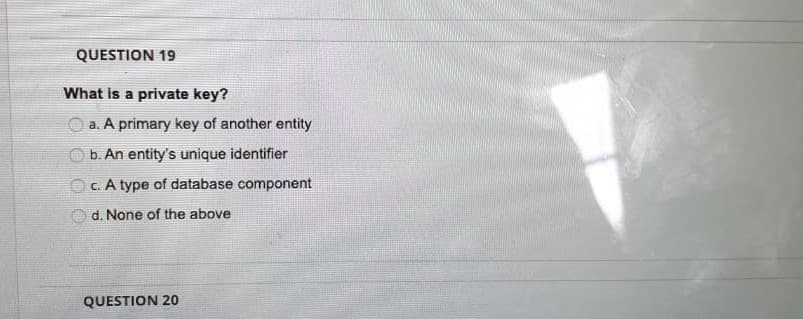
What is a private key? O a. A primary key of another entity b. An entity's unique identifier Oc. A type of database component O d. None of the above
Q: QUESTION 10 Which of the following terms describes the set of items that, if completed, would signal…
A: Velocity just specifies the speed of processing data. Sprint Retrospective is last think done in a…
Q: The semantic layer enables the user to view the technical layers of the database? True/False
A: Note: Hello. Since your question has multiple parts, we will solve the first question for you. If…
Q: 1) In a database Table, the each category of information Is called A. Field B,Record C Tuple D. All…
A: As per company guidelines we are suppose to answer only first 3 subparts of the question. Kindly…
Q: Defineanomaly? Having three abnormalities in a database? Will you see the problems and provide a…
A: Anomaly -- Anomalies are atypical occurrences.-- It is a relational issue brought on by repetition…
Q: Discuss the ACID properties of a transaction with the help of code example.
A: A transaction is a single logical unit of work which accesses and possibly modifies the contents…
Q: Create the database name Company which consists of one Entity name Employee which consists of 10…
A: Note: As per the guidance can answer the first three sections. Please re-submit the question for the…
Q: 9. How many types of keys in Database Design? a. Candidate key b. Primary key c. Foreign key d. All…
A: There are Seven Types of Database design keys, they are Super, Primary, Candidate, Alternate,…
Q: A)Which of the following are used to indicate cardinality symbols? a.WITH b.P c.None of the…
A: A) Cardinality symbols: Cardinality of a relationship defines the number of instances which can be…
Q: A collection of data which is stored in a logical form is known as? A. A field B. DBMS C. A…
A: Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: How is a database lockout different from a database deadlock? Give an accounting example to…
A: Database deadlock is a condition in which no data can be accessed as sites are held at halt due to…
Q: Triggers for a database must be written with caution. Exactly what kinds of issues could you run…
A: Any complex data integrity rule needs to have triggers. You can't enforce this elsewhere except the…
Q: QUESTION 3 "In a library database system, an employee at the front desk responsible of entry of…
A: 3) The correct answer is parametric end user
Q: 1. Create new database on Microsoft Access (give it your name). 2. Perform the following tasks on…
A: Note : As there are 5 questions, answering 1st question according to the guidelines. Repost other…
Q: Q3/ Consider the relational database of Figure 1. What are the appropriate primary keys? employee…
A: Answer Here most appropriately in relation employee person_name can be set s a primary key, because…
Q: 21.Schema is a skeleton structure that represent the logical view of entire databaseSingle choice.…
A: Data Base Management System: DBMS is a software that is used to store, manage and use database…
Q: 47. Which of the following hardware components is the most important to the operation of a database…
A: Database management system (DBMS) is a software used to manipulate, store and access large amount of…
Q: Which of the following is True about Relational Database Modeling? O a. It is a physical…
A: Relational data model represents how the data is stored and maintained in a relational database. It…
Q: Use the database Crow's Foot ERD shown below to answer the following: 1. Identify all partial…
A: A) partial dependencies: As we know, when non-prime attribute in a relation is functionally…
Q: Give two advantages to each of the strategies for storing a relational database listed below: Keep a…
A: advantages of relational databases Categorizing data. Database administrators can easily…
Q: our own words, how will explain database to no
A: Required: In your own words, how will explain database to non-IT.
Q: A database containing data about parking violations contains no transitive dependencies. Which of…
A: I have given an answer in step 2.
Q: Which is not included in the ACID properties of transactions? O A. Durability or permanency Changes…
A: In the context of transaction processing, the acronym ACID refers to the four key properties of a…
Q: 6. Which of the following is the structure of the Database? a. Table b. Schema c. Relation d. None…
A: Please find the answer to the above question below:
Q: se's mi
A: Preprocessing, or preparing the data for mining, is a crucial stage in data mining. Real-world data…
Q: - DBMS The most commonly hardware into database system * O True O False - define ERD * Your answer…
A: The given image has three questions related to DBMS, ERD and the relationship instance , each of…
Q: A) The following relations kind a part of a on-line database (the relations area unit self-…
A: The physical ER(Entity-Relationship) diagram is it is physically connected with the database schemas…
Q: Entity-relationship model is used for designing databases. True or False?
A: About entity relationship model:…
Q: Outline the role of the following people in the IS audit department: a. The executive b. IT…
A: The first three parts will be answered. Role of the following people in IS audit department: a. The…
Q: Consider the following normalized relations from a database in a large retail chain What…
A: Denormalisation is process related to the database. The primary requirement to do denormalisation is…
Q: Which of the three types of database critical events would initiate the recovery process? Describe…
A: Database recovery method: It is a form of recovery to restore an incoherent archive. Backup and…
Q: 3. Secondary keys are also known as: a. candidate keys. b. foreign keys. c. There are no other names…
A: The key that has not been chosen as the primary key is known as the secondary key. 3 answer…
Q: 1. Once the relationships and dependencies amongst the various pieces of information have been…
A: 1.False Actually it is is possible Once the realtionships and dependencies amongst the various…
Q: What three database critical events may trigger database recovery? Example: Discuss five transaction…
A: Recovery procedure for databases: It is a database recovery process that is used to restore an…
Q: A trend in database management, known as Database as a Service, places the responsibility of storing…
A: Given: A trend in database management, known as Database as a Service, places the responsibility of…
Q: just answer true/false. a] There are three main components of ER model which are an entity, an…
A: Defined the given statements true or false
Q: an Entity and Attribute? Write different types of Entities and Attributes, along with their specific
A: The fundamental distinction between the entity associated attribute is that associate entity is an…
Q: Defineanomaly? A database with three anomalies? Are you going to identify the issues and come up…
A: Introduction: Anomaly in database: Any flaw/issue that occurs while performing/completing the…
Q: 8. What is a Database? A. A Data mining program B. A Customer Table C. A collection of related…
A: Database refers to the organized collections of the raw datas that are collected and stored…
Q: . In database schema, the database snapshot is also called a. current set of entity b. current set…
A: A database schema represents the logical configuration of all or part of a relational database. It…
Q: Which of the following contains a complete record of all activity that affected the contents of a…
A: Database Management System(DBMS) is a software for storing and retrieving users data while…
Q: 4.1Illustrate the different types of users in a database environment and the distinct purpose of…
A: *As per the company norms and guidelines we are providing first question answer only,so please…
Q: A company has a single table in a computer(e.g a spreadsheet) in which every information about each…
A: 1) A company has a single table in a computer(e.g a spreadsheet) in which every information about…
Q: What is database security?
A: Actually, database is a used to stores the data.
Q: Fill in the blank with the appropriate word from the options given. A referential integrity…
A: Given:
Q: Describe three (3) modern approaches for safeguarding your database environment in more than sixty…
A: Introduction: For the sake of this part, we'll talk about data set and server hardening, as well as…
Answer:
The correct option is “(b) an entity’s unique identifier”
Step by step
Solved in 2 steps

- Which of the following are true about primary keys? SELECT ALL THAT APPLY. A) They must reference one or more columns in a single table. B) They are usually implemented using an index. C) They guarantee that no two rows in a table have duplicate primary key values. D) They must be defined for every database table.Defineanomaly? What's the big deal about finding three outliers in a database? When will you take notice of the issues and provide a solution?What are the four basic types of operations for a database application? a. Insert, Select, Update, and Delete b. Insert, Update, Delete, and Create c. Insert, Update, Delete, and Render d. Insert, Select, Update, and Render If stringa="Good Morning", what is the value of stringa[1:5]? a. "Good " b. "ood " c. "Good" d. "ood M" The instance that “a survey respondent in service occupation (x) is less likely to report income ” is an example of __________ . a. Missing completely at random. b. Missing at random. c. Missing not at random. d. None of the above.
- Hello can you help me make a normalized ERD using the table details from below The database name is Vaccination and there is a table login and table record which is below Thank You very muchHow do locks work? Describe the main distinction between a shared lock and an exclusive lock during a database transaction.Can you answer question 4 and 5: question 4: The unique identity assigned to each independent object in an ODB database is known as the:A) primary keyB) hidden valueC) candidate key D) foreign keyE) object identtiferquestion 5: One type of transaction schedulcing which is always considered to be correct is a(n) blank schedulce:A) serializable B) SQLC) train-basedD) deadlock E) object -oriented
- 1. Which of the following statements about ScroogeCoin is INCORRECT? A. A designated entity called Scrooge publishes an append‐only ledger containing the history of all the transactions that have happened. B. Scrooge can build a block chain, which is a series of data blocks, each with one transaction in it. C. ScroogeCoin can address the double spending issue. D. ScroogeCoin can implement coin minting, transaction, and IDs' assignment in a fully decentralized way.Which of the following is the representation of an entity in a database? Group of answer choices foreign key relation primary key attributeHelloI hope to answer my question and don't use your handwriting, pleaseThank you Try the answer to be unique with references please Describe two techniques that could be used to tune database schema. Support your answer with at least one example for each technique
- Which of the following has no repeating groups but can contain partial or transitive dependencies? unnormalized data 1NF 2NF 3NFHow is a database lockout different from a databasedeadlock? Give an accounting example to illustrate why a databaselockout is necessary and how a deadlock can occur. Use actual tablenames in your example.Which of the following three types of database critical events may initiate the database recovery procedure? Provide illustrations for each.Make a list of and explain the five transaction attributes.





